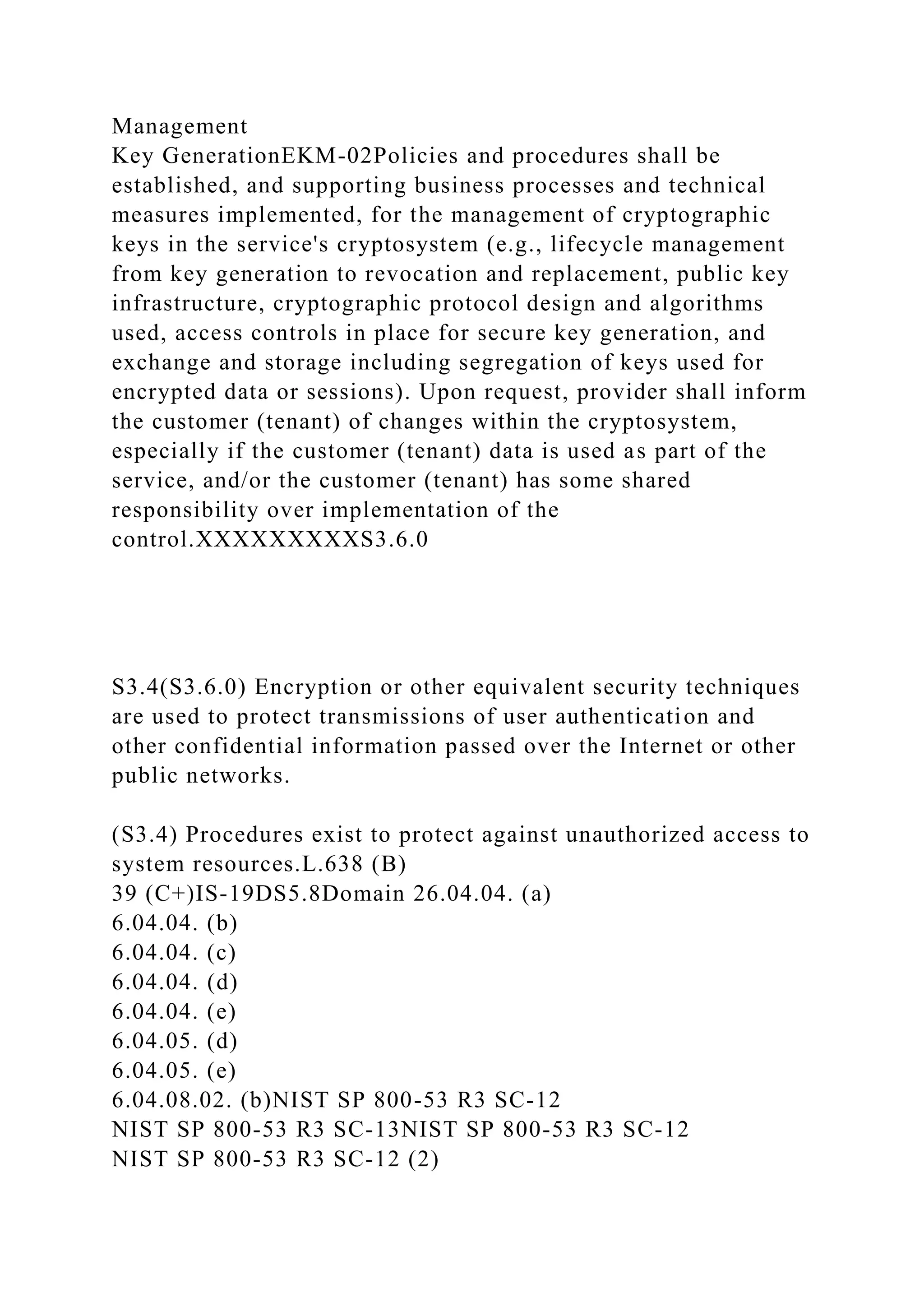
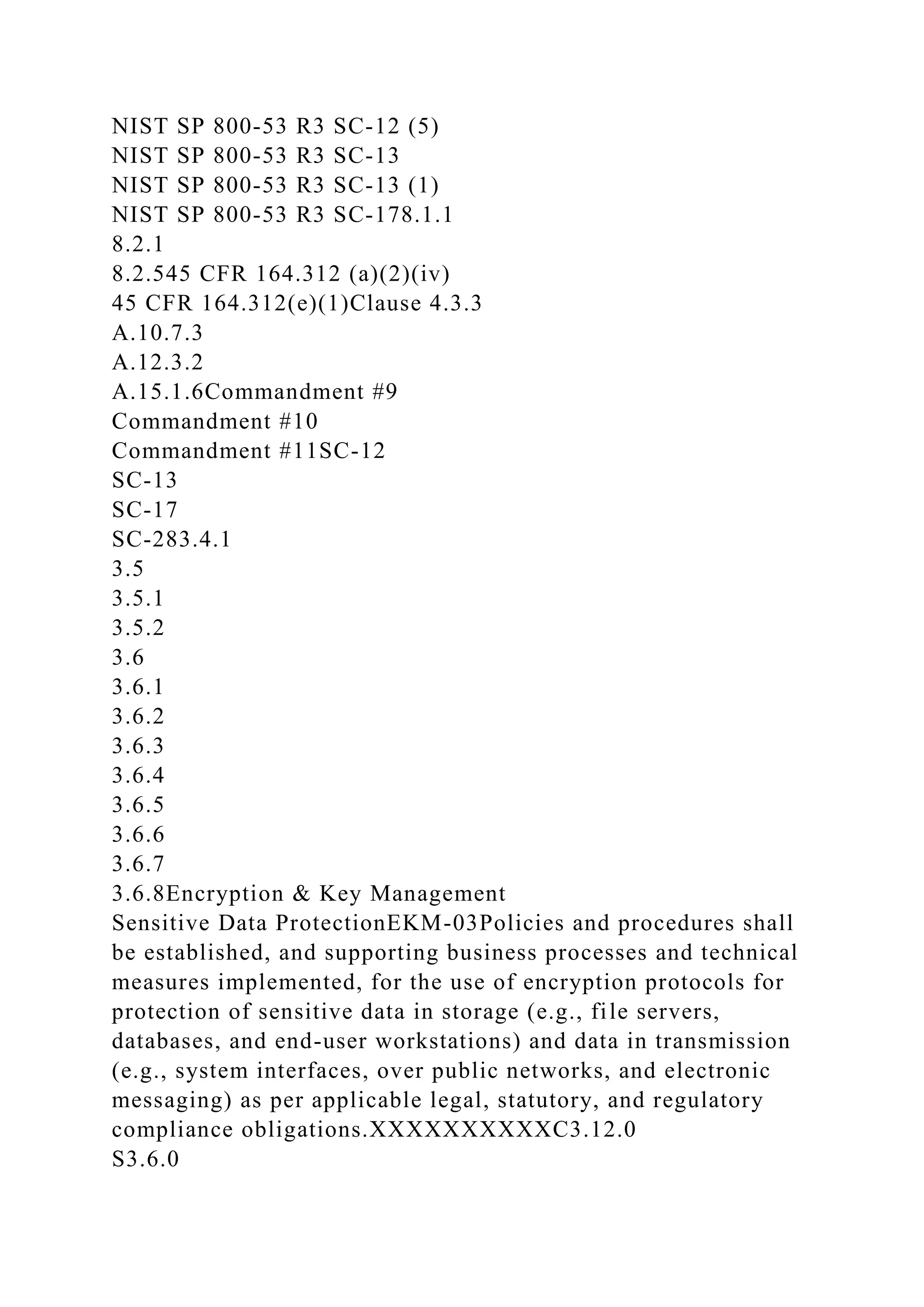
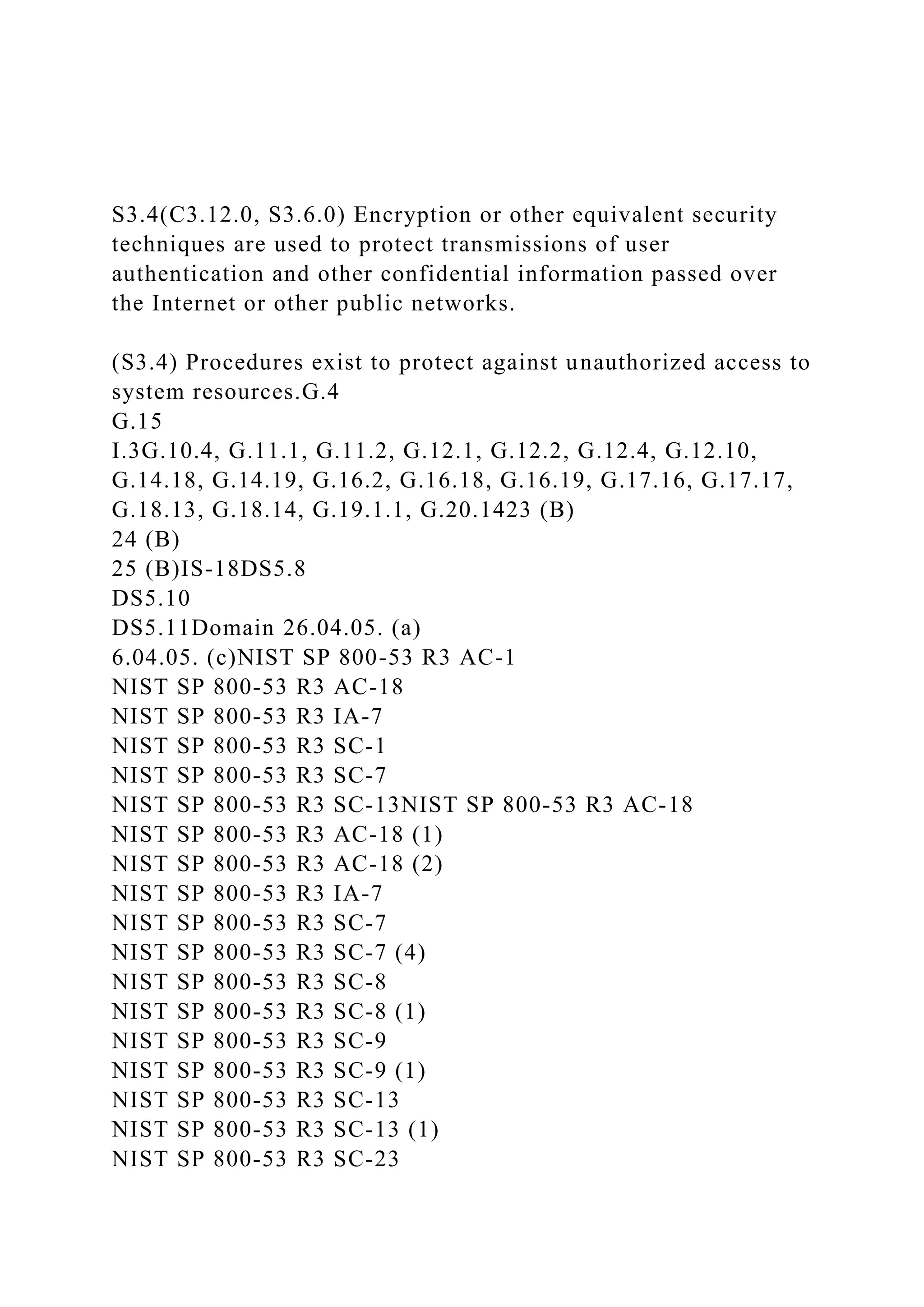
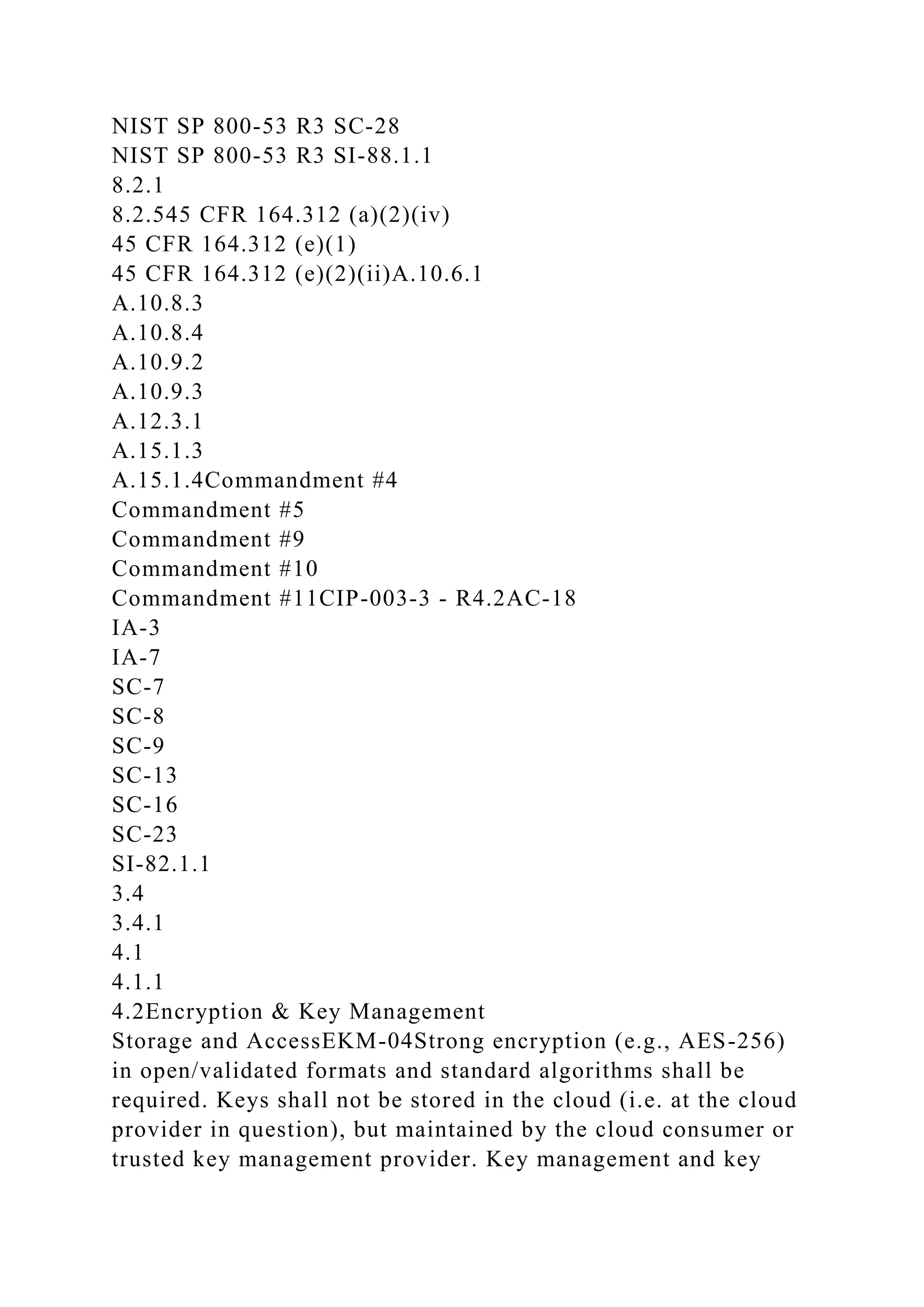
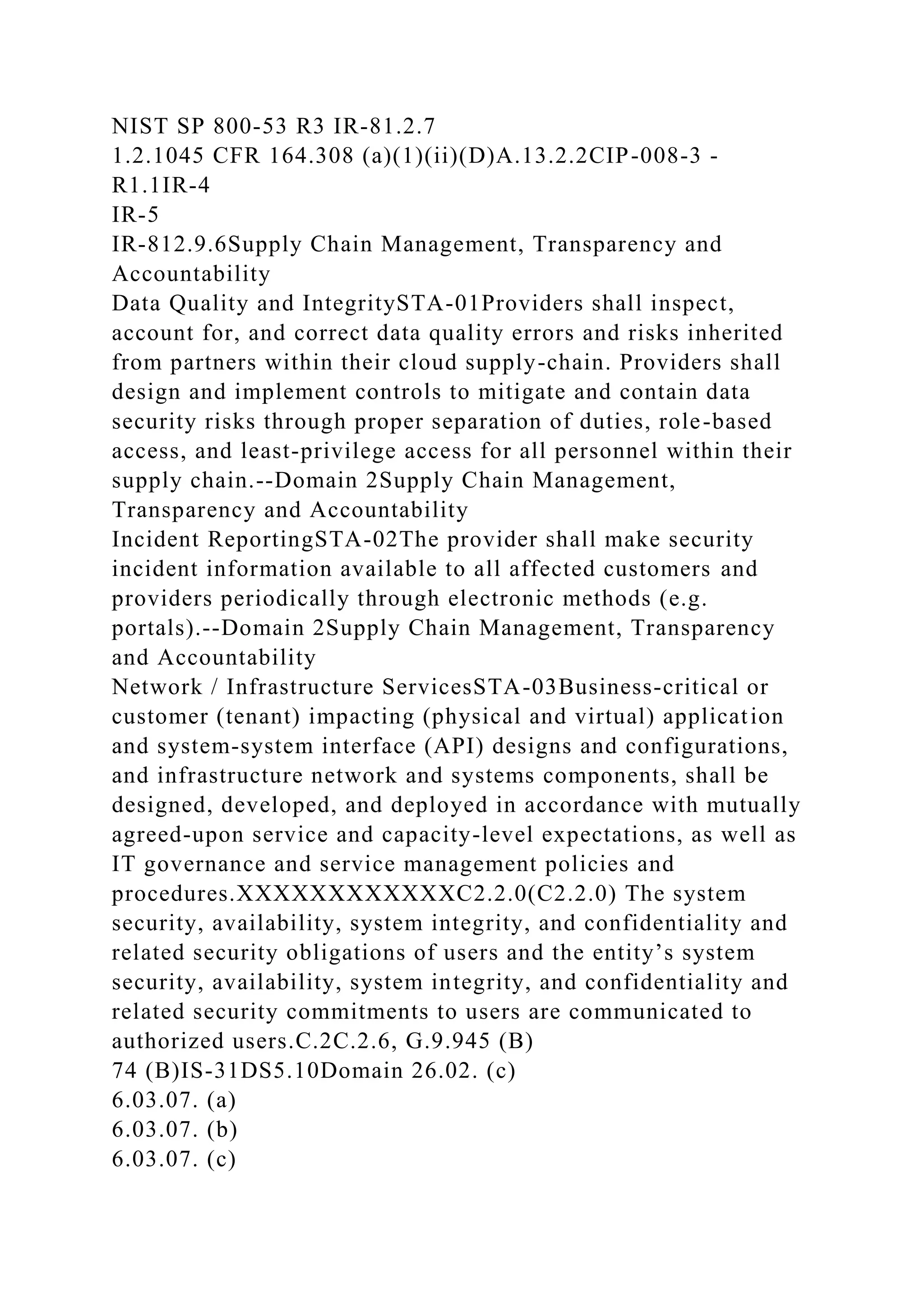
The document outlines the Cloud Controls Matrix (CCM) version 3.0, detailing various control domains and specifications related to cloud security and compliance. It references numerous guidelines and frameworks, including NIST standards and regulatory requirements, emphasizing the importance of application and interface security, customer access management, data integrity, and