Drone Jammer
•
1 like•326 views
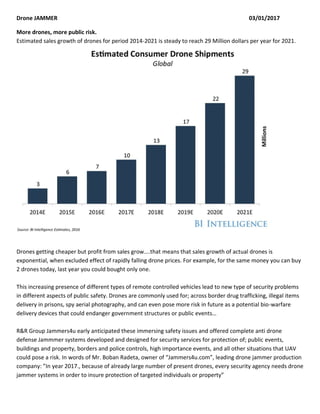
Drone sales are expected to grow exponentially through 2021 despite falling prices, leading to increased security risks from unauthorized drone use. Drones are commonly used for drug trafficking, smuggling contraband into prisons, and aerial spying, and there is concern they could deliver biological weapons. The company R&R Group Jammers4u developed drone jamming systems to protect public events, buildings, borders, and other areas where drones pose risks. The owner of Jammers4u stated that by 2017, security agencies will need drone jamming systems to ensure protection of individuals and property given the large number of drones.
Report
Share
Report
Share
Download to read offline
Recommended
Advanced WiFi Attacks Using Commodity Hardware

Presentation given at BruCON 2015 on low-level (physical layer) attacks against WiFi network. Includes selfish behavior, constant jammer, reactive and selective jamming. Additionally we show to to reliably manipulate encrypted WPA and WPA2 traffic, allowing us to attack WPA-TKIP.
Cell phone detector & jammer

Detector Detects the signal then jammer turns on and jaams the signal within the radius.
Are Drones our best friends?

"Are Drones our best friends?" by Nicola Marietti
Close to 4.3 million drones were shipped worldwide in 2015, and with each drone sold, the risk of 'bad-drone' abuse increases. During those years unexpected convergent consequences explode onto the drone scene at once .A drone is an aerial robot that can be controlled remotely or autonomously, drones are now effective data gathering platforms, Computer vision, sense-and-avoid and optical tracking become standard in consumer drones. Are we safe from a little drone attack? How we can defend our site from this new threat. Security solutions are the big new deal the next future.
Counter Drone Systems Market 2022-2032 - Aviation and Defense Market Reports

Global Counter Drone System market 2022-2032 includes Counter drone technology, commonly referred to as counter-UAS or C-UAS, refers to devices that detect and/or intercept unmanned aircraft systems in flight. As drones become more widely used, counter-UAS technology is continuously developing and changing. Concerns about the threat that drones offer in civilian and military situations have fueled the advancement of C-UAS technology The Table of Content would give the readers a perspective of the coverage of the Global Counter Drone System market 2022-2032.
Recommended
Advanced WiFi Attacks Using Commodity Hardware

Presentation given at BruCON 2015 on low-level (physical layer) attacks against WiFi network. Includes selfish behavior, constant jammer, reactive and selective jamming. Additionally we show to to reliably manipulate encrypted WPA and WPA2 traffic, allowing us to attack WPA-TKIP.
Cell phone detector & jammer

Detector Detects the signal then jammer turns on and jaams the signal within the radius.
Are Drones our best friends?

"Are Drones our best friends?" by Nicola Marietti
Close to 4.3 million drones were shipped worldwide in 2015, and with each drone sold, the risk of 'bad-drone' abuse increases. During those years unexpected convergent consequences explode onto the drone scene at once .A drone is an aerial robot that can be controlled remotely or autonomously, drones are now effective data gathering platforms, Computer vision, sense-and-avoid and optical tracking become standard in consumer drones. Are we safe from a little drone attack? How we can defend our site from this new threat. Security solutions are the big new deal the next future.
Counter Drone Systems Market 2022-2032 - Aviation and Defense Market Reports

Global Counter Drone System market 2022-2032 includes Counter drone technology, commonly referred to as counter-UAS or C-UAS, refers to devices that detect and/or intercept unmanned aircraft systems in flight. As drones become more widely used, counter-UAS technology is continuously developing and changing. Concerns about the threat that drones offer in civilian and military situations have fueled the advancement of C-UAS technology The Table of Content would give the readers a perspective of the coverage of the Global Counter Drone System market 2022-2032.
counter drone market

