Cybersecurity Compliance can Make or Break Your Business - DigiCert - Symantec
•
1 like•251 views
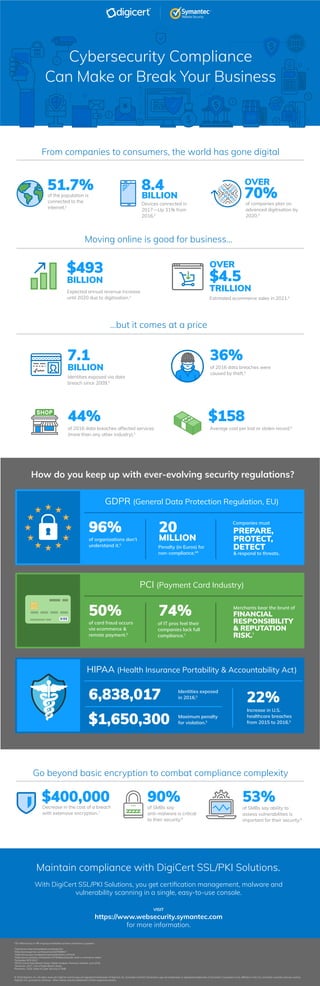
Over 70% of organizations are struggling to keep up with evolving security regulations as digitization increases connectivity and online commerce. Advanced encryption solutions and comprehensive compliance management are necessary to avoid the substantial penalties for non-compliance, which include fines up to 20 million Euros or 4% of annual global revenue. Emerging technologies connecting more devices and expanding ecommerce are driving exponential data growth and new compliance challenges for companies in protecting consumer information regulated by standards like GDPR, PCI, and HIPAA.
Report
Share
Report
Share
Download to read offline
Recommended
Detecting Frauds and Identifying Security Challenge | by Money2Conf

The Money 2.0 Conference dives into the latest market trends, enterprise risk management strategies, regulatory changes, and FinTech developments in the rapidly-evolving finance and insurance landscape. A three-day conference, it will delve into crucial topics such as the role of blockchain in banking, cybersecurity, digital forensics, spam identification; it will also review investments in emerging markets, money scam and fraud detection, retirement savings, and much more.
Listen to top-notch speakers from well-known organizations who will share their valuable insights and break down the latest developments so that you learn how to manage and grow your wealth in a secure manner! Join us on 18th-20th March 2022 in Dubai, UAE and on April 11th-13th 2022 in Las Vegas, USA.
2016 Cyber Security Breaches Survey for the UK

PIB Insurance Brokers is proud to present our report summarising the 2016 Cyber Security Breaches Survey for the United Kingdom, commissioned by the Department for Culture, Media & Sport as part of the National Cyber Security Programme.
The State of FIDO

Andrew Shikiar, Executive Director & CMO of the FIDO Alliance outlines what FIDO has achieved in the last 7 years, how the market is adopting FIDO, and new expanded work areas focusing on identity verification and binding and the Internet of Things.
Opening Keynote (Identity Live Berlin 2018)

Welcome and Opening Keynote - Michael Vaeth, Hermann Wimmer and Steve Ferris of ForgeRock
Cryptocurrency Scams | How Do You Protect Yourself?

Learn about the different types of cryptocurrency scams and frauds and join the Money 2.0 Conference as it reviews the entire landscape in this presentation. In the end, you’ll know how you can keep yourself safe from fake spammers while investing in cryptocurrencies.
Customer Safeguarding, Fraud and GDPR: Manah Khalil

Manah Khalil's presentation at ForgeRock Identity Live in Austin 2018
Identity Live in Austin Keynote 

Identity Live in Austin 2018 keynote presentation
Presenters:
Hermann Wimmer, Chief Revenue Officer & Global Field Operations, ForgeRock
Steve Ferris, SVP, Global Customer Success and Co-Founder, ForgeRock
Peter Barker, EVP & Chief Product Officer, ForgeRock
Recommended
Detecting Frauds and Identifying Security Challenge | by Money2Conf

The Money 2.0 Conference dives into the latest market trends, enterprise risk management strategies, regulatory changes, and FinTech developments in the rapidly-evolving finance and insurance landscape. A three-day conference, it will delve into crucial topics such as the role of blockchain in banking, cybersecurity, digital forensics, spam identification; it will also review investments in emerging markets, money scam and fraud detection, retirement savings, and much more.
Listen to top-notch speakers from well-known organizations who will share their valuable insights and break down the latest developments so that you learn how to manage and grow your wealth in a secure manner! Join us on 18th-20th March 2022 in Dubai, UAE and on April 11th-13th 2022 in Las Vegas, USA.
2016 Cyber Security Breaches Survey for the UK

PIB Insurance Brokers is proud to present our report summarising the 2016 Cyber Security Breaches Survey for the United Kingdom, commissioned by the Department for Culture, Media & Sport as part of the National Cyber Security Programme.
The State of FIDO

Andrew Shikiar, Executive Director & CMO of the FIDO Alliance outlines what FIDO has achieved in the last 7 years, how the market is adopting FIDO, and new expanded work areas focusing on identity verification and binding and the Internet of Things.
Opening Keynote (Identity Live Berlin 2018)

Welcome and Opening Keynote - Michael Vaeth, Hermann Wimmer and Steve Ferris of ForgeRock
Cryptocurrency Scams | How Do You Protect Yourself?