audit processes. The CCM serves as a comprehensive framework for organizations to ensure their cloud services meet industry-standard security measures and compliance obligations.
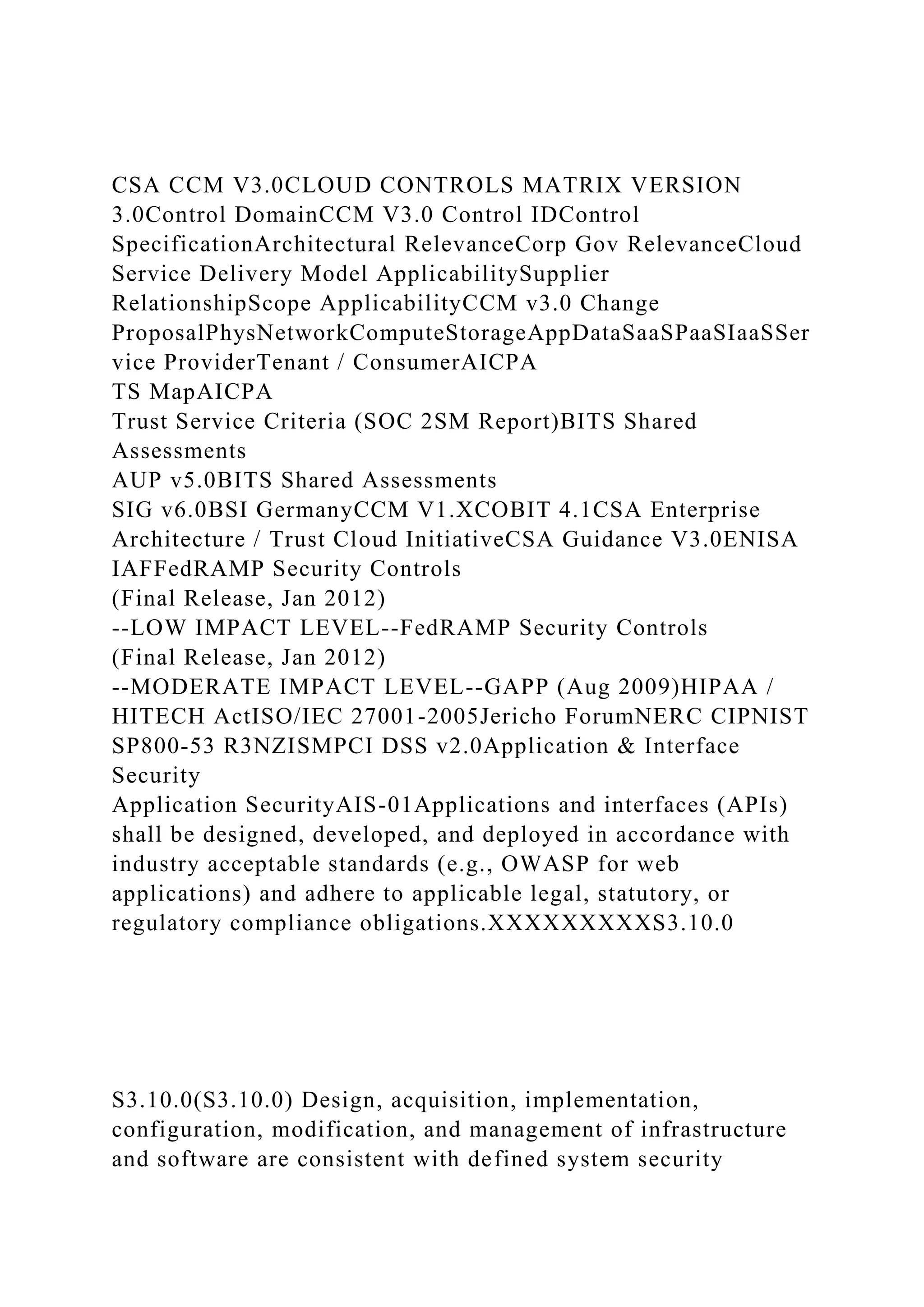
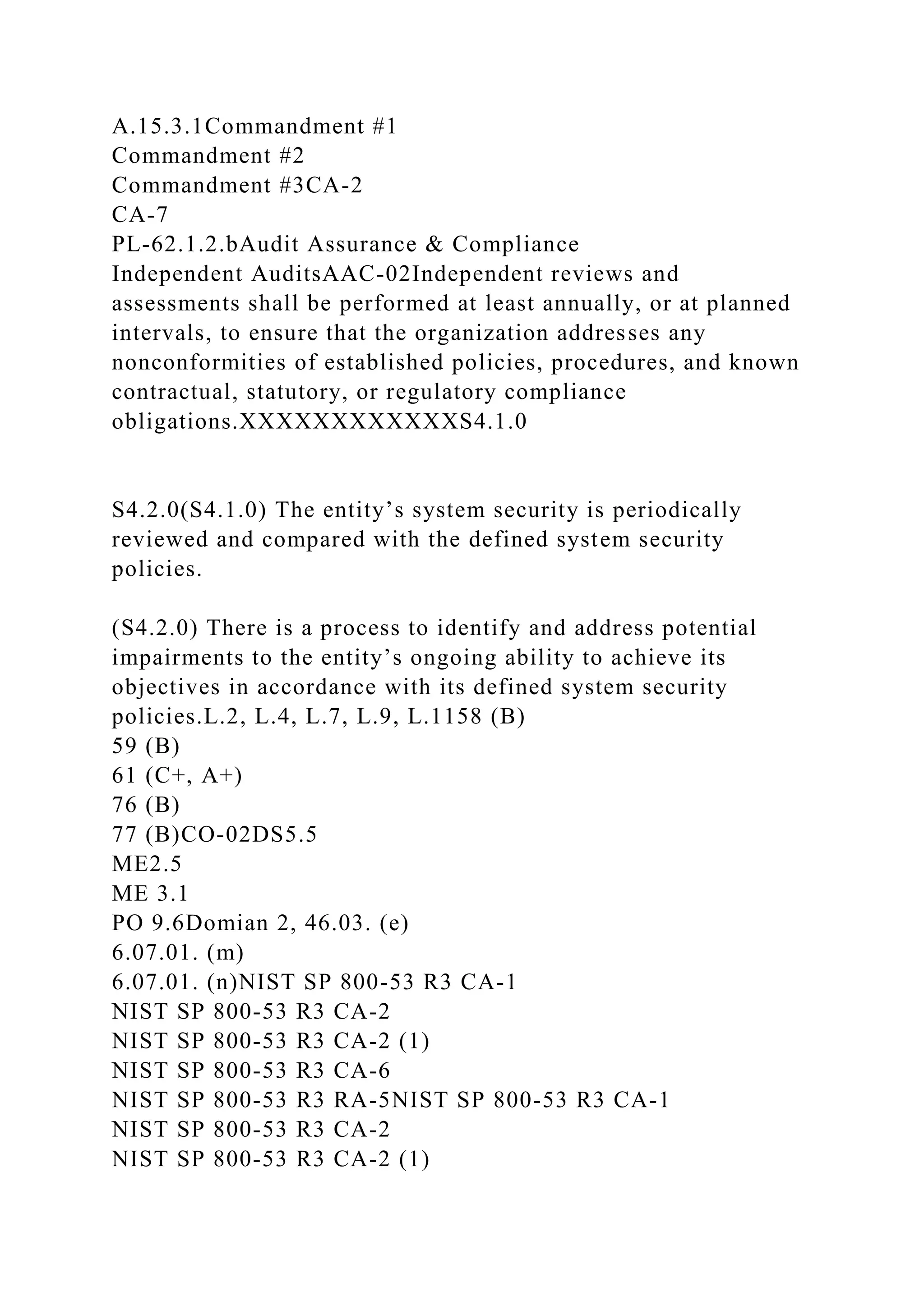
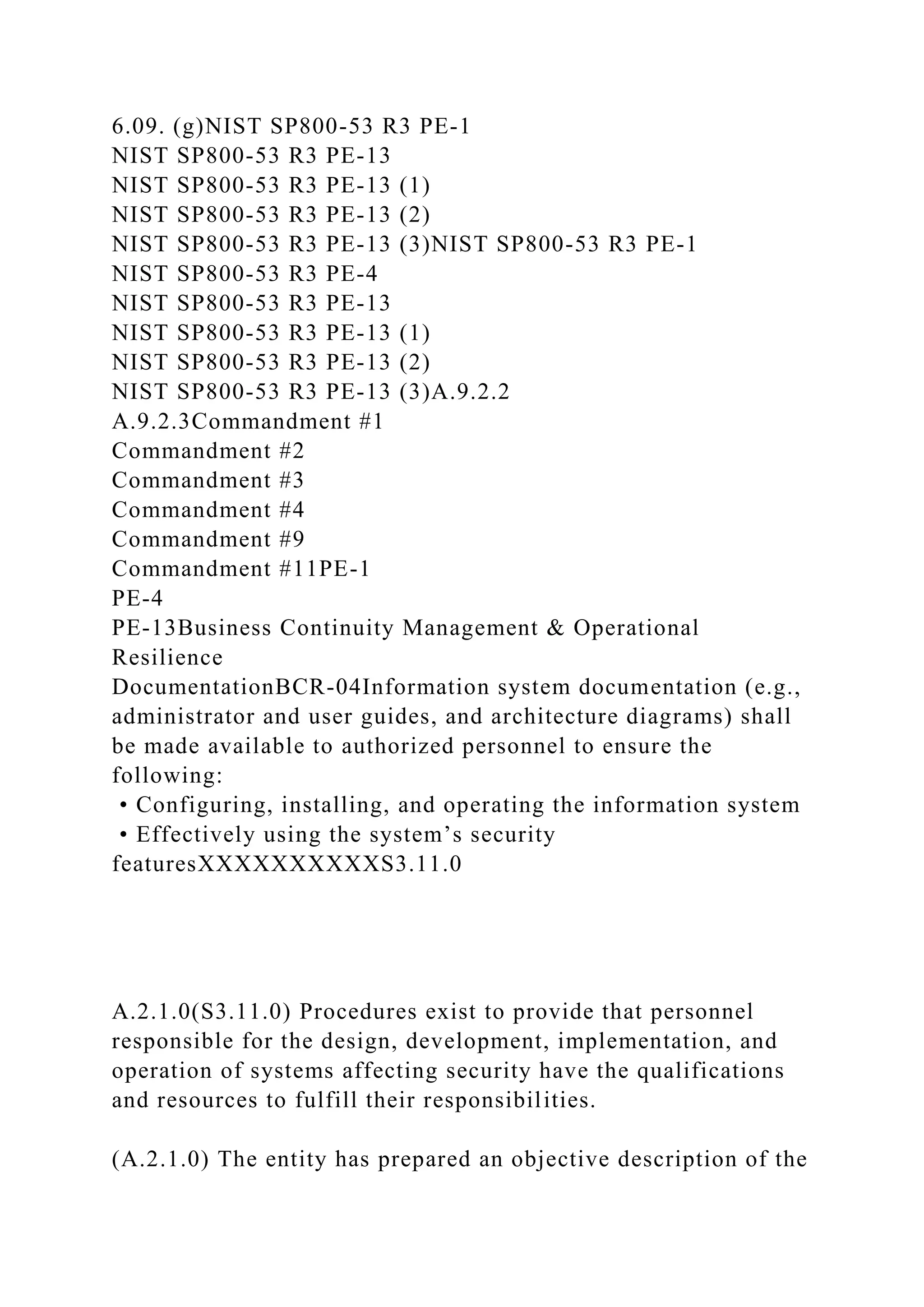
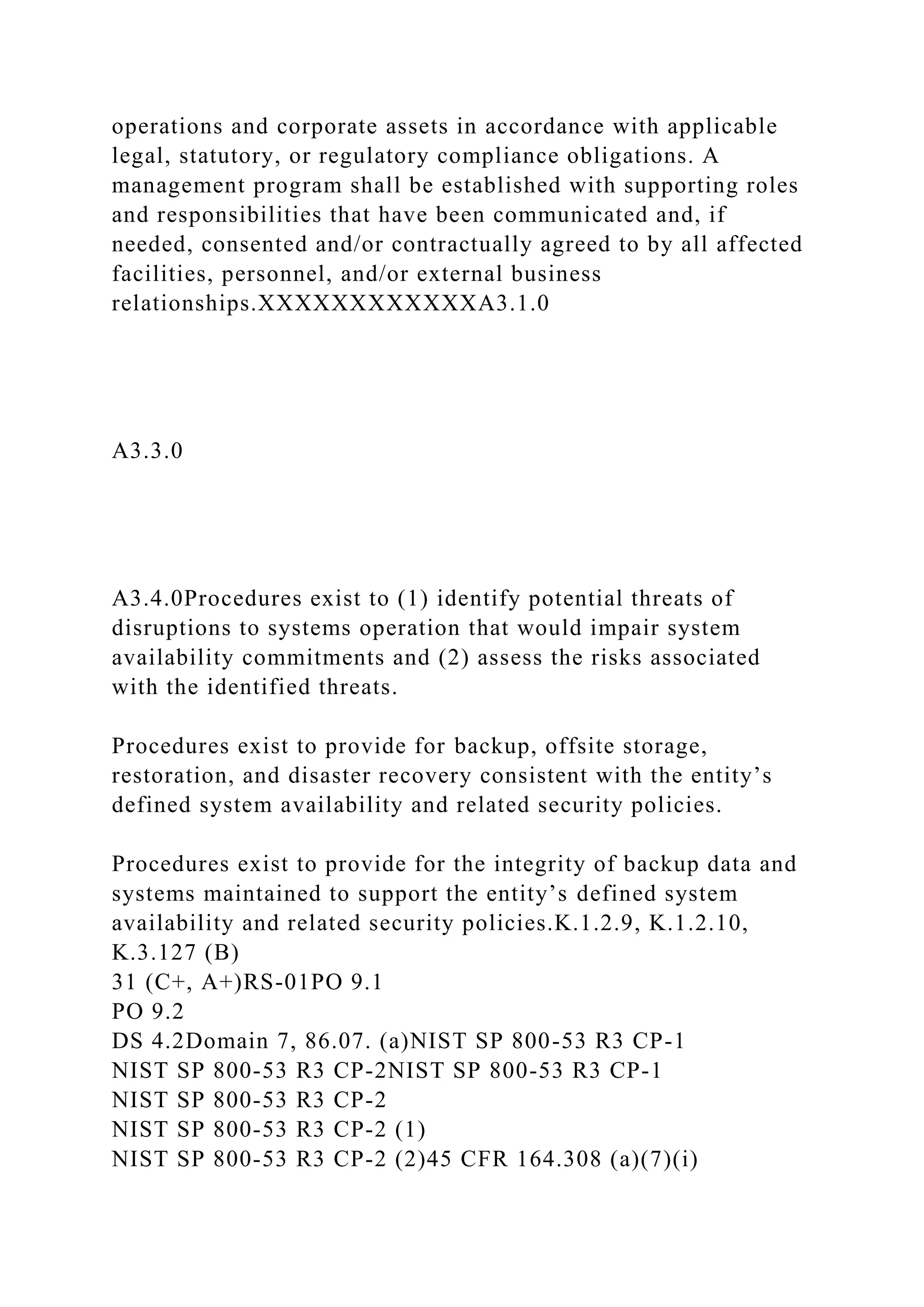
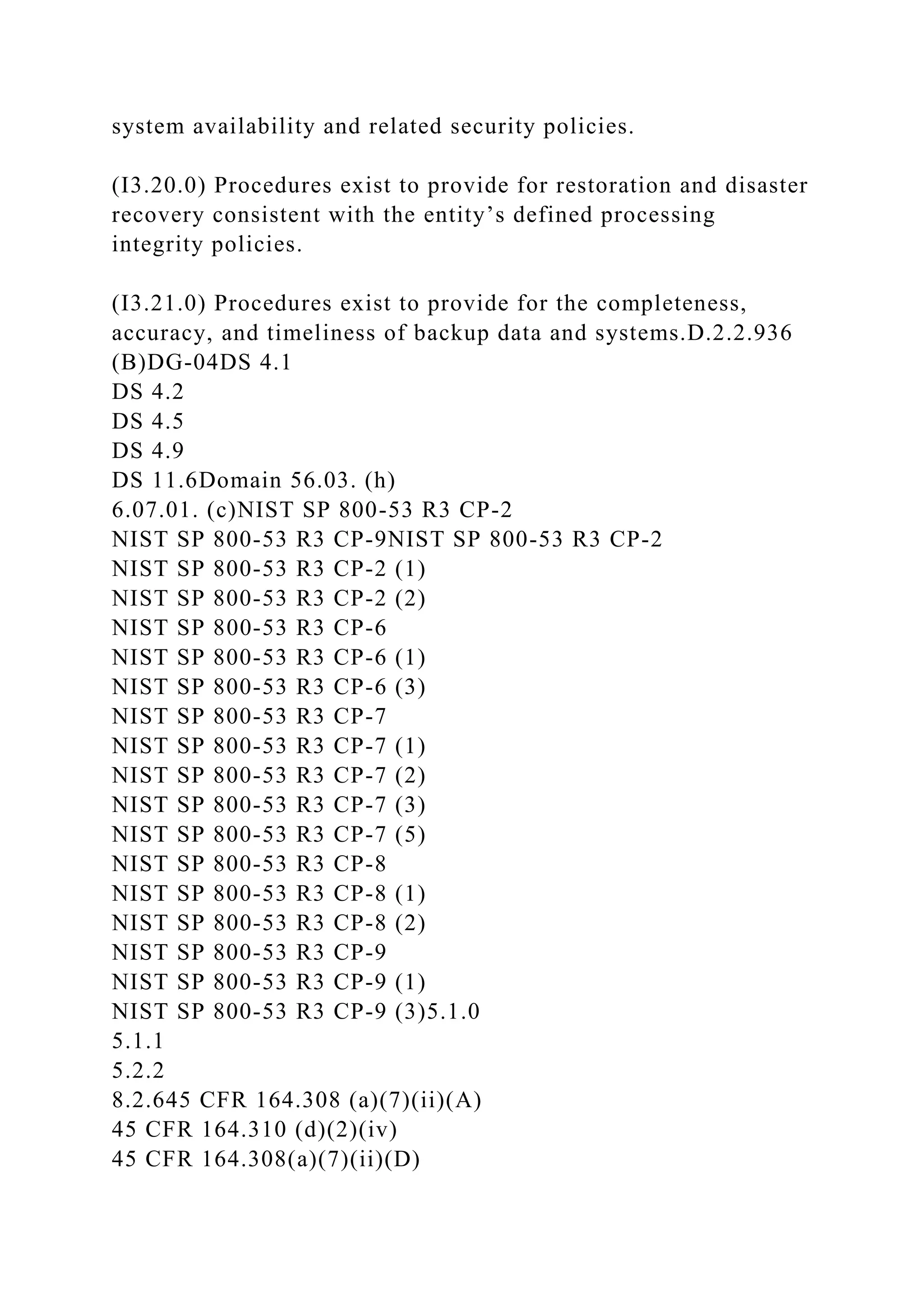
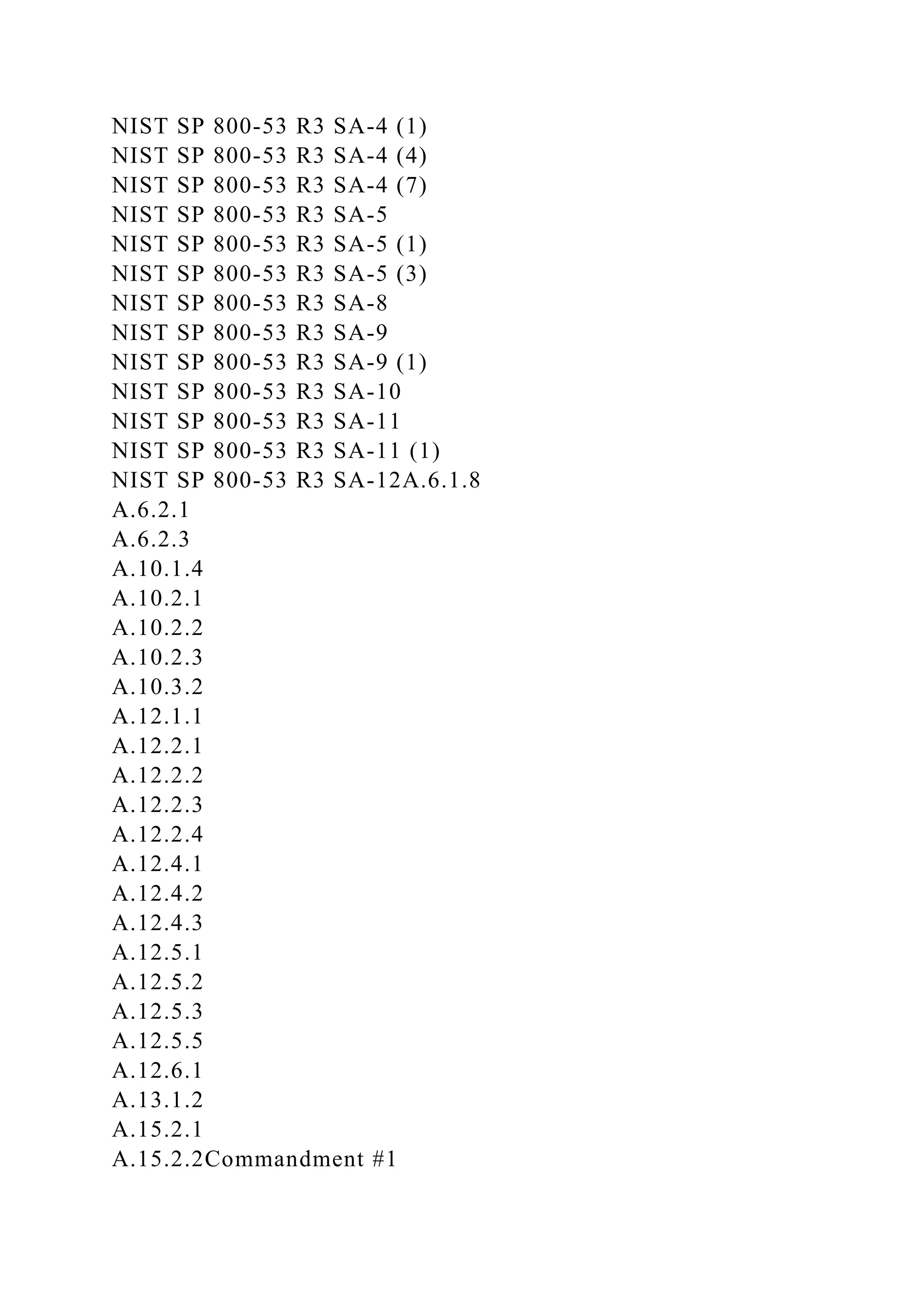
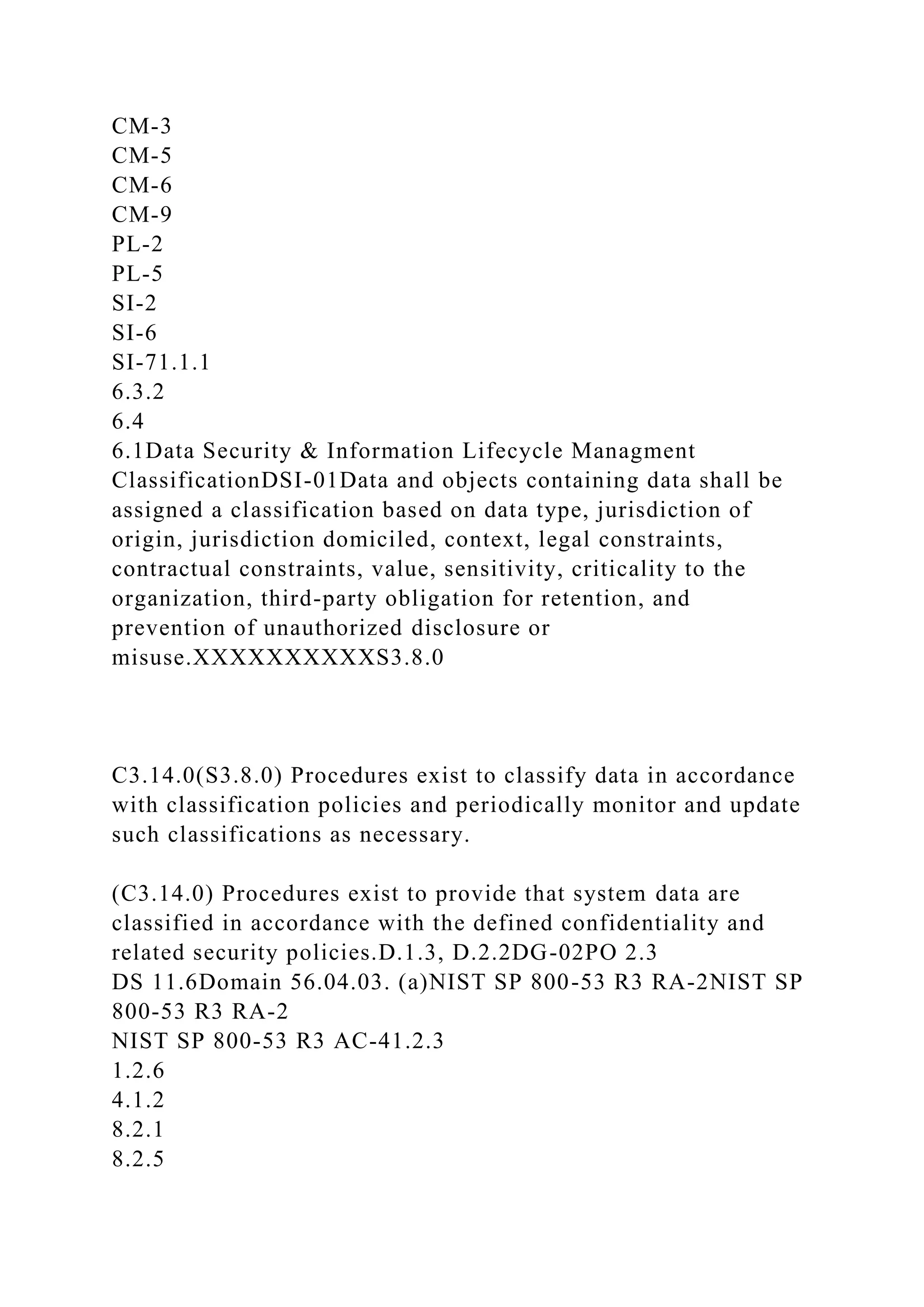
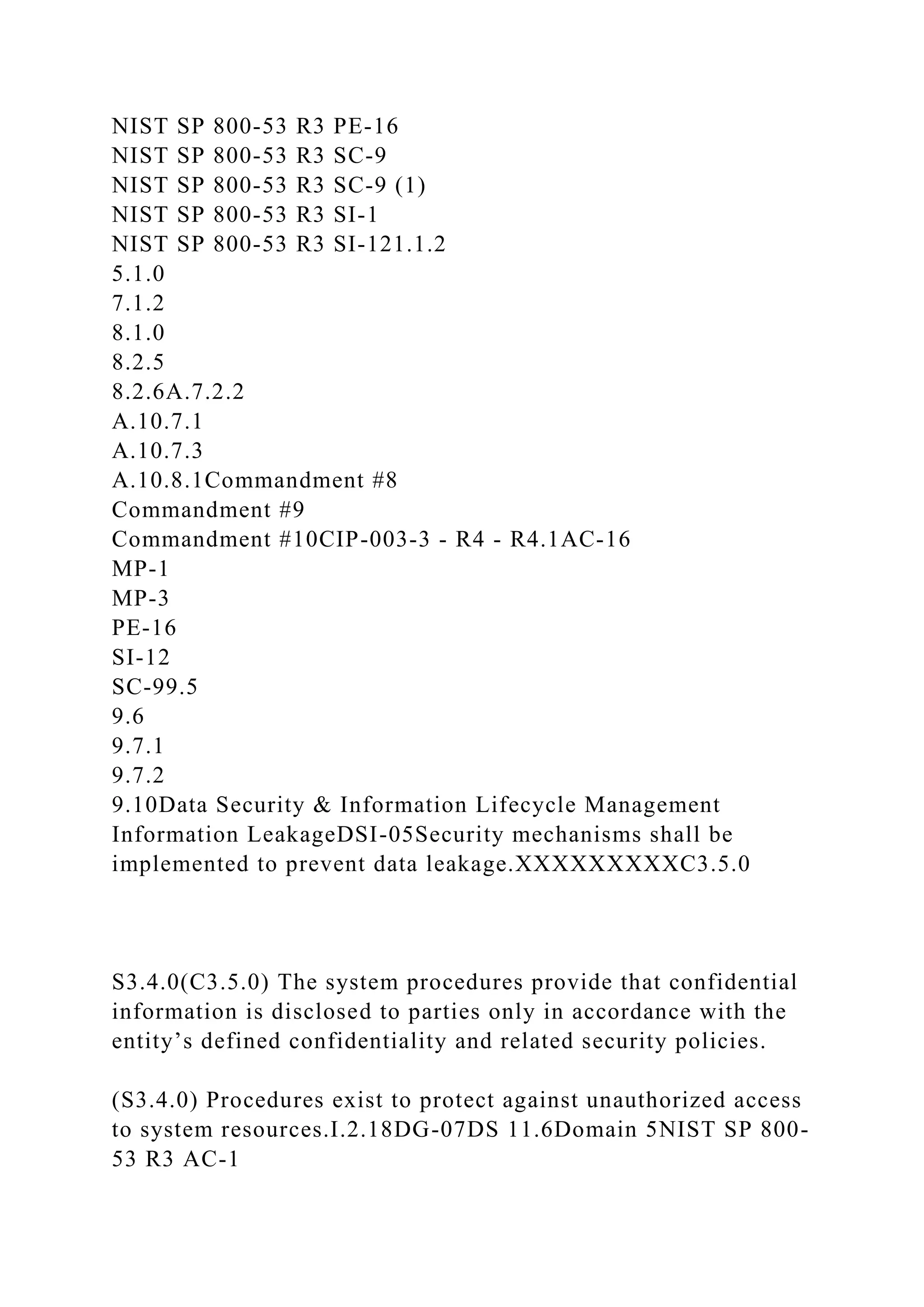
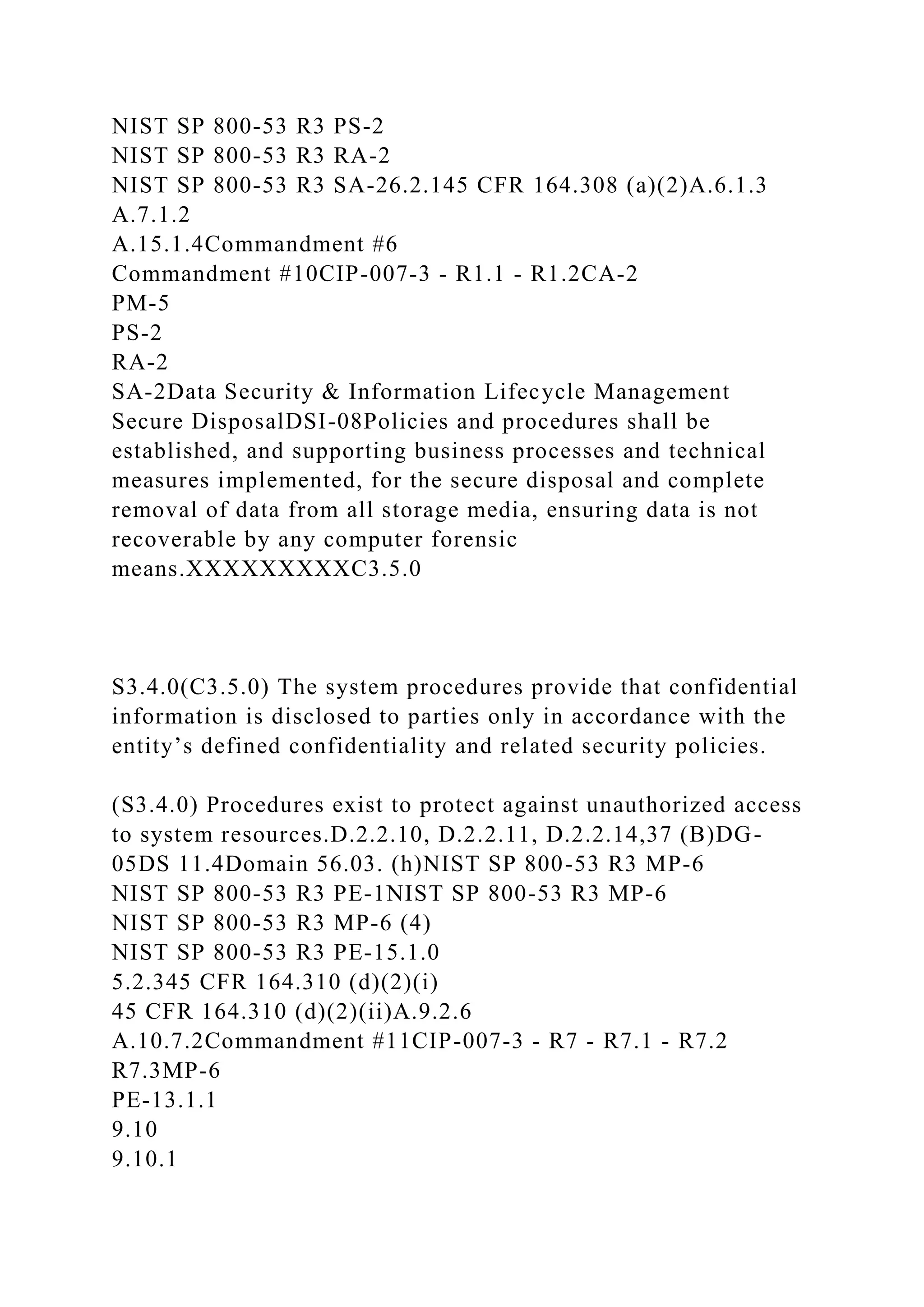
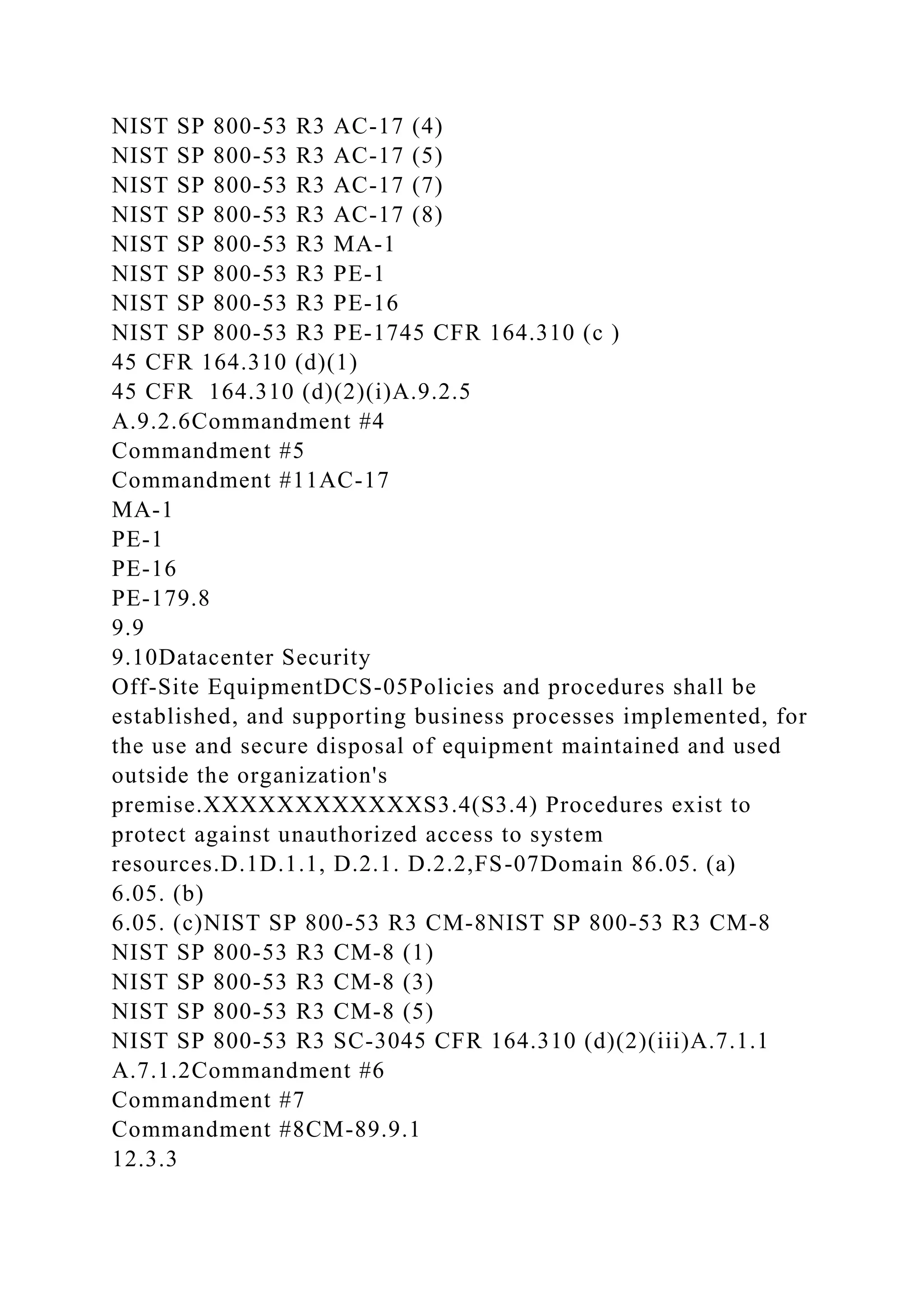
