Embed presentation
Download to read offline
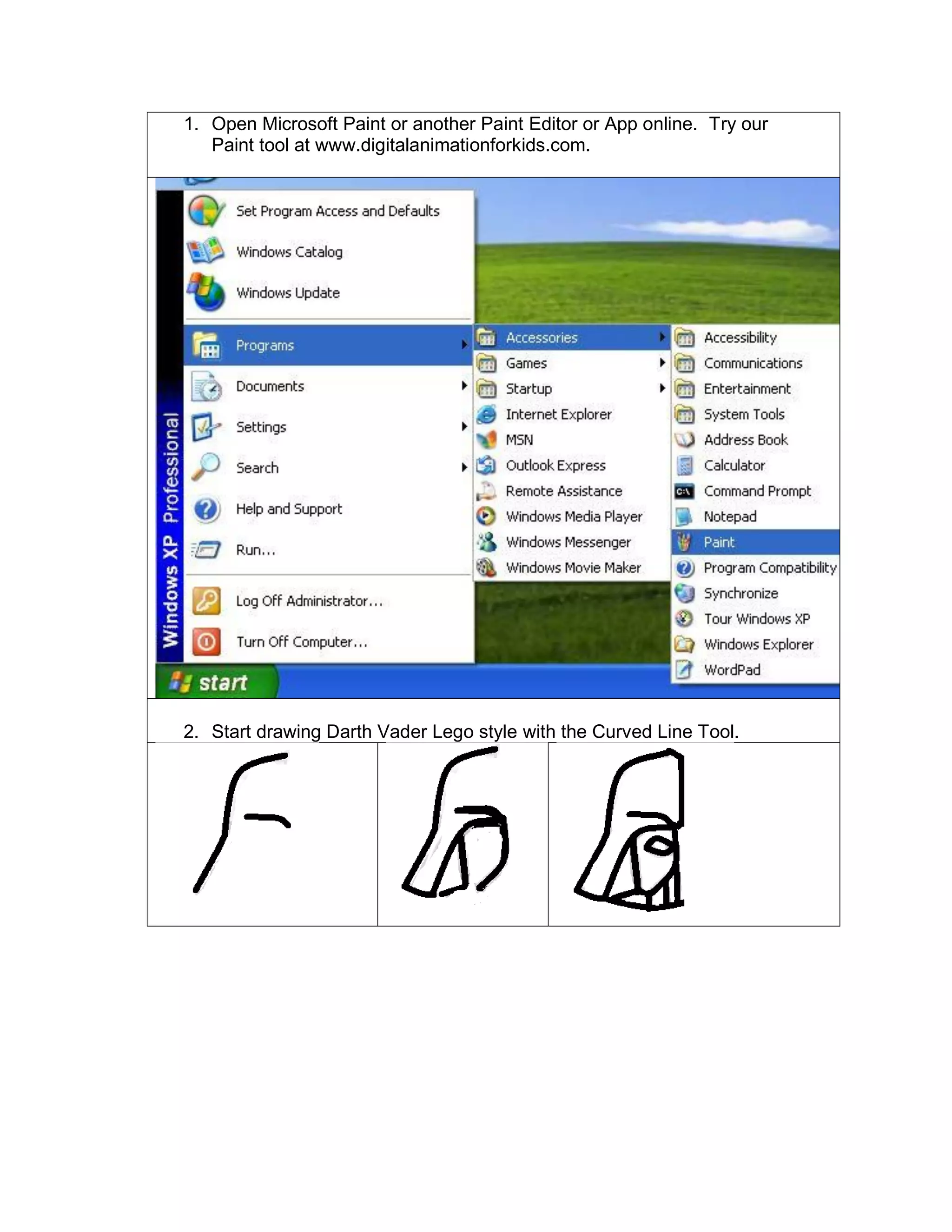
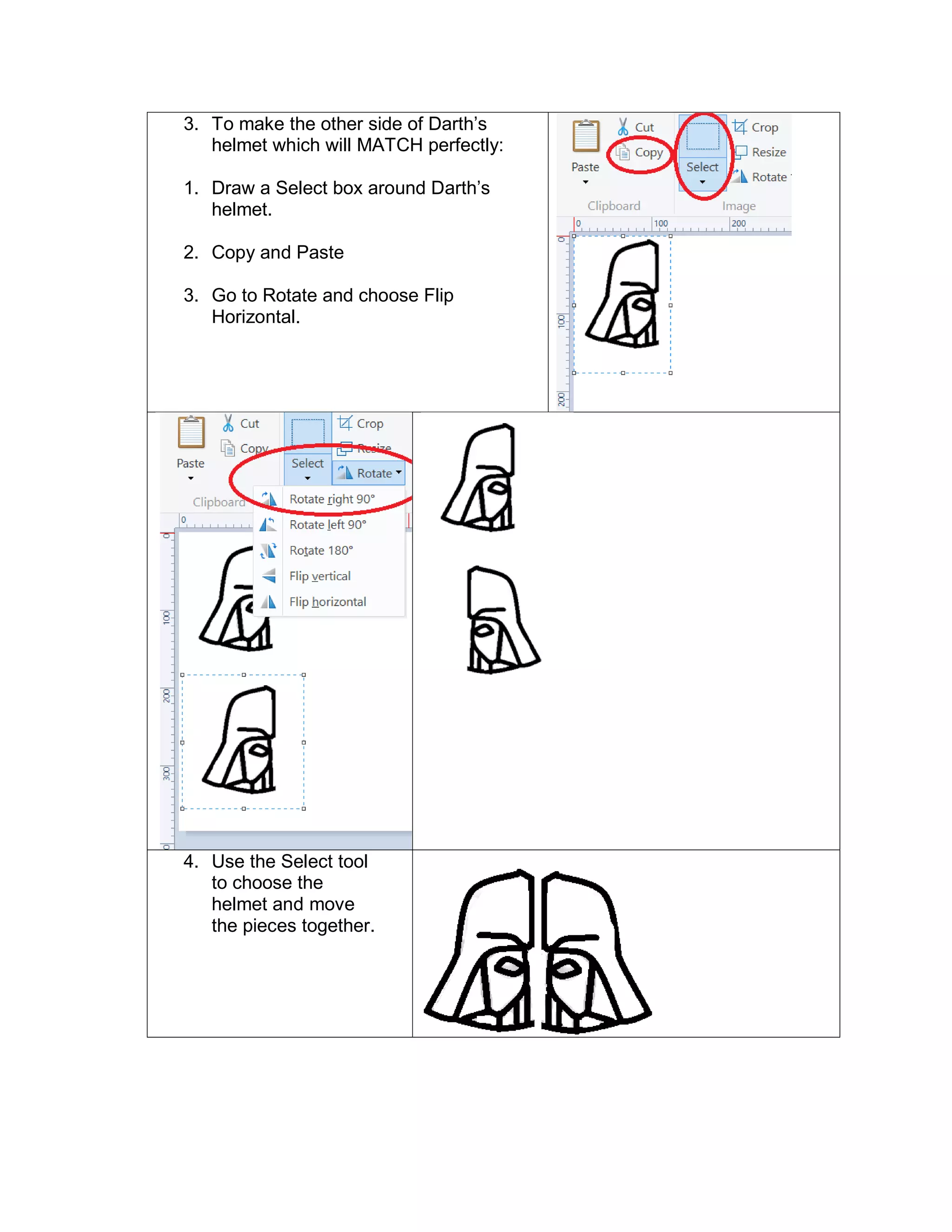