The Counter Drone Systems (anti drone) Market Industry is expected to grow from USD 3,965.0 Million in 2022 to USD 8,749.0 Million by 2022, at a CAGR of 18.7% between 2022 and 2032.
Protecting People and Property Against Drone Threats

Here you will learn about the potential risks of drones, the challenges to protecting people and property, and ways to overcome them.
Improve Commercial Drone Operations by ZenaDrone

ZenaDrone Business Drones technology is available for various industry sectors. Here are some examples of multiple industries.
The Rise of Anti-Drone Technology: A Look at Drone Jammers

By blocking signals, drone signal jammers keep people safe and stop possible dangers and illegal drone activities. Here, we will now go into more detail about drone signal jammers.
Drones Solution in Dubai

UAE based Dronesmisc specialized in different types of drones solutions like property monitoring drone, aerial mapping and photography drone, civil safety drone and rc vehicle made with advanced technologies.
Advantages of Handheld Drone Jammers

Handheld drone jammers might have a lot of benefits. Are you curious about how these portable device help to safeguard and preserve critical regions and stop the entry of unlawful drone activities? Read here.
The Necessity of Advanced Anti-Drone Tech

The exponential growth of drones has also provided tools or means to many crimes including espionage, drug delivery, trespassing and more. Anti-drone technology has become a formidable solution for safeguarding airspace integrity.
DRONES THE NEW WEAPON OF CHOICE - ALSO FOR HACKERS

My talk will be about drone threats in general and how you can assess drone based threats. I will show the comprehensive threat assessment methodology and the countermeasures you can take against the drone threat. The threat assessment is based on a catalog of about 140 items. Particularly interesting will be looking at the drone threats in relation to:
Planting payload at specific locations (i.e. hacking equipment transported to target location for instance)
Tampering communication equipment with the help of drones
Insider threat communicate with an insider with the help of a drone
Hacking the communication of a drone
Privacy violations
etc.
Drones: The Insurance Industry's Next Game-Changer?

Drones promise to be the next disruptive technology -- poised to dramatically alter how industry sectors, including property and casualty insurers, conduct business. Drones have the potential to streamline and reduce the cost of insurance-related processes, including claims adjustment, risk-engineering, post-catastrophe claims settlements and weeding out fraudulent agricultural claims.
The Most Amazing Examples Of Drones In Use Today: From Scary To Incredibly He...

Unmanned aerial vehicles (UAVs) or drones are starting to be more commonplace. While there are many ways they can be scary, drones can be deployed in lots of helpful ways, as well as just for entertainment. Here are a few of the ways drones are used today.
Drone-Proofing Critical Infrastructure with Anti-Drone Systems.pdf

In critical establishments like defense bases, government buildings, and public hubs like airports and stadiums where the crowd is beyond control, counter-drone technology isn’t just an alternative; it’s a mandate.
A TASK BASED information break down of COUNTERING UAV

THE RAPID SPREAD AND GROWING USE OF UNMANNED AERIAL VEHICLES (UAV) BY INDIVIDUALS, THE PRIVATE SECTOR AND TERRORISTS HAS GIVEN WAY TO NUMEROUS DEVELOPING SECURITY CONCERNS. THIS ARTICLE ANALYSES HOW GOVERNMENT, REGULATORS, SECURITY SERVICES, LAW ENFORCEMENT CAN ADDRESS SOME OF THESE CONCERNS. COUNTERING THESE SECURITY THREATS IS COMPLEX AS THE THREATS HAVE TO BE COUNTERED AT DIFFERENT TECHNOLOGICAL LEVELS AND INTENDED USE SUCH AS TERRORIST, CRIMINAL, MILITARY, INTELLIGENCE, SAFETY ETC. TO ENABLE ANALYSIS A FRAMEWORK IS INTRODUCED TO CLASSIFY THE TASKS COMMONLY ASSOCIATED WITH ADDRESSING SECURITY THREATS: INTELLIGENCE, GUARD AND SECURE, OPERATIONS AND LAW ENFORCEMENT. USING THIS FRAMEWORK A BREAKDOWN OF THE INFORMATION NECESSARY TO PERFORM THE DIFFERENT TASKS IS INTRODUCED. WE ANALYSED WHAT INFORMATION NEEDS TO BE GATHERED TO ENABLE THE DEVELOPMENT AND EXECUTION OF COUNTER MEASURES ASSOCIATED WITH THE DIFFERENT TASKS. SPECIAL ATTENTION IS PAID TO HOW DIGITAL FORENSICS ON UAV’S COULD CONTRIBUTE TO THE TASKS OF INTELLIGENCE, GUARD AND SECURE, OPERATIONS AND LAW ENFORCEMENT.
How Drone Guns Are Shaping the Future of Security