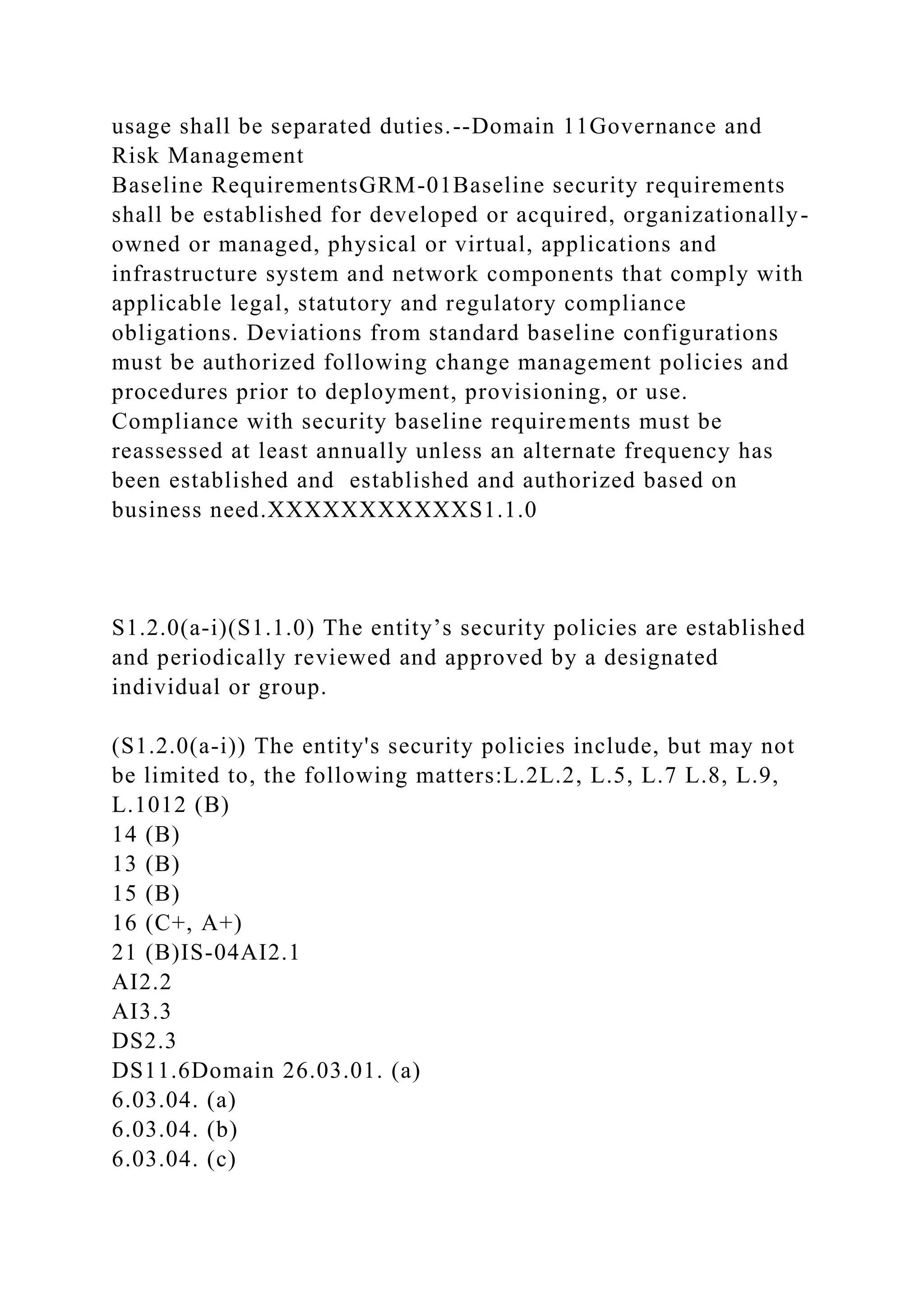
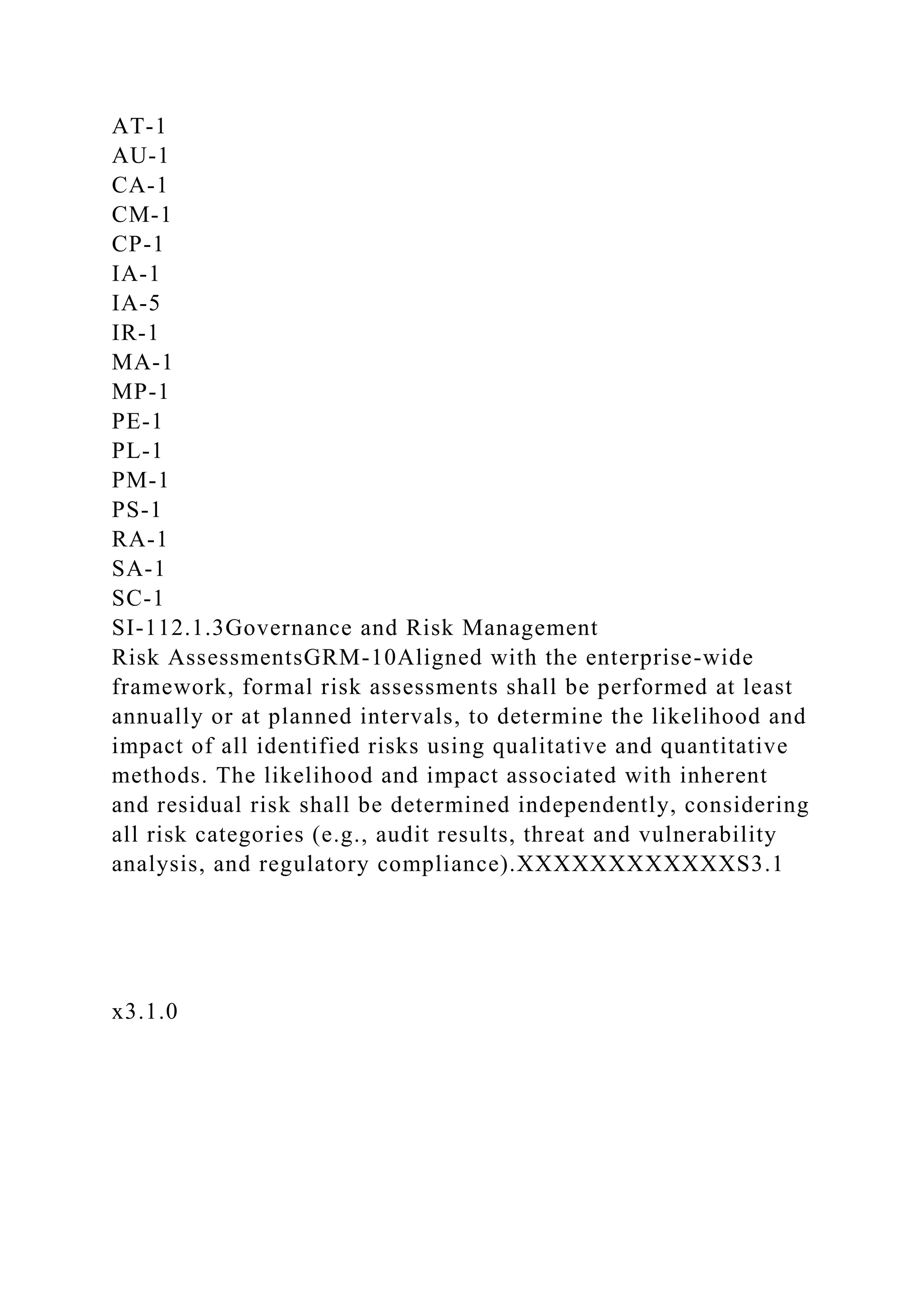
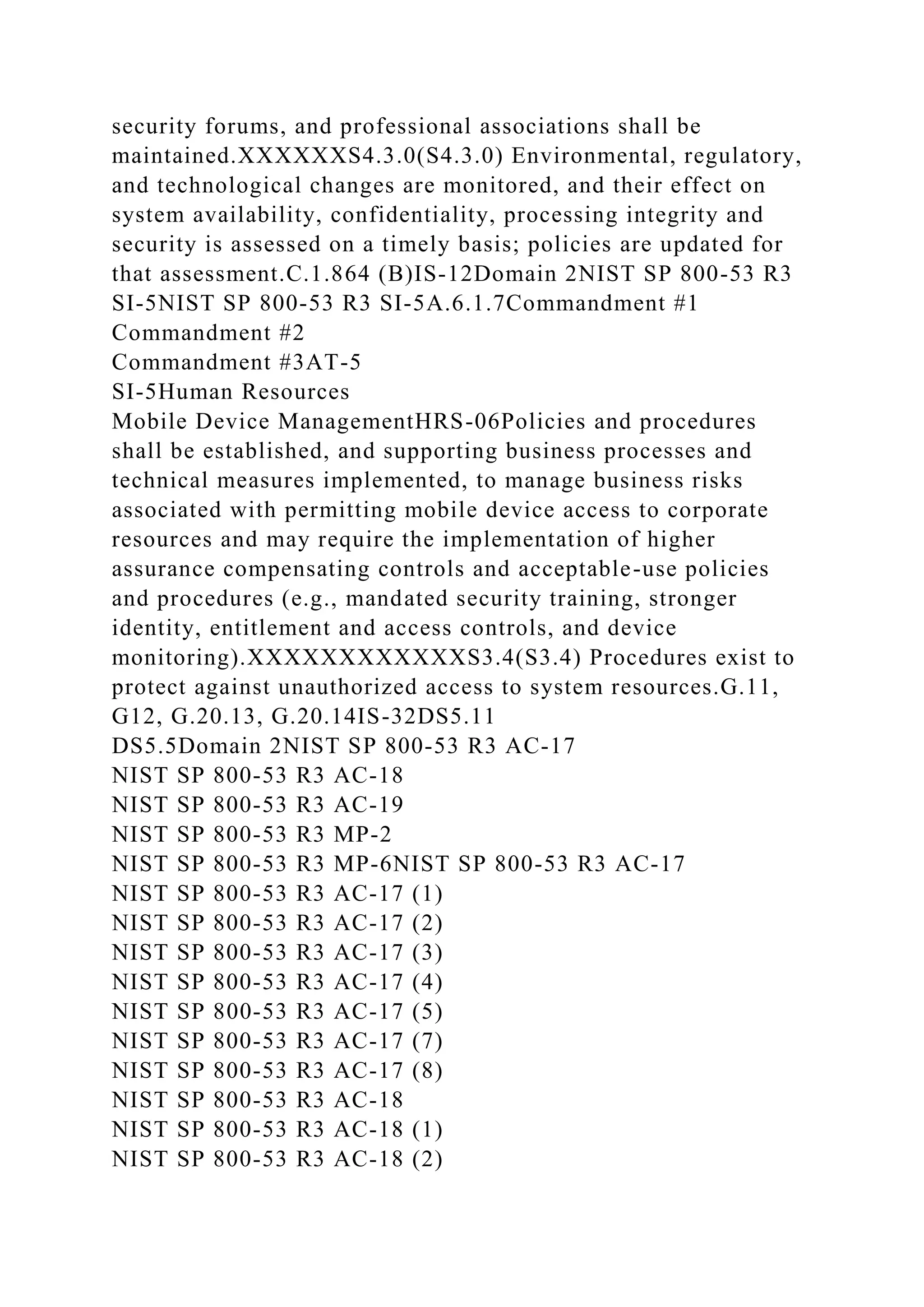
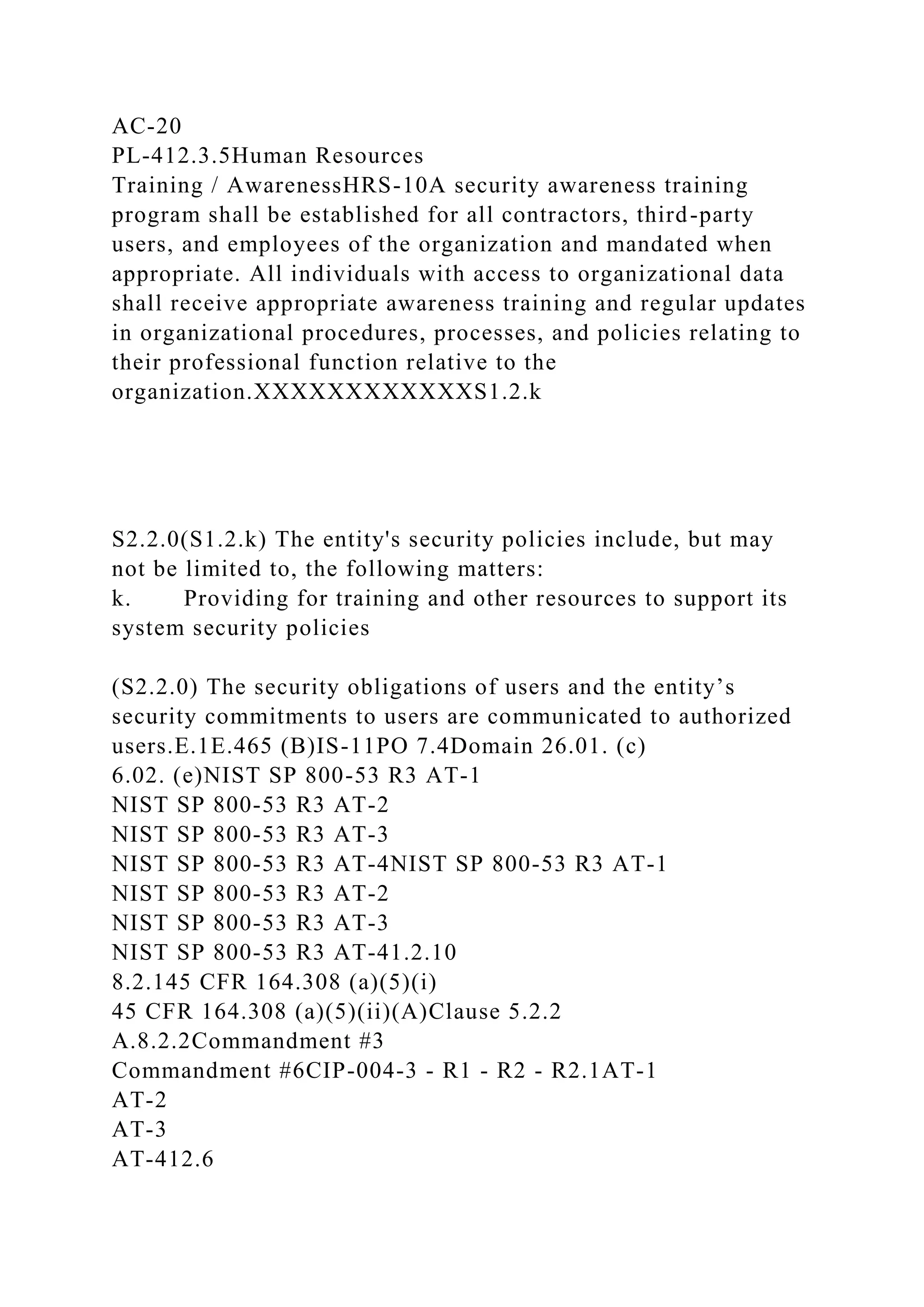
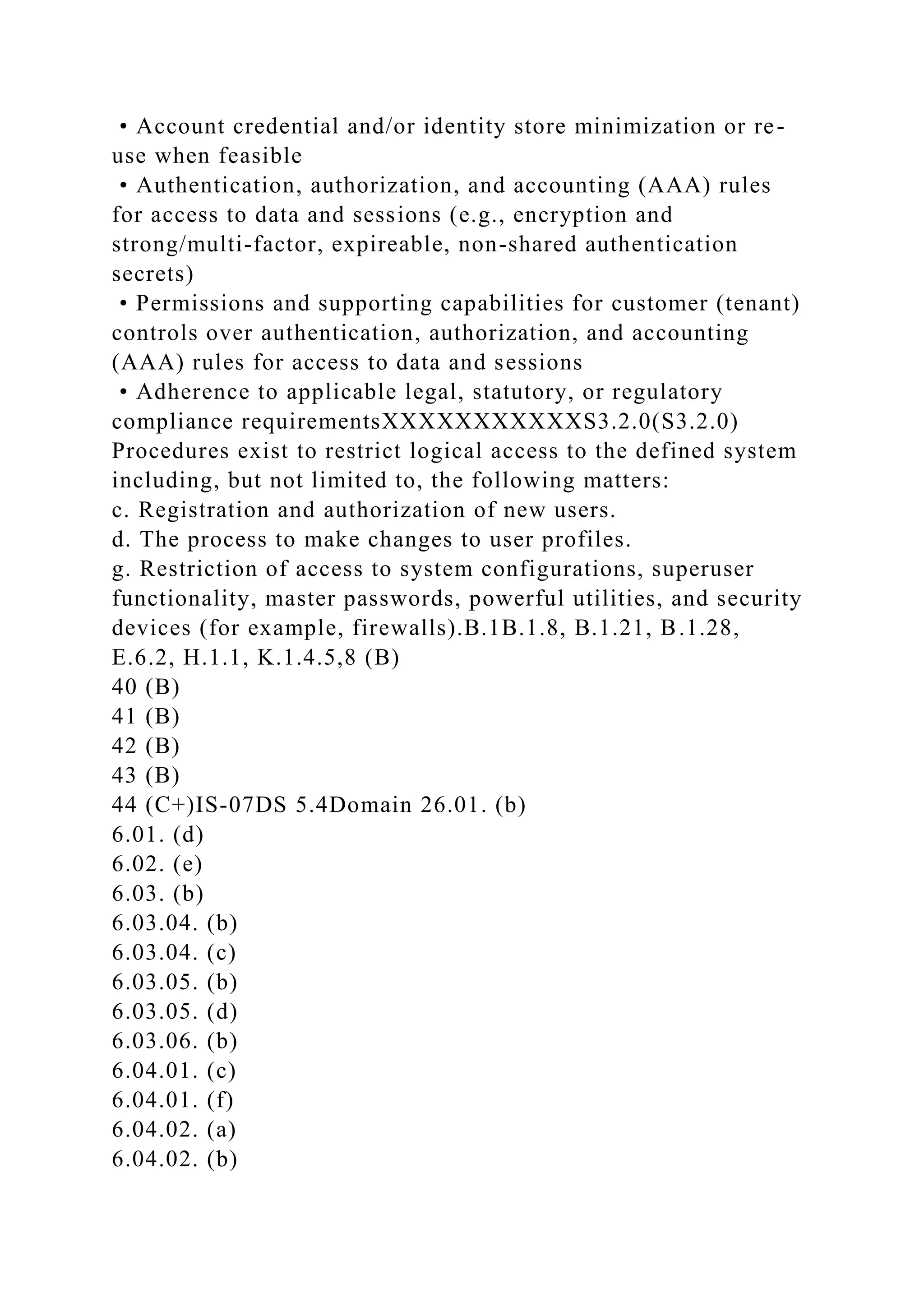
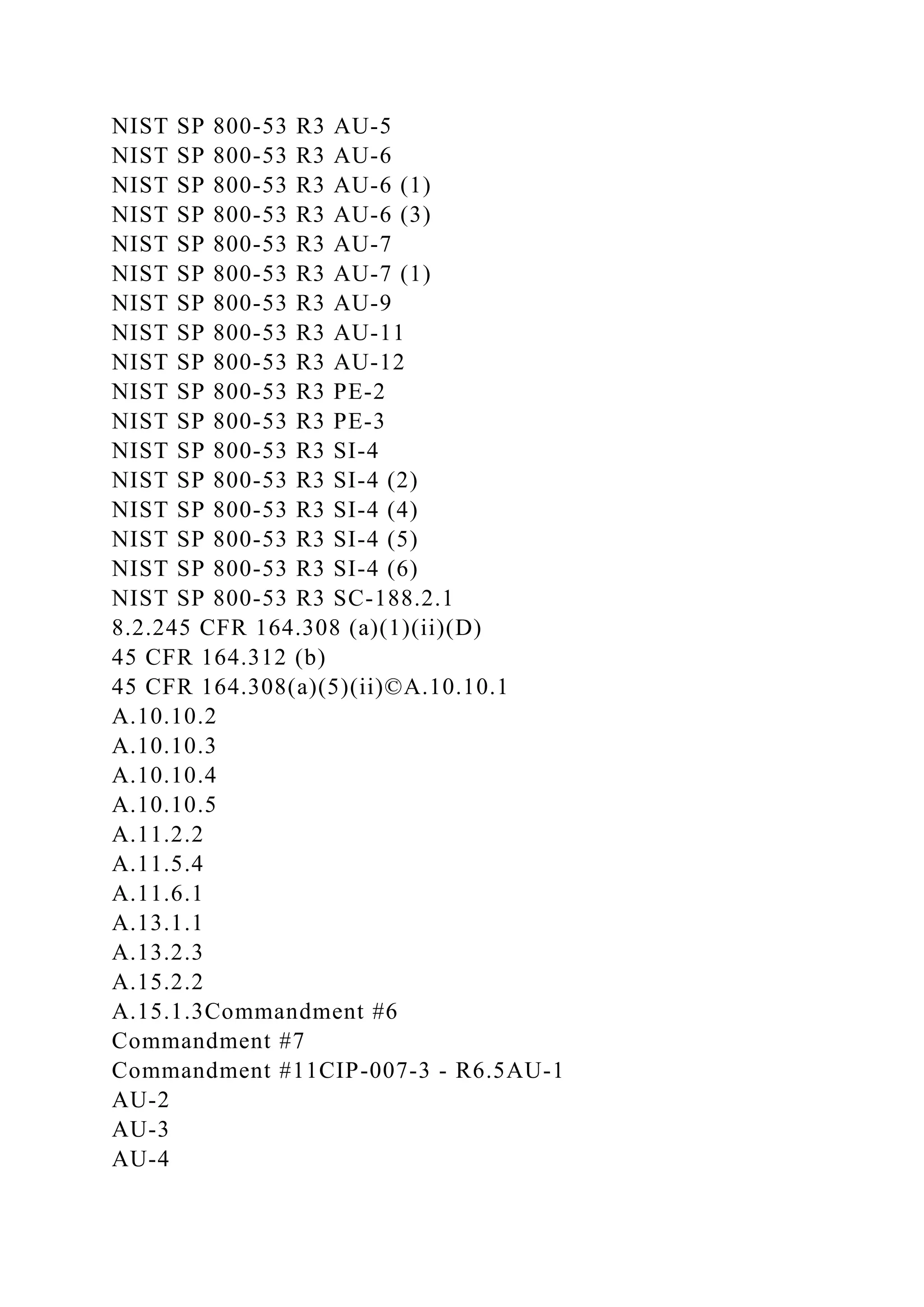
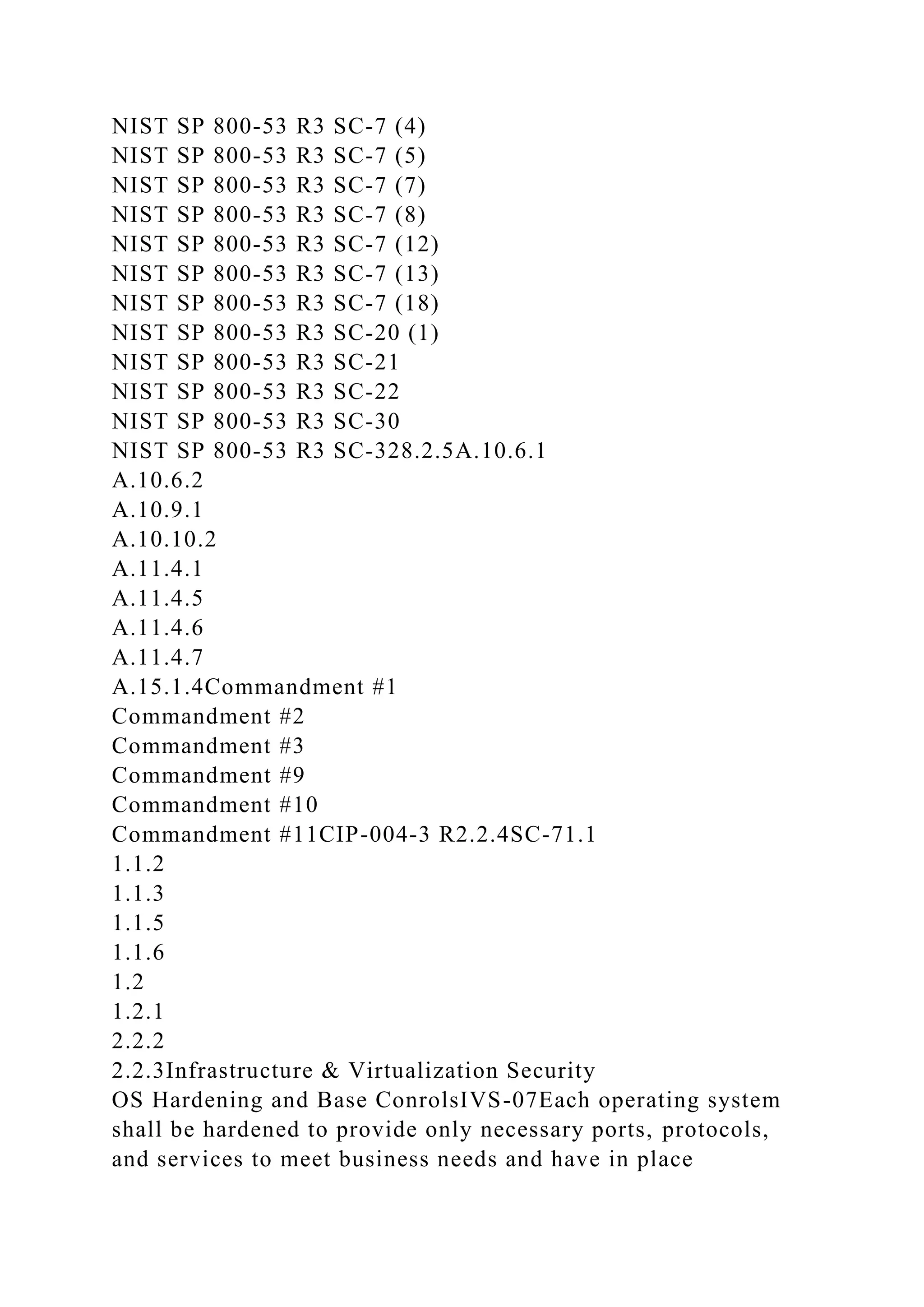
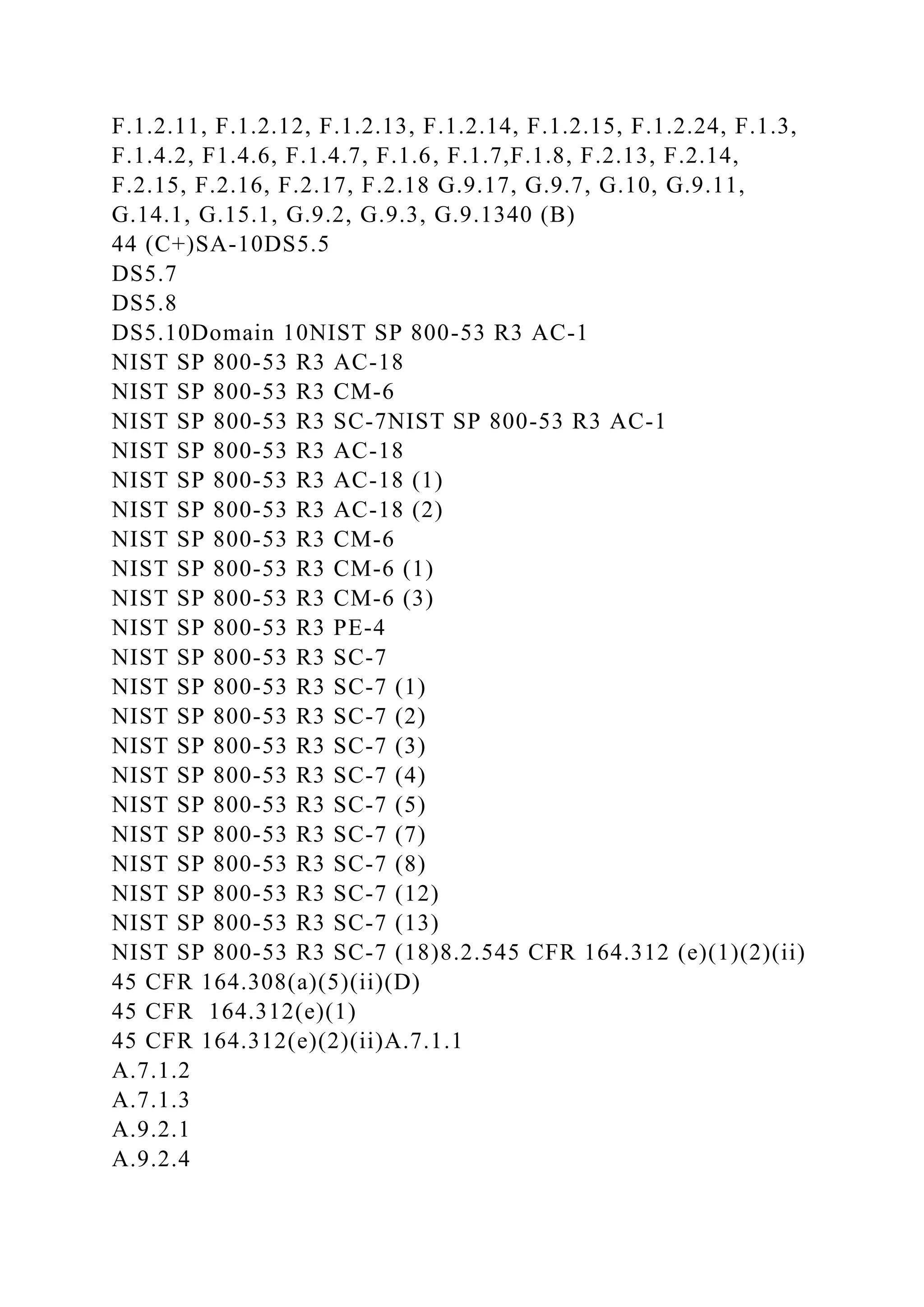
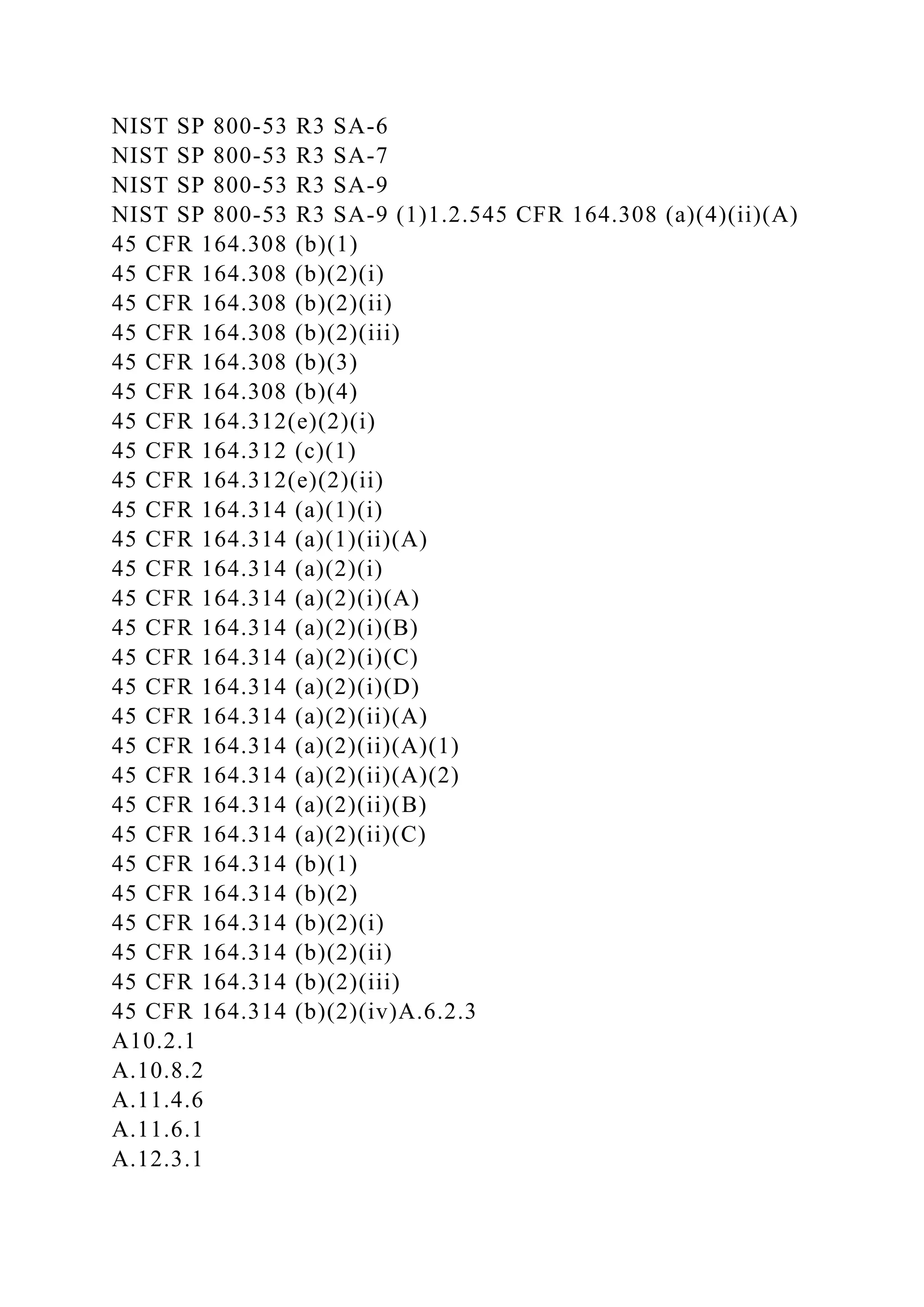
![x3.1.0(S3.1.0) Procedures exist to (1) identify potential threats
of disruption to systems operation that would impair system
security commitments and (2) assess the risks associated with
the identified threats.