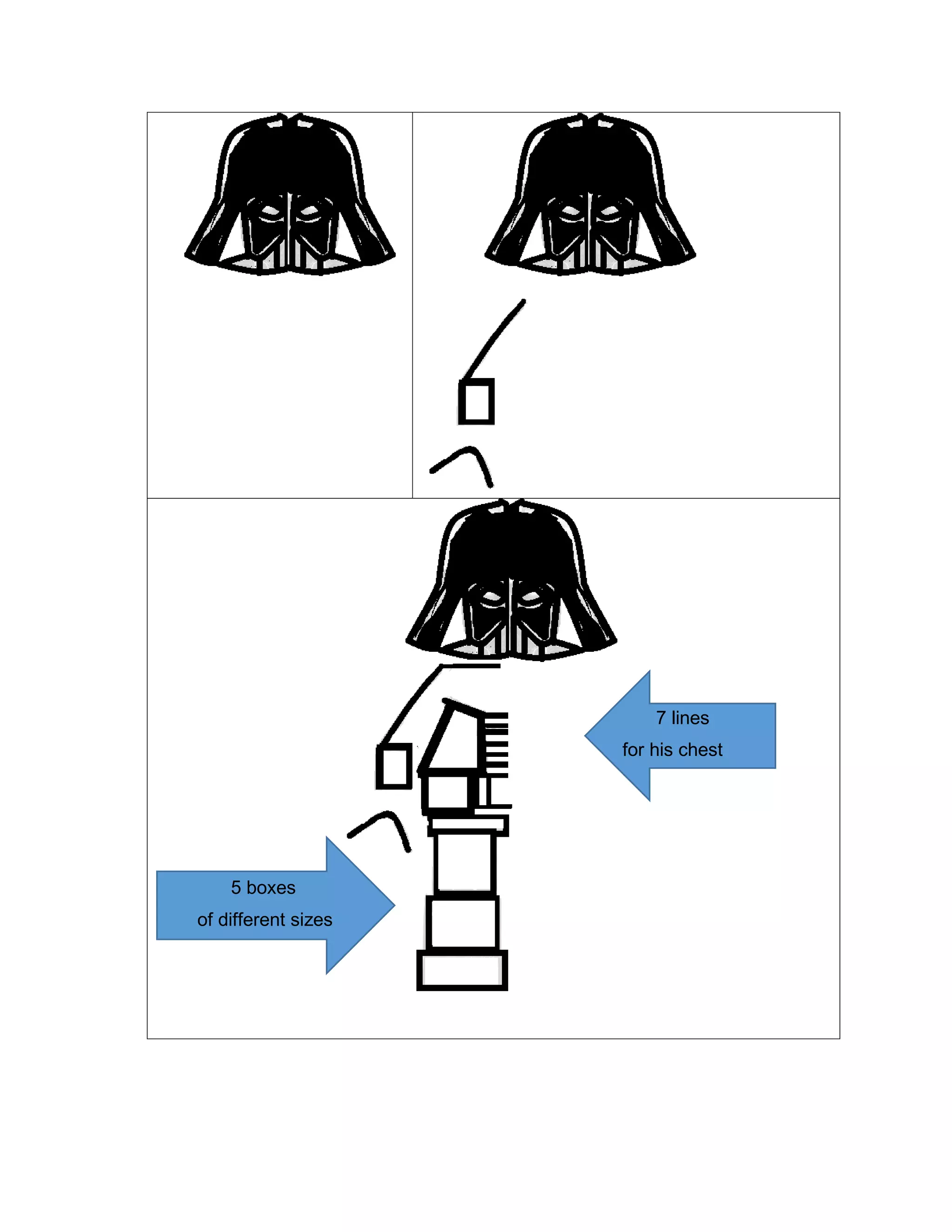
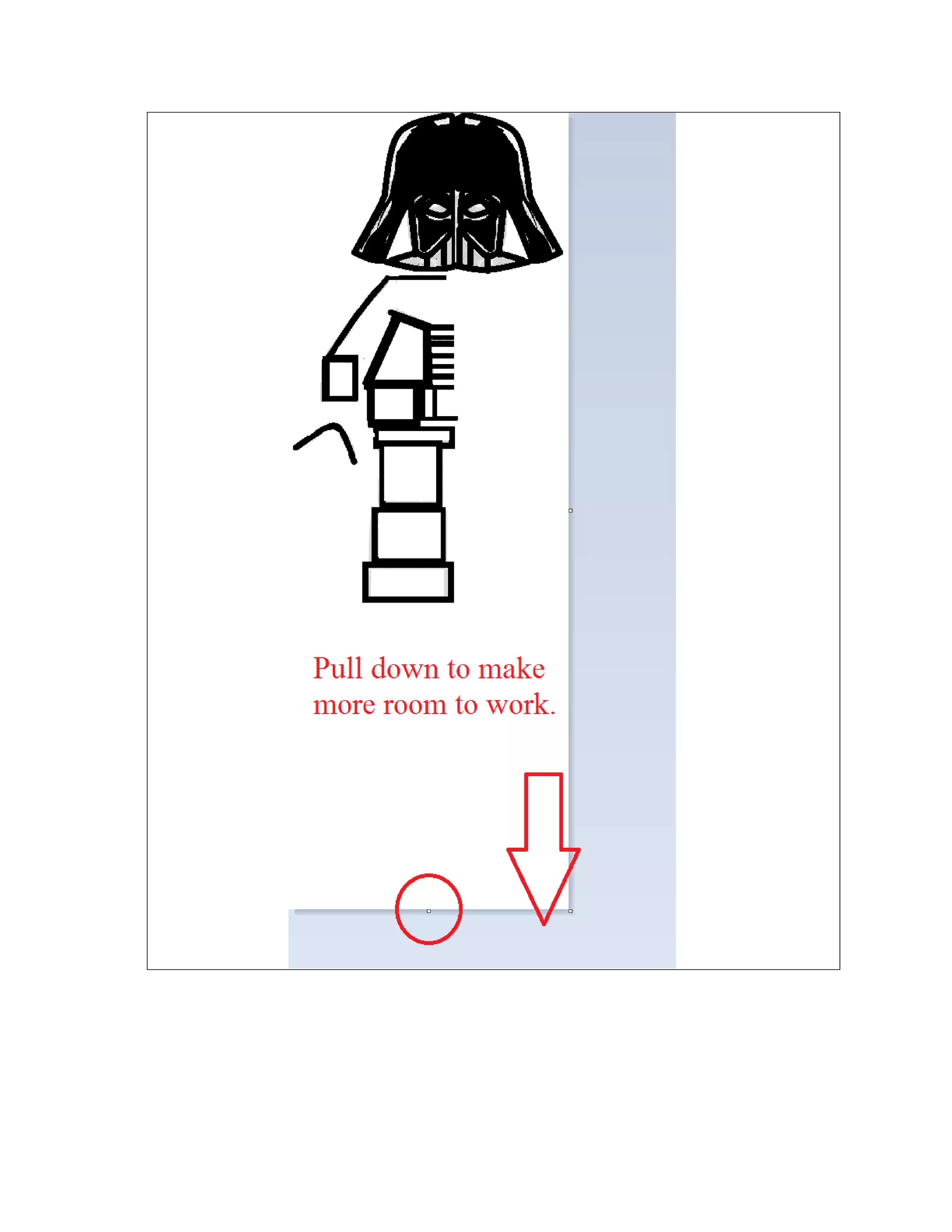