Learn about the different types of cryptocurrency scams and frauds and join the Money 2.0 Conference as it reviews the entire landscape in this presentation. In the end, you’ll know how you can keep yourself safe from fake spammers while investing in cryptocurrencies.
Customer Safeguarding, Fraud and GDPR: Manah Khalil

Manah Khalil's presentation at ForgeRock Identity Live in Austin 2018
Identity Live in Austin Keynote 

Identity Live in Austin 2018 keynote presentation
Presenters:
Hermann Wimmer, Chief Revenue Officer & Global Field Operations, ForgeRock
Steve Ferris, SVP, Global Customer Success and Co-Founder, ForgeRock
Peter Barker, EVP & Chief Product Officer, ForgeRock
The Road to Intelligent Authentication Journeys

The pressure is on. You need to build a great customer login experience that is secure but doesn’t burden your customers with complicated password requirements. But wait, there’s more – you also need to personalize the login experience and provide metrics back to the business. Legacy authentication has you boxed in. What are you to do? Solutions like multi-factor authentication (MFA) are replacing traditional login methods but its limitations are often static and offer up inconsistent customer experiences, leading to abandonment. Organizations need an intelligent authentication approach that strikes a balance between usability, security, and customer choice. In this webcast you will learn what Intelligent Authentication is and how it enables you to: Easily configure, measure, and adjust login journeys using digital signals including device, contextual, behavioral, user choice, and risk-based factors Leverage user login analytics to increase user adoption rates, and improve the customer experience Automatically redirect suspicious users for further monitoring Quickly consume out-of-the-box authenticators, utilize existing authenticators, and integrate with cyber security solutions — all in one place
Digital Identity In Government

Presented at GSMA Mobile Connect + FIDO Alliance: The Future of Strong Authentication
By: Alastair Treharne,Digital Identity Advisory, UK Cabinet Office
Current Trends Related to Mobile Network Operators & FIDO SCA Adoption

Presented at GSMA Mobile Connect + FIDO Alliance: The Future of Strong Authentication
By: Walter Beisheim,Chief Business Development Officer, Nok Nok Labs
Detecting Wire Fraud in Real-Time

Faster payments mean higher risk for fraud, especially through Business Email Compromise (BEC). Learn how to prevent fraudulent Wire transfers from identification to intervention.
With Problematic Car Thefts Increasing, MicroTRAK's AutoTRAK GPS Will Be the ...

DALLAS--(BUSINESS WIRE)--April 21, 2005--Every 27 seconds, a motor vehicle is stolen in the United S...
Global CCISO Forum 2018 | Ondrej Krehel | The Era of Cyber Extortion and Rans...

Global CCISO Forum
Ondrej Krehel | The Era of Cyber Extortion and Ransomware for EC Council
Applying Innovative Tools for GDPR Success

The GDPR's enforcement date is finally around the corner: May 25th. Have you successfully conceived of this groundbreaking EU regulation as a business opportunity? Have you addressed the challenges of both compliance and customer trust in a more comprehensive fashion? In this webcast, ForgeRock experts Nick Caley, VP of Financial and Regulatory, and Eve Maler, VP of Innovation and Emerging Technology, and Carlos Scott, Digital Risk Consultant will:
Discuss the GDPR in the context of regulatory compliance, digital innovation, and "ripped from the headlines" tensions in consumer trust and the personal data economy
Describe important privacy, consent, and trust innovations made in recent times, including in the standards world (OAuth, UMA, and more)
Demonstrate capabilities of the ForgeRock Identity Platform that address GDPR requirements, including a Profile and Privacy Management dashboard
2020 i gaming report webinar 

Join iovation in partnership with Clarion Events, for our iGaming Report Highlights Webinar, featuring product expert Angie White. She will review key takeaways from the 2020 iGaming industry report, forecast how these trends will impact both gambling operators and platform providers and answer all of your related questions.
Key topics:
Top iGaming industry trends and market threats
Growth in bonus abuse and other game abuses
Optimizing compliance
Winning in a mobile-first market
Expediting player onboarding
The Value of User and Data Centricity Beyond IoT Devices: Stein Myrseth and G...

Presented by Stein Myrseth, Senior Technology Solutions Director of ForgeRock and Gerhard Zehethofer, VP or Industries (IOT & Manufacturing) present at Identity Live in Austin in 2018
AML Transaction Monitoring Tuning Webinar

Poorly defined thresholds have a number of key impacts on a bank’s operations and compliance departments. Often times, analysts spend considerable time investigating useless alerts which increases operational costs significantly and causes a delay in regulatory filings. Also, the absence of risk-focused thresholds may cause potential money laundering patterns to go un-detected which poses higher monitoring risk to the bank.
Learn how financial institutions can leverage advanced analytics techniques to improve the productivity of the rules by setting up appropriate thresholds. Our speaker will also discuss how to leverage automation techniques for alert investigation in order to reduce the effort spent on false positives, thereby giving more time for the investigations to focus on true suspicious activities.
Topics covered:
- Regulatory Implications
- Managing AML Risks and Emerging Typologies
- Developing Targeted Detection Scenarios
- Customer Segmentation/Population Groups
- Understanding Normal and Outliers
- Operational Improvement through automation
European Regulation And The Need For Strong Customer Authentication

