CYBER SCCURITY AND ETHICAL HACKING.pptx
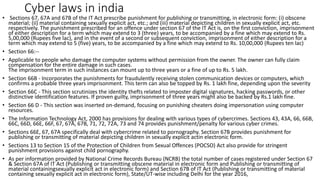
- 1. Cyber laws in india • Sections 67, 67A and 67B of the IT Act prescribe punishment for publishing or transmitting, in electronic form: (i) obscene material; (ii) material containing sexually explicit act, etc.; and (iii) material depicting children in sexually explicit act, etc. respectively. The punishment prescribed for an offence under section 67 of the IT Act is, on the first conviction, imprisonment of either description for a term which may extend to 3 (three) years, to be accompanied by a fine which may extend to Rs. 5,00,000 (Rupees five lac), and in the event of a second or subsequent conviction, imprisonment of either description for a term which may extend to 5 (five) years, to be accompanied by a fine which may extend to Rs. 10,00,000 (Rupees ten lac) • Section 66:-- • Applicable to people who damage the computer systems without permission from the owner. The owner can fully claim compensation for the entire damage in such cases. The imprisonment term in such instances can mount up to three years or a fine of up to Rs. 5 lakh. • Section 66B - Incorporates the punishments for fraudulently receiving stolen communication devices or computers, which confirms a probable three years imprisonment. This term can also be topped by Rs. 1 lakh fine, depending upon the severity • Section 66C - This section scrutinizes the identity thefts related to imposter digital signatures, hacking passwords, or other distinctive identification features. If proven guilty, imprisonment of three years might also be backed by Rs.1 lakh fine. • Section 66 D - This section was inserted on-demand, focusing on punishing cheaters doing impersonation using computer resources. • The Information Technology Act, 2000 has provisions for dealing with various types of cybercrimes. Sections 43, 43A, 66, 66B, 66C, 66D, 66E, 66F, 67, 67A, 67B, 71, 72, 72A, 73 and 74 provides punishment/penalty for various cyber crimes. • Sections 66E, 67, 67A specifically deal with cybercrime related to pornography. Section 67B provides punishment for publishing or transmitting of material depicting children in sexually explicit actin electronic form. • Sections 13 to Section 15 of the Protection of Children from Sexual Offences (POCSO) Act also provide for stringent punishment provisions against child pornography. • As per information provided by National Crime Records Bureau (NCRB) the total number of cases registered under Section 67 & Section 67A of IT Act (Publishing or transmitting obscene material in electronic form and Publishing or transmitting of material containingsexually explicit act in electronic form) and Section 67B of IT Act (Publishing or transmitting of material containing sexually explicit act in electronic form), State/UT-wise including Delhi for the year 2016,
- 2. 1.offensive 2.diffensive WHAT ARE HACKING HAKING ARE THE GETTING ACCESS WITHOUT PERMISSION TYPES (CYBER ATTACKS):- 1.PHISHING- 1.2fa 2. password modify 3.sec. checkup 2.BRUTEFORCE 12 char .special symbil up[ercase lower case numerica 3.MIM-wifi website and gmail conversation 4.MALWARE-software or app # social engineering- information gathering 5.PASSWORD ATTACK 6.DDOS- boat checkup 7.DRIVE BY DOWNLOAD 8.ROGUE SOFTWARE
- 3. • Cdlu • 1sec 100000server
- 5. BASICS OF ETHICAL HACKING • HOW THE MALWARE ARE SEND :- • EMAIL ATTACHMENT • SOFTWARE DOWNLOAD • OS VULNERABILITY
- 6. 2. PHISHING • PHISHING ARE THE MOST COMMON ARE HIGHLY USED TOOLS BY THE HACKERS • IT CONTAINS A LINK • IT ACCESS YOUR USER ID AND PASSWORD IN BACKGROUND • FOR PHISHING USE FAKE EMAIL • https://f4b07164b10a.ngrok.io
- 7. 3. PASSWORD ATTACK • Try some essiential passwords by guessing the password through algorithms • It has 3 types • 1. bruteforce • 2. dictionary • 3. keylogger Password attack Bruteforce Keylogger Dictionary
- 8. 4. Ddos • It is mostly use on website or a private network to down their performance by this that network either go down(slow) or crash • Every server or website has a limit that the handle or access limited request to join like 1lakh/sec • In ddos attack a virtual plateform sends multiple request to join that network as a result the performance that server or site go down slow if the traffic are increase it can be crash
- 9. 5. Man in middle attack • In mima we use a intermediate apk for some activity and these apk leaks your data • Like dominoz • Or in benking we use some upi app that are not verified and sell your account details Intermediate apk
- 10. 6. Drive by download • We visite a fake site a enter the gmail id and password then it can access your drive and get your data and also save it on storage device • User Data bsse
- 11. 7. MALWERTISEMENT • Malware + advertisement • It uses advertisement(ad) • Add redirect the malware and get access Site Ad (redirect it ) Malware injection (it happens in background ) User