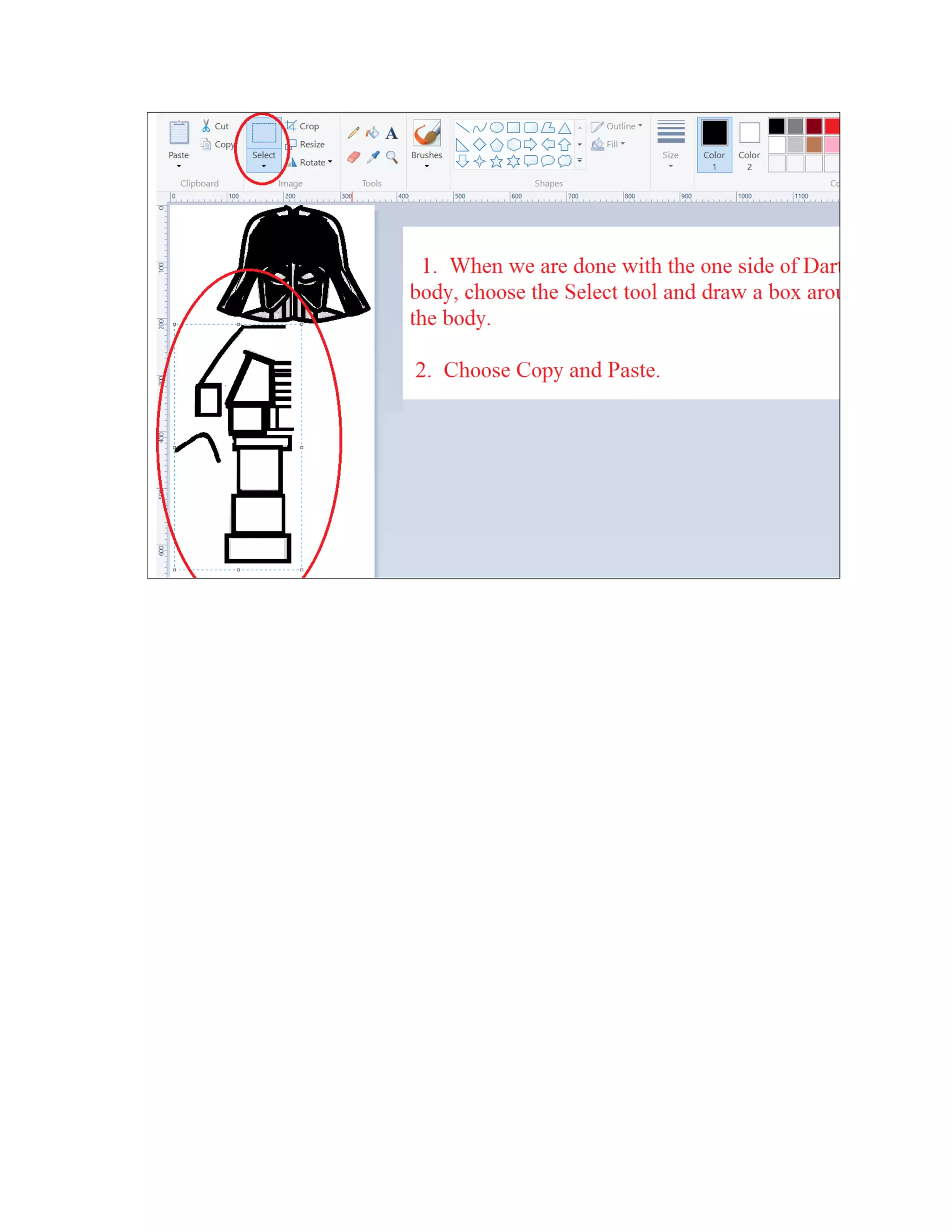
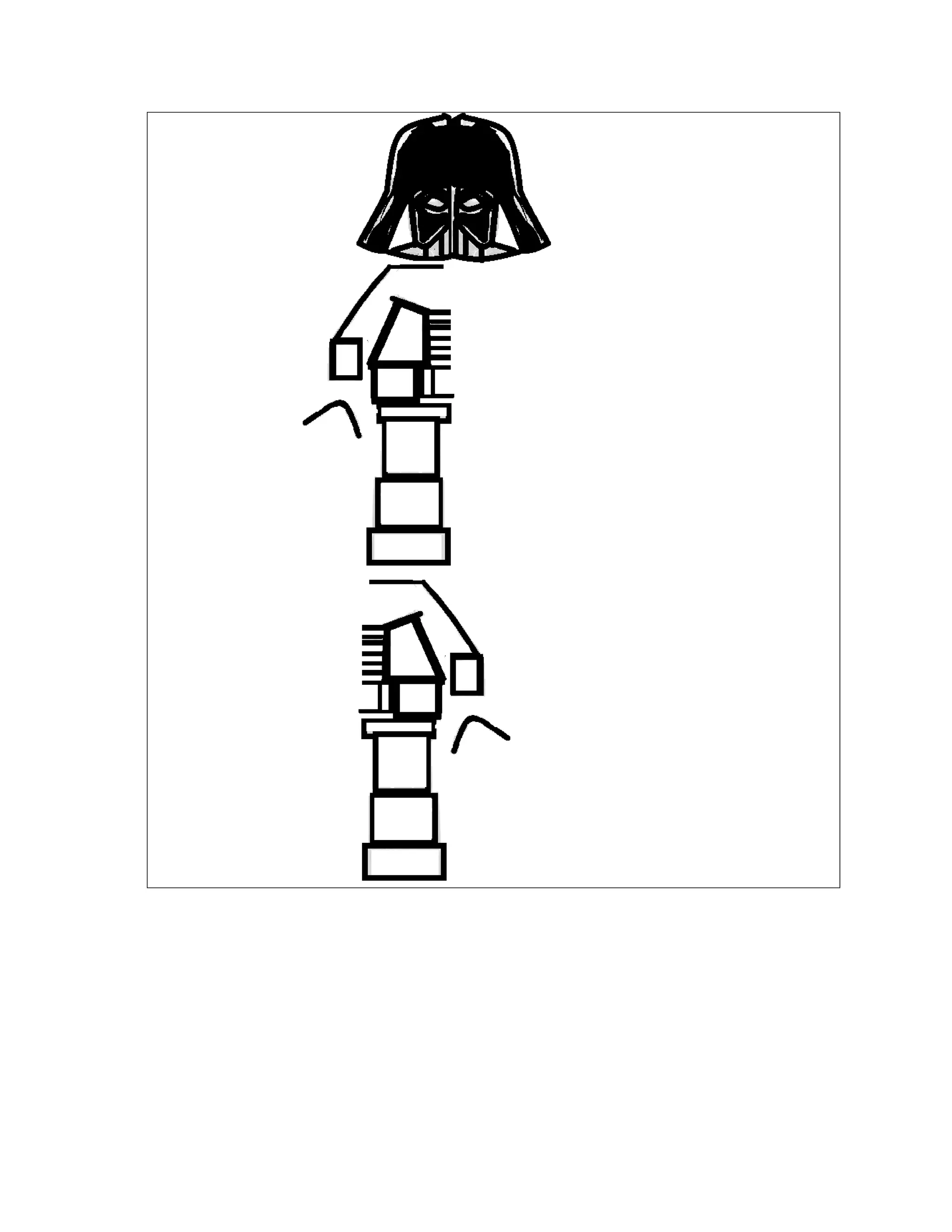
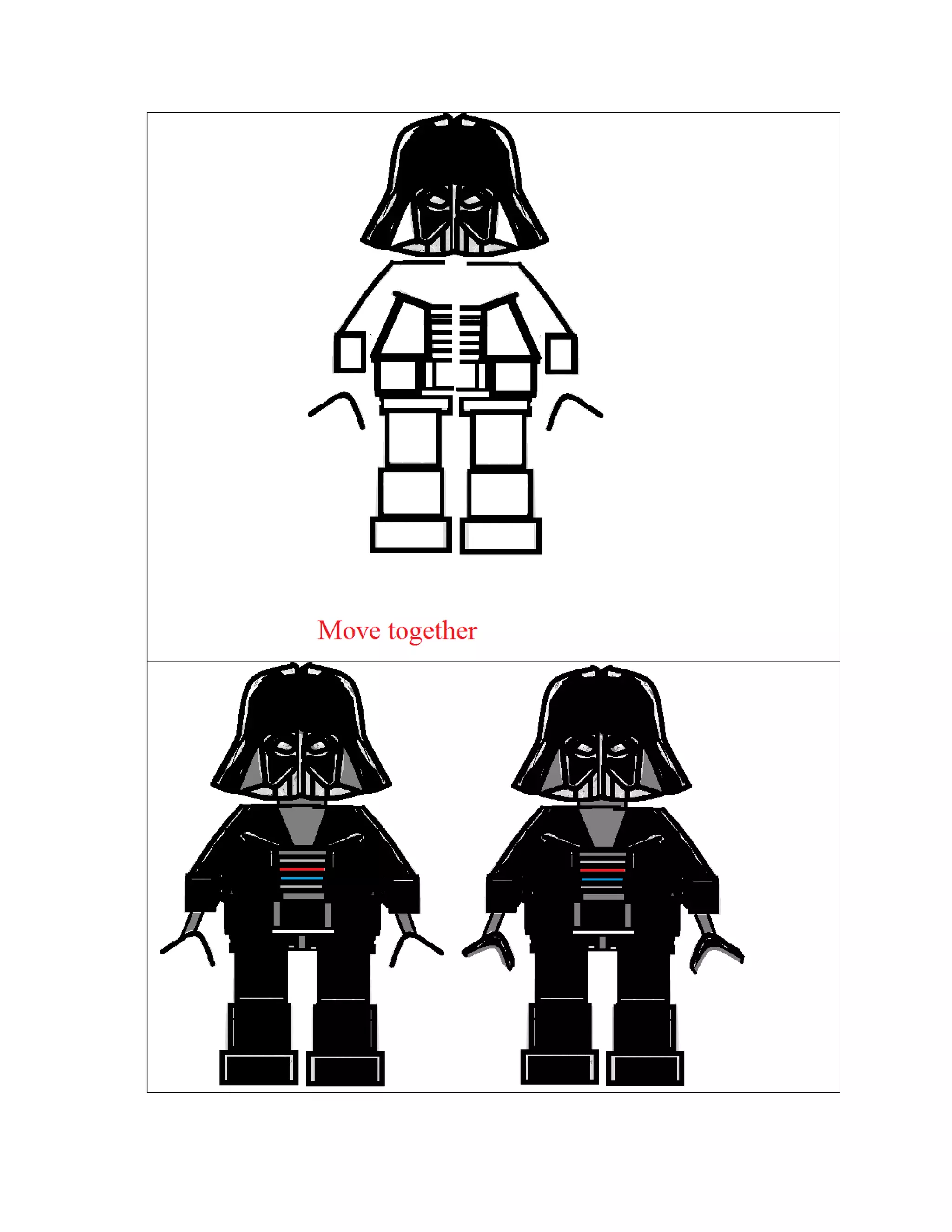