Presented at GSMA Mobile Connect + FIDO Alliance: The Future of Strong Authentication
By: Alain Martin, CO-CHAIR FIDO EUROPE WG VP STRATEGIC PARTNERSHIPS , GEMALTO
The Insurance Digital Revolution Has a Fraud Problem

The rapid digitalization of the Insurance Industry has not only opened up access channels for customers, but also created targets for fraudsters. The time is now to protect your business from fraud as you convert to digital. In this webinar, we’ll analyze the 5 Strategic Approaches to Digital Optimization and Transformation in Insurance that Gartner laid out in their report and explore possible fraud threats that can arise as a result of such transformation.
Register today to learn more from us about:
- Combating fraud threats introduced by the move to digital, such as ghost broking
- Detecting and preventing growing account takeover
- Protecting the entire customer lifecycle
- How to arm your SIU to more effectively fight fraudulent claims
- Improve identity verification to reduce early term losses
Trust is Everything - The Future of Identity and the ForgeRock Platform (Iden...

Trust is Everything - The Future of Identity and the ForgeRock Platform - Peter Barker, ForgeRock
Preventing P2P Fraud with Aite Group

Only real-time fraud detection solutions can prevent Peer-to-Peer fraud. Aite Group and Guardian Analytics show you what to be concerned about and how to detect in real-time evolving attacks from fraudsters.
Tech stocks to buy - Top small cap tech stocks

Tech stocks to buy - Top small cap tech stocks
Security tech stocks, tech stocks to buy and top security stocks to buy news, links and free information.
Tech Stocks News Alert
Top Tech Stock News
Share Reductions, Core Business Growth and
New 3-5 Year Contract Recurring Revenue Stream
Product Partnership Increases
Potential For Significant Upward Share Movements
SOUTHERN ITS INTERNATIONAL, Inc.
(Stock Symbol: SITS)
Read The Southern ITS Tech Stocks To Buy Research Report
Partnership Agreement To Market, Sell and Operate Innovative New
GPS Electronic Monitoring and Tracking Ankle Bracelets.
Small Cap Tech Stock News Alert:
Southern ITS International partners with Emap, Inc. to commercialize their new innovative tracking and monitoring GPS tracking ankle bracelets for house arrest, parole, and other types of offenders that require monitoring.
Investing in Cybersecurity, 2020 outlook for Mexico

As part of the 2019 Global Ventures Summit being hosted at Tech Expo Guadalajara, we shared our outlook for cybersecurity entrepreneurship in the region
Same day ach bec fraud detection prevention webinar 3 1-18 

Detect ACH Business Email Compromise (BEC) with Machine Learning
Beware of Scam Artists - Recognize Them Before They Get You!

Scam artists are expected to steal over $2 billion in 2020, according to ScamSpotter.org. They invariably contact you via phone calls, text messages or email, pretend to be someone you trust (e.g. IRS, your Bank, or IT support), and create a sense of urgency for you to respond. Scammers are primarily out to get your personal information, credit card numbers, or your money.
I will be walking through a few common scamming scenarios and arm you with the top actions that you can take to avoid being defrauded. It would be enlightening to hear some of your stories too, to make this session interactive. Together, we will learn how to stay a step ahead of the scammers.
Accounting for Cyber Risks - How much does Cyber actually cost the Industry?

A presentation made to 2018 Asian Insurers’ CFO Summit
Global Cyber Security Overview | TechSci Research 

Simple Cyber Security Overview that provide you a simple way to understand the cyber security and their benefits. https://www.techsciresearch.com/
More Related Content
What's hot
The Road to Intelligent Authentication Journeys

The pressure is on. You need to build a great customer login experience that is secure but doesn’t burden your customers with complicated password requirements. But wait, there’s more – you also need to personalize the login experience and provide metrics back to the business. Legacy authentication has you boxed in. What are you to do? Solutions like multi-factor authentication (MFA) are replacing traditional login methods but its limitations are often static and offer up inconsistent customer experiences, leading to abandonment. Organizations need an intelligent authentication approach that strikes a balance between usability, security, and customer choice. In this webcast you will learn what Intelligent Authentication is and how it enables you to: Easily configure, measure, and adjust login journeys using digital signals including device, contextual, behavioral, user choice, and risk-based factors Leverage user login analytics to increase user adoption rates, and improve the customer experience Automatically redirect suspicious users for further monitoring Quickly consume out-of-the-box authenticators, utilize existing authenticators, and integrate with cyber security solutions — all in one place
Digital Identity In Government

Presented at GSMA Mobile Connect + FIDO Alliance: The Future of Strong Authentication
By: Alastair Treharne,Digital Identity Advisory, UK Cabinet Office
Current Trends Related to Mobile Network Operators & FIDO SCA Adoption

Presented at GSMA Mobile Connect + FIDO Alliance: The Future of Strong Authentication
By: Walter Beisheim,Chief Business Development Officer, Nok Nok Labs
Detecting Wire Fraud in Real-Time

Faster payments mean higher risk for fraud, especially through Business Email Compromise (BEC). Learn how to prevent fraudulent Wire transfers from identification to intervention.
With Problematic Car Thefts Increasing, MicroTRAK's AutoTRAK GPS Will Be the ...