Anti-drone systems like drone guns have evolved as a game-changer in safeguarding airspaces and reshaping the future of security. Read here.
Understanding the Functionalities of the Anti-Drone Systems.pdf

The ideal solution is to rely on anti-drone systems to counter threats and enhance airspace security. Here, you will explore the top functionalities of counter-drone systems.
The Role of Anti-Drone Systems in Ensuring Public Safety

The need for anti-drone for law enforcement now is more substantial than ever, and to prove this, here’s how drones pose a threat to public gatherings.
Zena drone 1000 uses in Commercial Drone Industry

ZenaDrone 1000 creates a new perspective and plenty of possibilities in the field of commercial drones and is very useful as a Drone.
Let's hack your mobile device. Yes we can. And many other do.

Tommi Kallberg, Mobile security engineer, Checkpoint / Opticom https://dssitsec.eu
Why are Drone Jammers Used for the Security?

Drone usage is becoming more prevalent than you think! Especially when it comes to our security authorities, these unmanned aerial vehicles (UAVs) / drones are identified as potential threats.
Jamaxpro 5G 21 Antenna 21w handheld mobile phone wif gps lojack jammer

Jamaxpro 5G 21 Antenna 21w handheld mobile phone wif gps lojack jammerShop-WiFi - Wireless RF Technology R&R Group Jammers4u
Jamaxpro 5G 21 Antenna 21w handheld mobile phone wif gps lojack jammer http://www.jammers4u.com
#jammer #jammers #5gJammer #rfJammer #21antennajammer #rf #Rc #gpsCt-2020 20 bands 5 g mobile phone wif gps uhf vhf jammer

Ct-2020 20 bands 5 g mobile phone wif gps uhf vhf jammerShop-WiFi - Wireless RF Technology R&R Group Jammers4u
Ct-2020 20 bands 5 g mobile phone wif gps uhf vhf all jammer up to 50m http://www.jammers4u.com
#jammer #jammers #alljammer #signaljammer #wifi #5gMore Related Content
Similar to Drone Jammer
counter drone market

The Counter Drone Systems (anti drone) Market Industry is expected to grow from USD 3,965.0 Million in 2022 to USD 8,749.0 Million by 2022, at a CAGR of 18.7% between 2022 and 2032.
Protecting People and Property Against Drone Threats

Here you will learn about the potential risks of drones, the challenges to protecting people and property, and ways to overcome them.
Improve Commercial Drone Operations by ZenaDrone

ZenaDrone Business Drones technology is available for various industry sectors. Here are some examples of multiple industries.
The Rise of Anti-Drone Technology: A Look at Drone Jammers

By blocking signals, drone signal jammers keep people safe and stop possible dangers and illegal drone activities. Here, we will now go into more detail about drone signal jammers.
Drones Solution in Dubai

UAE based Dronesmisc specialized in different types of drones solutions like property monitoring drone, aerial mapping and photography drone, civil safety drone and rc vehicle made with advanced technologies.
Advantages of Handheld Drone Jammers

Handheld drone jammers might have a lot of benefits. Are you curious about how these portable device help to safeguard and preserve critical regions and stop the entry of unlawful drone activities? Read here.
The Necessity of Advanced Anti-Drone Tech

The exponential growth of drones has also provided tools or means to many crimes including espionage, drug delivery, trespassing and more. Anti-drone technology has become a formidable solution for safeguarding airspace integrity.
DRONES THE NEW WEAPON OF CHOICE - ALSO FOR HACKERS

My talk will be about drone threats in general and how you can assess drone based threats. I will show the comprehensive threat assessment methodology and the countermeasures you can take against the drone threat. The threat assessment is based on a catalog of about 140 items. Particularly interesting will be looking at the drone threats in relation to:
Planting payload at specific locations (i.e. hacking equipment transported to target location for instance)
Tampering communication equipment with the help of drones
Insider threat communicate with an insider with the help of a drone
Hacking the communication of a drone
Privacy violations
etc.
Drones: The Insurance Industry's Next Game-Changer?