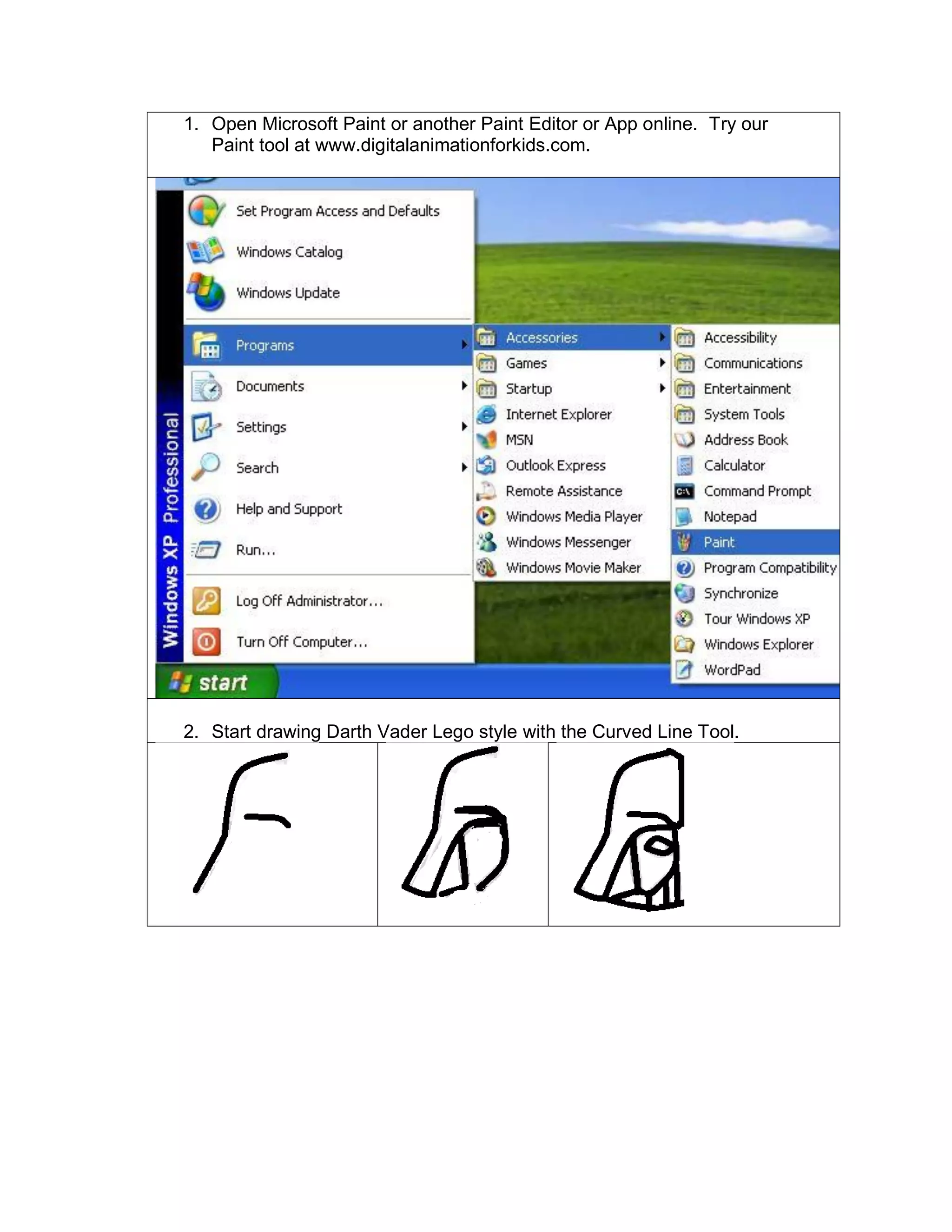
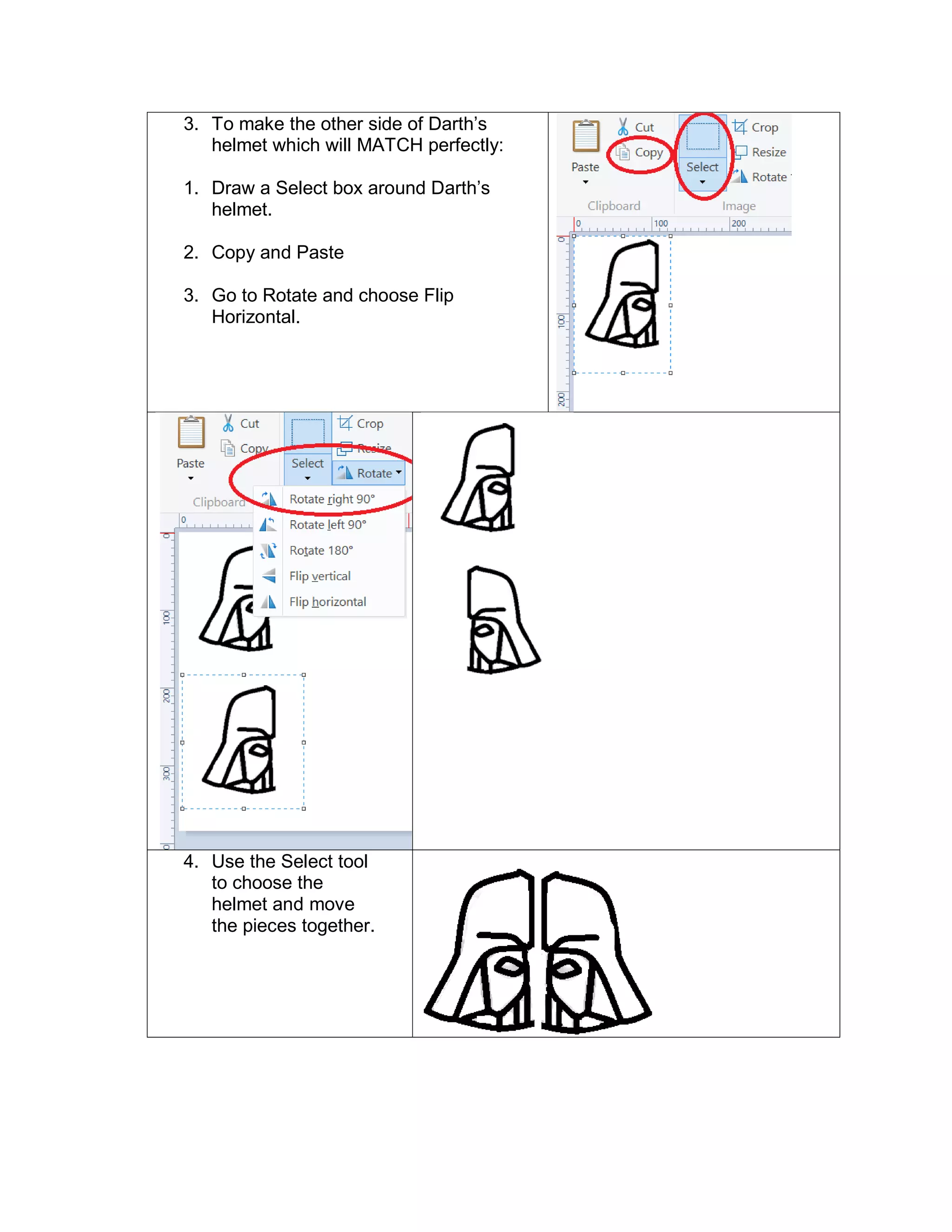
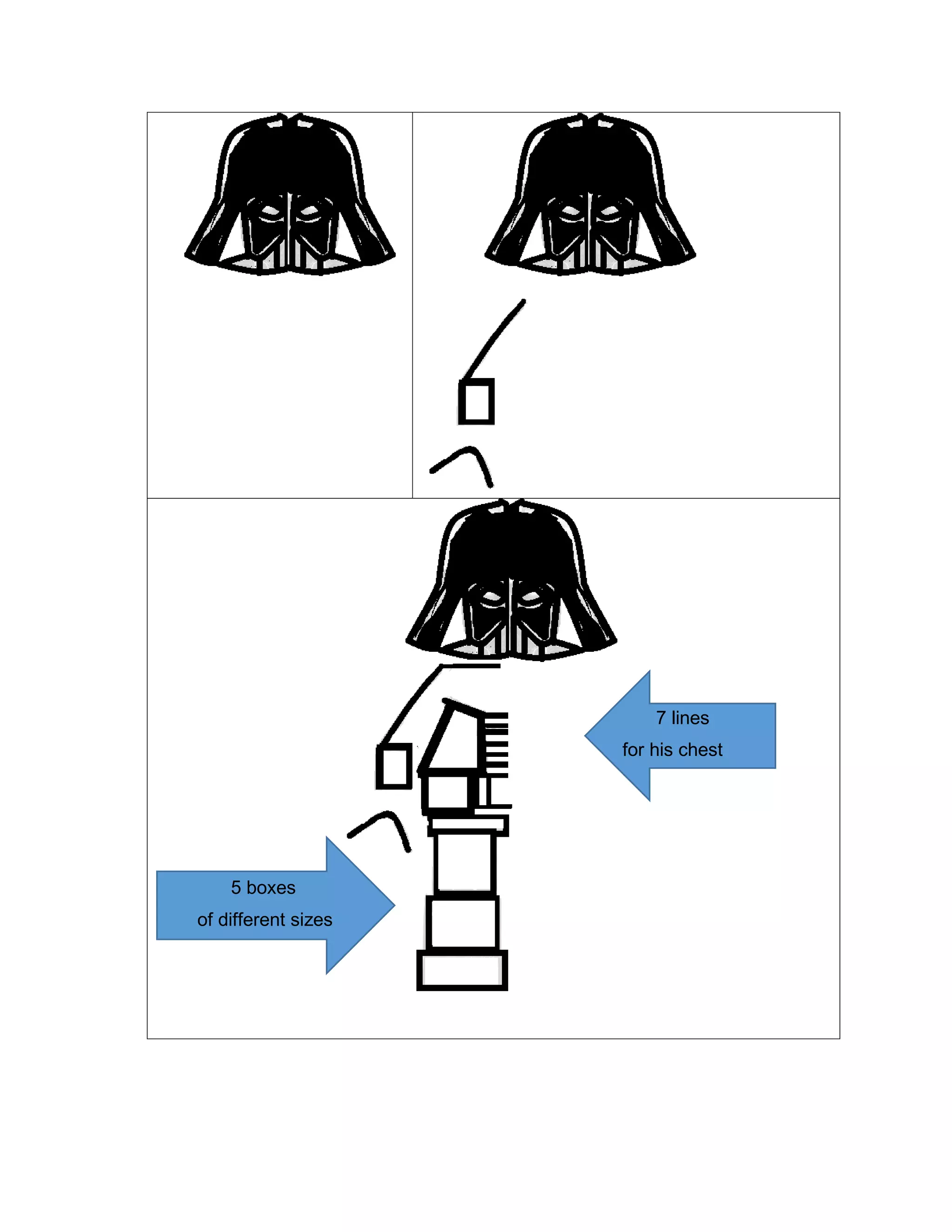