DALLAS--(BUSINESS WIRE)--April 21, 2005--Every 27 seconds, a motor vehicle is stolen in the United S...
Global CCISO Forum 2018 | Ondrej Krehel | The Era of Cyber Extortion and Rans...

Global CCISO Forum
Ondrej Krehel | The Era of Cyber Extortion and Ransomware for EC Council
Applying Innovative Tools for GDPR Success

The GDPR's enforcement date is finally around the corner: May 25th. Have you successfully conceived of this groundbreaking EU regulation as a business opportunity? Have you addressed the challenges of both compliance and customer trust in a more comprehensive fashion? In this webcast, ForgeRock experts Nick Caley, VP of Financial and Regulatory, and Eve Maler, VP of Innovation and Emerging Technology, and Carlos Scott, Digital Risk Consultant will:
Discuss the GDPR in the context of regulatory compliance, digital innovation, and "ripped from the headlines" tensions in consumer trust and the personal data economy
Describe important privacy, consent, and trust innovations made in recent times, including in the standards world (OAuth, UMA, and more)
Demonstrate capabilities of the ForgeRock Identity Platform that address GDPR requirements, including a Profile and Privacy Management dashboard
2020 i gaming report webinar 

Join iovation in partnership with Clarion Events, for our iGaming Report Highlights Webinar, featuring product expert Angie White. She will review key takeaways from the 2020 iGaming industry report, forecast how these trends will impact both gambling operators and platform providers and answer all of your related questions.
Key topics:
Top iGaming industry trends and market threats
Growth in bonus abuse and other game abuses
Optimizing compliance
Winning in a mobile-first market
Expediting player onboarding
The Value of User and Data Centricity Beyond IoT Devices: Stein Myrseth and G...

Presented by Stein Myrseth, Senior Technology Solutions Director of ForgeRock and Gerhard Zehethofer, VP or Industries (IOT & Manufacturing) present at Identity Live in Austin in 2018
AML Transaction Monitoring Tuning Webinar

Poorly defined thresholds have a number of key impacts on a bank’s operations and compliance departments. Often times, analysts spend considerable time investigating useless alerts which increases operational costs significantly and causes a delay in regulatory filings. Also, the absence of risk-focused thresholds may cause potential money laundering patterns to go un-detected which poses higher monitoring risk to the bank.
Learn how financial institutions can leverage advanced analytics techniques to improve the productivity of the rules by setting up appropriate thresholds. Our speaker will also discuss how to leverage automation techniques for alert investigation in order to reduce the effort spent on false positives, thereby giving more time for the investigations to focus on true suspicious activities.
Topics covered:
- Regulatory Implications
- Managing AML Risks and Emerging Typologies
- Developing Targeted Detection Scenarios
- Customer Segmentation/Population Groups
- Understanding Normal and Outliers
- Operational Improvement through automation
European Regulation And The Need For Strong Customer Authentication

Presented at GSMA Mobile Connect + FIDO Alliance: The Future of Strong Authentication
By: Alain Martin, CO-CHAIR FIDO EUROPE WG VP STRATEGIC PARTNERSHIPS , GEMALTO
The Insurance Digital Revolution Has a Fraud Problem

The rapid digitalization of the Insurance Industry has not only opened up access channels for customers, but also created targets for fraudsters. The time is now to protect your business from fraud as you convert to digital. In this webinar, we’ll analyze the 5 Strategic Approaches to Digital Optimization and Transformation in Insurance that Gartner laid out in their report and explore possible fraud threats that can arise as a result of such transformation.
Register today to learn more from us about:
- Combating fraud threats introduced by the move to digital, such as ghost broking
- Detecting and preventing growing account takeover
- Protecting the entire customer lifecycle
- How to arm your SIU to more effectively fight fraudulent claims
- Improve identity verification to reduce early term losses
Trust is Everything - The Future of Identity and the ForgeRock Platform (Iden...

Trust is Everything - The Future of Identity and the ForgeRock Platform - Peter Barker, ForgeRock
Preventing P2P Fraud with Aite Group

Only real-time fraud detection solutions can prevent Peer-to-Peer fraud. Aite Group and Guardian Analytics show you what to be concerned about and how to detect in real-time evolving attacks from fraudsters.
Tech stocks to buy - Top small cap tech stocks

Tech stocks to buy - Top small cap tech stocks
Security tech stocks, tech stocks to buy and top security stocks to buy news, links and free information.
Tech Stocks News Alert
Top Tech Stock News
Share Reductions, Core Business Growth and
New 3-5 Year Contract Recurring Revenue Stream
Product Partnership Increases
Potential For Significant Upward Share Movements
SOUTHERN ITS INTERNATIONAL, Inc.
(Stock Symbol: SITS)
Read The Southern ITS Tech Stocks To Buy Research Report
Partnership Agreement To Market, Sell and Operate Innovative New
GPS Electronic Monitoring and Tracking Ankle Bracelets.
Small Cap Tech Stock News Alert:
Southern ITS International partners with Emap, Inc. to commercialize their new innovative tracking and monitoring GPS tracking ankle bracelets for house arrest, parole, and other types of offenders that require monitoring.
Investing in Cybersecurity, 2020 outlook for Mexico

As part of the 2019 Global Ventures Summit being hosted at Tech Expo Guadalajara, we shared our outlook for cybersecurity entrepreneurship in the region
Same day ach bec fraud detection prevention webinar 3 1-18 

Detect ACH Business Email Compromise (BEC) with Machine Learning
Beware of Scam Artists - Recognize Them Before They Get You!

