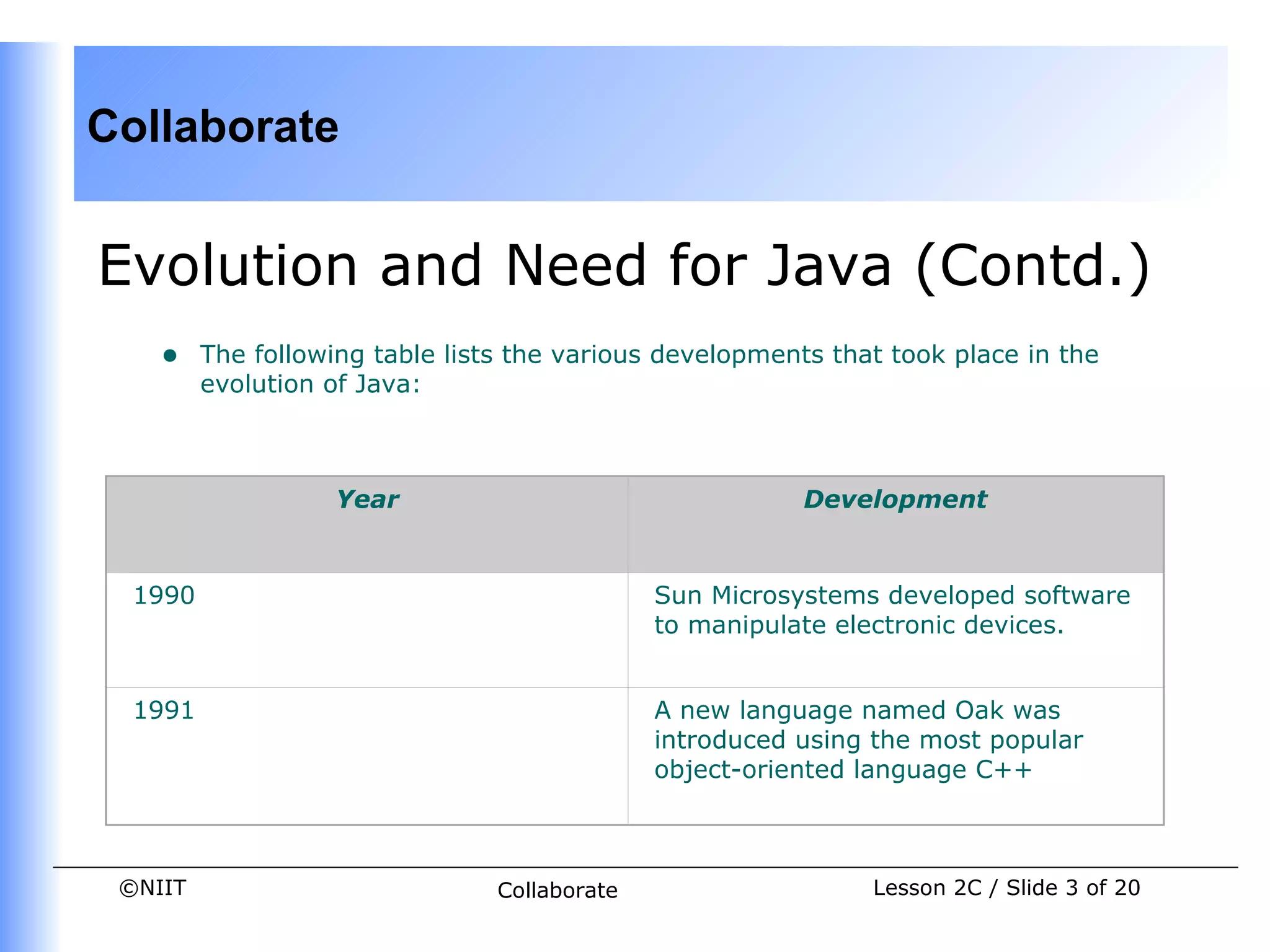
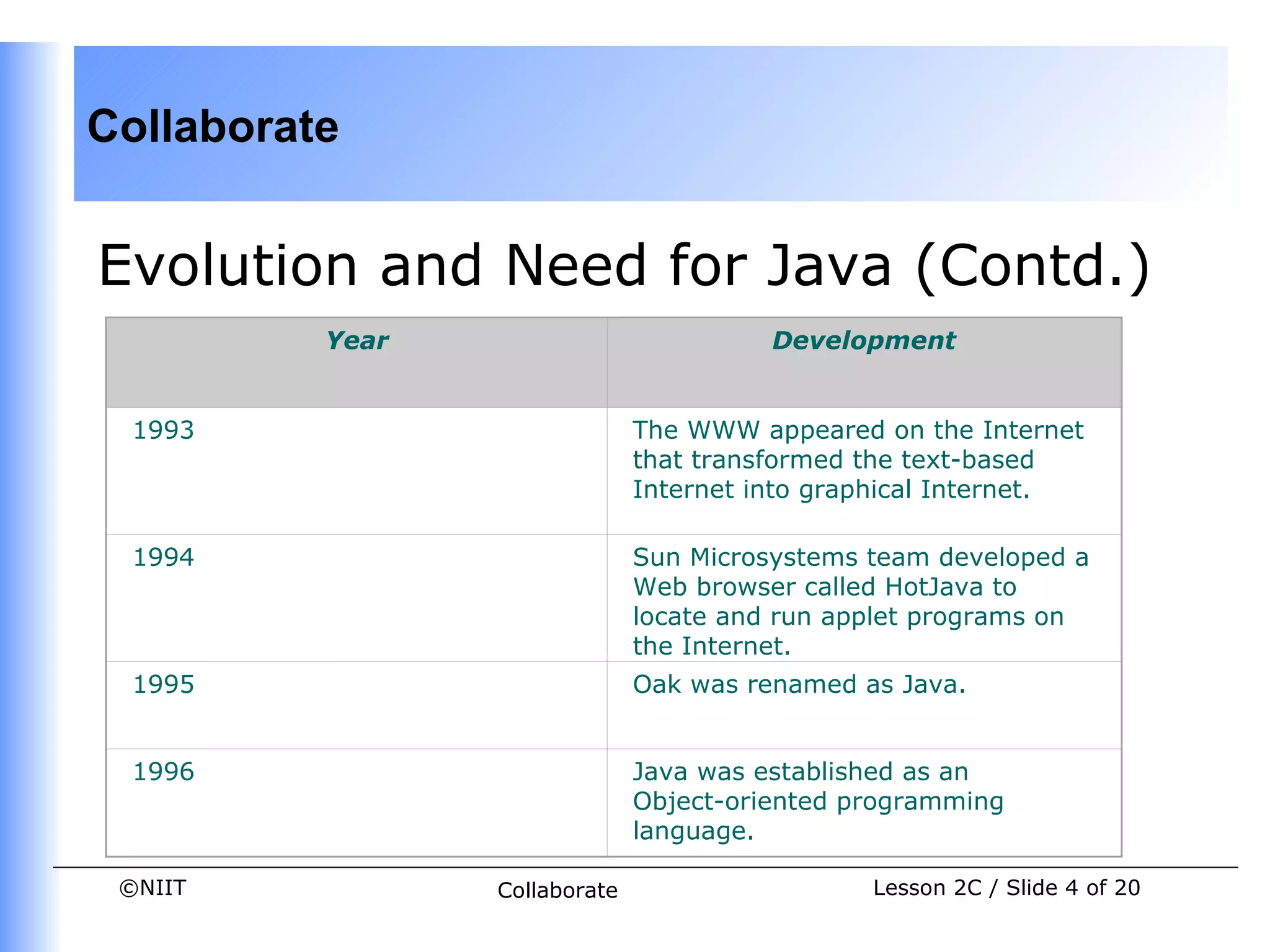
- Java was developed by Sun Microsystems in 1991 as a portable language that could run on different platforms. It was initially called Oak but later renamed to Java.
- The Java Virtual Machine (JVM) performs garbage collection to free memory from objects that are no longer in use. Different approaches like reference counting and tracing are used to detect garbage objects.
- The CLASSPATH environment variable instructs the JVM on finding classes. It can be set to include classpaths when using Java tools like java, javac, and javadoc.

![Collaborate
FAQs (Contd.)
• What will happen if the data type of a variable and the value assigned to the
variable are different?
If the data type of a variable and the value assigned to the variable are
different then compilation error occurs. The following code shows assigning a
character value to an integer variable:
class datatype{
public static void main(String a[])
{
int x= 'b';
System.out.print(x);
}
}
In the preceding code, the ASCII value of the character b is displayed as 98.
©NIIT Collaborate Lesson 2C / Slide 15 of 20](https://image.slidesharecdn.com/dacj-1-2c-120518023031-phpapp02/75/Dacj-1-2-c-15-2048.jpg)
![Collaborate
FAQs (Contd.)
Similarly, if you assign a float or a double value to a character variable, an error
message is displayed.
The following code shows assigning a double value to a character variable:
class datatype{
public static void main(String a[])
{
char x= 5.5;
System.out.print(x);
}
}
Java is a strongly typed language and it allows the values of the specific data
types, which are compatible with the type of variable.
©NIIT Collaborate Lesson 2C / Slide 16 of 20](https://image.slidesharecdn.com/dacj-1-2c-120518023031-phpapp02/75/Dacj-1-2-c-16-2048.jpg)