Drones promise to be the next disruptive technology -- poised to dramatically alter how industry sectors, including property and casualty insurers, conduct business. Drones have the potential to streamline and reduce the cost of insurance-related processes, including claims adjustment, risk-engineering, post-catastrophe claims settlements and weeding out fraudulent agricultural claims.
The Most Amazing Examples Of Drones In Use Today: From Scary To Incredibly He...

Unmanned aerial vehicles (UAVs) or drones are starting to be more commonplace. While there are many ways they can be scary, drones can be deployed in lots of helpful ways, as well as just for entertainment. Here are a few of the ways drones are used today.
Drone-Proofing Critical Infrastructure with Anti-Drone Systems.pdf

In critical establishments like defense bases, government buildings, and public hubs like airports and stadiums where the crowd is beyond control, counter-drone technology isn’t just an alternative; it’s a mandate.
A TASK BASED information break down of COUNTERING UAV

THE RAPID SPREAD AND GROWING USE OF UNMANNED AERIAL VEHICLES (UAV) BY INDIVIDUALS, THE PRIVATE SECTOR AND TERRORISTS HAS GIVEN WAY TO NUMEROUS DEVELOPING SECURITY CONCERNS. THIS ARTICLE ANALYSES HOW GOVERNMENT, REGULATORS, SECURITY SERVICES, LAW ENFORCEMENT CAN ADDRESS SOME OF THESE CONCERNS. COUNTERING THESE SECURITY THREATS IS COMPLEX AS THE THREATS HAVE TO BE COUNTERED AT DIFFERENT TECHNOLOGICAL LEVELS AND INTENDED USE SUCH AS TERRORIST, CRIMINAL, MILITARY, INTELLIGENCE, SAFETY ETC. TO ENABLE ANALYSIS A FRAMEWORK IS INTRODUCED TO CLASSIFY THE TASKS COMMONLY ASSOCIATED WITH ADDRESSING SECURITY THREATS: INTELLIGENCE, GUARD AND SECURE, OPERATIONS AND LAW ENFORCEMENT. USING THIS FRAMEWORK A BREAKDOWN OF THE INFORMATION NECESSARY TO PERFORM THE DIFFERENT TASKS IS INTRODUCED. WE ANALYSED WHAT INFORMATION NEEDS TO BE GATHERED TO ENABLE THE DEVELOPMENT AND EXECUTION OF COUNTER MEASURES ASSOCIATED WITH THE DIFFERENT TASKS. SPECIAL ATTENTION IS PAID TO HOW DIGITAL FORENSICS ON UAV’S COULD CONTRIBUTE TO THE TASKS OF INTELLIGENCE, GUARD AND SECURE, OPERATIONS AND LAW ENFORCEMENT.
How Drone Guns Are Shaping the Future of Security

Anti-drone systems like drone guns have evolved as a game-changer in safeguarding airspaces and reshaping the future of security. Read here.
Understanding the Functionalities of the Anti-Drone Systems.pdf

The ideal solution is to rely on anti-drone systems to counter threats and enhance airspace security. Here, you will explore the top functionalities of counter-drone systems.
The Role of Anti-Drone Systems in Ensuring Public Safety

The need for anti-drone for law enforcement now is more substantial than ever, and to prove this, here’s how drones pose a threat to public gatherings.
Zena drone 1000 uses in Commercial Drone Industry

ZenaDrone 1000 creates a new perspective and plenty of possibilities in the field of commercial drones and is very useful as a Drone.
Let's hack your mobile device. Yes we can. And many other do.

Tommi Kallberg, Mobile security engineer, Checkpoint / Opticom https://dssitsec.eu
Why are Drone Jammers Used for the Security?