(x3.1.0) Procedures exist to (1) identify potential threats of
disruptions to systems operations that would impair system
[availability, processing integrity, confidentiality] commitments
and (2) assess the risks associated with the identified
threats.L.1, L.2, L.4, L.7, L.976 (B)
77 (B)
78 (B)
83 (B)
84 (B)
85 (B)CO-05ME 3.1Domain 2, 46.10. (a)
6.10. (b)
6.10. (c)
6.10. (d)
6.10. (e)
6.10. (f)
6.10. (g)
6.10. (h)
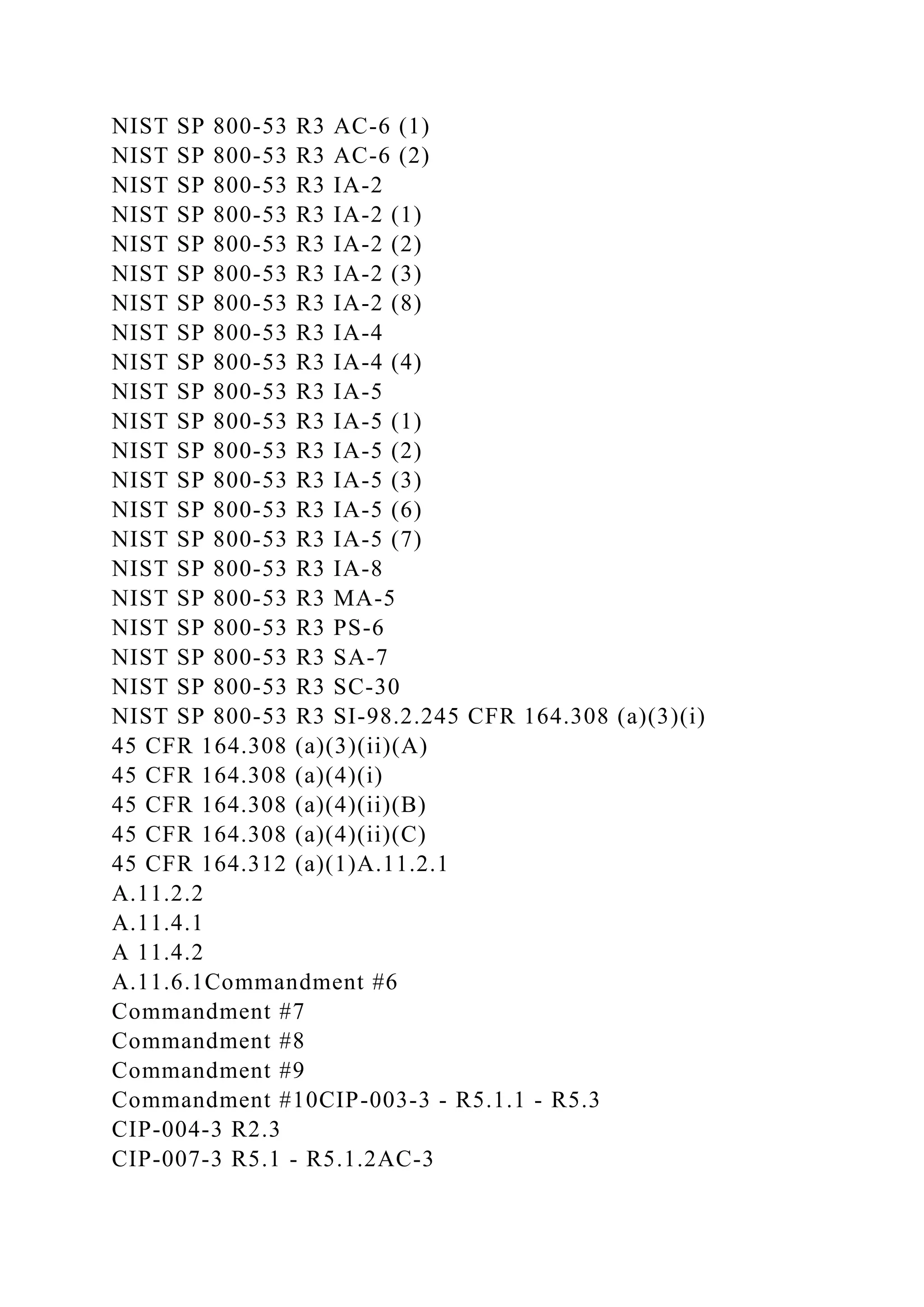
6.10. (i)NIST SP 800-53 R3 AC-1
NIST SP 800-53 R3 AT-1
NIST SP 800-53 R3 AU-1
NIST SP 800-53 R3 CA-1
NIST SP 800-53 R3 CM-1
NIST SP 800-53 R3 CP-1
NIST SP 800-53 R3 IA-1
NIST SP 800-53 R3 IA-7
NIST SP 800-53 R3 IR-1
