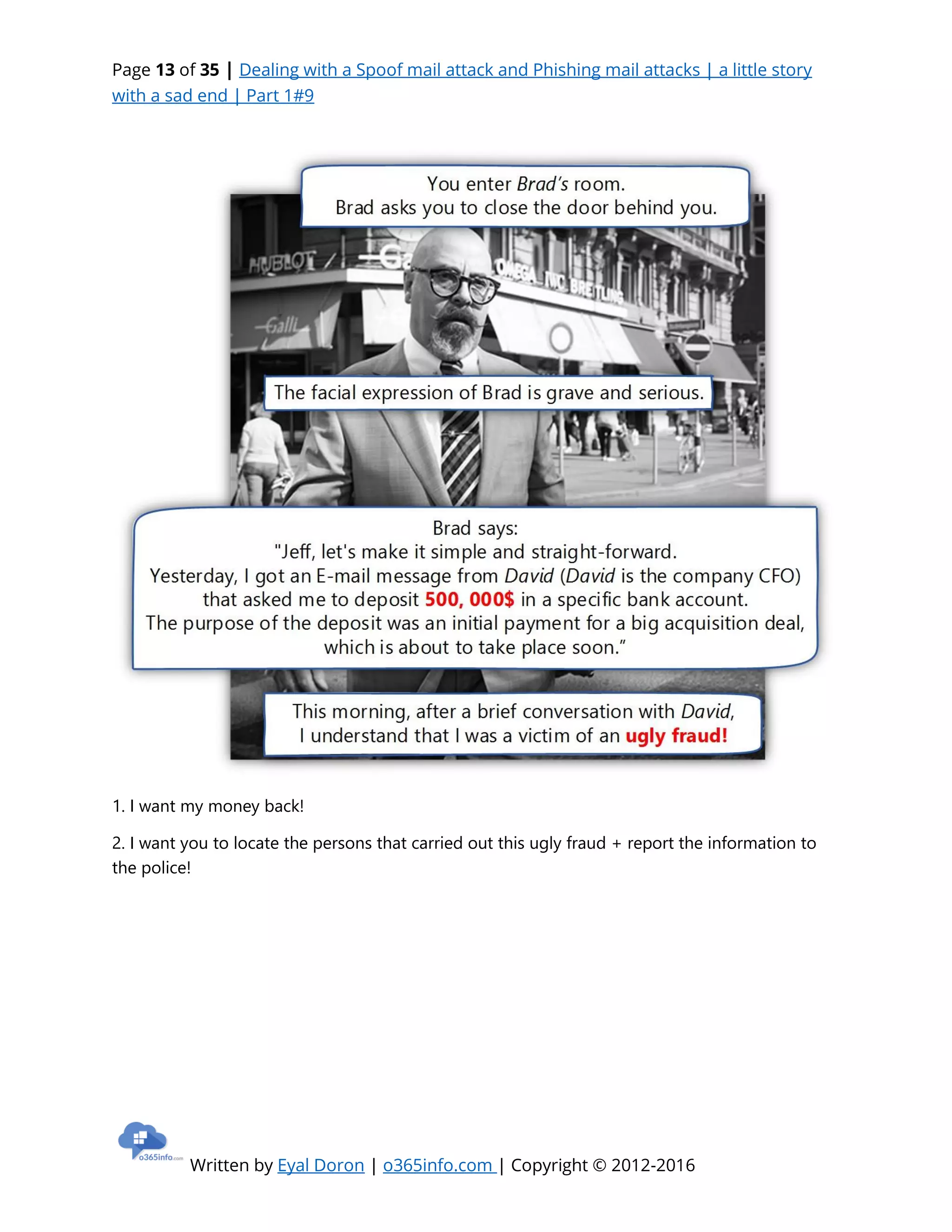
The document narrates a fictional but cautionary tale about the severe consequences of phishing and spoof mail attacks, illustrating the emotional turmoil faced by IT professionals during such incidents. It emphasizes the unfortunate ignorance and overconfidence that organizations possess, leading to vulnerabilities in their mail systems. The story culminates in the protagonist's downfall, serving as a wakeup call for vigilance against cyber threats.