Drone usage is becoming more prevalent than you think! Especially when it comes to our security authorities, these unmanned aerial vehicles (UAVs) / drones are identified as potential threats.
Similar to Drone Jammer (20)
Protecting People and Property Against Drone Threats

Protecting People and Property Against Drone Threats
The Rise of Anti-Drone Technology: A Look at Drone Jammers

The Rise of Anti-Drone Technology: A Look at Drone Jammers
DRONES THE NEW WEAPON OF CHOICE - ALSO FOR HACKERS

DRONES THE NEW WEAPON OF CHOICE - ALSO FOR HACKERS
Drones: The Insurance Industry's Next Game-Changer?

Drones: The Insurance Industry's Next Game-Changer?
The Most Amazing Examples Of Drones In Use Today: From Scary To Incredibly He...

The Most Amazing Examples Of Drones In Use Today: From Scary To Incredibly He...
Drone-Proofing Critical Infrastructure with Anti-Drone Systems.pdf

Drone-Proofing Critical Infrastructure with Anti-Drone Systems.pdf
A TASK BASED information break down of COUNTERING UAV

A TASK BASED information break down of COUNTERING UAV
Understanding the Functionalities of the Anti-Drone Systems.pdf

Understanding the Functionalities of the Anti-Drone Systems.pdf
The Role of Anti-Drone Systems in Ensuring Public Safety

The Role of Anti-Drone Systems in Ensuring Public Safety
Let's hack your mobile device. Yes we can. And many other do.

Let's hack your mobile device. Yes we can. And many other do.
More from Shop-WiFi - Wireless RF Technology R&R Group Jammers4u
Jamaxpro 5G 21 Antenna 21w handheld mobile phone wif gps lojack jammer

Jamaxpro 5G 21 Antenna 21w handheld mobile phone wif gps lojack jammerShop-WiFi - Wireless RF Technology R&R Group Jammers4u
Jamaxpro 5G 21 Antenna 21w handheld mobile phone wif gps lojack jammer http://www.jammers4u.com
#jammer #jammers #5gJammer #rfJammer #21antennajammer #rf #Rc #gpsCt-2020 20 bands 5 g mobile phone wif gps uhf vhf jammer

Ct-2020 20 bands 5 g mobile phone wif gps uhf vhf jammerShop-WiFi - Wireless RF Technology R&R Group Jammers4u
Ct-2020 20 bands 5 g mobile phone wif gps uhf vhf all jammer up to 50m http://www.jammers4u.com
#jammer #jammers #alljammer #signaljammer #wifi #5gCt-2020h 20 bands Antennas 5g mobile phone wif gps uhf vhf all jammer

Ct-2020h 20 bands Antennas 5g mobile phone wif gps uhf vhf all jammerShop-WiFi - Wireless RF Technology R&R Group Jammers4u
Ct-2020h 20 bands Antennas 5g mobile phone wif gps uhf vhf all jammer up to 80m http://www.jammers4u.com #jammers #jammer #alljammer #jammers4u Ct-1080h new 4G 5G 8 bands 69w handheld mobile phone jammer

Ct-1080h new 4G 5G 8 bands 69w handheld mobile phone jammerShop-WiFi - Wireless RF Technology R&R Group Jammers4u
Ct-1080h new 4G 5G 8 bands antennas 69w handheld mobile phone jammer
#jammer #jammers #jammers4u http://www.jammers4u.com Ct 1016 new 16 bands 16 w handheld 5g 4g mobile phone wif gps lojack jammer

Ct 1016 new 16 bands 16 w handheld 5g 4g mobile phone wif gps lojack jammerShop-WiFi - Wireless RF Technology R&R Group Jammers4u
t 1016 new 16 bands 16 w handheld 5g 4g mobile phone wif gps lojack jammer Ct 1016 16 bands handheld jammer user manual v.21.01

Ct 1016 16 bands handheld jammer user manual v.21.01Shop-WiFi - Wireless RF Technology R&R Group Jammers4u
Ct 1016 16 bands handheld jammer user manual v.21.01DJ-UAV series outdoor anti-drone uav jammer up to 2500m