Scam artists are expected to steal over $2 billion in 2020, according to ScamSpotter.org. They invariably contact you via phone calls, text messages or email, pretend to be someone you trust (e.g. IRS, your Bank, or IT support), and create a sense of urgency for you to respond. Scammers are primarily out to get your personal information, credit card numbers, or your money.
I will be walking through a few common scamming scenarios and arm you with the top actions that you can take to avoid being defrauded. It would be enlightening to hear some of your stories too, to make this session interactive. Together, we will learn how to stay a step ahead of the scammers.
What's hot (20)
Current Trends Related to Mobile Network Operators & FIDO SCA Adoption

Current Trends Related to Mobile Network Operators & FIDO SCA Adoption
With Problematic Car Thefts Increasing, MicroTRAK's AutoTRAK GPS Will Be the ...

With Problematic Car Thefts Increasing, MicroTRAK's AutoTRAK GPS Will Be the ...
Global CCISO Forum 2018 | Ondrej Krehel | The Era of Cyber Extortion and Rans...

Global CCISO Forum 2018 | Ondrej Krehel | The Era of Cyber Extortion and Rans...
The Value of User and Data Centricity Beyond IoT Devices: Stein Myrseth and G...

The Value of User and Data Centricity Beyond IoT Devices: Stein Myrseth and G...
European Regulation And The Need For Strong Customer Authentication

European Regulation And The Need For Strong Customer Authentication
The Insurance Digital Revolution Has a Fraud Problem

The Insurance Digital Revolution Has a Fraud Problem
Trust is Everything - The Future of Identity and the ForgeRock Platform (Iden...

Trust is Everything - The Future of Identity and the ForgeRock Platform (Iden...
Investing in Cybersecurity, 2020 outlook for Mexico

Investing in Cybersecurity, 2020 outlook for Mexico
Same day ach bec fraud detection prevention webinar 3 1-18 

Same day ach bec fraud detection prevention webinar 3 1-18
Beware of Scam Artists - Recognize Them Before They Get You!

Beware of Scam Artists - Recognize Them Before They Get You!
Similar to Cybersecurity Compliance can Make or Break Your Business - DigiCert - Symantec
Accounting for Cyber Risks - How much does Cyber actually cost the Industry?

A presentation made to 2018 Asian Insurers’ CFO Summit
Global Cyber Security Overview | TechSci Research 

Simple Cyber Security Overview that provide you a simple way to understand the cyber security and their benefits. https://www.techsciresearch.com/
Global Cybersecurity Market (2017 - 2022) 

The global cybersecurity market is expected to witness high adoption, owing to rapid digitalization, higher spending on information security, and the advent of 5G. Various industrial and commercial sectors are implementing cybersecurity solutions to safeguard their data. The market is anticipated to expand at a compound annual growth rate (CAGR) of 11.6% during the period of 2017 to 2022. Read More: https://www.researchonglobalmarkets.com/global-cybersecurity-market.html
5 Security Trends to Watch in 2020

Personal and corporate privacy continue encoding away as cyber attacks and data hackers become more common.
Digital Transformation & Cloud Profitability

A quick view about Digital Transformation and what's happening with Industries across the globe.
A guidance to IT Channel to accelerate Cloud Profitability with valuable resources for download.
Cybersecurity 2020 the biggest threats to watch out for

Read our new blog about Cybersecurity threats and ways to overcome them in 2020.
Cybersecurity in the Cloud: Safer Than You Think

Listen to our podcast on cybersecurity in the cloud: https://ap.pn/2K0dQhS
The explosion of cloud computing has connected more people than anyone ever imagined. But the massive numbers of companies migrating to the cloud has also amplified the urgency of data security and regulatory compliance as well.
The skeptics get snagged on lingering assumptions that cloud technology is insecure. But it’s hard to be skeptical when the best cloud vendors may be more expert at cybersecurity than many inhouse IT administrators.
Perhaps the trust gap is perpetuated by the numerous data breach horror stories that litter the Web. But don’t let the cyber smash and grab headlines stop you from giving cloud the benefit of the doubt.
In our thought-provoking podcast, Malcolm Ross sat down with Appian Chief Information Security Officer, Omesh Agam to take a fresh look at how to keep your data, applications and infrastructure secure in the cloud. Listen now: https://ap.pn/2K0dQhS
Towards the Next Generation Financial Crimes Platform - How Data, Analytics, ...