NIST SP 800-53 R3 MA-1](https://image.slidesharecdn.com/csaccmv3-230108121115-6a39b129/75/CSA-CCM-V3-0CLOUD-CONTROLS-MATRIX-VERSION-3-0Control-DomainCCM-V3-docx-11-2048.jpg)
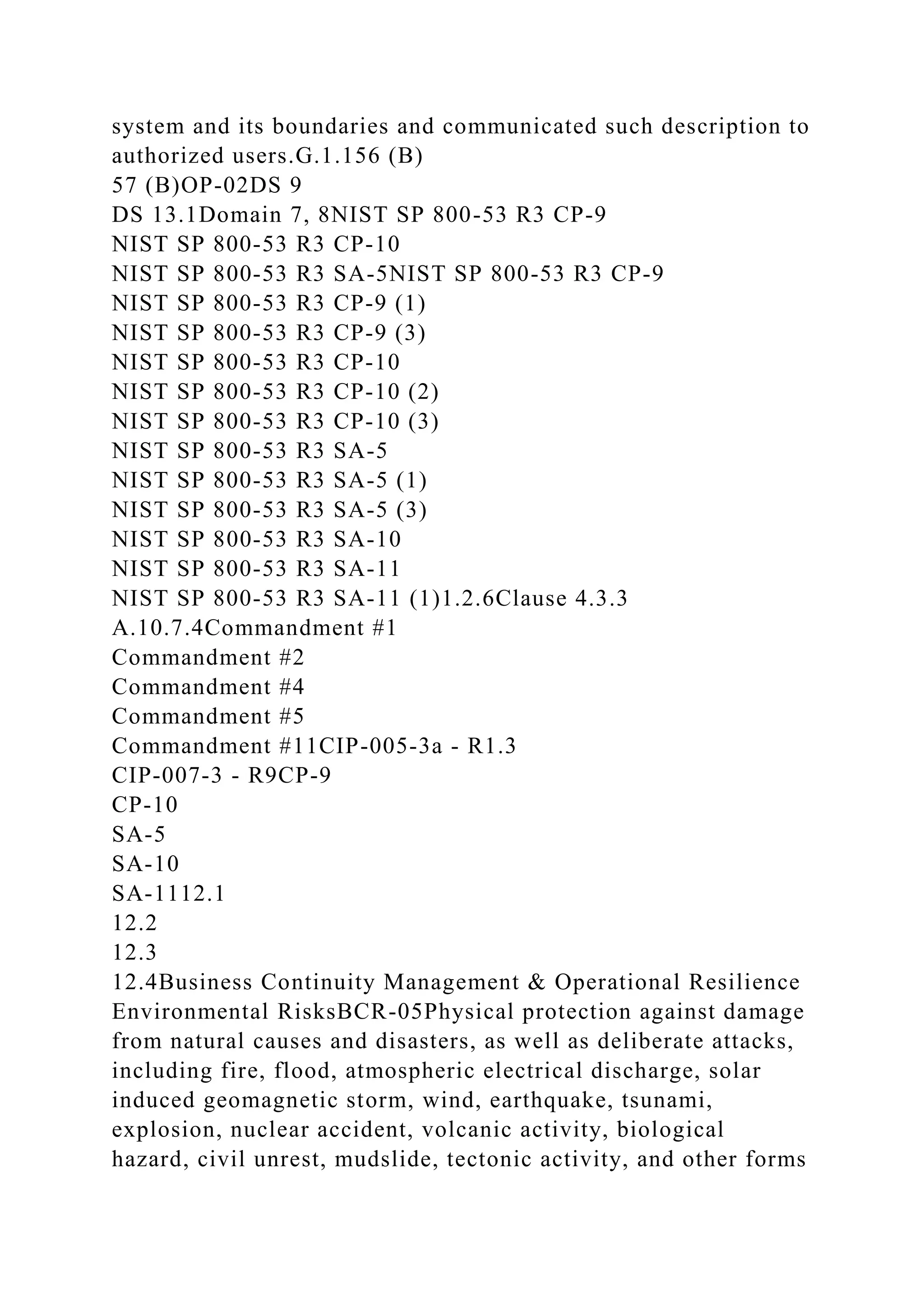
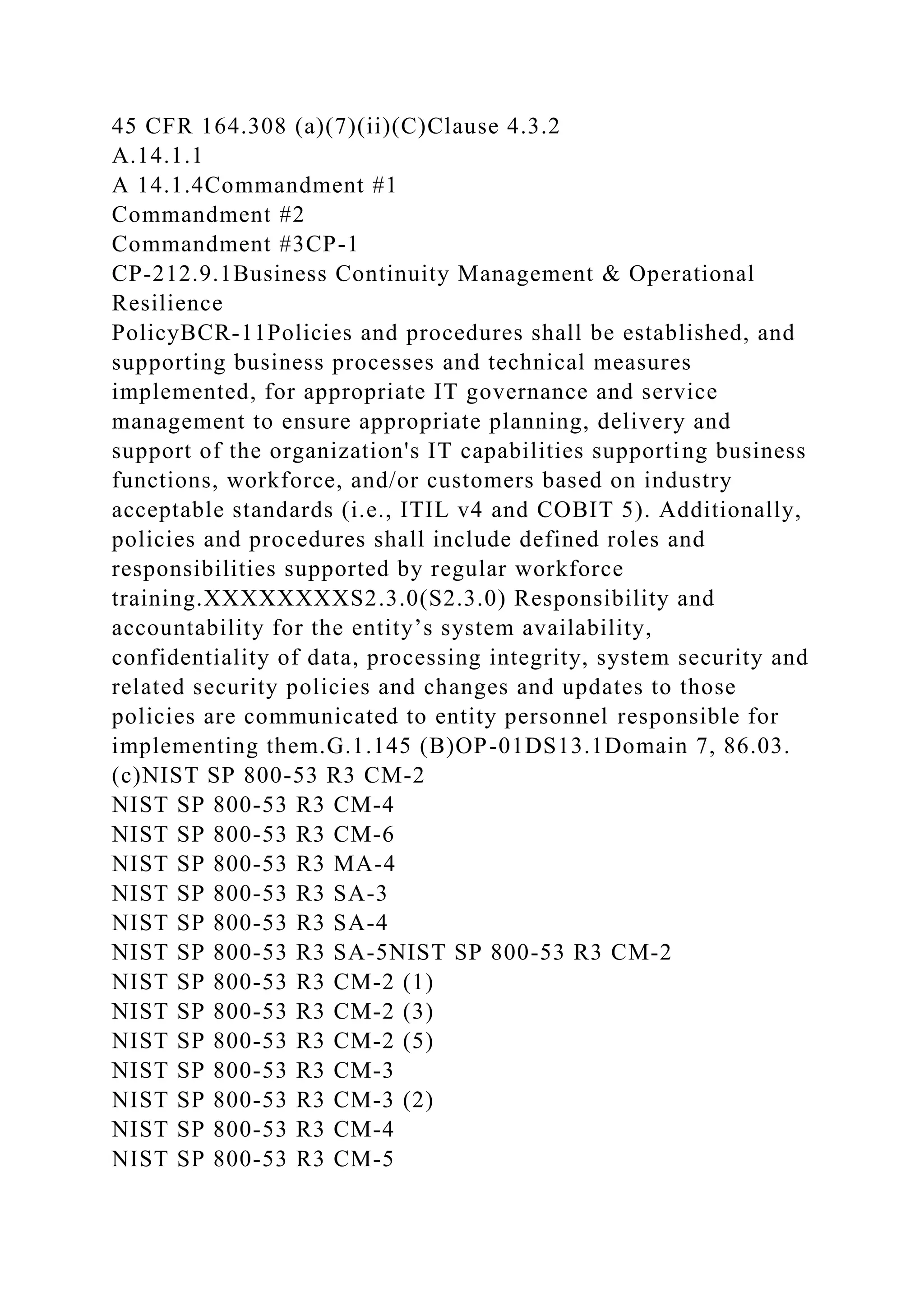
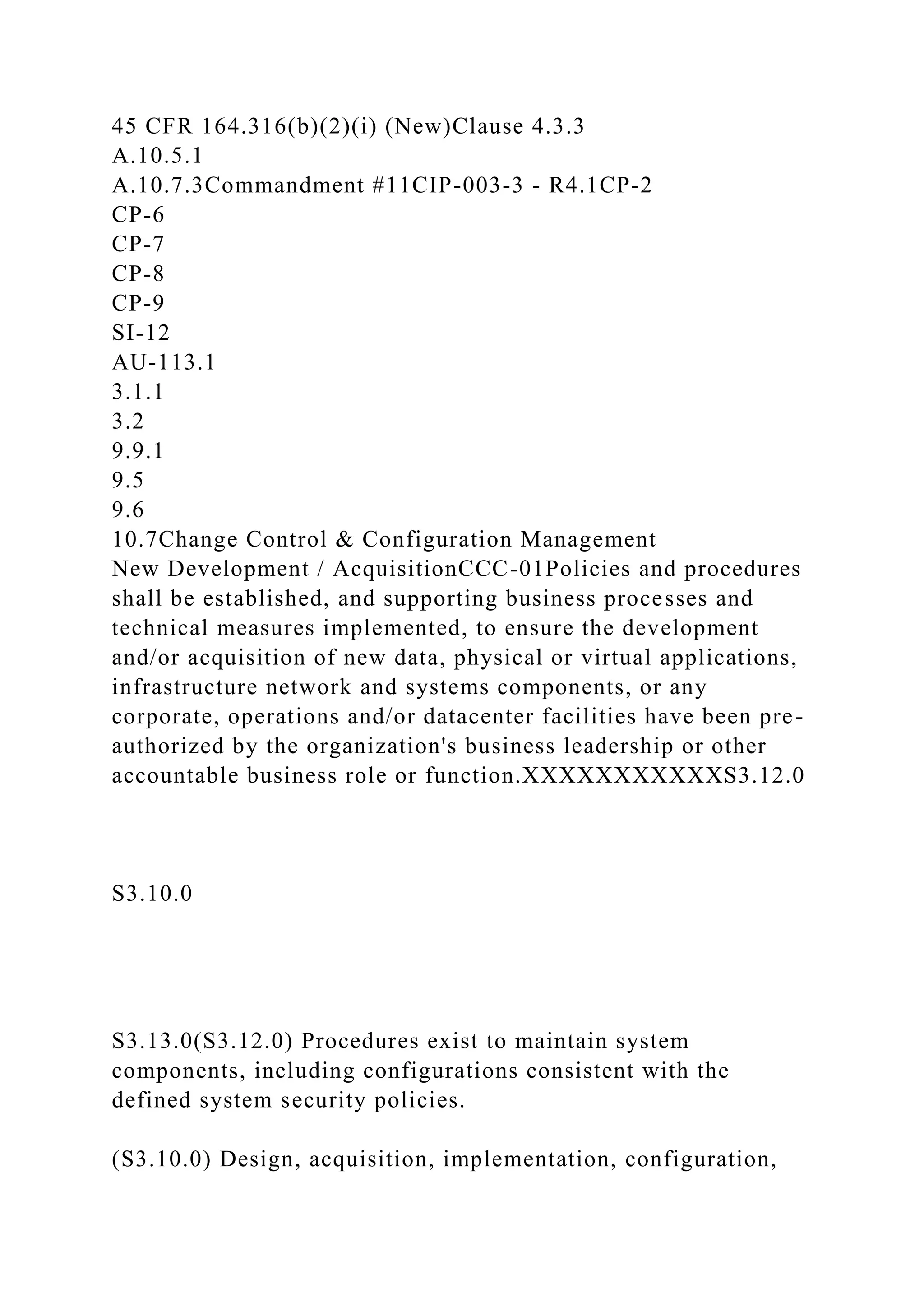
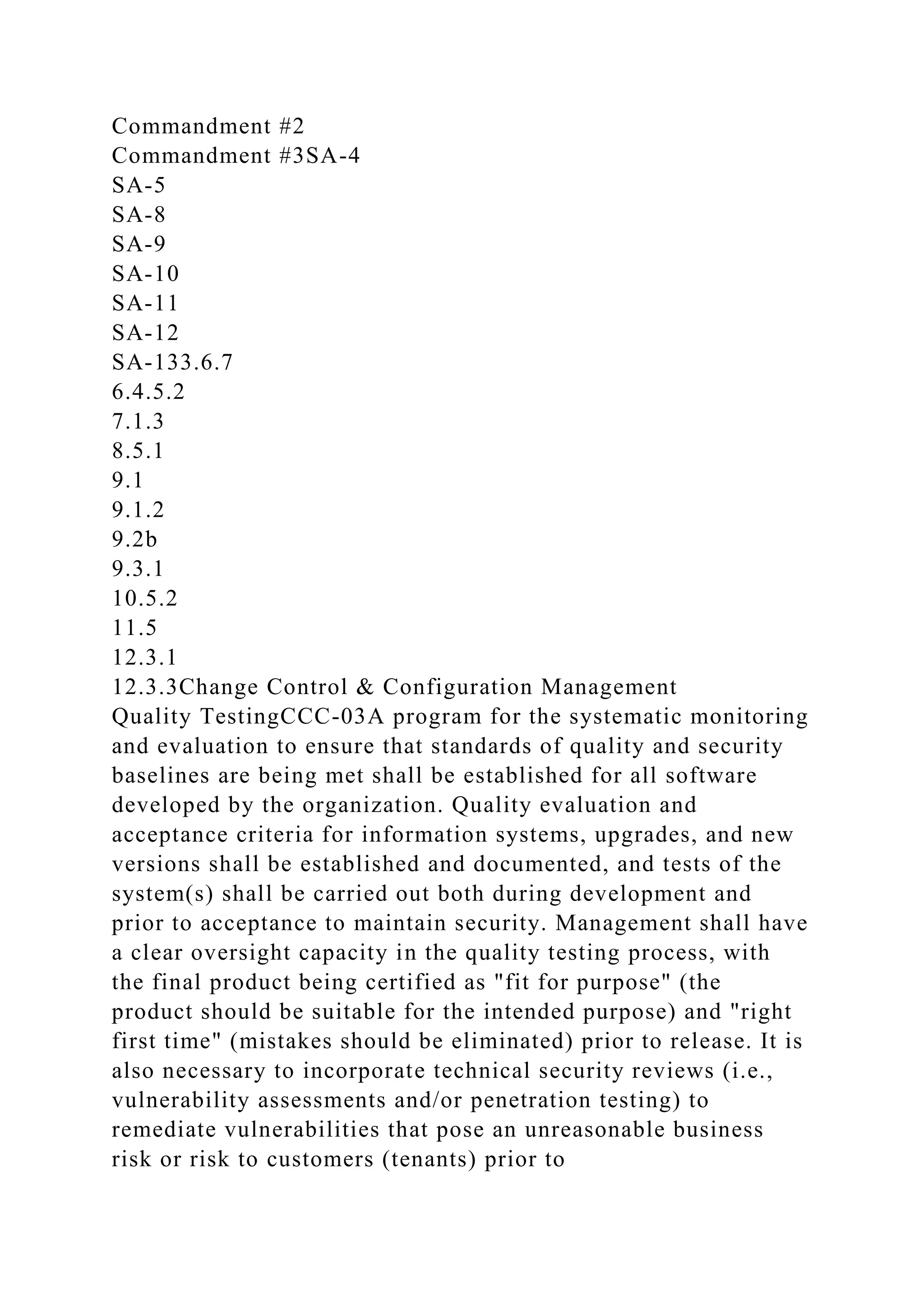
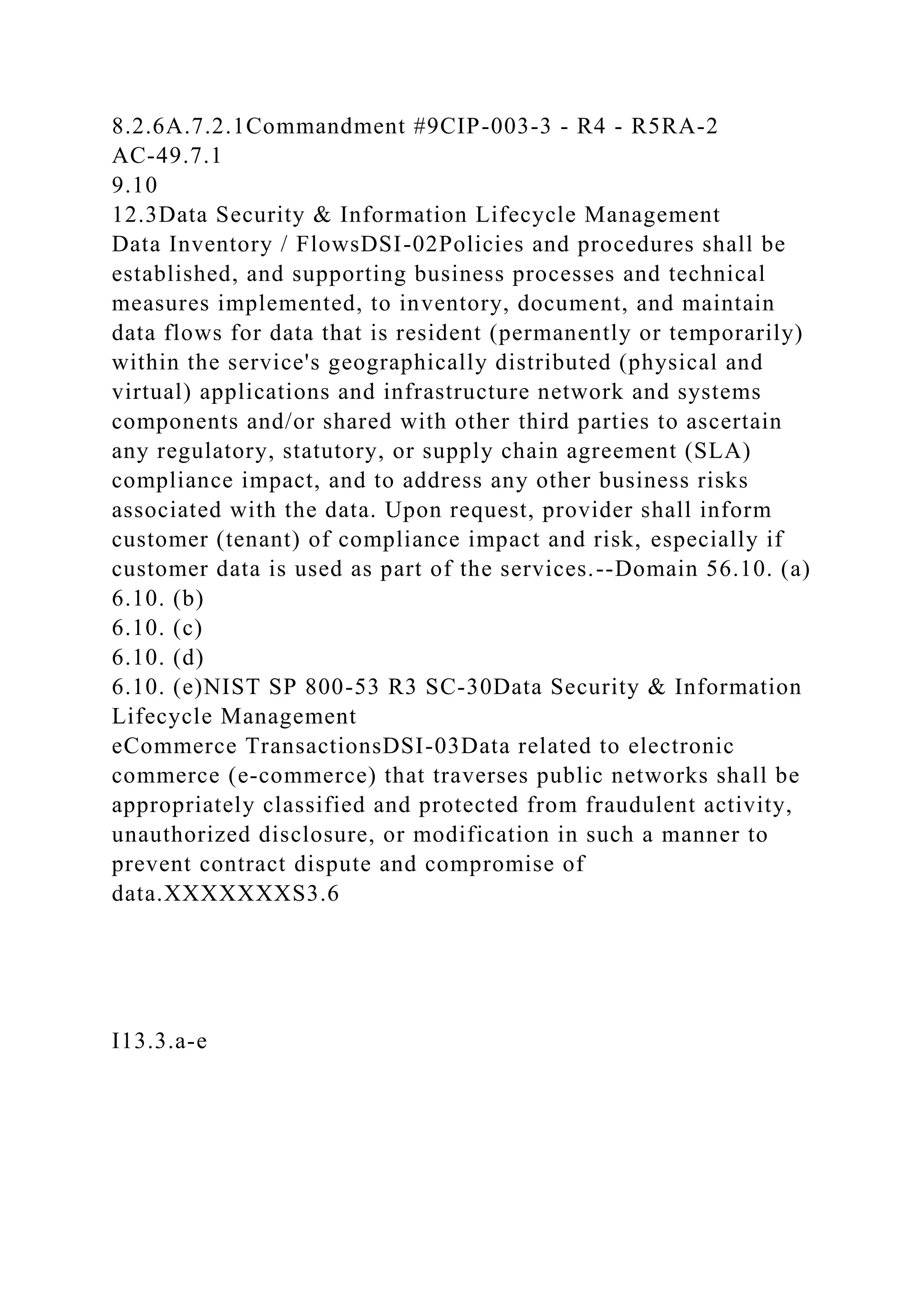
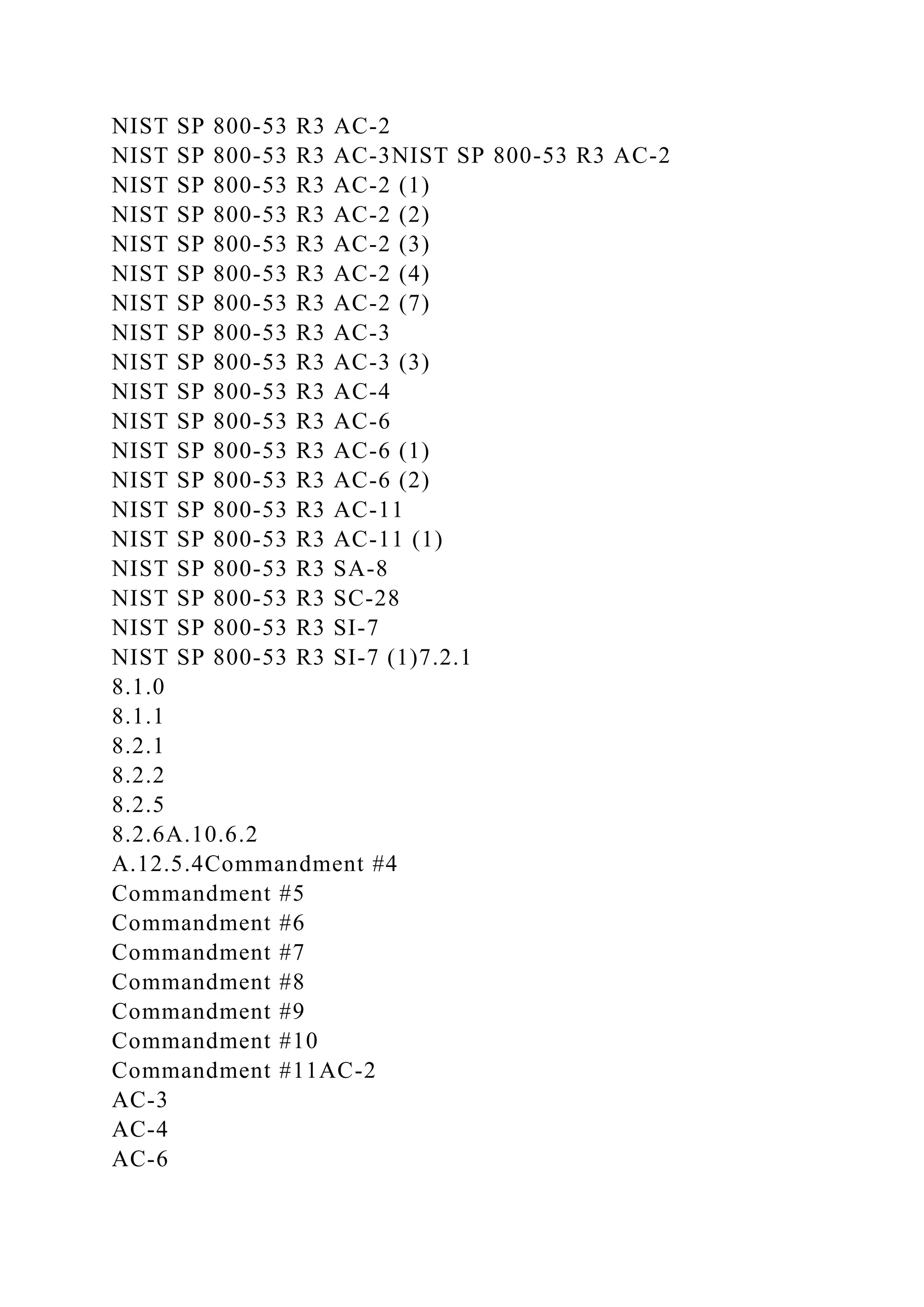
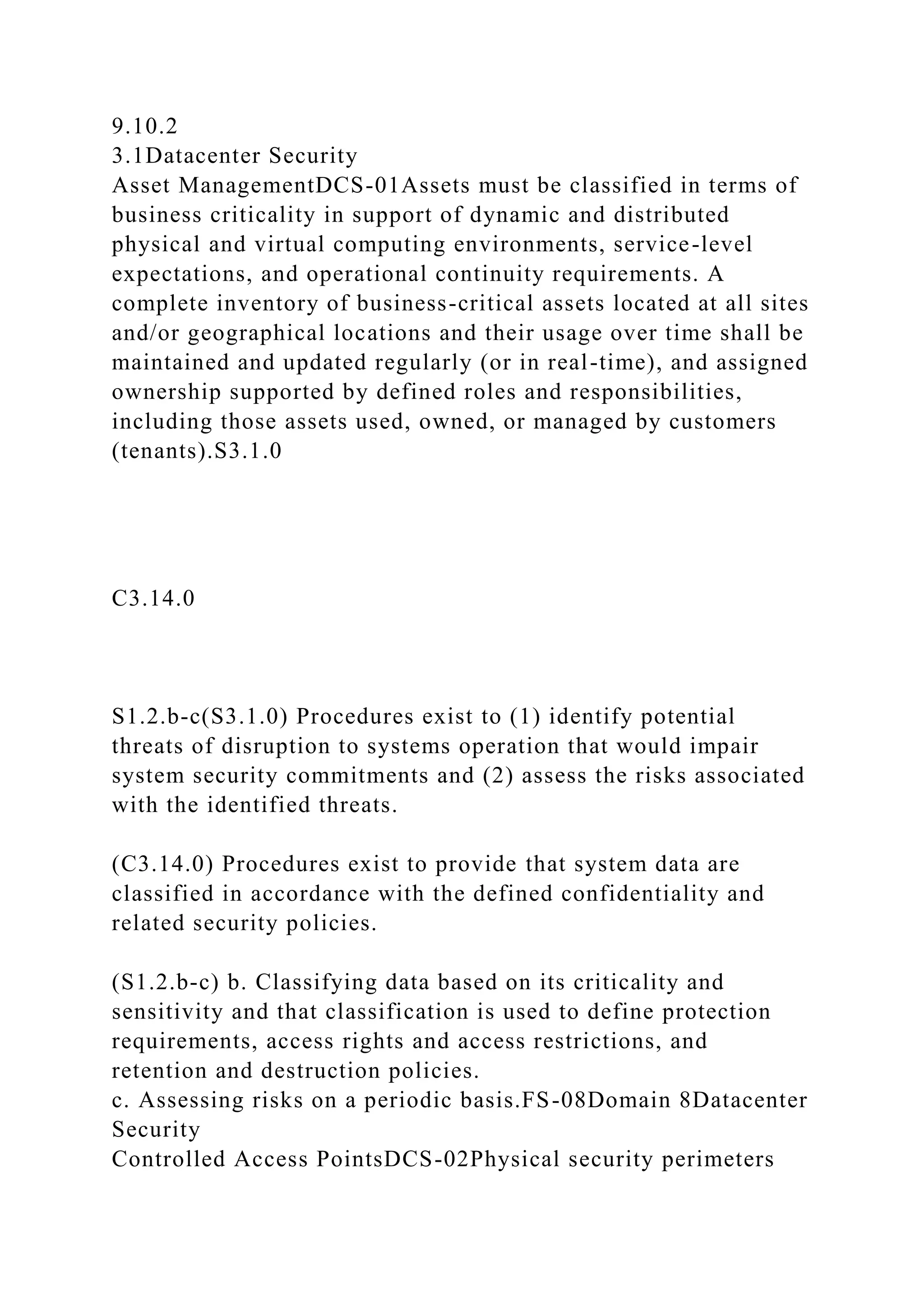
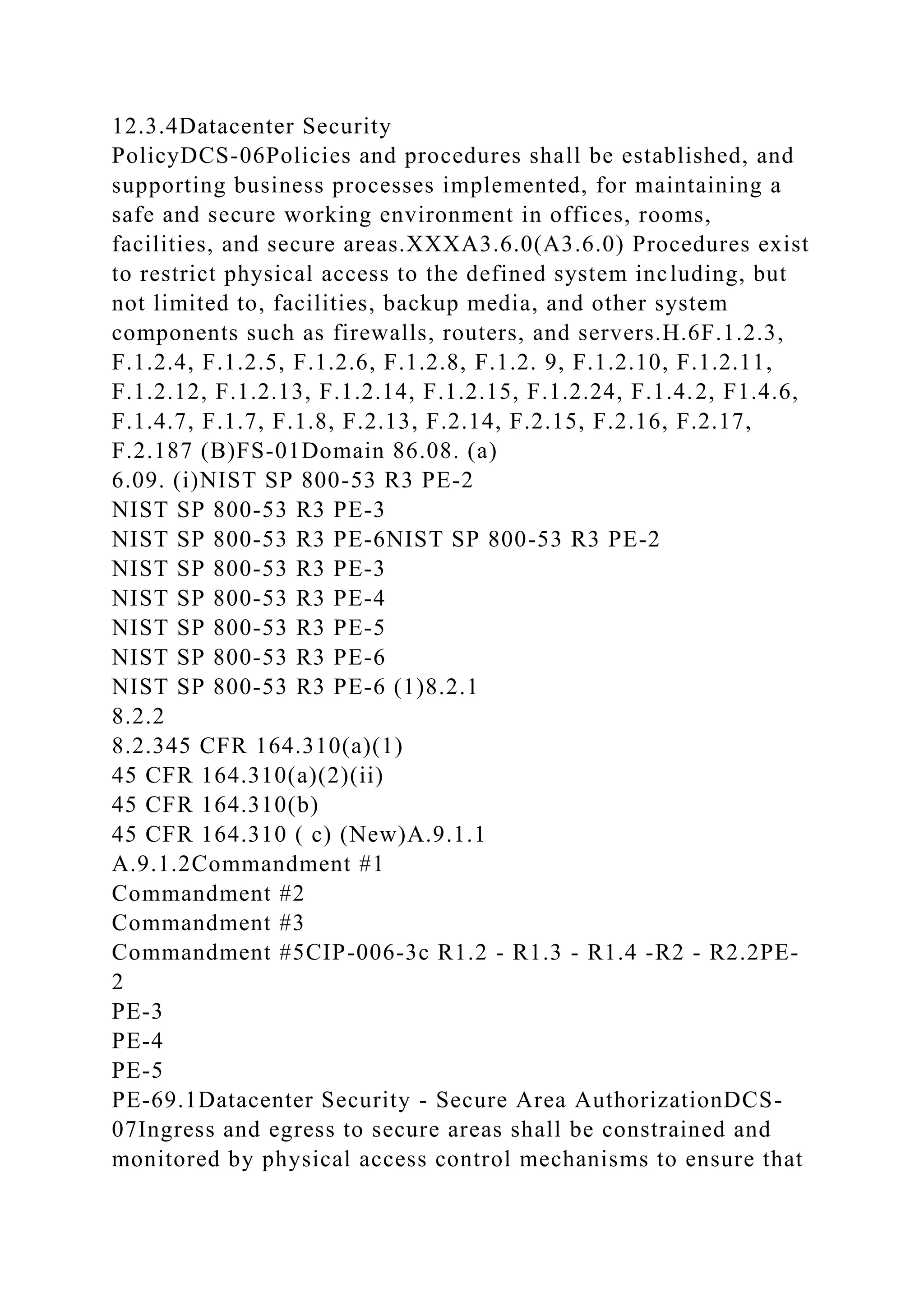
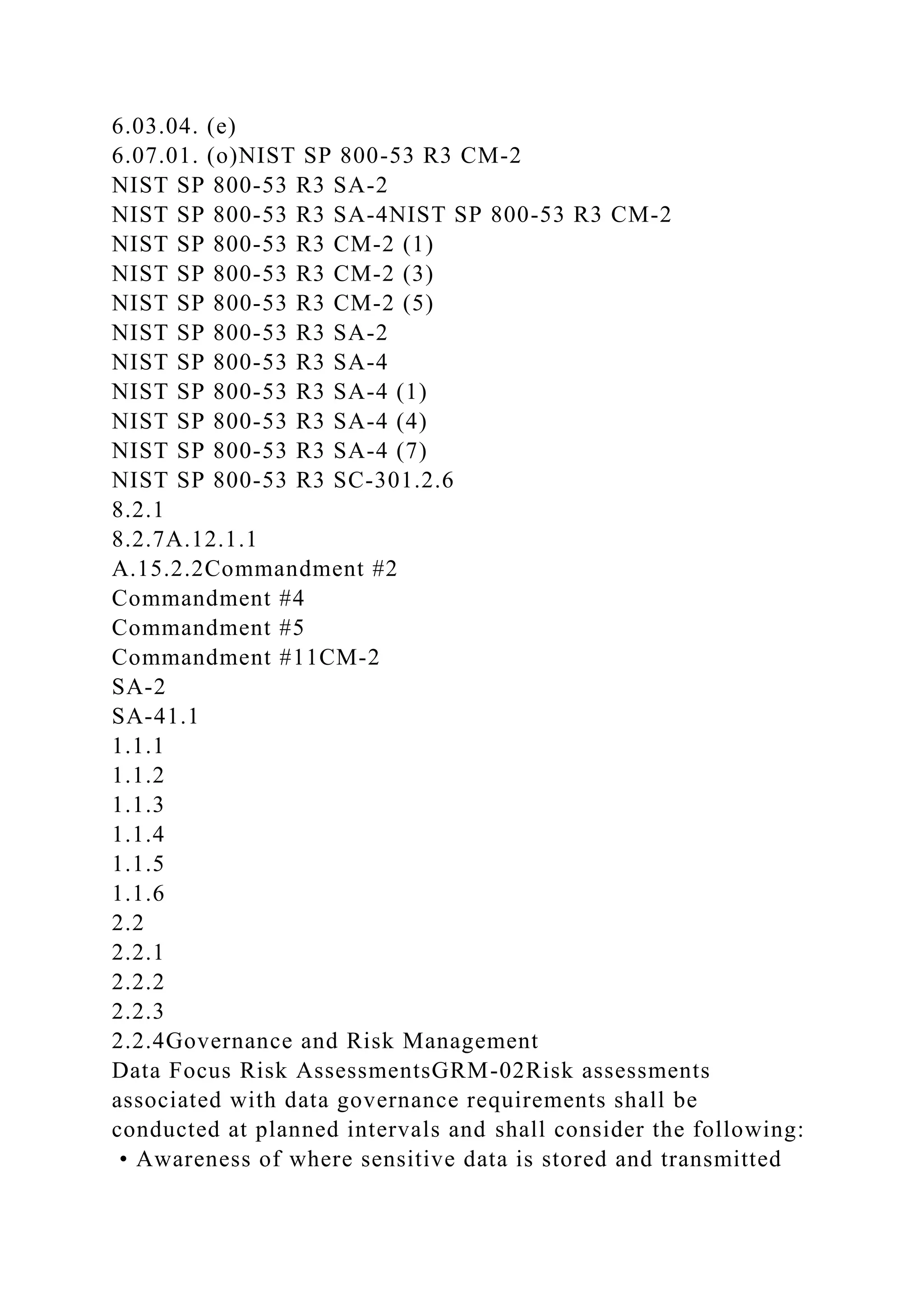
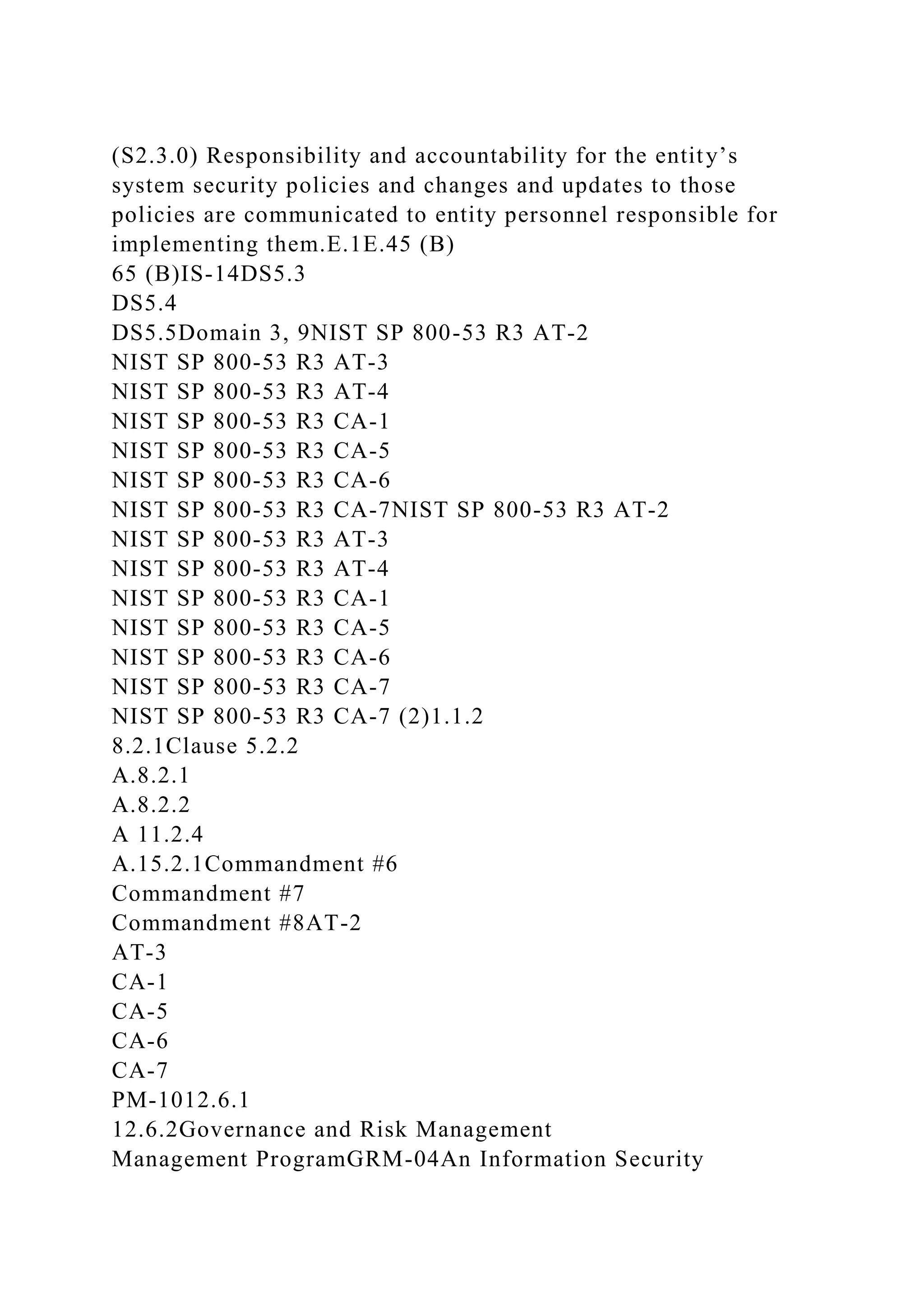
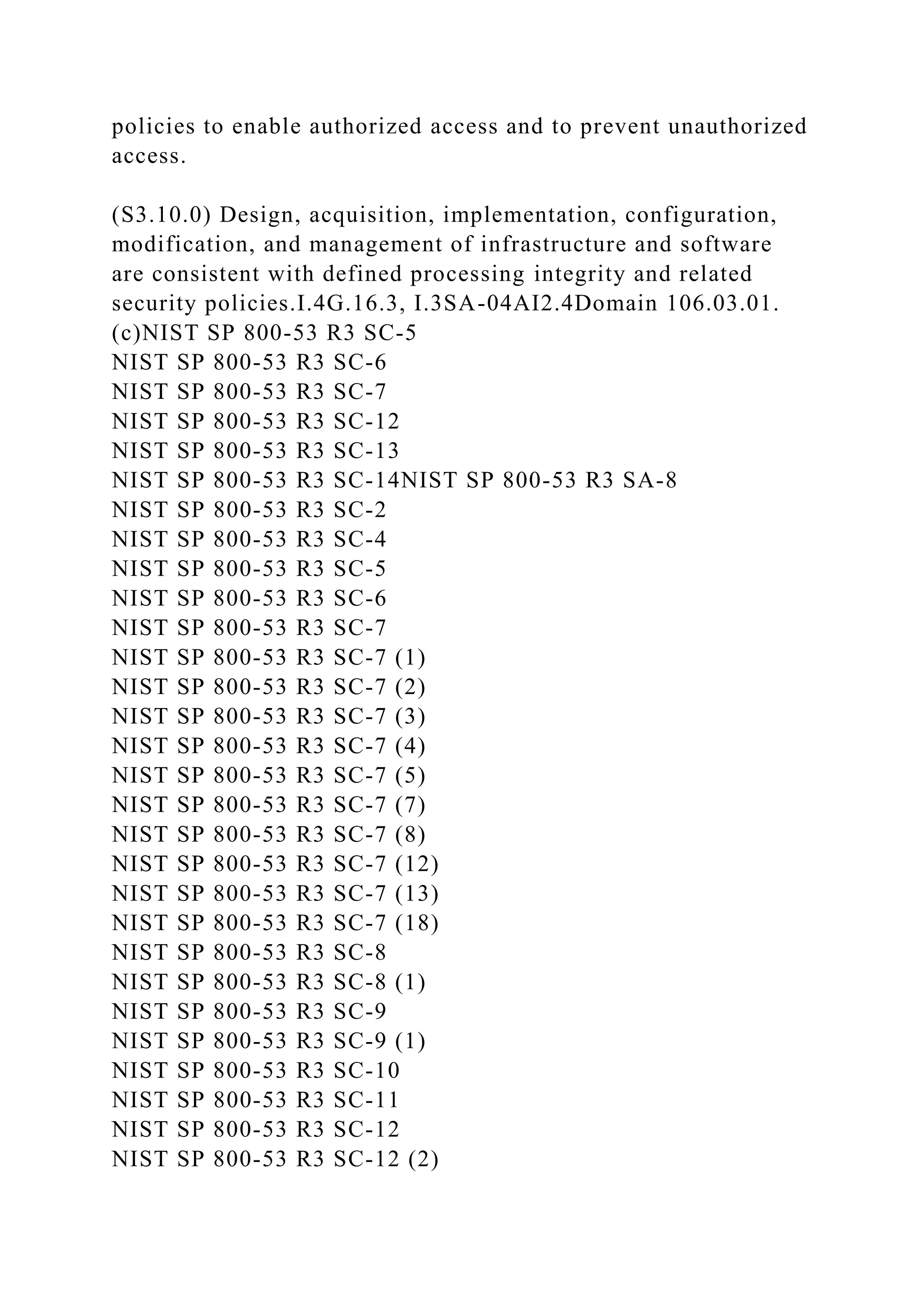
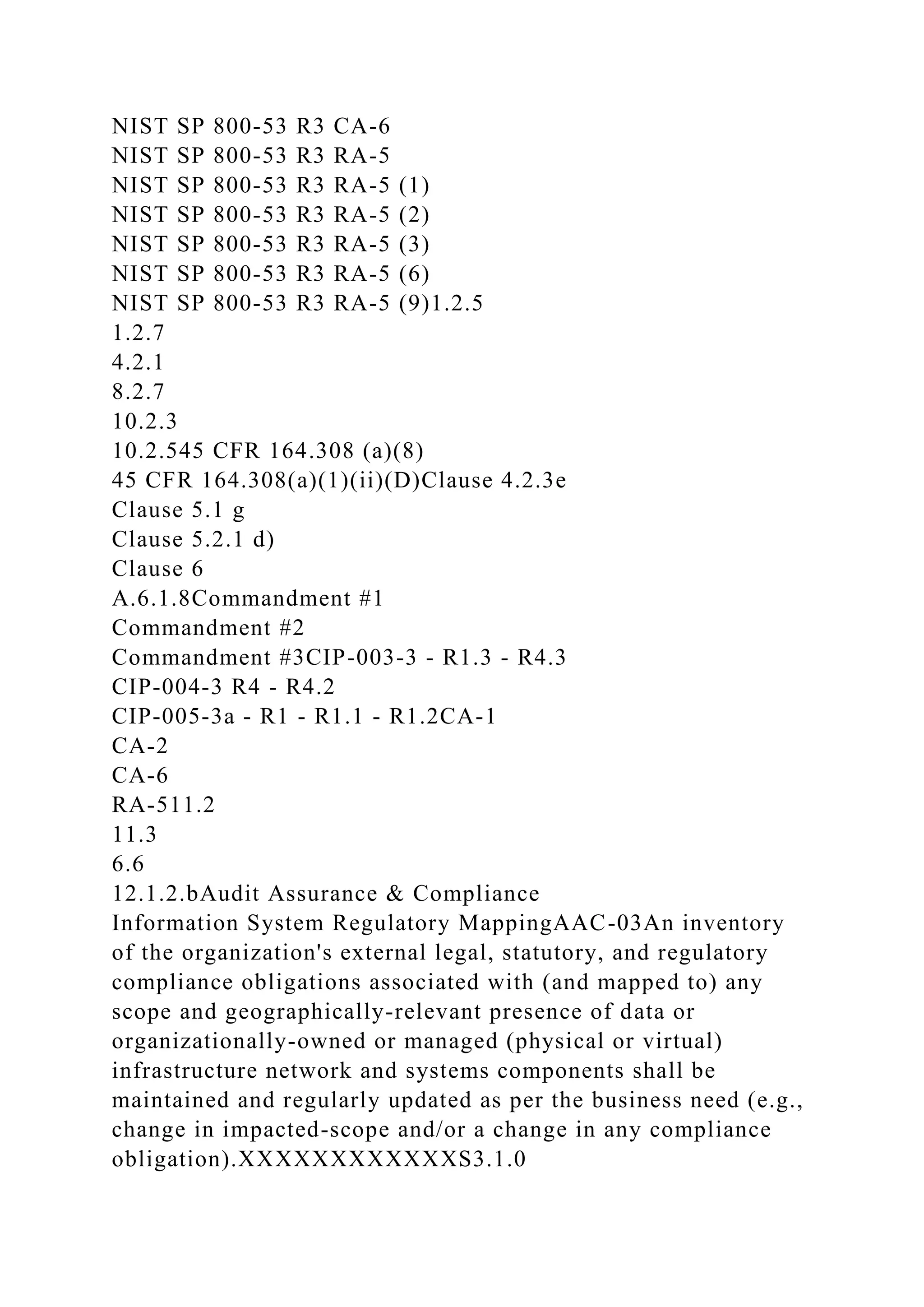
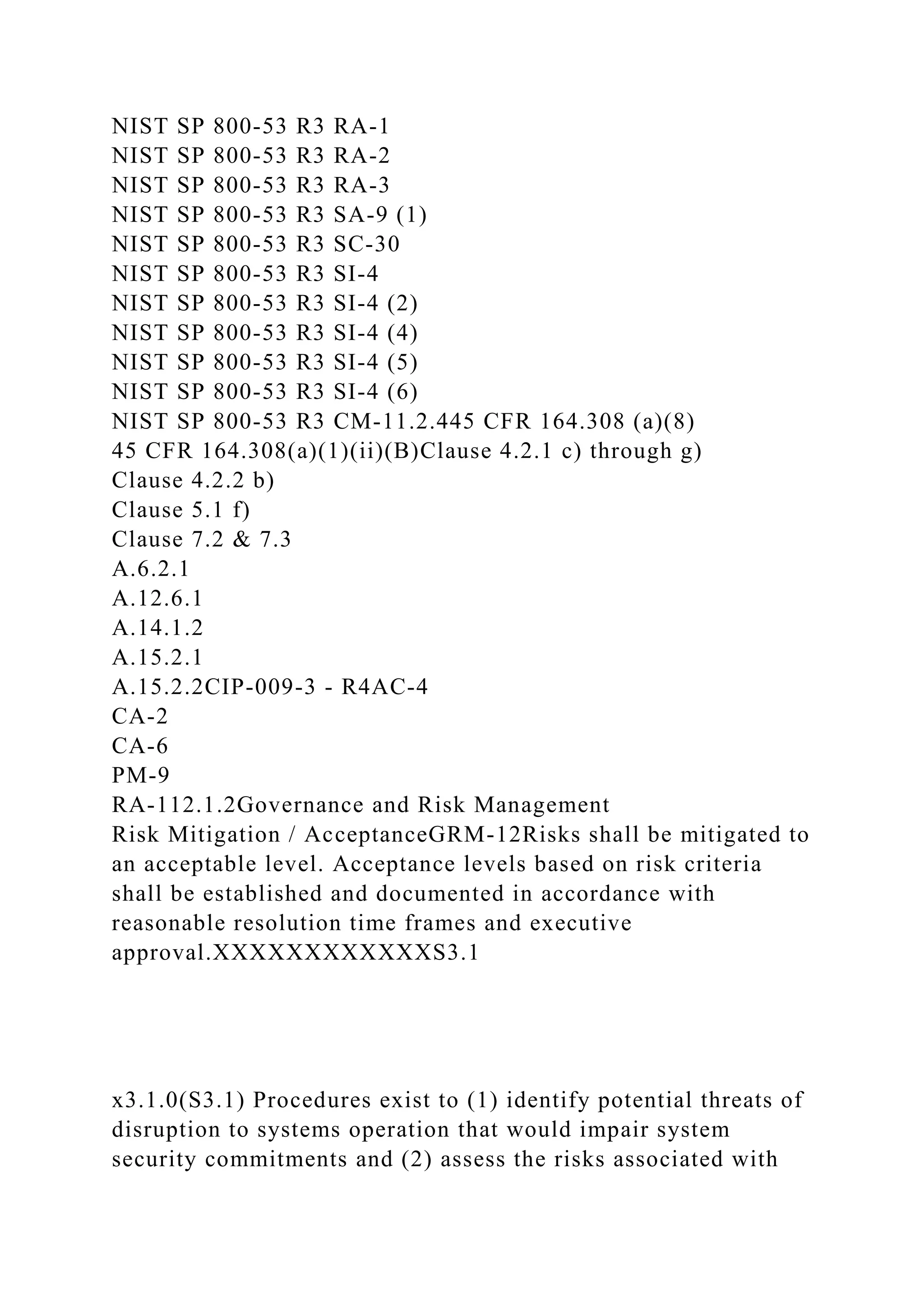
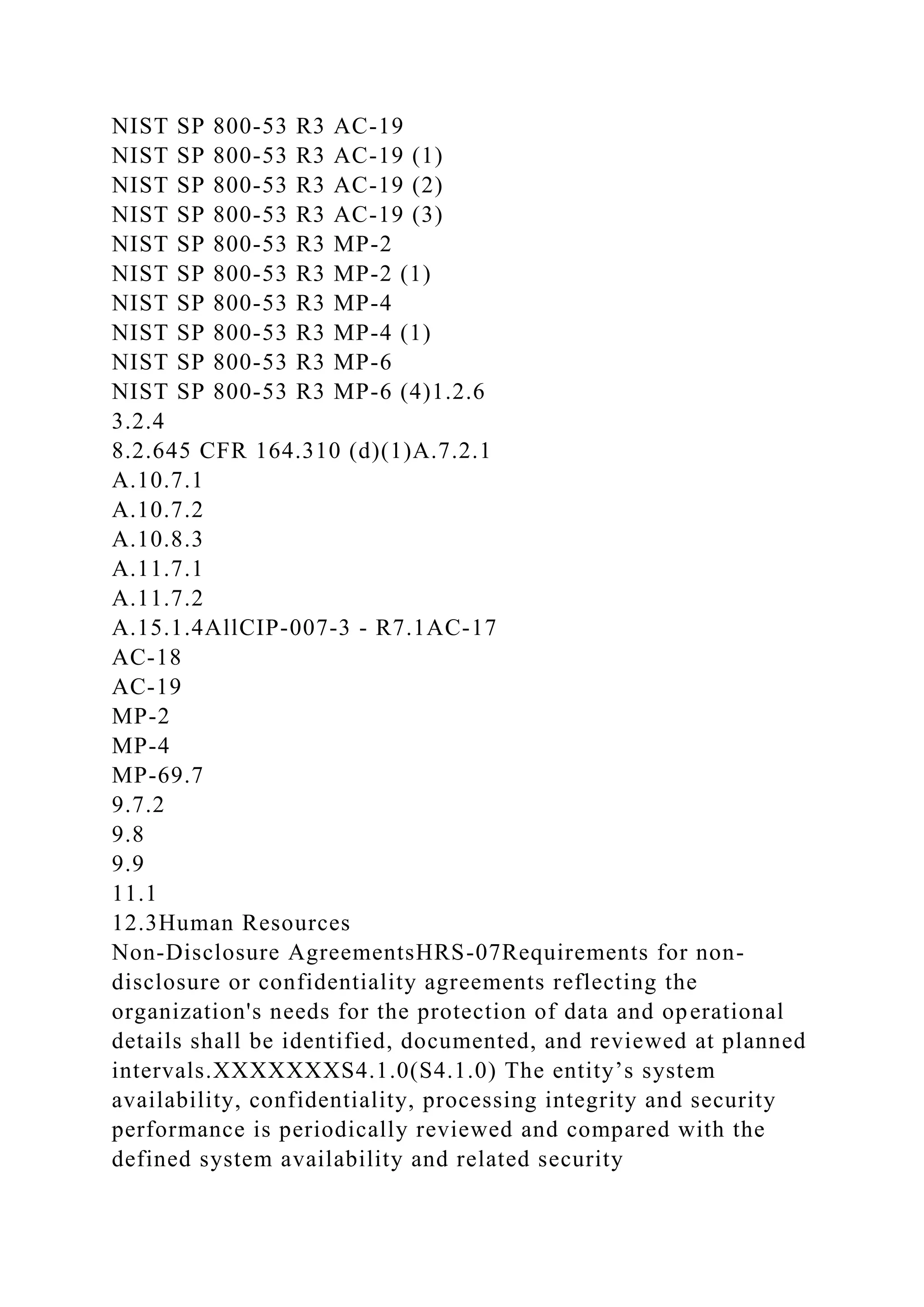