DJ-UAV series outdoor anti-drone uav jammer up to 2500mShop-WiFi - Wireless RF Technology R&R Group Jammers4u
DJI-UAV series outdoor anti-drone uav jammer up to 2500m http://www.jammers4u.comCT-1040H-DJ Anti-drone hunter jammer user manual v.19.03

CT-1040H-DJ Anti-drone hunter jammer user manual v.19.03Shop-WiFi - Wireless RF Technology R&R Group Jammers4u
CT-1040H-DJ Anti UAV Drone RC GPS 2.4Ghz 5.8Ghz 28W Handheld wearable Jammer up to 500m
Designed to be compact for easy carrying of police and military on terrain use, CT-1040H-DJ Wearable Handheld portable Jammer is specialized to protect soldiers against commercially available drones used by enemy forces for reconnaissance or as weapon delivery systems.
It is fully autonomus with built in antennas and battery for 40 min operation. It is best suited for military special operations teams, police, security forces that are deployed in different situations
Specialized to block 2.4Ghz, GPS, and 5.8Ghz signals that use most of commercial UAV Drones for their remote controls.. The effective blocking range is up to 500 meters. The jamming distance always varied depending on the signal strength and location Do not blocking GSM Cell phones.DDS Bomb IED Jammer Direct Digital Synthesizer Technology

DDS Bomb IED Jammer Direct Digital Synthesizer TechnologyShop-WiFi - Wireless RF Technology R&R Group Jammers4u
DDS Bomb IED Jammer Direct Digital Synthesizer Technology
CT-6080DDS Digital Synthesis Bomb RCIED 8 Bands 800W Jammer up to 1km 16 antennas 123W 8-10w per band 4g mobile phone wif 5ghz gps uhf vhf jammer 

16 antennas 123W 8-10w per band 4g mobile phone wif 5ghz gps uhf vhf jammer Shop-WiFi - Wireless RF Technology R&R Group Jammers4u
16 antennas Medium Power 123W - 8-10w per band 4g mobile phone wif 5ghz gps uhf vhf jammer CT-2016H www.jammers4u.comCt-3076b-uav high power anti-drone pelican jammer

Ct-3076b-uav high power anti-drone pelican jammerShop-WiFi - Wireless RF Technology R&R Group Jammers4u
Ct-3076b-uav high power anti-drone pelican jammerJammers4u ct 3080 n 8 bands 150w 4g mobile phone wifi gps vhf uhf jammer

Jammers4u ct 3080 n 8 bands 150w 4g mobile phone wifi gps vhf uhf jammerShop-WiFi - Wireless RF Technology R&R Group Jammers4u
Jammers4u ct 3080 n 8 bands 150w 4g mobile phone wifi gps vhf uhf jammer(2)More from Shop-WiFi - Wireless RF Technology R&R Group Jammers4u (20)
Jamaxpro 5G 21 Antenna 21w handheld mobile phone wif gps lojack jammer

Jamaxpro 5G 21 Antenna 21w handheld mobile phone wif gps lojack jammer
Ct-2020 20 bands 5 g mobile phone wif gps uhf vhf jammer

Ct-2020 20 bands 5 g mobile phone wif gps uhf vhf jammer
Ct-2020h 20 bands Antennas 5g mobile phone wif gps uhf vhf all jammer

Ct-2020h 20 bands Antennas 5g mobile phone wif gps uhf vhf all jammer
Ct-1080h new 4G 5G 8 bands 69w handheld mobile phone jammer

Ct-1080h new 4G 5G 8 bands 69w handheld mobile phone jammer
Ct 1016 new 16 bands 16 w handheld 5g 4g mobile phone wif gps lojack jammer

Ct 1016 new 16 bands 16 w handheld 5g 4g mobile phone wif gps lojack jammer
Ct 1016 16 bands handheld jammer user manual v.21.01

Ct 1016 16 bands handheld jammer user manual v.21.01
DJ-UAV series outdoor anti-drone uav jammer up to 2500m

DJ-UAV series outdoor anti-drone uav jammer up to 2500m
CT-1040H-DJ Anti-drone hunter jammer user manual v.19.03

CT-1040H-DJ Anti-drone hunter jammer user manual v.19.03
DDS Bomb IED Jammer Direct Digital Synthesizer Technology