Towards the Next Generation Financial Crimes Platform - How Data, Analytics, & ML Are Transforming the Fight Against Fraud, AML & Cybersecurity -Nadeem Asghar
How AI is impacting digital identity security.pdf

AI is revolutionizing digital identity security by enhancing authentication methods, detecting anomalies, and preventing fraud with its ability to analyze vast data sets and recognize patterns accurately.
Website : https://vlinkinc-my.sharepoint.com/:w:/g/personal/vipul_bhardwaj_vlinkinfo_com/EaQPA2UFPuxKomhOXisVC40Bmj4Jvbu6Zx5XRvmCfNJMSQ?e=cjJXCt
Why is cyber security a disruption in the digital economy

As we enter the digital economy, companies will quickly realize that the differentiator in the digital economy is information and information being a valuable resource is subject to theft, hacking, phishing and a host of other issues which compromise a company’s ability to participate in the digital economy. Cybersecurity misfires compromise the trust of buyers and partners necessary to participate in the digital economy. It is up to every company to ensure that the information shared with them is protected to the best of their ability and proactively notify persons and organizations who entrust their information necessary to transact business (any personal identity information including but not limited to addresses, credit card information, social security numbers, account information, credit information, medical records, etc.) with any potential compromises which can yield harm to them by that information either being used maliciously or shared with others.
The digital economy is different than other versions of commerce because in the digital economy, information is the lifeblood of digital commerce that passes through the hands of many platforms involved in a digital event. Each of these platforms are an opportunity to wreak havoc on your well-intended but incomplete intents to protect the information contained within the network you control. In the digital economy, it is not only the network you control, but the platforms that touch the personal data entrusted to you as a means of enabling digital commerce, and several techniques have begun to emerge to protect personal information contained within your information domain and the domain of platforms participating in digital commerce.
Because the life blood of the digital economy is information, information hacked in the digital economy is akin to shrinkage in the legacy economy. Both are means to directly attack your bottom line, whether it is redirecting customers elsewhere because they don’t trust your privacy program, ransomware which makes your site or one of your partner platform sites dangerous to use or some other reason which challenges your ability to participate in the digital economy. Shrinking the potential market share because of information safety and security challenges is a disruption, making cyber-security a disruptive activity, particularly if it is not dealt with swiftly.
If your cyber-security program is focused entirely on protecting the information housed in your four walls, you have exposed yourself to problems you will have difficulty in identifying both the source and the entry point of these issues.
The Five Biggest Cyber Security Trends In 2022

Cyber security is evolving rapidly and is becoming one of today's most important technology areas. In 2022, we will see many new developments and advances. Here are some trends that will reshape the cyber security space over the next year.
Top 10 Cybersecurity Trends to Watch Out For in 2022

With the Digital revolution around all businesses, small or large, corporates, organizations and even governments are relying on computerized systems to manage their day-to-day activities and thus making cybersecurity a primary goal to safeguard data from various online attacks or any unauthorized access. Continuous change in technologies also implies a parallel shift in cybersecurity trends as news of data breach, ransomware and hacks become the norms. Here are the top cybersecurity trends for 2022.
The 10 Fastest Growing Cyber Security Companies of 2017

The 10 Fastest Growing Cyber Security Companies of 2017Insights success media and technology pvt ltd
The 10 Fastest Growing Cyber Security Companies of 2017Top cybersecurity trends to adapt in 2022

As a result of the pandemic's transition to remote work, companies have become more exposed to malicious assaults. To combat such attacks, you must keep a close eye on developing cybersecurity trends. The main cybersecurity trends for 2022 will be discussed in this article.
Read more: https://www.cigniti.com/blog/cybersecurity-trends-2022/
An Overview and Competitive Analysis of the One-Time Password (OTP) Market

This Frost & Sullivan report examines the proliferation of identity theft and data breaches caused by single-factor authentication or weak passwords, and describes how, to decrease the impact of threats, companies are integrating mobile OTP, OTP tokens, and USB tokens to protect network access and end users.
Department of Justice IT Sales Opportunities

Make your sales efforts more effective within DOJ as immixGroup’s Market Intelligence Consultant, Tom O’Keefe, provides you with an inside look at organizations, major initiatives, and key funded IT programs across the Department.
Similar to Cybersecurity Compliance can Make or Break Your Business - DigiCert - Symantec (20)
Accounting for Cyber Risks - How much does Cyber actually cost the Industry?

Accounting for Cyber Risks - How much does Cyber actually cost the Industry?
Cybersecurity 2020 the biggest threats to watch out for

Cybersecurity 2020 the biggest threats to watch out for
Towards the Next Generation Financial Crimes Platform - How Data, Analytics, ...

Towards the Next Generation Financial Crimes Platform - How Data, Analytics, ...
Why is cyber security a disruption in the digital economy

Why is cyber security a disruption in the digital economy
Top 10 Cybersecurity Trends to Watch Out For in 2022

Top 10 Cybersecurity Trends to Watch Out For in 2022
The 10 Fastest Growing Cyber Security Companies of 2017

The 10 Fastest Growing Cyber Security Companies of 2017
An Overview and Competitive Analysis of the One-Time Password (OTP) Market

An Overview and Competitive Analysis of the One-Time Password (OTP) Market
More from RapidSSLOnline.com
Tackle ERR_SSL_PROTOCOL_ERROR in Google Chrome

Step-by-step instructions for taking care of Chrome’s ERR_SSL_PROTOCOL_ERROR
Viewing SSL Certificate in Chrome | RapidSSLonline

Steps to view an SSL certificate in Chrome. Check your SSL certificate in Google Chrome for more details.
Compare GeoTrust True BusinessID SSL Data Sheet

Compare and understand the features of GeoTrust True BusinessID SSL certificate.
Introducing TLS 1.3 – The future of Encryption

