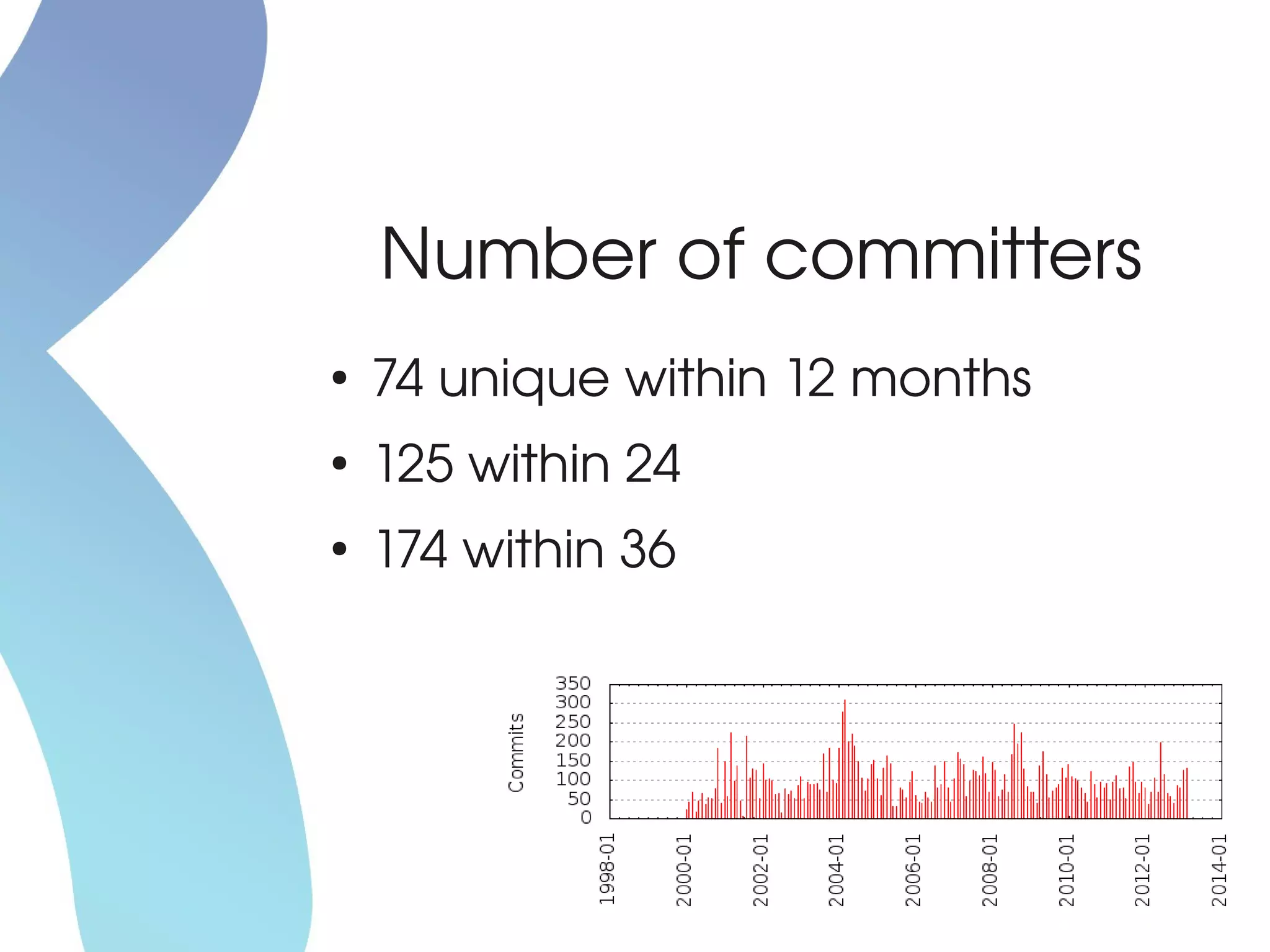
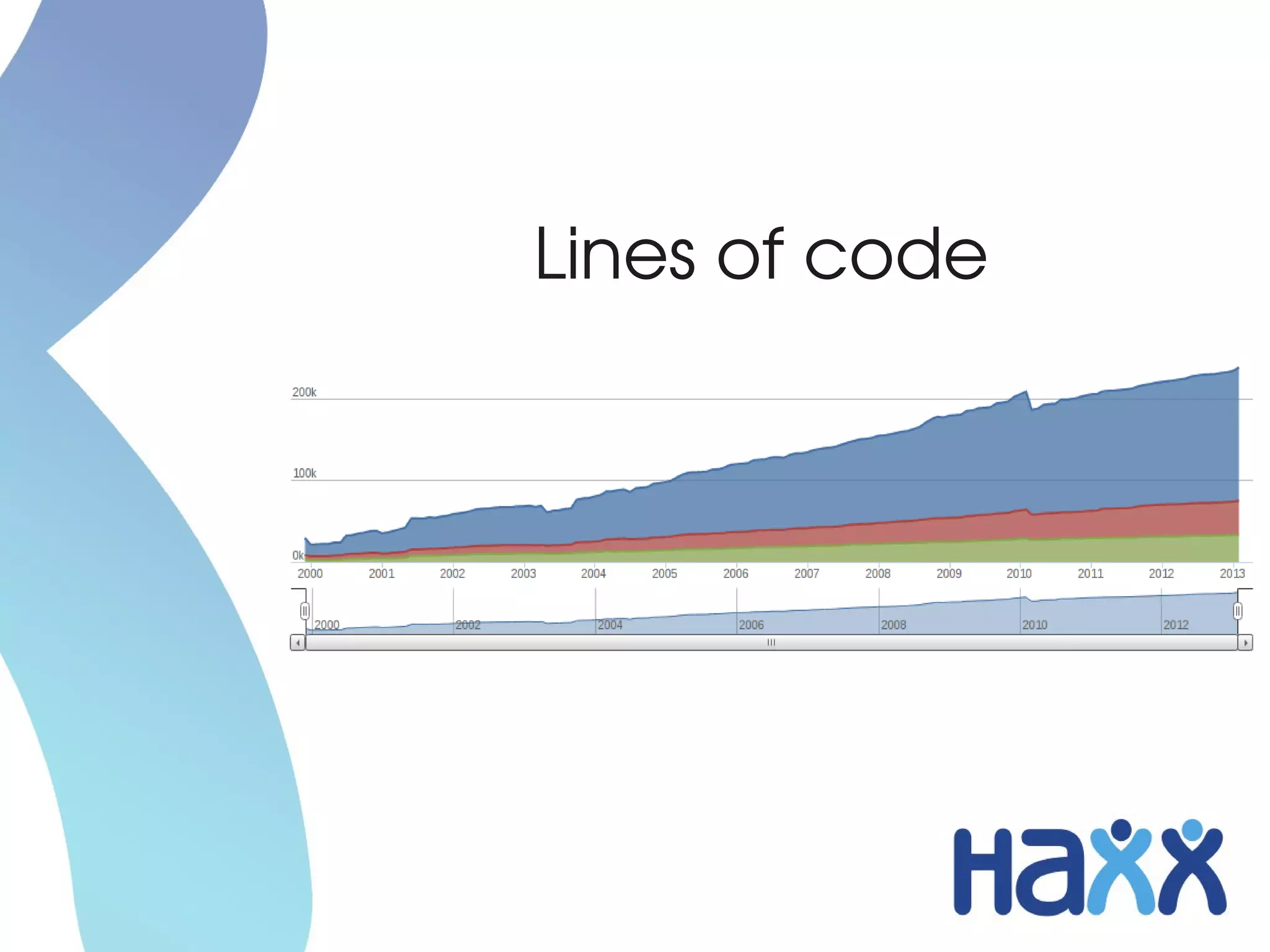
The document discusses curl, a command-line tool for transferring data using various application protocols, highlighting its extensive features, user base of 500 million, and over 1,000 contributors. It emphasizes the importance of continuous evolution of curl to adapt to new technologies and protocols, as well as the community-driven nature of its development. Additionally, it addresses security challenges and outlines future advancements such as HTTP/2 and improvements in authentication methods.