DDS Bomb IED Jammer Direct Digital Synthesizer Technology
16 antennas 123W 8-10w per band 4g mobile phone wif 5ghz gps uhf vhf jammer 

16 antennas 123W 8-10w per band 4g mobile phone wif 5ghz gps uhf vhf jammer
Jammers4u ct 3080 n 8 bands 150w 4g mobile phone wifi gps vhf uhf jammer

Jammers4u ct 3080 n 8 bands 150w 4g mobile phone wifi gps vhf uhf jammer
Recently uploaded
Connector Corner: Automate dynamic content and events by pushing a button

Here is something new! In our next Connector Corner webinar, we will demonstrate how you can use a single workflow to:
Create a campaign using Mailchimp with merge tags/fields
Send an interactive Slack channel message (using buttons)
Have the message received by managers and peers along with a test email for review
But there’s more:
In a second workflow supporting the same use case, you’ll see:
Your campaign sent to target colleagues for approval
If the “Approve” button is clicked, a Jira/Zendesk ticket is created for the marketing design team
But—if the “Reject” button is pushed, colleagues will be alerted via Slack message
Join us to learn more about this new, human-in-the-loop capability, brought to you by Integration Service connectors.
And...
Speakers:
Akshay Agnihotri, Product Manager
Charlie Greenberg, Host
Essentials of Automations: Optimizing FME Workflows with Parameters

Are you looking to streamline your workflows and boost your projects’ efficiency? Do you find yourself searching for ways to add flexibility and control over your FME workflows? If so, you’re in the right place.
Join us for an insightful dive into the world of FME parameters, a critical element in optimizing workflow efficiency. This webinar marks the beginning of our three-part “Essentials of Automation” series. This first webinar is designed to equip you with the knowledge and skills to utilize parameters effectively: enhancing the flexibility, maintainability, and user control of your FME projects.
Here’s what you’ll gain:
- Essentials of FME Parameters: Understand the pivotal role of parameters, including Reader/Writer, Transformer, User, and FME Flow categories. Discover how they are the key to unlocking automation and optimization within your workflows.
- Practical Applications in FME Form: Delve into key user parameter types including choice, connections, and file URLs. Allow users to control how a workflow runs, making your workflows more reusable. Learn to import values and deliver the best user experience for your workflows while enhancing accuracy.
- Optimization Strategies in FME Flow: Explore the creation and strategic deployment of parameters in FME Flow, including the use of deployment and geometry parameters, to maximize workflow efficiency.
- Pro Tips for Success: Gain insights on parameterizing connections and leveraging new features like Conditional Visibility for clarity and simplicity.
We’ll wrap up with a glimpse into future webinars, followed by a Q&A session to address your specific questions surrounding this topic.
Don’t miss this opportunity to elevate your FME expertise and drive your projects to new heights of efficiency.
JMeter webinar - integration with InfluxDB and Grafana

Watch this recorded webinar about real-time monitoring of application performance. See how to integrate Apache JMeter, the open-source leader in performance testing, with InfluxDB, the open-source time-series database, and Grafana, the open-source analytics and visualization application.
In this webinar, we will review the benefits of leveraging InfluxDB and Grafana when executing load tests and demonstrate how these tools are used to visualize performance metrics.
Length: 30 minutes
Session Overview
-------------------------------------------
During this webinar, we will cover the following topics while demonstrating the integrations of JMeter, InfluxDB and Grafana:
- What out-of-the-box solutions are available for real-time monitoring JMeter tests?
- What are the benefits of integrating InfluxDB and Grafana into the load testing stack?
- Which features are provided by Grafana?
- Demonstration of InfluxDB and Grafana using a practice web application
To view the webinar recording, go to:
https://www.rttsweb.com/jmeter-integration-webinar
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

Reflecting on new architectures for knowledge based systems in light of generative ai
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovation With Your Product by VP of Product Design, Warner Music Group
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, Product School
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
"Impact of front-end architecture on development cost", Viktor Turskyi