RapidSSLonline explains about TLS 1.3 Encryption Mechanism for its implementation and official details.
GUIDE ON INSTALLING SSL CERTIFICATE ON IBM HTTP SERVER

A COMPLETE GUIDE AND RESOURCES TO INSTALL AN SSL CERTIFICATE ON IBM HTTP SERVER BY RAPIDSSLONLINE.
Adobe Connect on-premise SSL Guide

This is supposed to be a complete SSL configuration guide for Connect on-premise installs of version 9.0
and higher.
How to Move SSL Certificate from Windows Server to Another Windows Server

Guide for moving SSL certificate from on windows server to another windows server in few steps.
Symmetric and Asymmetric Encryption

Fundamental Differences between Symmetric and Asymmetric Encryption explained by RapidSSLonline.
SSL / TLS Validation | CASecurity.org | RapidSSLonline

It's moment to have the better knowledge about SSL or TLS Certificate validation methods.
Geek Guide: Apache Web Servers and SSL Authentication

GeoTrust sponsored exclusive Geek Guide for Apache Web Servers and SSL authentication. Download Now!
All About SSL/TLS

Thanks to Symantec. Learn how SSL/TLS certificates work—and the benefits of better website security.
A Complete RapidSSL Guide on Securing Online Business with SSL Certificate

Being an owner of the website or e-commerce store, you must know everything about an SSL certificate to protect data on a web,
Google Chrome 56 What You Need to Know?

Google Chrome 56 changes regarding HTTPS or SSL Certificates. Thanks to Symantec!!
The Hidden Costs of SelfSigned SSL Certificates 

Thawte CA has researched on estimate hidden costs of selfsigned SSL certificates. Read it before you go for selfsigned SSL.
2016 Symantec Internet Security Threat Report

2016 Symantec Internet Security Threat Report to dive into big data of website security.
How Does The Wildcard SSL Work?

A Research on How Does The Wildcard SSL work? & What Are The Key Gains in Wildcard SSL Security?
Uncover threats and protect your organization

Ensure your organization data as secured through possible vulnerabilities. There are
ways to close the gaps in your
defenses and secure your organization
against dangerous advanced threats.
A New Zero-Day Vulnerability Discovered Every Week in 2015

In 2015, 54 zero-day vulnerabilities were discovered as Per Recent Symantec Threat Report 2016.
Symantec 2016 Security Predictions - Looking ahead

Symantec 2016 Security Predictions to Improve The Better Security Elements and Stay Safe on the Internet.
More from RapidSSLOnline.com (20)
Viewing SSL Certificate in Chrome | RapidSSLonline

Viewing SSL Certificate in Chrome | RapidSSLonline
GUIDE ON INSTALLING SSL CERTIFICATE ON IBM HTTP SERVER

GUIDE ON INSTALLING SSL CERTIFICATE ON IBM HTTP SERVER
How to Move SSL Certificate from Windows Server to Another Windows Server

How to Move SSL Certificate from Windows Server to Another Windows Server
SSL / TLS Validation | CASecurity.org | RapidSSLonline

SSL / TLS Validation | CASecurity.org | RapidSSLonline
Geek Guide: Apache Web Servers and SSL Authentication

Geek Guide: Apache Web Servers and SSL Authentication
A Complete RapidSSL Guide on Securing Online Business with SSL Certificate

A Complete RapidSSL Guide on Securing Online Business with SSL Certificate
A New Zero-Day Vulnerability Discovered Every Week in 2015

A New Zero-Day Vulnerability Discovered Every Week in 2015
Symantec 2016 Security Predictions - Looking ahead

Symantec 2016 Security Predictions - Looking ahead
Recently uploaded
History+of+E-commerce+Development+in+China-www.cfye-commerce.shop

History+of+E-commerce+Development+in+China-www.cfye-commerce.shop
Multi-cluster Kubernetes Networking- Patterns, Projects and Guidelines

Talk presented at Kubernetes Community Day, New York, May 2024.
Technical summary of Multi-Cluster Kubernetes Networking architectures with focus on 4 key topics.
1) Key patterns for Multi-cluster architectures
2) Architectural comparison of several OSS/ CNCF projects to address these patterns
3) Evolution trends for the APIs of these projects
4) Some design recommendations & guidelines for adopting/ deploying these solutions.
The+Prospects+of+E-Commerce+in+China.pptx

The Prospects of E-commerce in China,www.cfye-commerce.shop
1.Wireless Communication System_Wireless communication is a broad term that i...

Wireless communication involves the transmission of information over a distance without the help of wires, cables or any other forms of electrical conductors.
Wireless communication is a broad term that incorporates all procedures and forms of connecting and communicating between two or more devices using a wireless signal through wireless communication technologies and devices.
Features of Wireless Communication
The evolution of wireless technology has brought many advancements with its effective features.
The transmitted distance can be anywhere between a few meters (for example, a television's remote control) and thousands of kilometers (for example, radio communication).
Wireless communication can be used for cellular telephony, wireless access to the internet, wireless home networking, and so on.
test test test test testtest test testtest test testtest test testtest test ...

salamsasalamlamsalamsalamsalamsalamsalamsalamsalam
This 7-second Brain Wave Ritual Attracts Money To You.!

