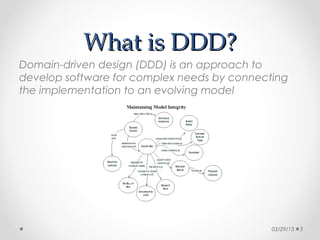
This document provides an overview and introduction to Domain-Driven Design (DDD). It discusses what DDD is, why it is used, and its main building blocks. DDD is an approach to software development that bases the design around the domain model. The document outlines key DDD concepts like entities, value objects, aggregates, repositories, and services. It also discusses patterns like ubiquitous language, bounded contexts, and anticorruption layers. Examples are provided throughout to illustrate DDD concepts and how they apply to complex domain models.