I have heard many times that architecture is not important for the front-end. Also, many times I have seen how developers implement features on the front-end just following the standard rules for a framework and think that this is enough to successfully launch the project, and then the project fails. How to prevent this and what approach to choose? I have launched dozens of complex projects and during the talk we will analyze which approaches have worked for me and which have not.
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase Enterprise-Wide Efficiency by VP Data Platform, American Express
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Search and Society: Reimagining Information Access for Radical Futures

The field of Information retrieval (IR) is currently undergoing a transformative shift, at least partly due to the emerging applications of generative AI to information access. In this talk, we will deliberate on the sociotechnical implications of generative AI for information access. We will argue that there is both a critical necessity and an exciting opportunity for the IR community to re-center our research agendas on societal needs while dismantling the artificial separation between the work on fairness, accountability, transparency, and ethics in IR and the rest of IR research. Instead of adopting a reactionary strategy of trying to mitigate potential social harms from emerging technologies, the community should aim to proactively set the research agenda for the kinds of systems we should build inspired by diverse explicitly stated sociotechnical imaginaries. The sociotechnical imaginaries that underpin the design and development of information access technologies needs to be explicitly articulated, and we need to develop theories of change in context of these diverse perspectives. Our guiding future imaginaries must be informed by other academic fields, such as democratic theory and critical theory, and should be co-developed with social science scholars, legal scholars, civil rights and social justice activists, and artists, among others.
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

“AGI should be open source and in the public domain at the service of humanity and the planet.”
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on the notifications, alerts, and approval requests using Slack for Bonterra Impact Management. The solutions covered in this webinar can also be deployed for Microsoft Teams.
Interested in deploying notification automations for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
ODC, Data Fabric and Architecture User Group

Let's dive deeper into the world of ODC! Ricardo Alves (OutSystems) will join us to tell all about the new Data Fabric. After that, Sezen de Bruijn (OutSystems) will get into the details on how to best design a sturdy architecture within ODC.
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

In today's fast-changing business world, Companies that adapt and embrace new ideas often need help to keep up with the competition. However, fostering a culture of innovation takes much work. It takes vision, leadership and willingness to take risks in the right proportion. Sachin Dev Duggal, co-founder of Builder.ai, has perfected the art of this balance, creating a company culture where creativity and growth are nurtured at each stage.
Bits & Pixels using AI for Good.........

A whirlwind tour of tech & AI for socio-environmental impact.
Recently uploaded (20)
Connector Corner: Automate dynamic content and events by pushing a button

Connector Corner: Automate dynamic content and events by pushing a button
Essentials of Automations: Optimizing FME Workflows with Parameters

Essentials of Automations: Optimizing FME Workflows with Parameters
JMeter webinar - integration with InfluxDB and Grafana

JMeter webinar - integration with InfluxDB and Grafana
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

To Graph or Not to Graph Knowledge Graph Architectures and LLMs
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, P...
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...
"Impact of front-end architecture on development cost", Viktor Turskyi

"Impact of front-end architecture on development cost", Viktor Turskyi
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase E...
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
Search and Society: Reimagining Information Access for Radical Futures

Search and Society: Reimagining Information Access for Radical Futures
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...
Drone Jammer
- 1. Drone JAMMER 03/01/2017 More drones, more public risk. Estimated sales growth of drones for period 2014-2021 is steady to reach 29 Million dollars per year for 2021. Drones getting cheaper but profit from sales grow....that means that sales growth of actual drones is exponential, when excluded effect of rapidly falling drone prices. For example, for the same money you can buy 2 drones today, last year you could bought only one. This increasing presence of different types of remote controlled vehicles lead to new type of security problems in different aspects of public safety. Drones are commonly used for; across border drug trafficking, illegal items delivery in prisons, spy aerial photography, and can even pose more risk in future as a potential bio-warfare delivery devices that could endanger government structures or public events… R&R Group Jammers4u early anticipated these immersing safety issues and offered complete anti drone defense Jammmer systems developed and designed for security services for protection of; public events, buildings and property, borders and police controls, high importance events, and all other situations that UAV could pose a risk. In words of Mr. Boban Radeta, owner of “Jammers4u.com”, leading drone jammer production company: ”In year 2017., because of already large number of present drones, every security agency needs drone jammer systems in order to insure protection of targeted individuals or property”