Discover the power of a simple 7-second brain wave ritual that can attract wealth and abundance into your life. By tapping into specific brain frequencies, this technique helps you manifest financial success effortlessly. Ready to transform your financial future? Try this powerful ritual and start attracting money today!
急速办(bedfordhire毕业证书)英国贝德福特大学毕业证成绩单原版一模一样

原版纸张【微信:741003700 】【(bedfordhire毕业证书)英国贝德福特大学毕业证成绩单】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
原版仿制(uob毕业证书)英国伯明翰大学毕业证本科学历证书原版一模一样

原版纸张【微信:741003700 】【(uob毕业证书)英国伯明翰大学毕业证】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
How to Use Contact Form 7 Like a Pro.pptx

Contact Form 7 is a popular plugins for WordPress. This is an introduction into its features and usage.
ER(Entity Relationship) Diagram for online shopping - TAE

https://bit.ly/3KACoyV
The ER diagram for the project is the foundation for the building of the database of the project. The properties, datatypes, and attributes are defined by the ER diagram.
1比1复刻(bath毕业证书)英国巴斯大学毕业证学位证原版一模一样

原版纸张【微信:741003700 】【(bath毕业证书)英国巴斯大学毕业证学位证】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
Recently uploaded (16)
History+of+E-commerce+Development+in+China-www.cfye-commerce.shop

History+of+E-commerce+Development+in+China-www.cfye-commerce.shop
Multi-cluster Kubernetes Networking- Patterns, Projects and Guidelines

Multi-cluster Kubernetes Networking- Patterns, Projects and Guidelines
1.Wireless Communication System_Wireless communication is a broad term that i...

1.Wireless Communication System_Wireless communication is a broad term that i...
test test test test testtest test testtest test testtest test testtest test ...

test test test test testtest test testtest test testtest test testtest test ...
This 7-second Brain Wave Ritual Attracts Money To You.!

This 7-second Brain Wave Ritual Attracts Money To You.!
guildmasters guide to ravnica Dungeons & Dragons 5...

guildmasters guide to ravnica Dungeons & Dragons 5...
Living-in-IT-era-Module-7-Imaging-and-Design-for-Social-Impact.pptx

Living-in-IT-era-Module-7-Imaging-and-Design-for-Social-Impact.pptx
ER(Entity Relationship) Diagram for online shopping - TAE

ER(Entity Relationship) Diagram for online shopping - TAE
Cybersecurity Compliance can Make or Break Your Business - DigiCert - Symantec
- 1. 8.4 BILLION OVER 70% How do you keep up with ever-evolving security regulations? Devices connected in 2017—Up 31% from 2016.2 $493 BILLION Expected annual revenue increase until 2020 due to digitisation.3 OVER $4.5 TRILLION Estimated ecommerce sales in 2021.4 96% of organizations don’t understand it.5 20 MILLION Penalty (in Euros) for non-compliance.*5 Companies must of companies plan on advanced digitisation by 2020.3 GDPR (General Data Protection Regulation, EU) Maintain compliance with DigiCert SSL/PKI Solutions. With DigiCert SSL/PKI Solutions, you get certification management, malware and vulnerability scanning in a single, easy-to-use console. VISIT https://www.websecurity.symantec.com for more information. *20 million Euros or 4% of group worldwide turnover (whichever is greater) 1 http://www.internetworldstats.com/stats.htm 2 https://www.gartner.com/newsroom/id/3598917 3 https://www.pwc.com/gx/en/industries/industry-4.0.html 4 https://www.statista.com/statistics/379046/worldwide-retail-e-commerce-sales/ 5 Symantec ISTR 2017, 6 2016 Cost of Data Breach Study: Global Analysis, Ponemon Institute, June 2016 7 Ponemon, 2017, Cost of Data Breach Study 8 Ponemon, 2016, State of Cyber Security in SMB © 2018 DigiCert, Inc. All rights reserved. DigiCert and its logo are registered trademarks of DigiCert, Inc. Symantec and the Checkmark Logo are trademarks or registered trademarks of Symantec Corporation or its affiliates in the U.S. and other countries and are used by DigiCert, Inc. pursuant to a license. Other names may be trademarks of their respective owners. $158 Average cost per lost or stolen record.6 7.1 BILLION Identities exposed via data breach since 2009.5 36% of 2016 data breaches were caused by theft.5 44% of 2016 data breaches affected services (more than any other industry).5 Cybersecurity Compliance Can Make or Break Your Business From companies to consumers, the world has gone digital Go beyond basic encryption to combat compliance complexity 51.7%of the population is connected to the internet.1 90%of SMBs say anti-malware is critical to their security.8 53% of SMBs say ability to assess vulnerabilities is important for their security.8 $400,000Decrease in the cost of a breach with extensive encryption.7 Moving online is good for business… 50% of card fraud occurs via ecommerce & remote payment.5 74% of IT pros feel their companies lack full compliance.7 Merchants bear the brunt of FINANCIAL RESPONSIBILITY & REPUTATION RISK.5 PCI (Payment Card Industry) …but it comes at a price 6,838,017 Identities exposed in 2016.5 22% Increase in U.S. healthcare breaches from 2015 to 2016.5 $1,650,300 HIPAA (Health Insurance Portability & Accountability Act) Maximum penalty for violation.5 PREPARE, PROTECT, DETECT & respond to threats.