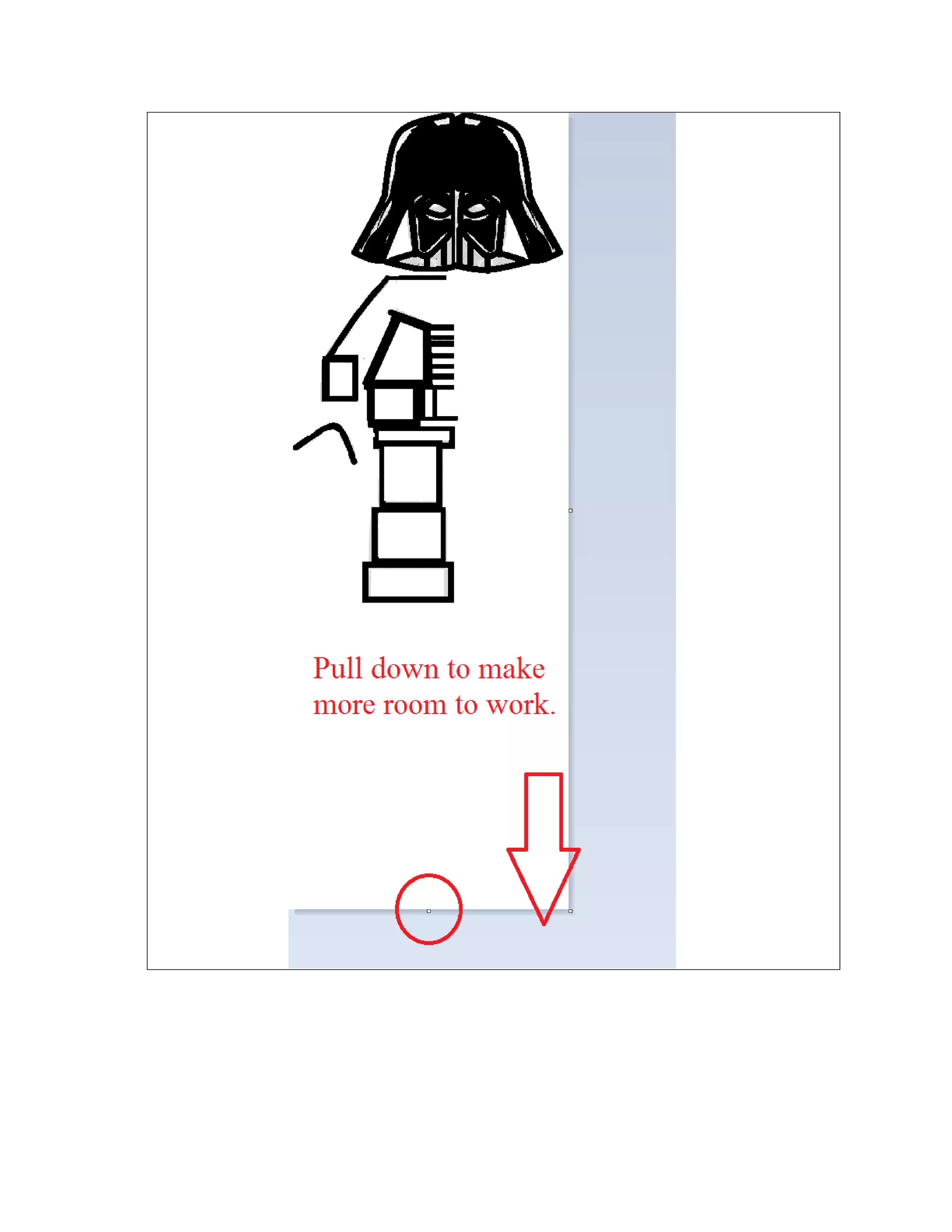
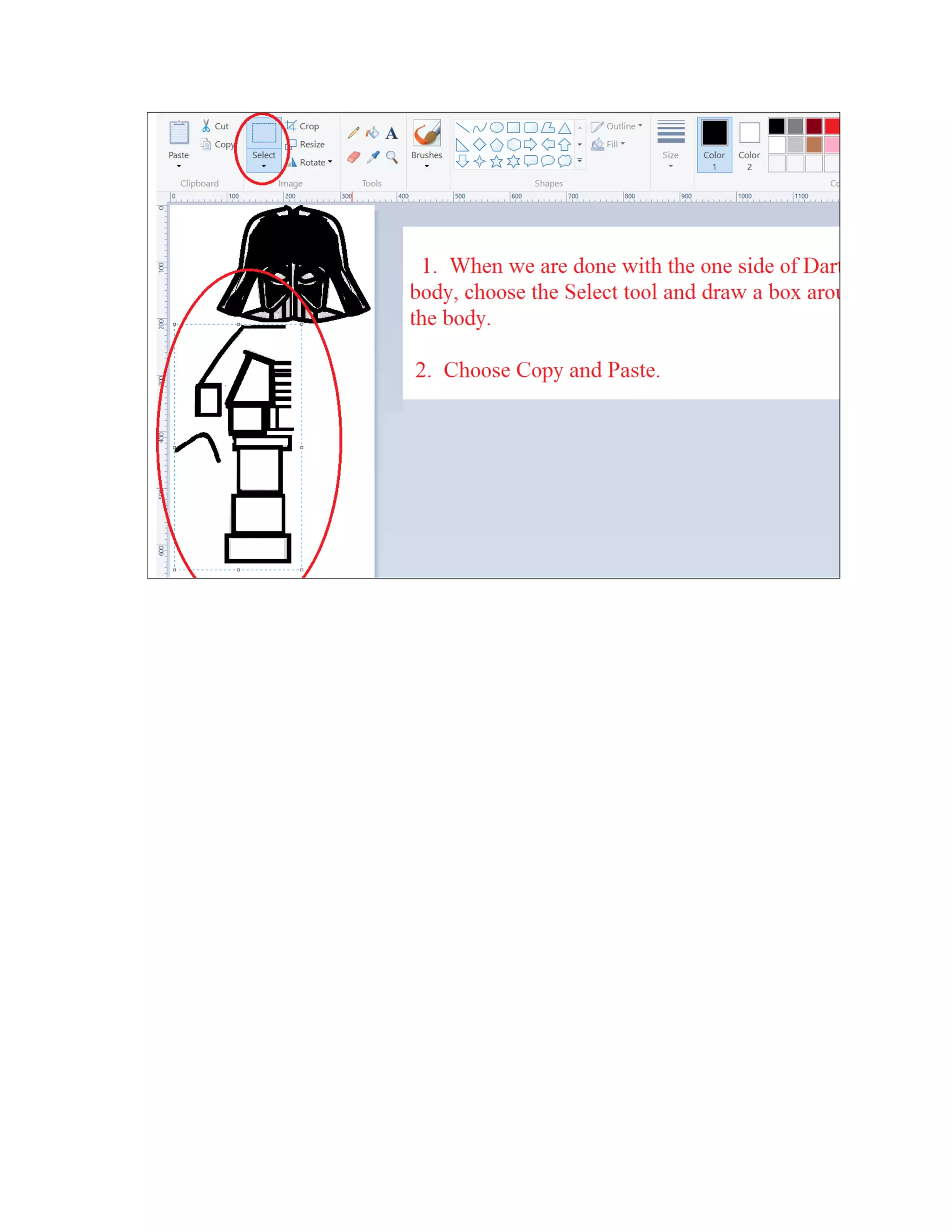
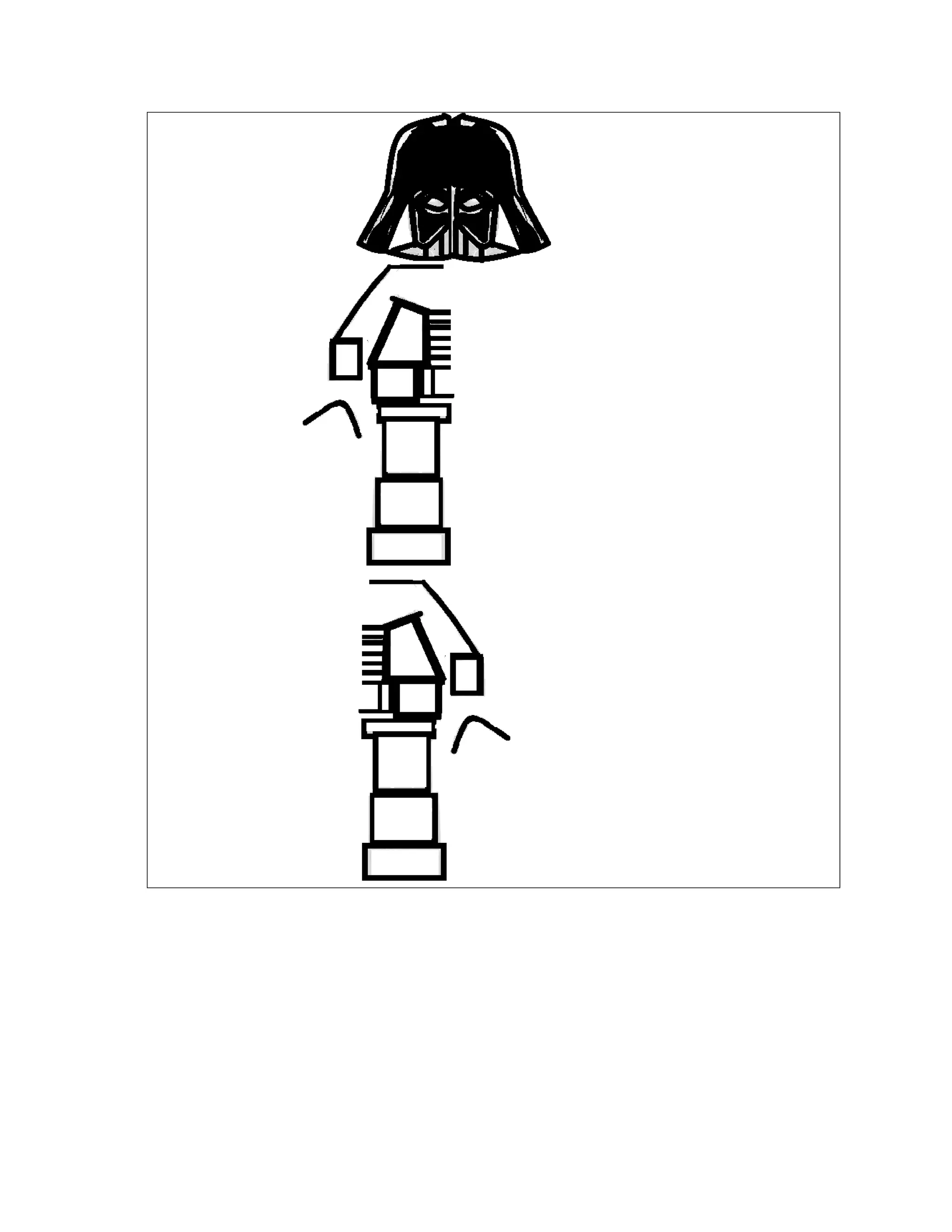