- 12. 8. Rogue software • It is called scamware • It designed for damage your system • It can stole your card detail Virus alert Plxz update your software to protect yourself from unknown access Redi rect User
- 13. Ransomeware • Type of virus that encrypt your data and ask money to decrypt your data
- 14. Tracing • By ip address (use vpn and tor to shift and fake ip) • Digital footprinting – • Isp • It taken by isp(internet service provider) • Vpn entry time – ipaddress • Exit time –ipaddress • Mac spoofing – • Ip hideusing tor • Ips avoid (use public or private wifi ) • Device rooted (RDP )(virtual machine )
- 15. Termux it is an open source terminal that can access any reposetry • «: TERMUX:» • What is Termux ? Termux is an Android terminal emulator and Linux environment app that works directly with no rooting or setup required. A minimal base system is installed automatically — additional packages are available using the APT package manag -> App link »https://play.google.com/store/apps/details?id=com.termux • apt update && apt upgrade • termux-setup-storage • pkg install sl(for install any tool we use pkg install that tool which you want to install ) • pwd • This command will tell you, your present working directory • ls • this command will show you the folder and files in your current working directory •
- 16. Termux basic • clear • by typing clear in the termux you can clear all the previous results. • mkdir (folderName) • Mkdir Stand for make directory. Type mkdir and give a space and type folder name and press enter to see the folder you have just created just type ls • rmdir (folderName) or rm –rf (folder name ) • Rmdir stands for Remove Directory.Type rmdir space folder name to remove that folder. • pkg uninstall (packageName) • you can uninstall any package from the list, just type pkg uninstall package-name.it will ask you where if you wanna delete the package or not press y and the package will be uninstalled. • cat (file-name) • Run this command and everything in the text file will be printed on the terminal. • e.g: cat data.txt •
- 17. Basic pkg for termux • pkg update -y&& pkg upgrade -y&& pkg install python -y&& pkg install python2 -y&& pkg install python2-dev -y&& pkg install python3 -y&& pkg install java - y&& pkg install fish -y&& pkg install ruby -y&& pkg install help -y&& pkg install git -y&& pkg install host -y&& pkg install php -y&& pkg install perl -y&& pkg install nmap -y&& pkg install bash -y&& pkg install clang -y &&pkg install nano - y&& pkg install w3m -y&& pkg install havij -y&&pkg install hydra -y&& pkg install figlet -y&&pkg install cowsay -y&&pkg install curl -y&& pkg install tar -y&& pkg install zip -y&& pkg install unzip -y&& pkg install tor -y&& pkg install google -y&& pkg install sudo -y&& pkg install wget -y&&pkg install wireshark -y &&pkg install wgetrc -y &&pkg install wcalc -y&&pkg install bmon -y&& pkg install vpn -y && pkg install unrar -y&& pkg install toilet -y&&pkg install proot -y&&pkg install net- tools -y&& pkg install golang -y&& pkg install chroot -y&&termux-chroot - y&&pkg install macchanger -y&&pkg install openssl -y&&pkg install cmatrix - y&&pkg install openssh -y&& pkg install wireshark -y&& termux-setup-storage - y&&pkg install macchanger -y&&apt update && apt upgrade -y
- 18. Social media crime:- • Facebook • Instagram • Twitter • Snapchat • Gmail • It contains financial faroud ,scams, • Cyber sccurity works on offensive,defensive,repair the attack,recover the attack • Cheack data breaches on • https://haveipawned.com/ • https://amisecure.in •
- 19. Email extortion • Hacker send Fake mail with your password • In this case change your password immediately and always on 2 FA • Some useful sites • 1 https://.cybercrime.gov.in/ • www.csk.gov.in • www.nciipc.gov.in • www.ceir.gov.in • www.bprd.nic.in • www.exifdata.com • www.urlex.org • www.safeweb.Norton.com • www.tineye.com • Reverse image search google • www.cqcounter.com • www.bevigil.com • Goole authenticator • Bulk sms software
- 20. • Footprinting • It stends about information gathering ip Dns(isp) Gmail or any social Cont infp footprinting
- 21. • Way back machine used for footprinting
- 22. • 1.operating system • Eg window,mac,linux ,parrot, • Networking • Basics of programming and web site development • Window _ Microsoft 1.32bit • 64bit (processor ) • 1xp vista • Window 7 • Window 8 • Window 8.1 • Window 10 • Window 11 • Linux open source o/s (type of debian • Kali linux open source cmd based android amulator ) • Apple (Mac) • Parrot
- 23. • Networking -connection of millions of comp • Type of network -3 • 1.LAN-local area network • 2.WAN-wide area network • 3.MAN- • Every device has a unique address (ip address )192.168.60.1 • Protocol • https http udp tcp/ip