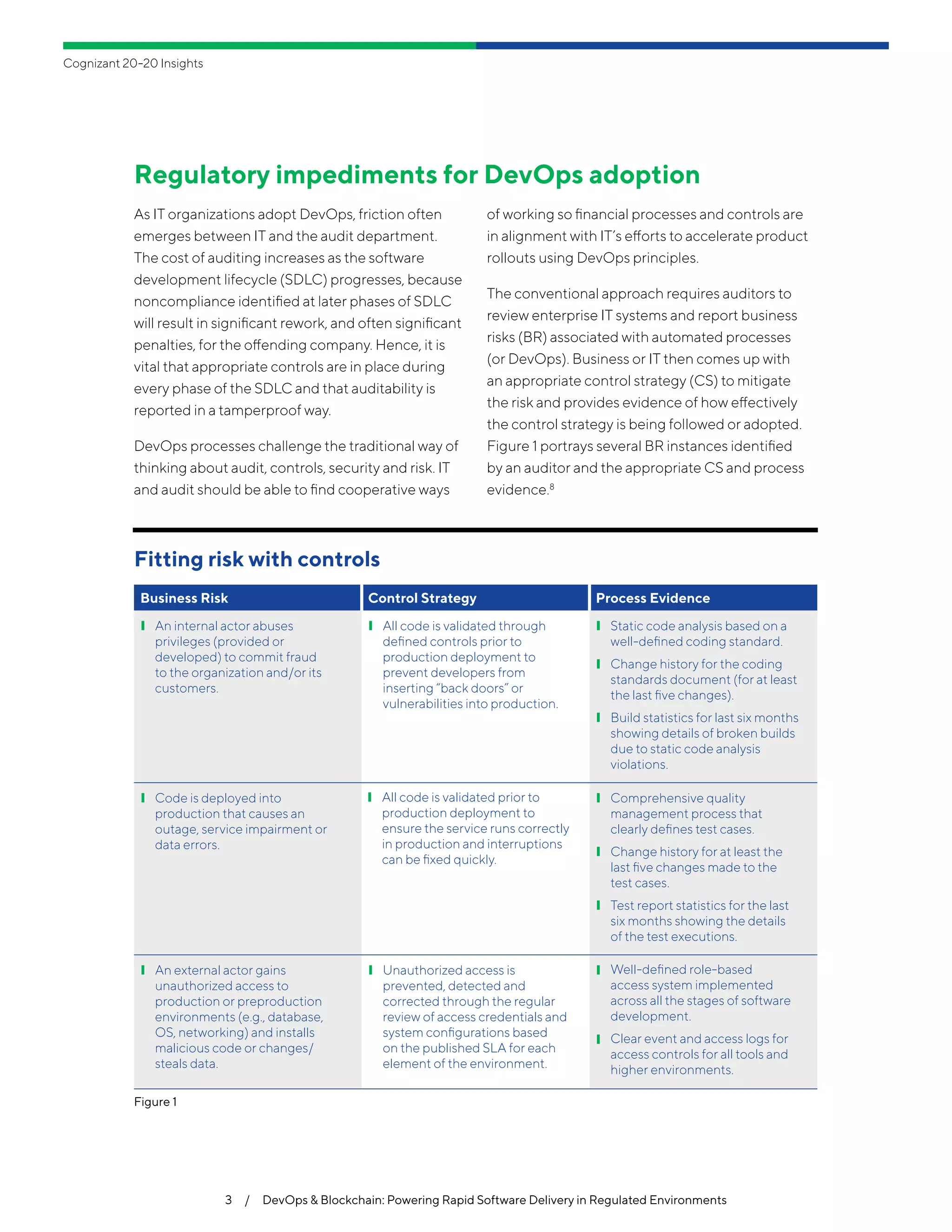
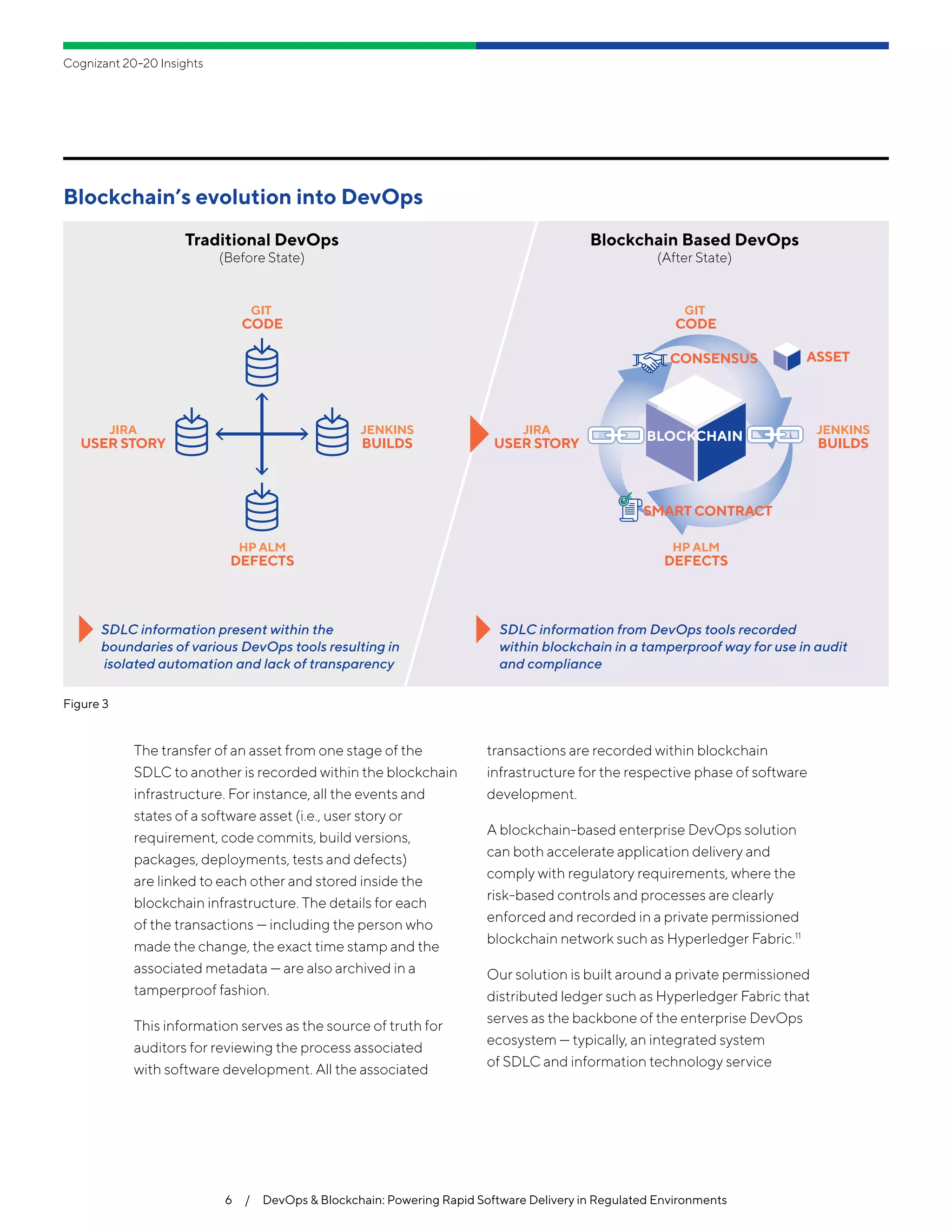
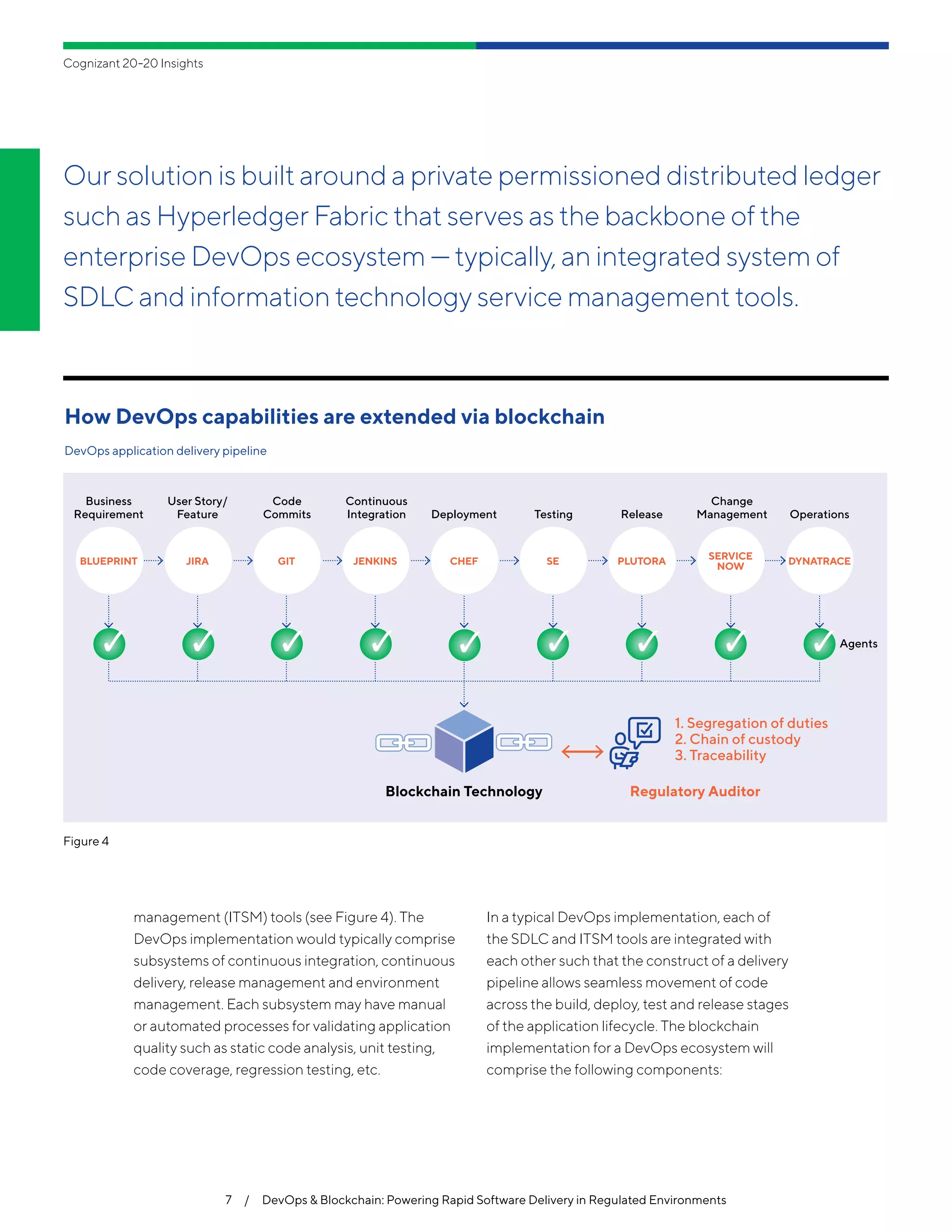
The document discusses the intersection of DevOps and blockchain technology in regulated industries, highlighting challenges in regulatory compliance and the potential of blockchain to provide a tamperproof record of software delivery processes. It emphasizes the need for enterprises to integrate automation in a compliant manner to meet stringent regulatory requirements, particularly in sectors like healthcare and finance. By leveraging blockchain, organizations can achieve faster application delivery while maintaining necessary audit trails and compliance, effectively reducing the time spent on manual processes and enhancing overall transparency.