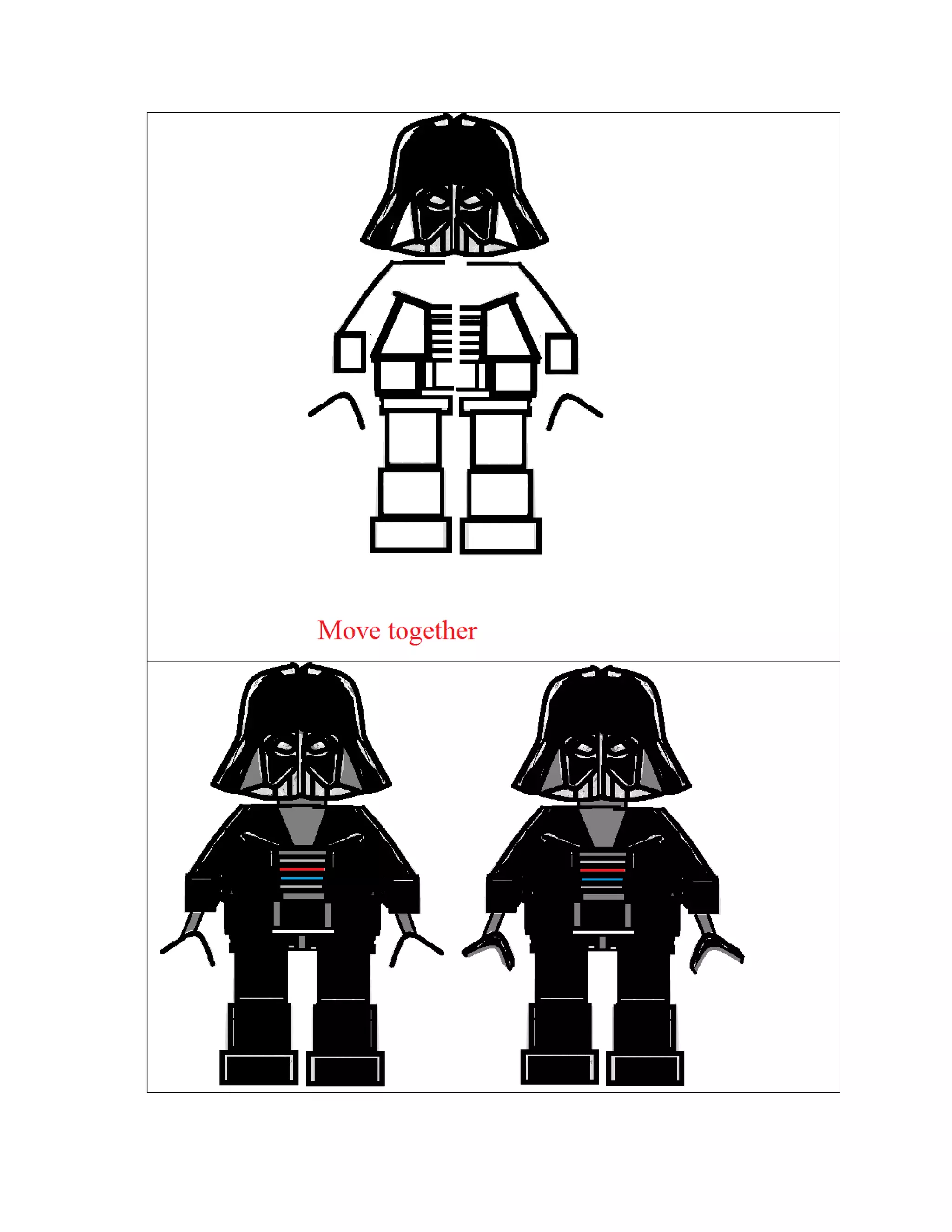
This document provides a step-by-step guide to drawing a Lego-style Darth Vader using a paint application. It includes instructions on using tools like the curved line tool, select box, copy-paste, and rotate. Additionally, it mentions creating shapes for his helmet and chest.