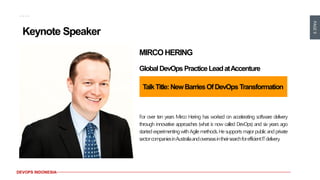
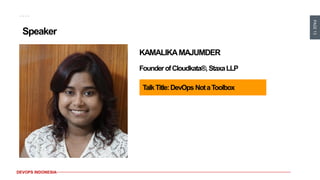
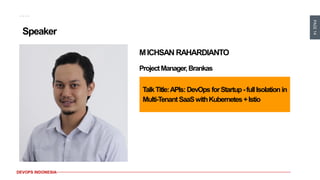
This document announces DevOps Meetup #14 in Jakarta, Indonesia on April 10-11, 2019. It will feature keynote speakers from Accenture and HSBC discussing DevOps transformations and implementing DevSecOps. Additional speakers will discuss topics like continuous delivery, the relationship between DevOps and leadership, and integrating APIs with Kubernetes and Istio. Early bird registration is Rp. 450,000 until February 28th, with prices increasing until the event. Contact information is provided for those interested in attending or getting involved with the DevOps community in Indonesia.