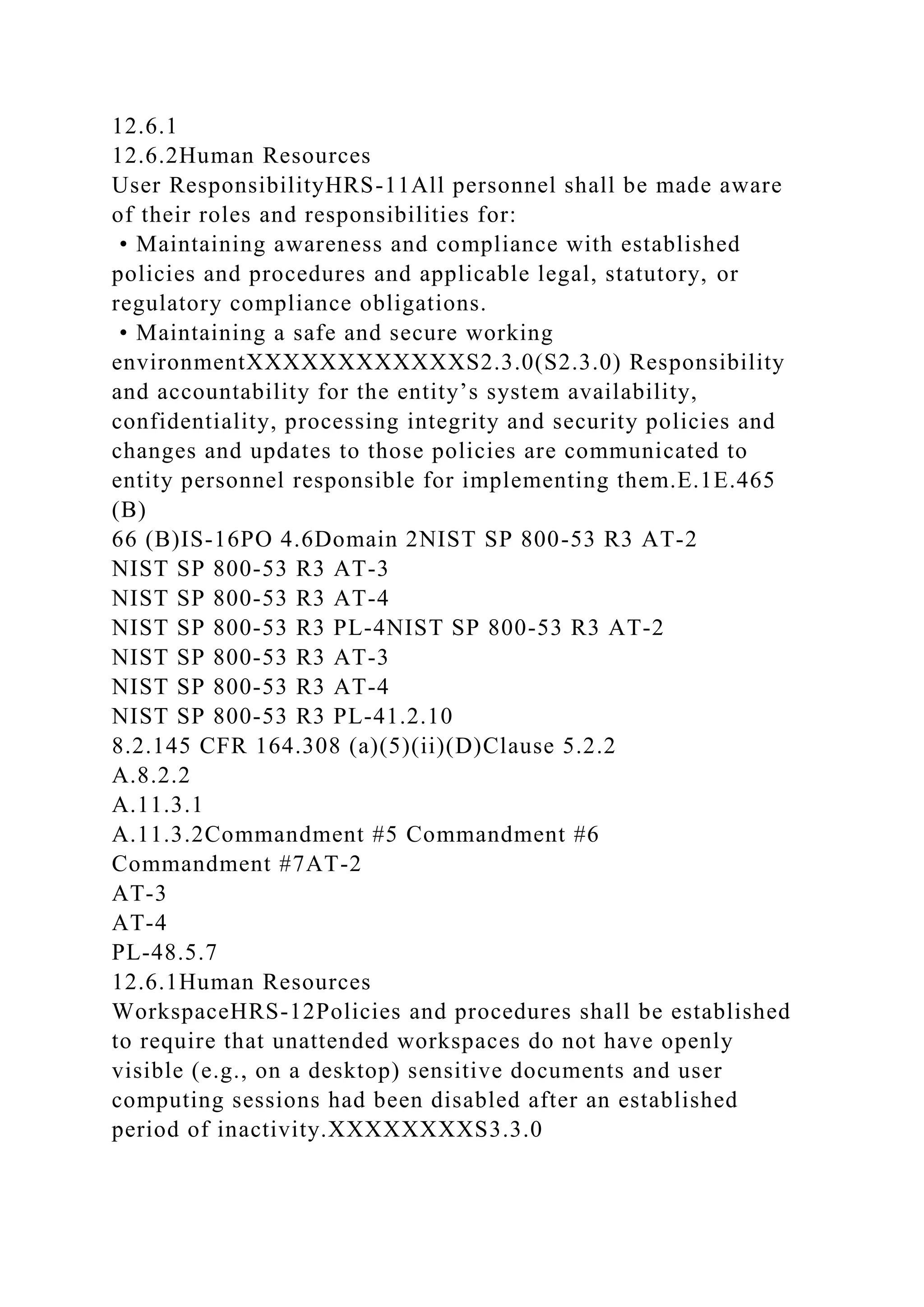
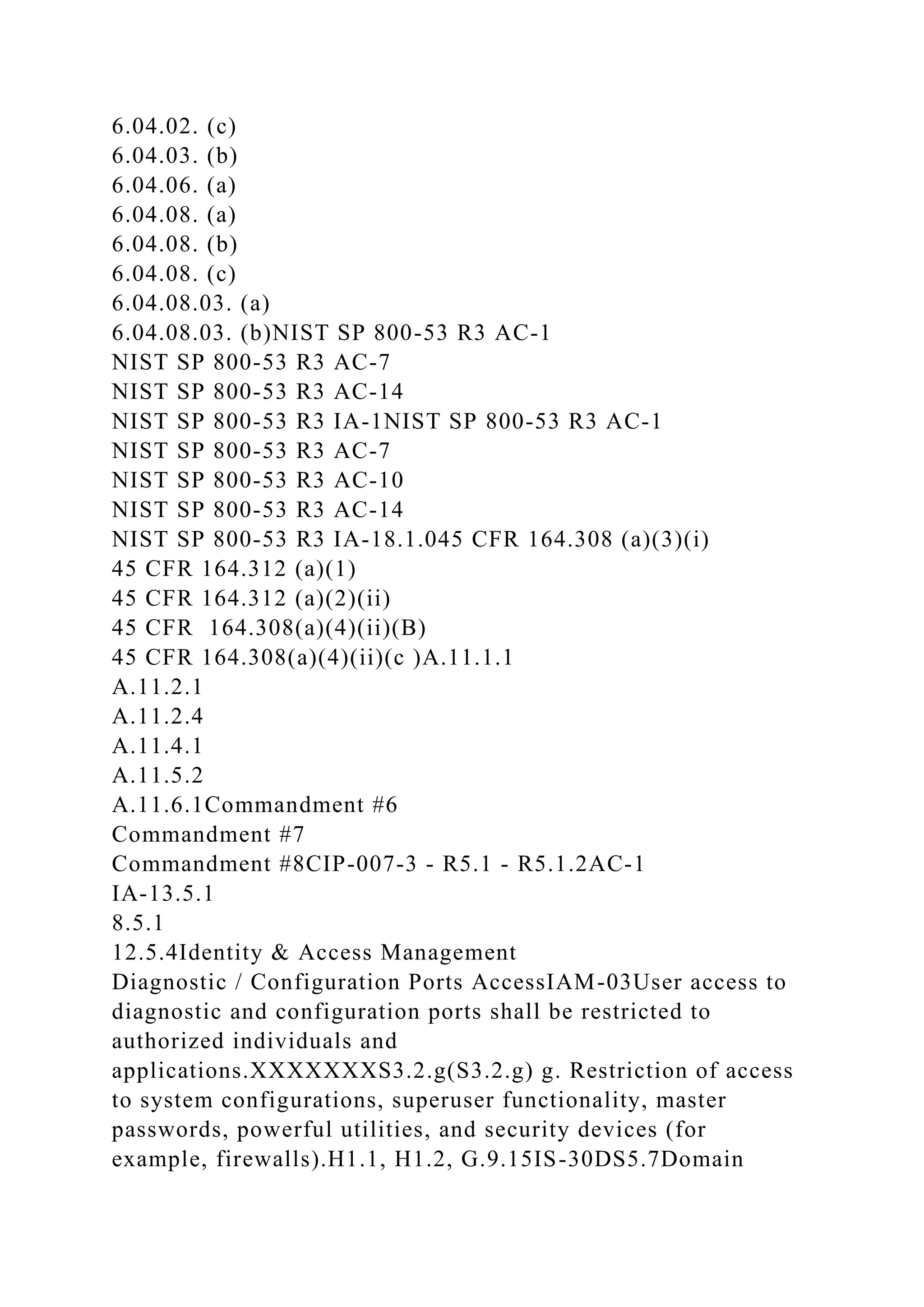
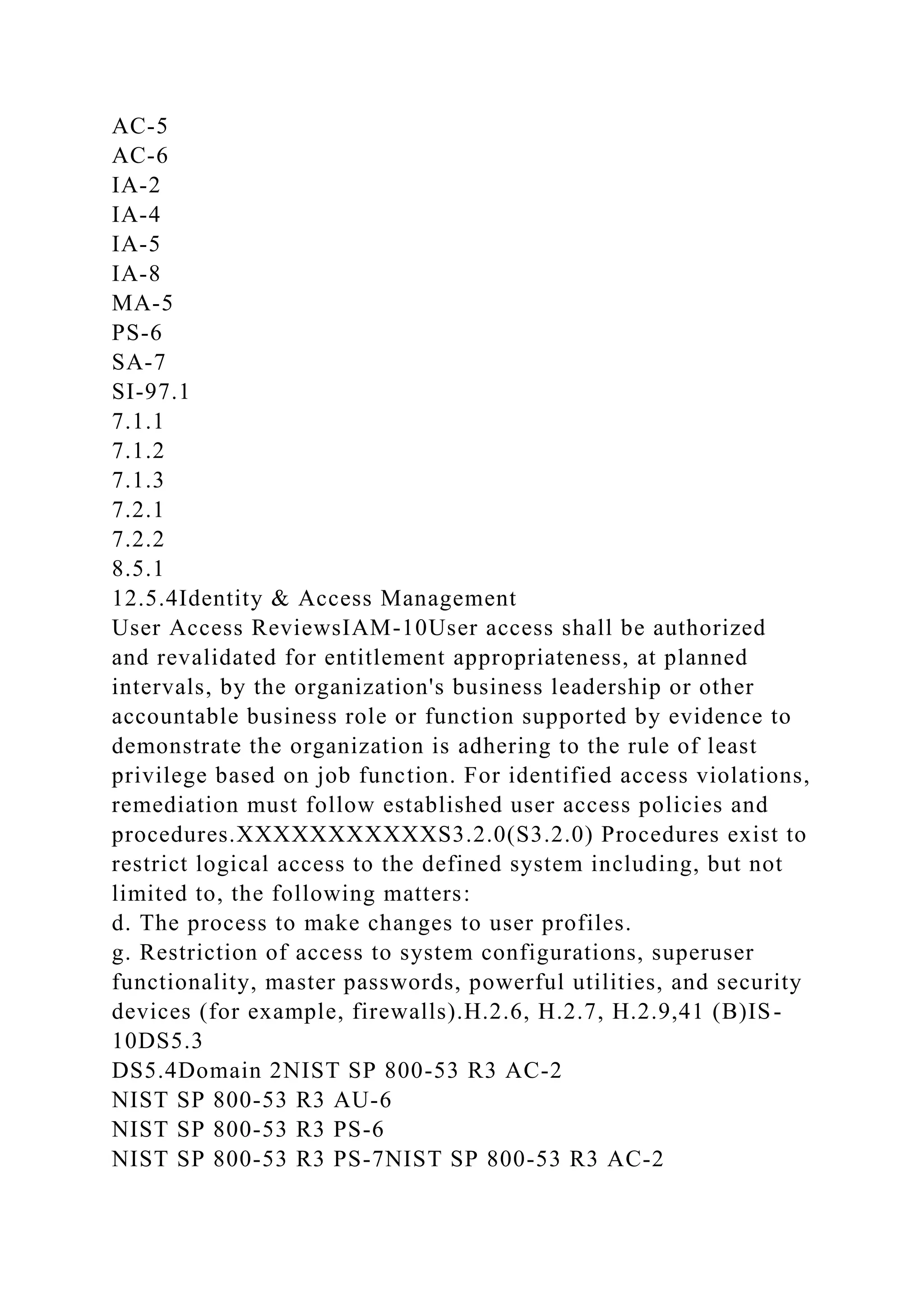
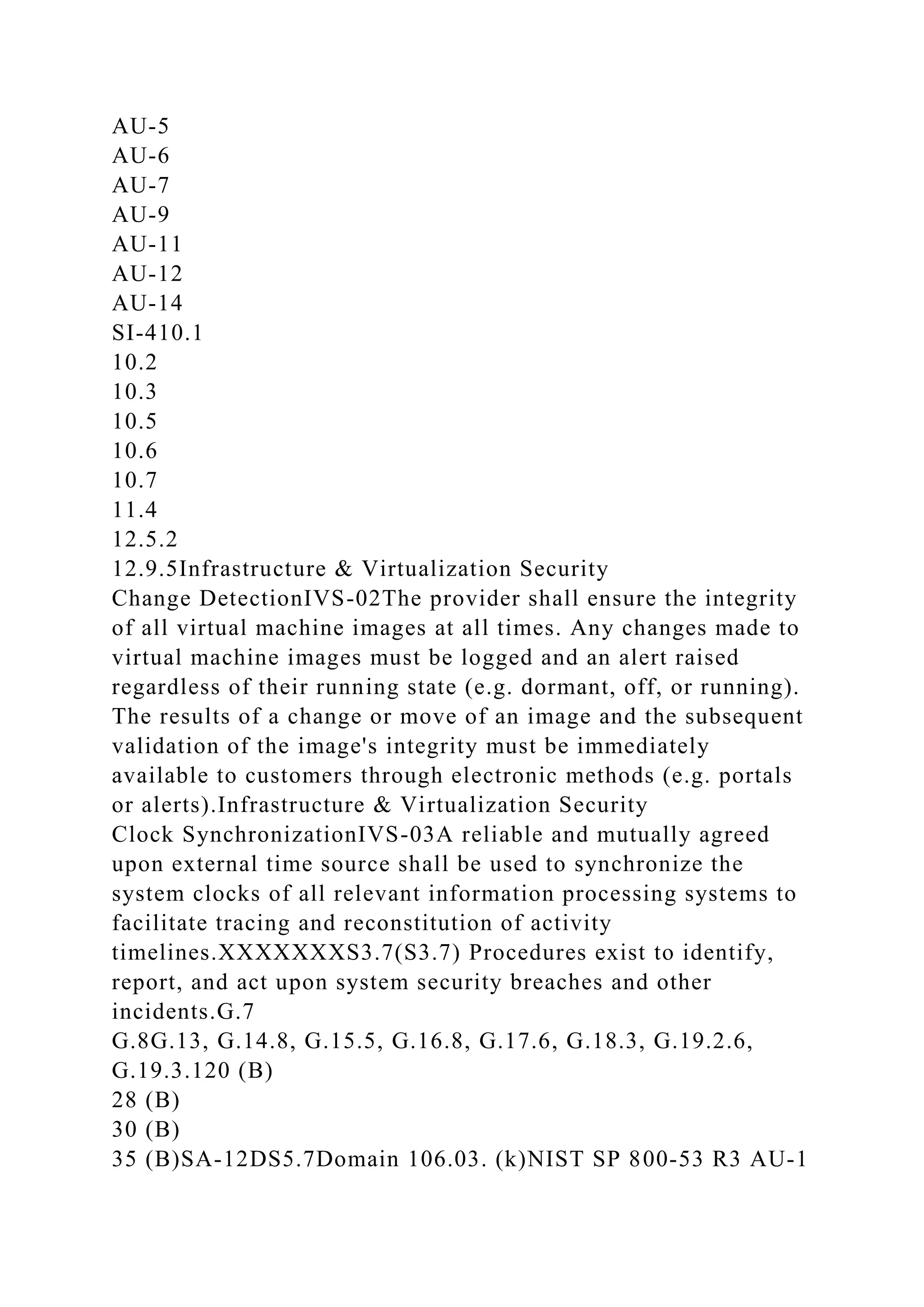
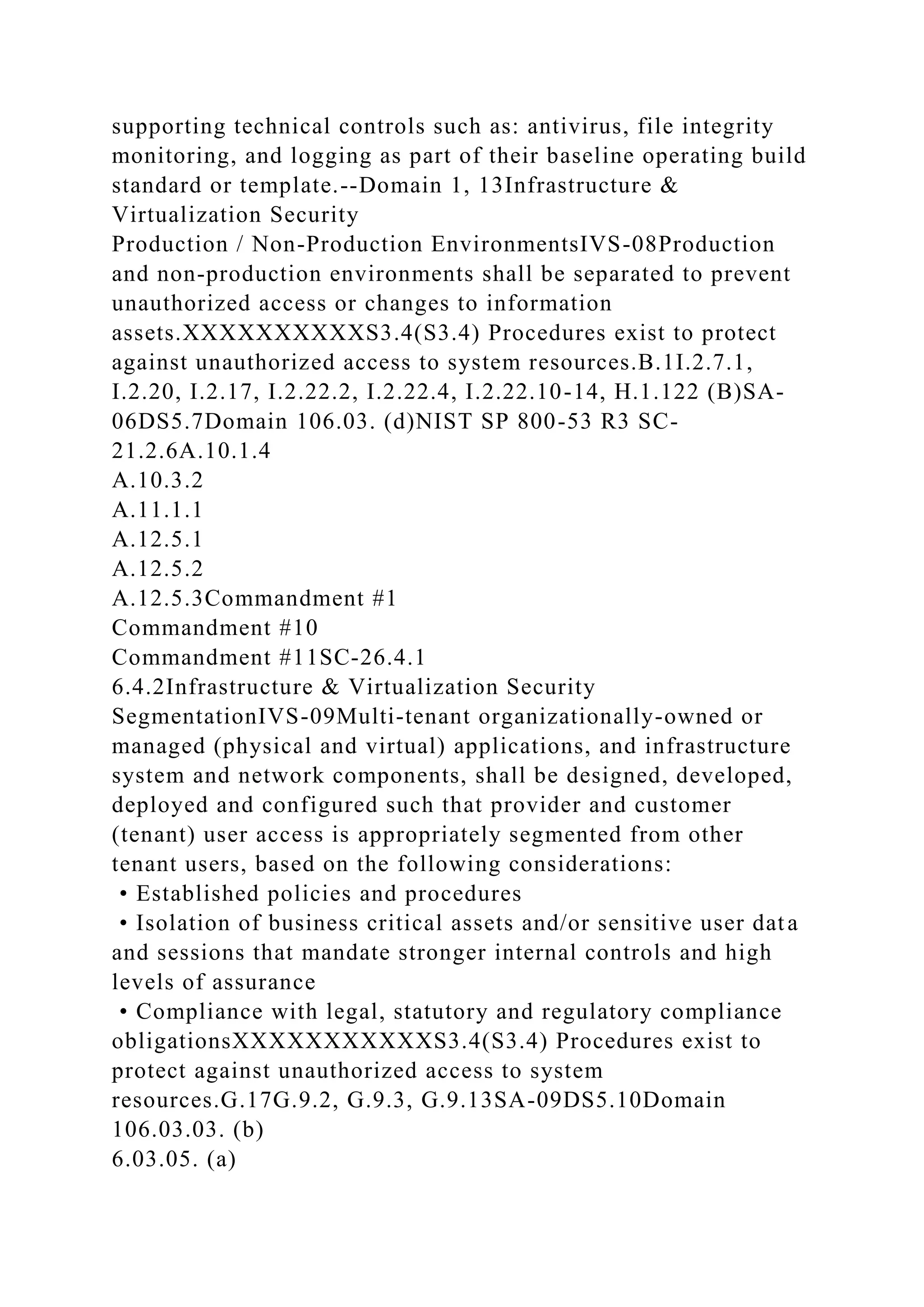
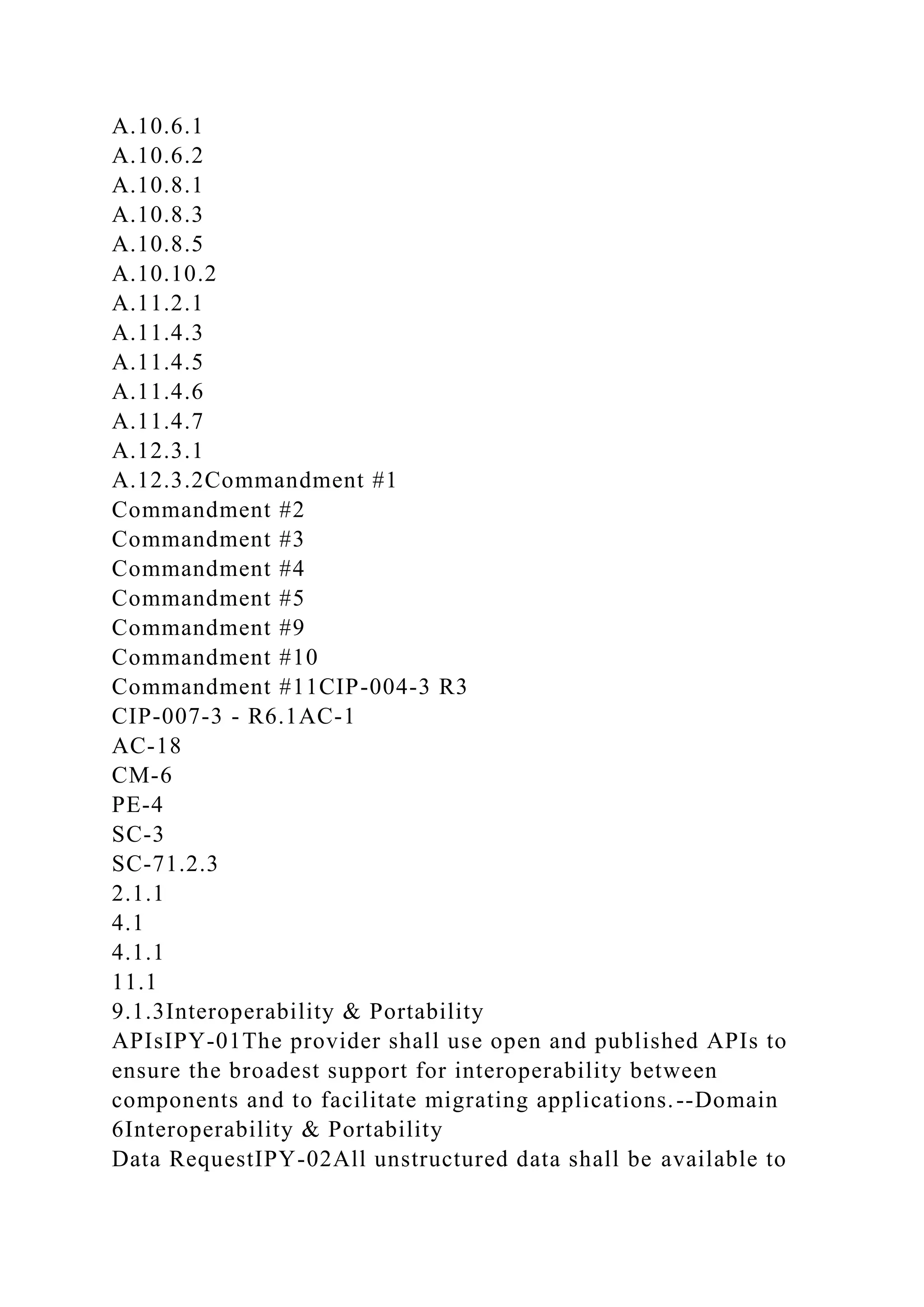
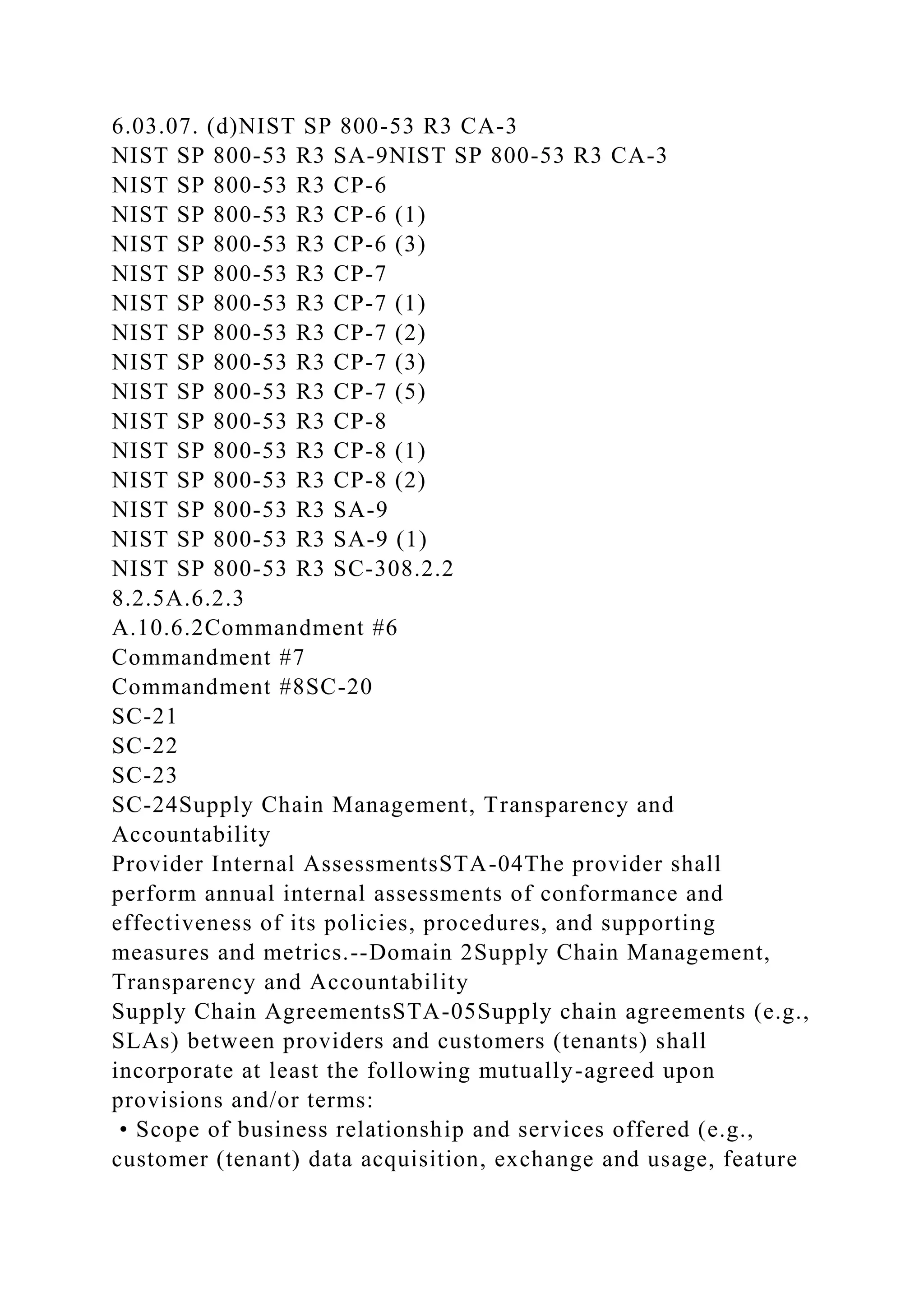
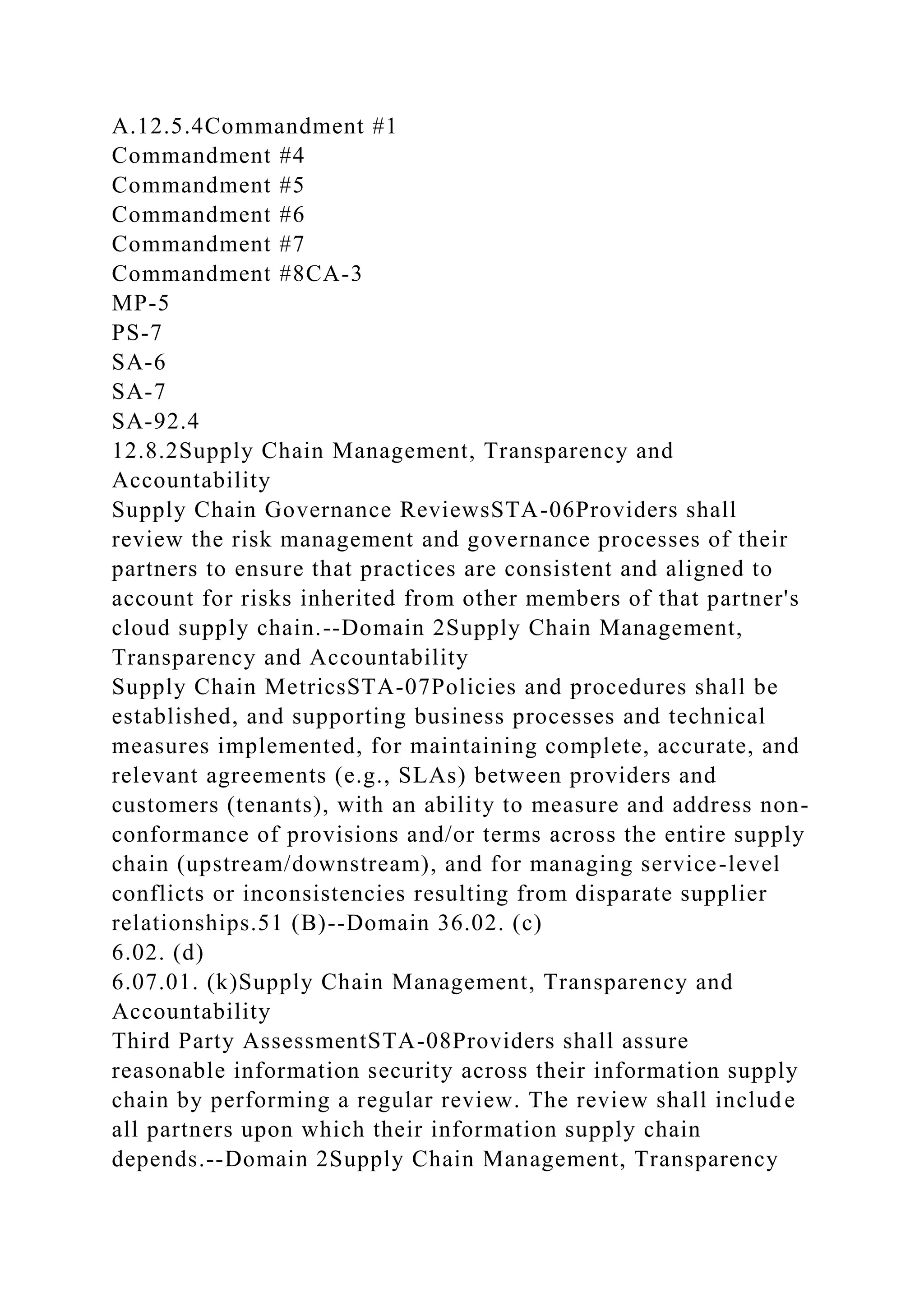
![Management Program (ISMP) shall be developed, documented,
approved, and implemented that includes administrative,
technical, and physical safeguards to protect assets and data
from loss, misuse, unauthorized access, disclosure, alteration,
and destruction. The security program shall include, but not be
limited to, the following areas insofar as they relate to the
characteristics of the business:
• Risk management
• Security policy
• Organization of information security
• Asset management
• Human resources security
• Physical and environmental security
• Communications and operations management
• Access control
• Information systems acquisition, development, and
maintenanceXXXXXXXXXXXXx1.2.(x1.2.) The entity’s
system [availability, processing integrity, confidentiality and
related] security policies include, but may not be limited to, the
following matters:A.1, B.12 (B)
3 (B)
5 (B)IS-01R2 DS5.2
R2 DS5.5Domain 28.2.145 CFR 164.308(a)(1)(i)
45 CFR 164.308(a)(1)(ii)(B)
45 CFR 164.316(b)(1)(i)
45 CFR 164.308(a)(3)(i) (New)
45 CFR 164.306(a) (New)Clause 4.2
Clause 5
A.6.1.1
A.6.1.2
A.6.1.3
A.6.1.4
A.6.1.5
A.6.1.6
A.6.1.7
A.6.1.8Commandment #1](https://image.slidesharecdn.com/csaccmv3-230108121115-6a39b129/75/CSA-CCM-V3-0CLOUD-CONTROLS-MATRIX-VERSION-3-0Control-DomainCCM-V3-docx-67-2048.jpg)
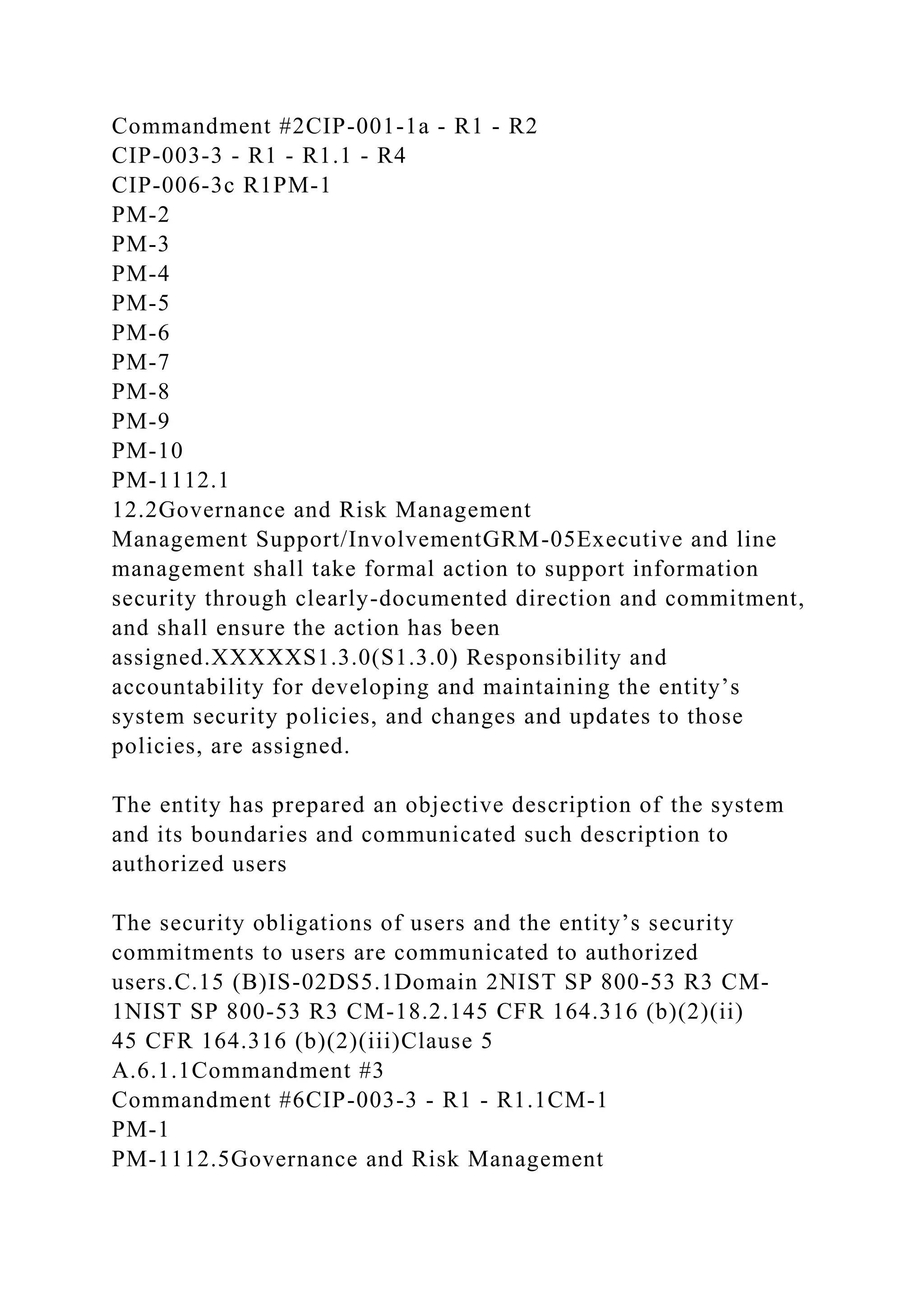
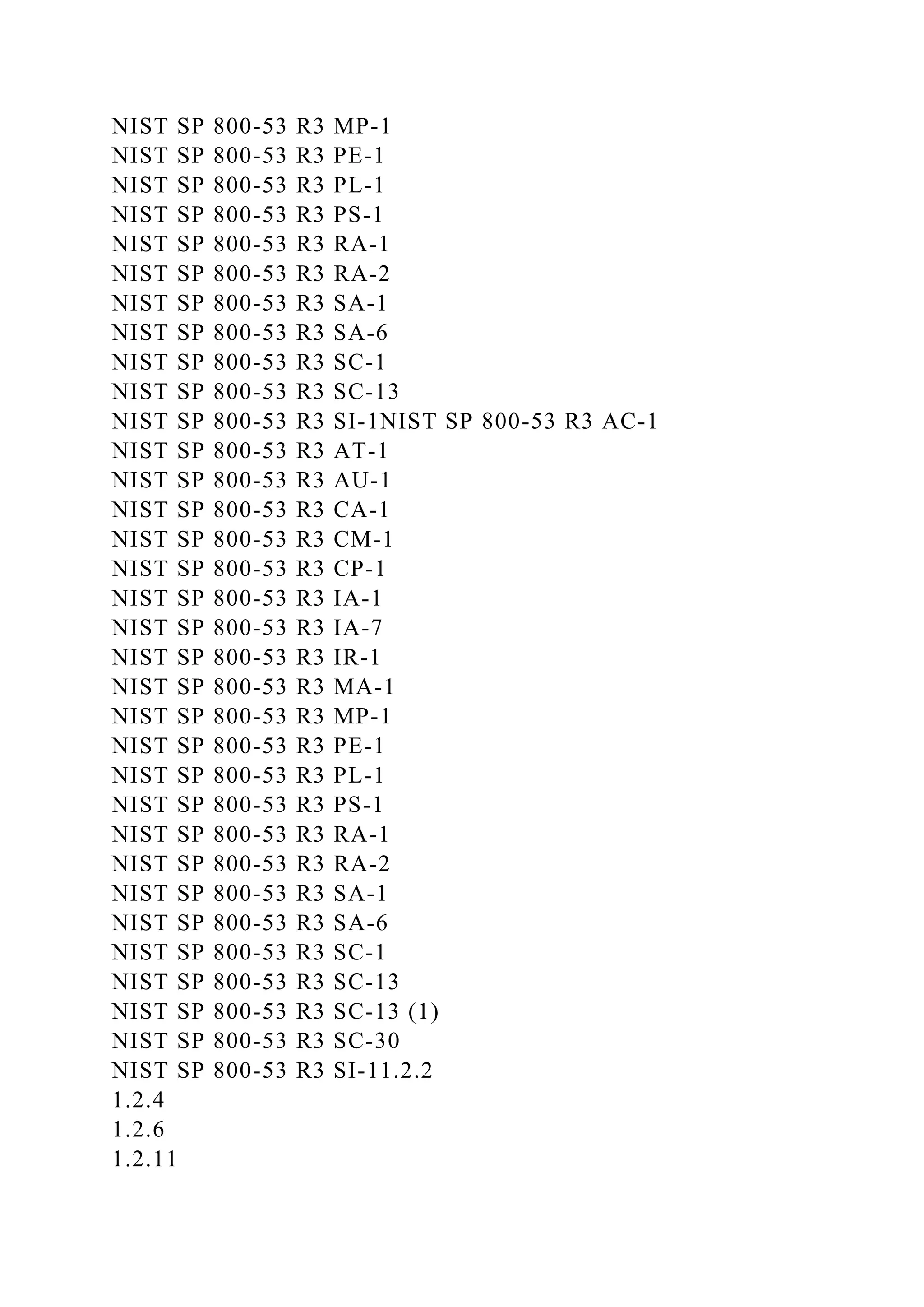
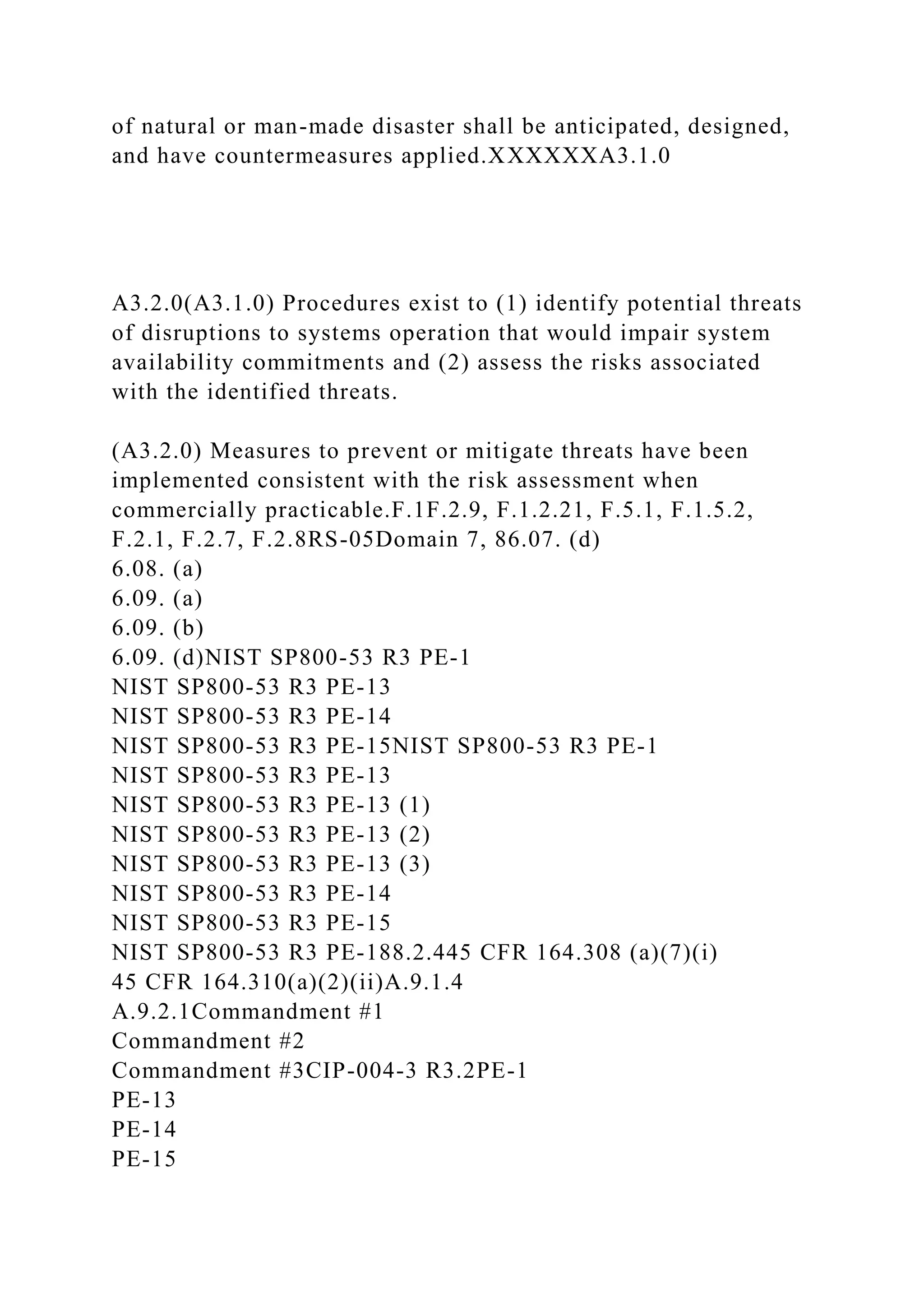
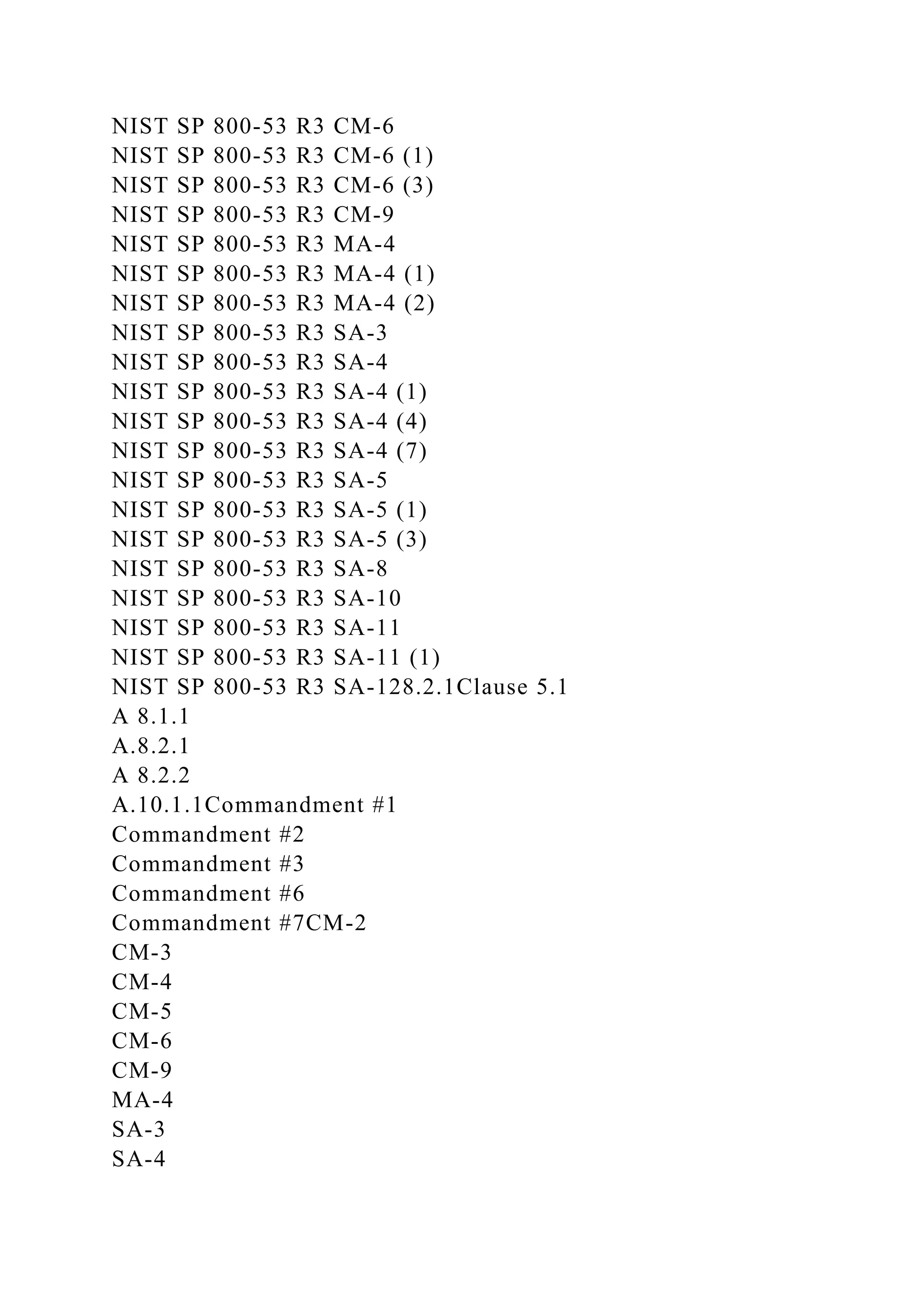
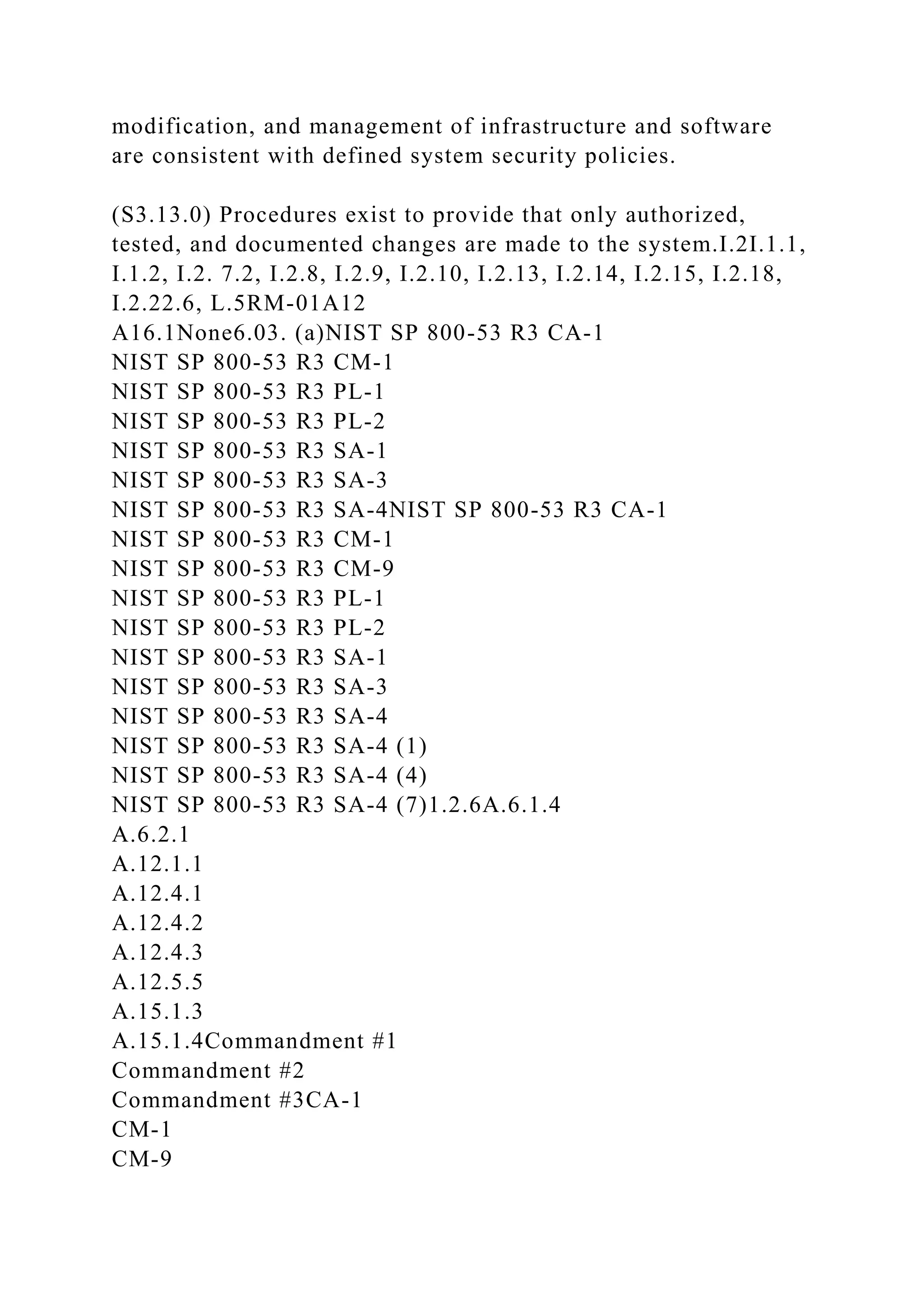
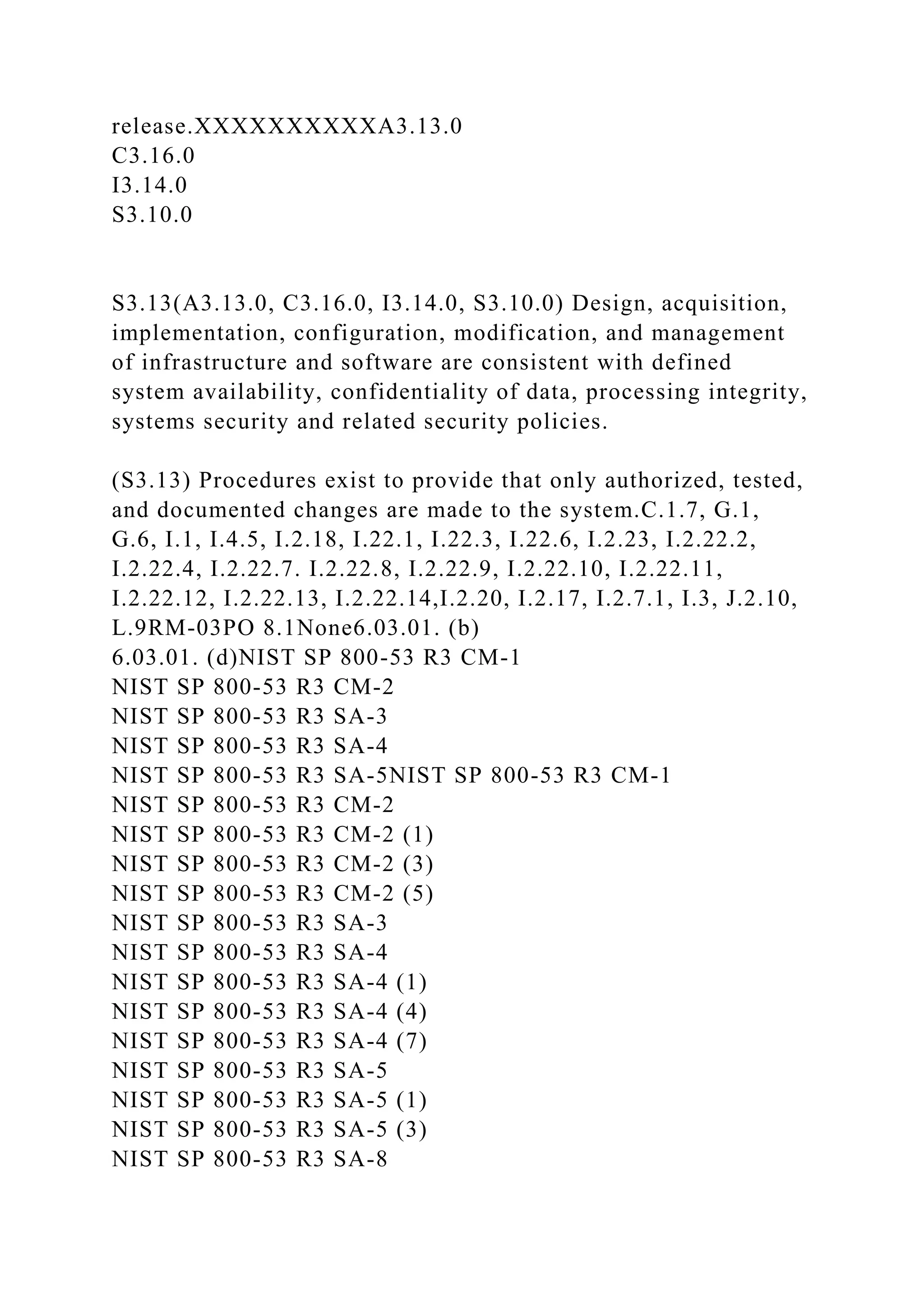
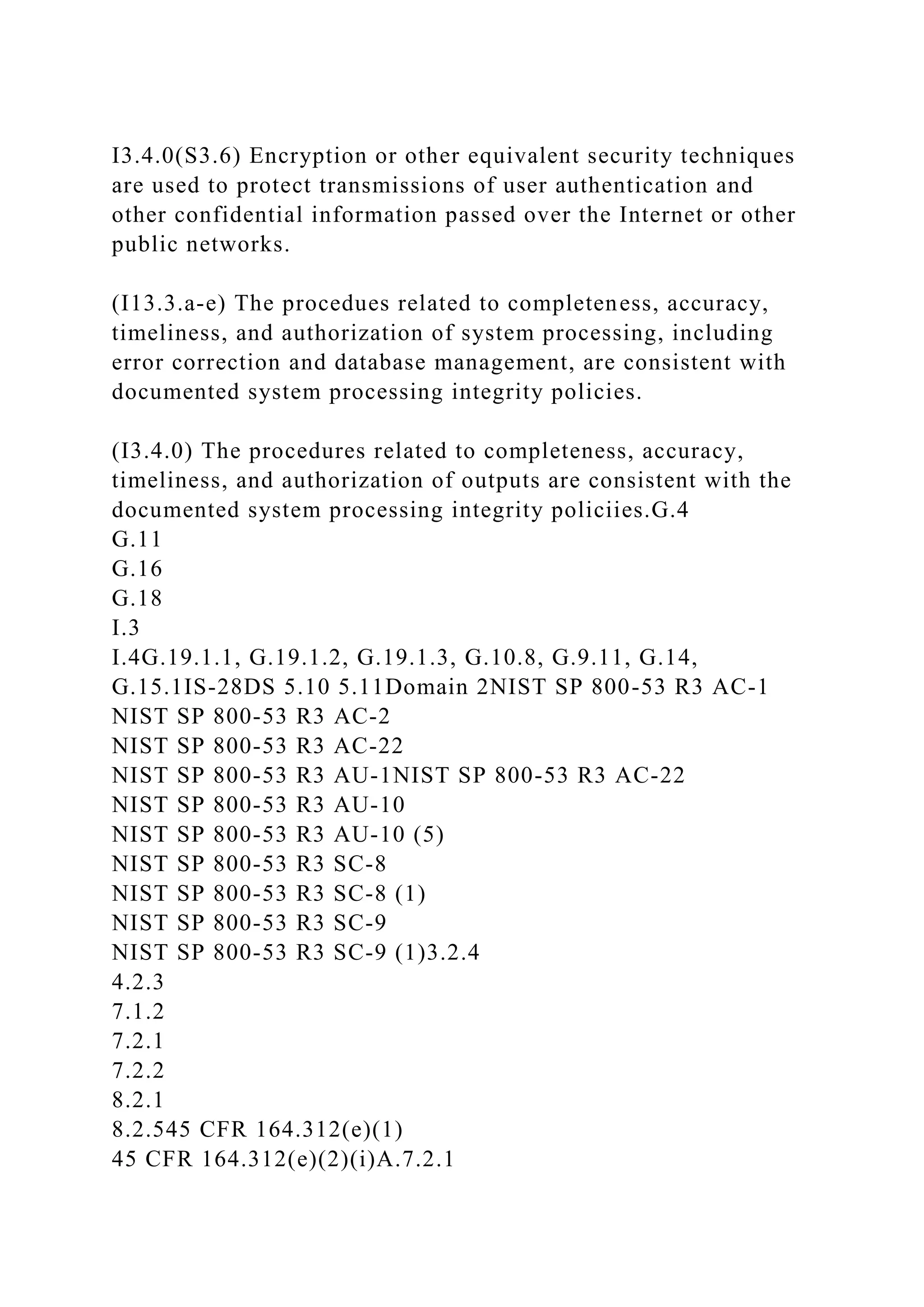
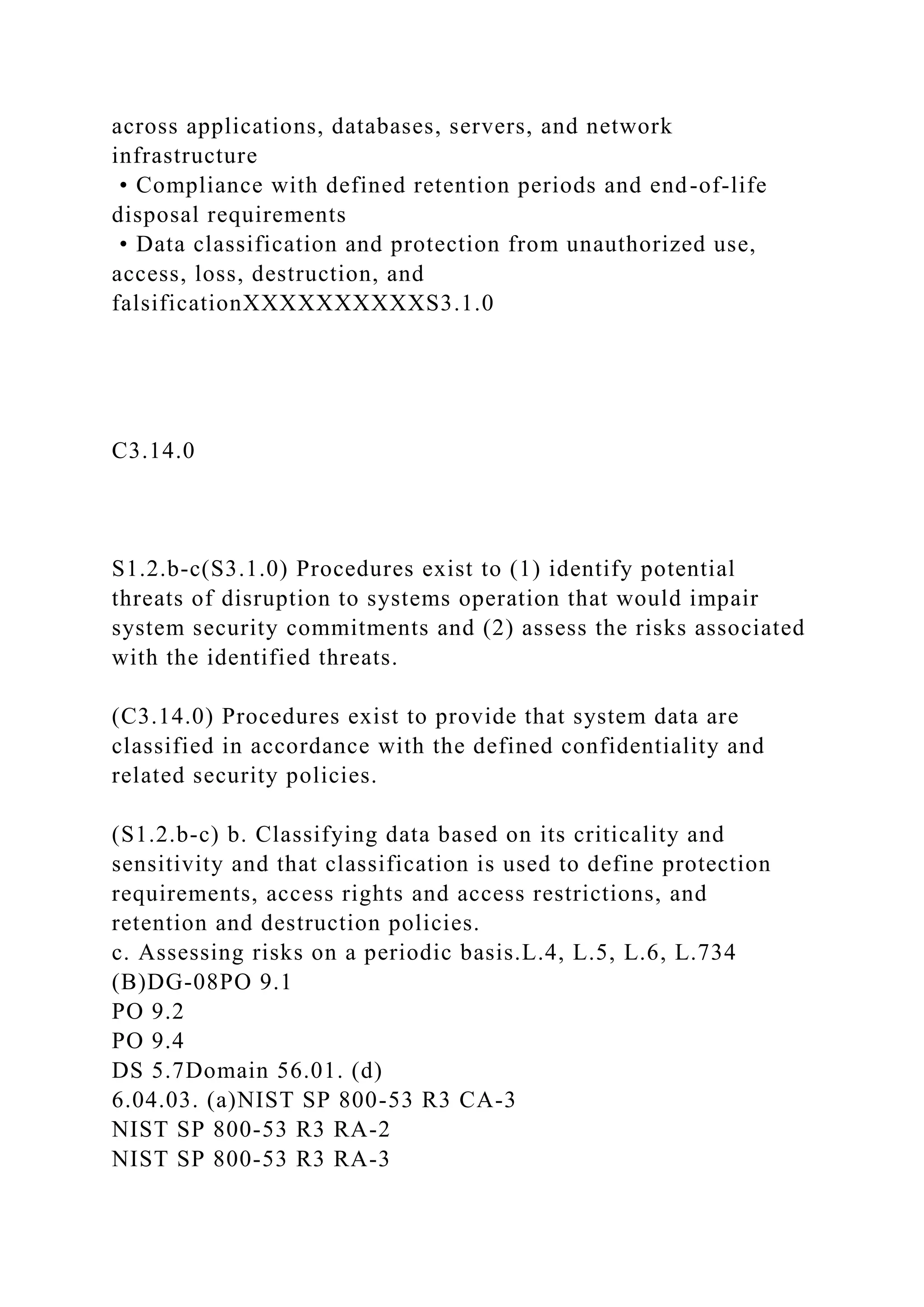
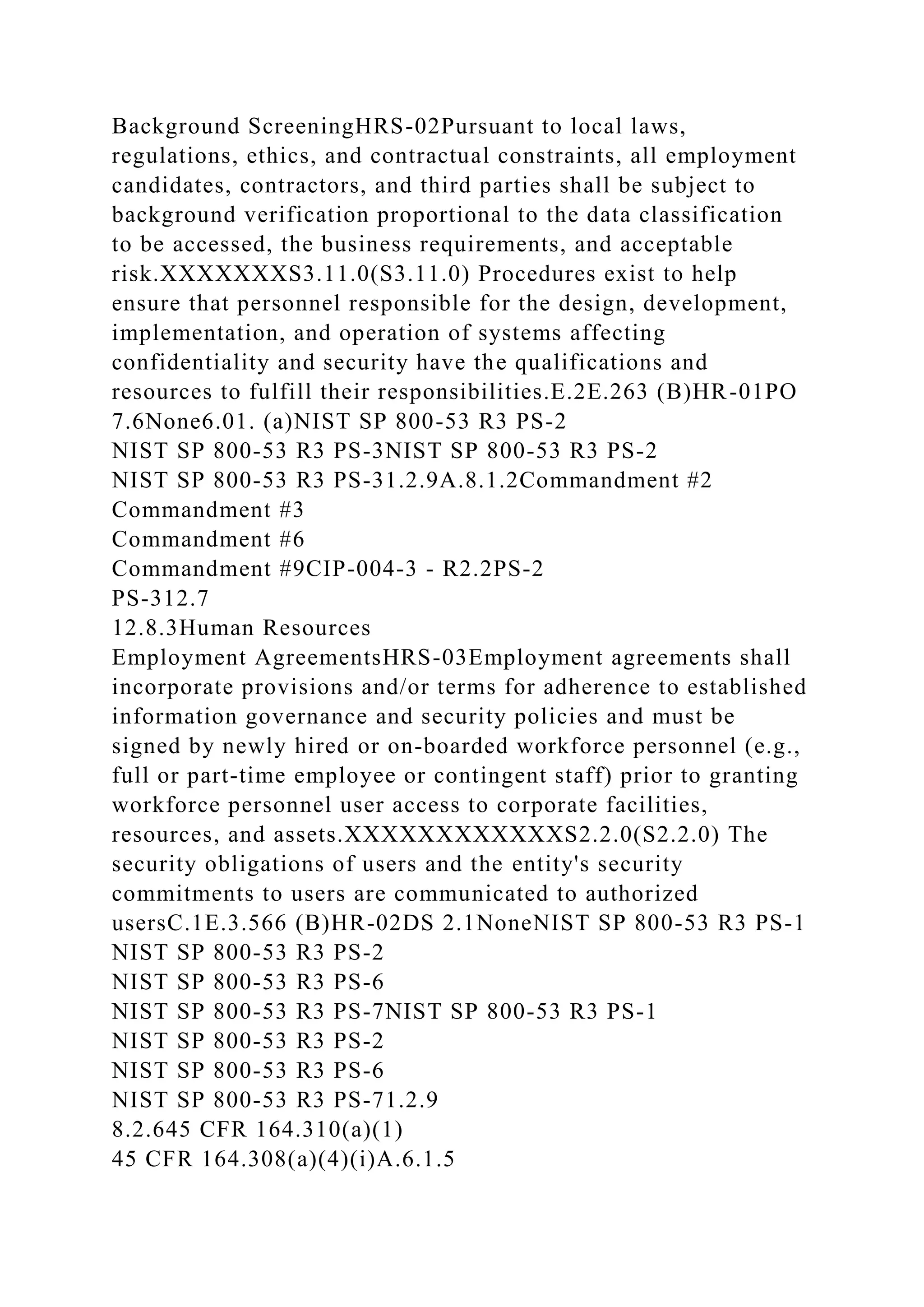
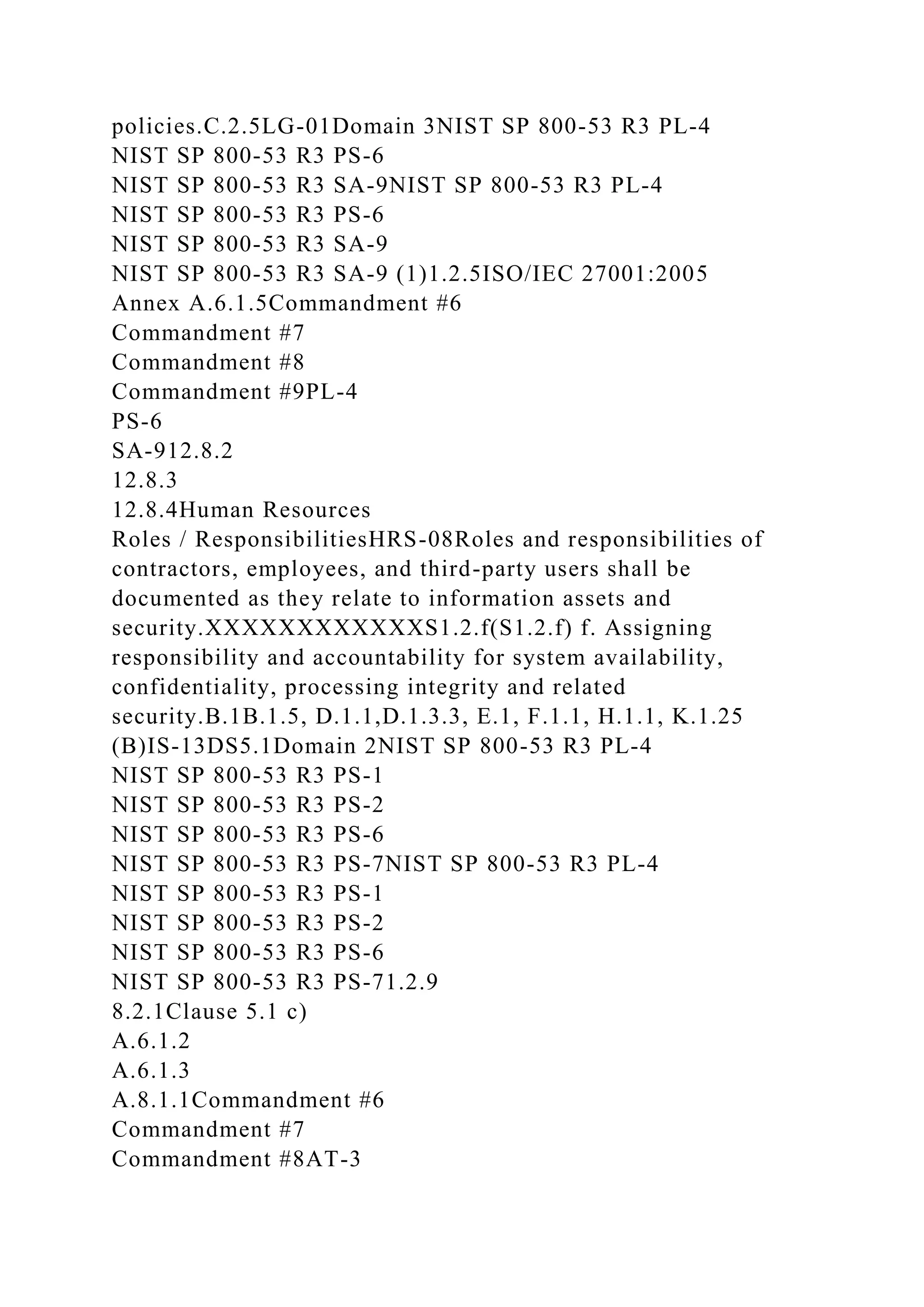
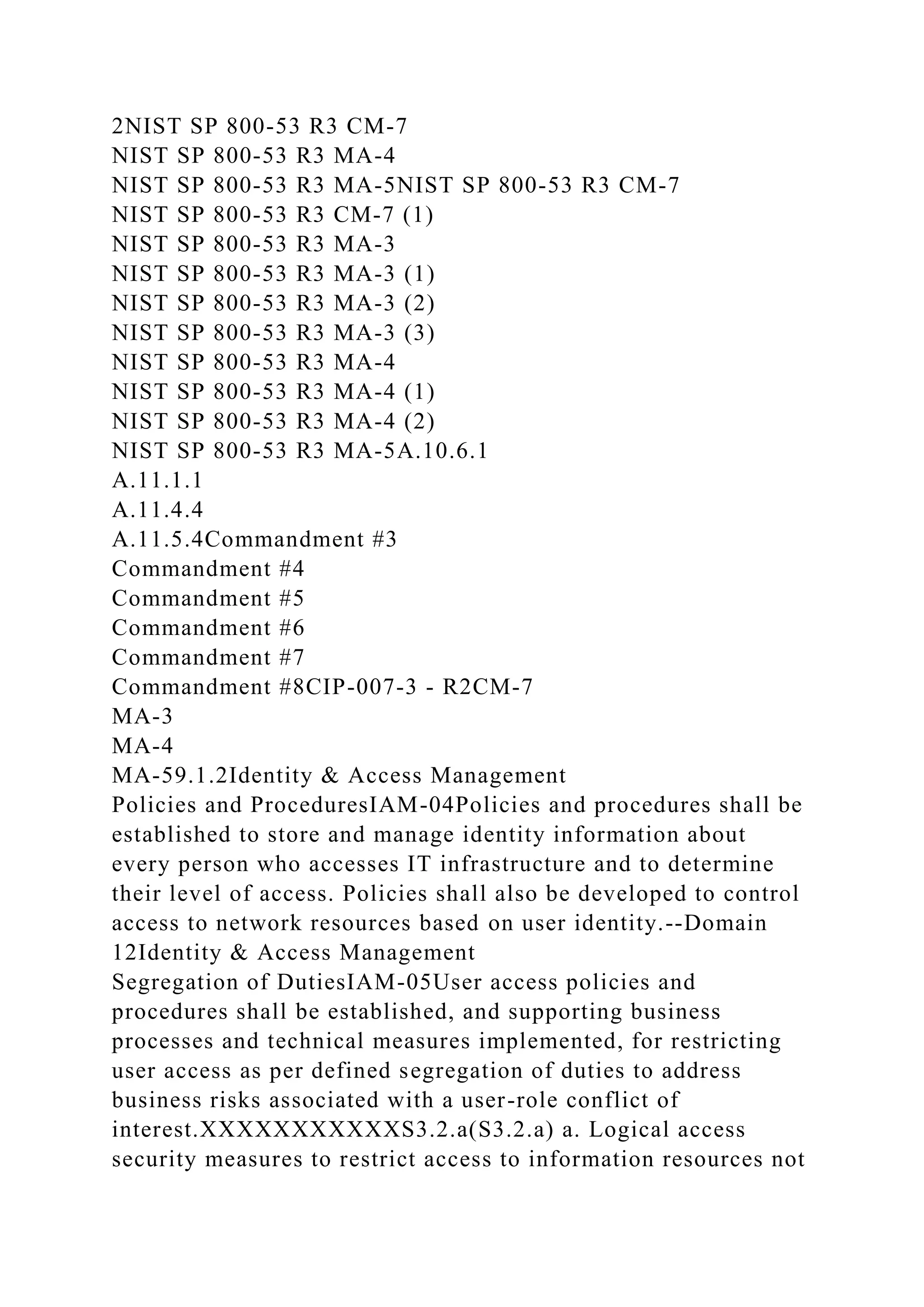
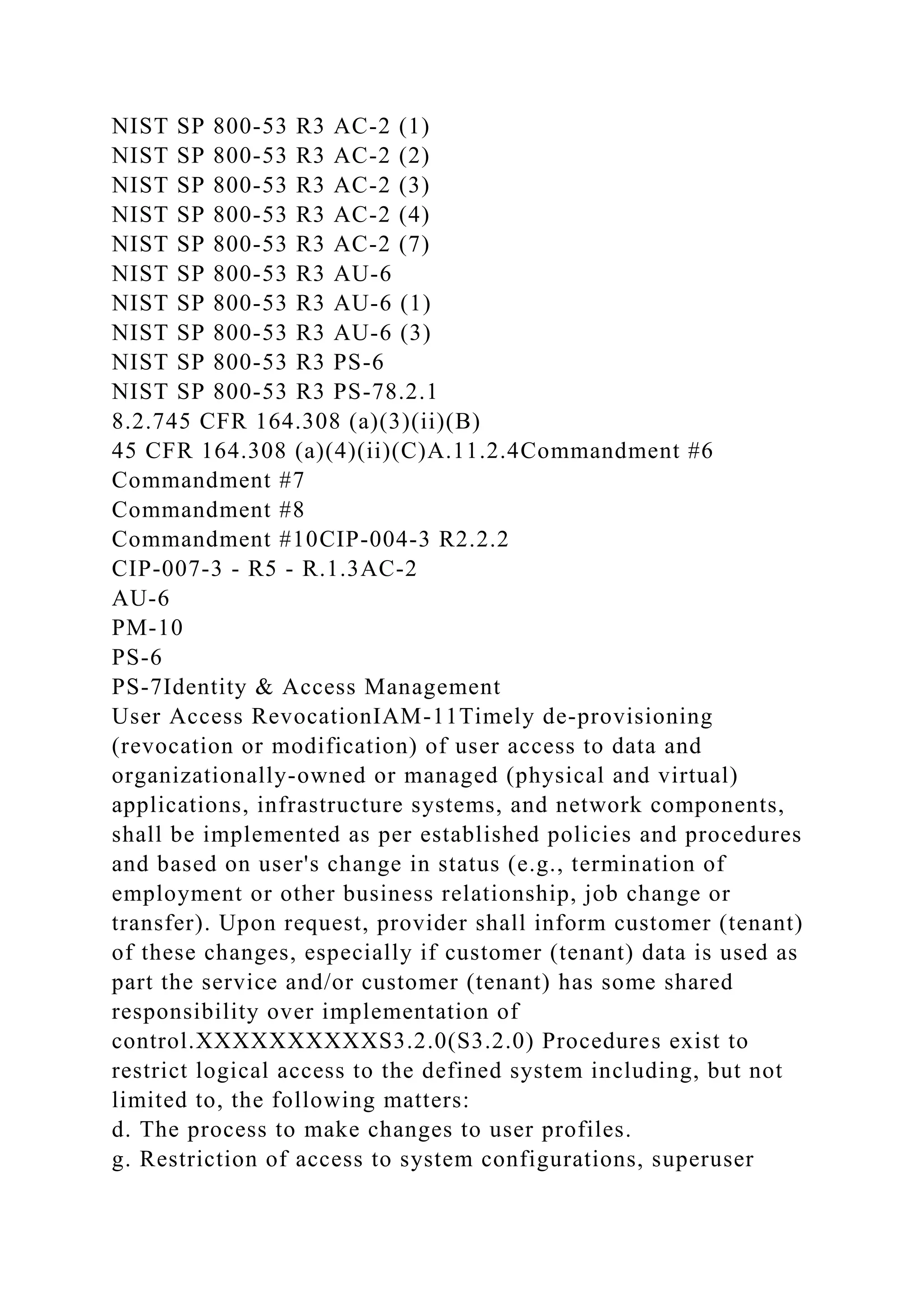
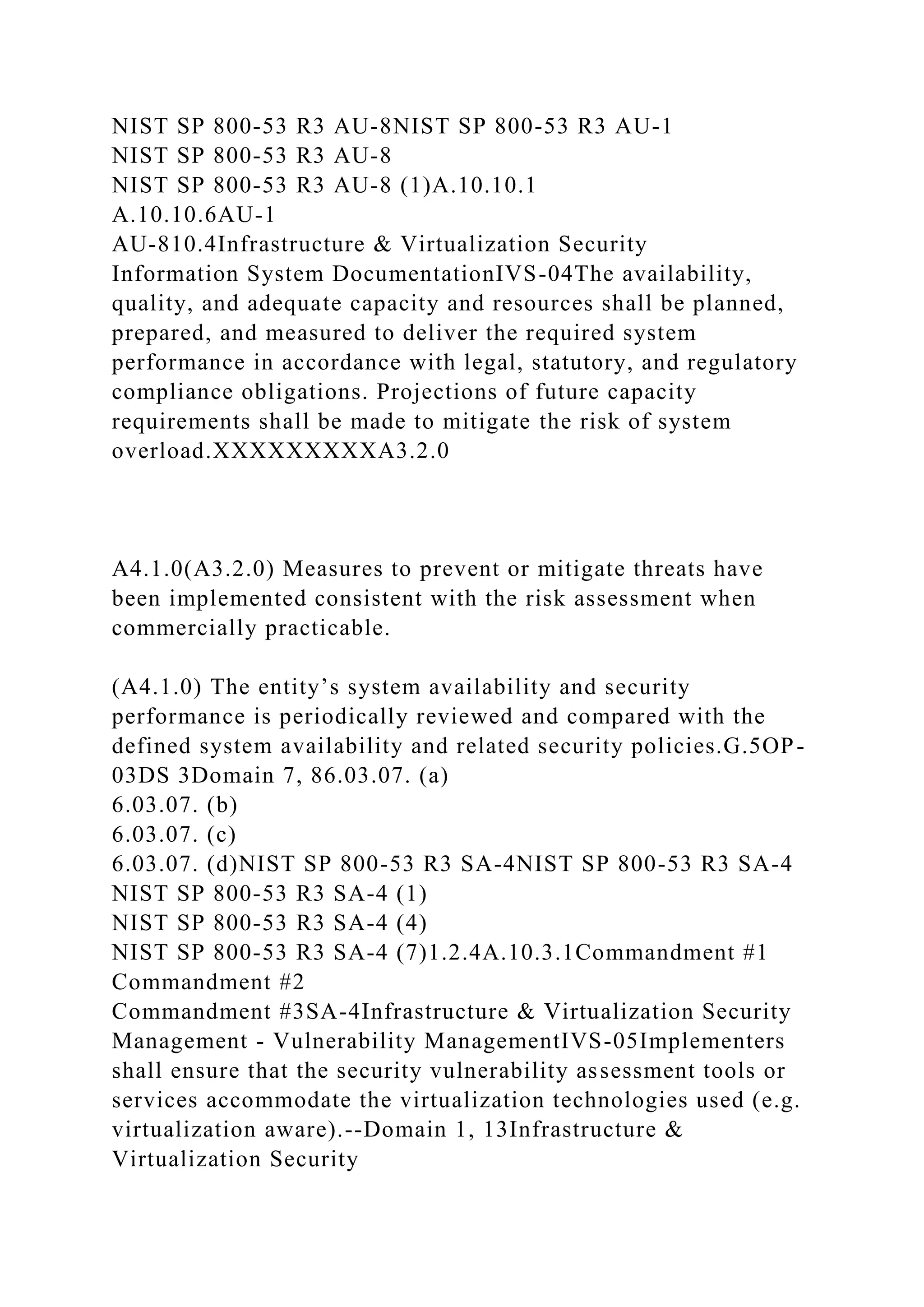
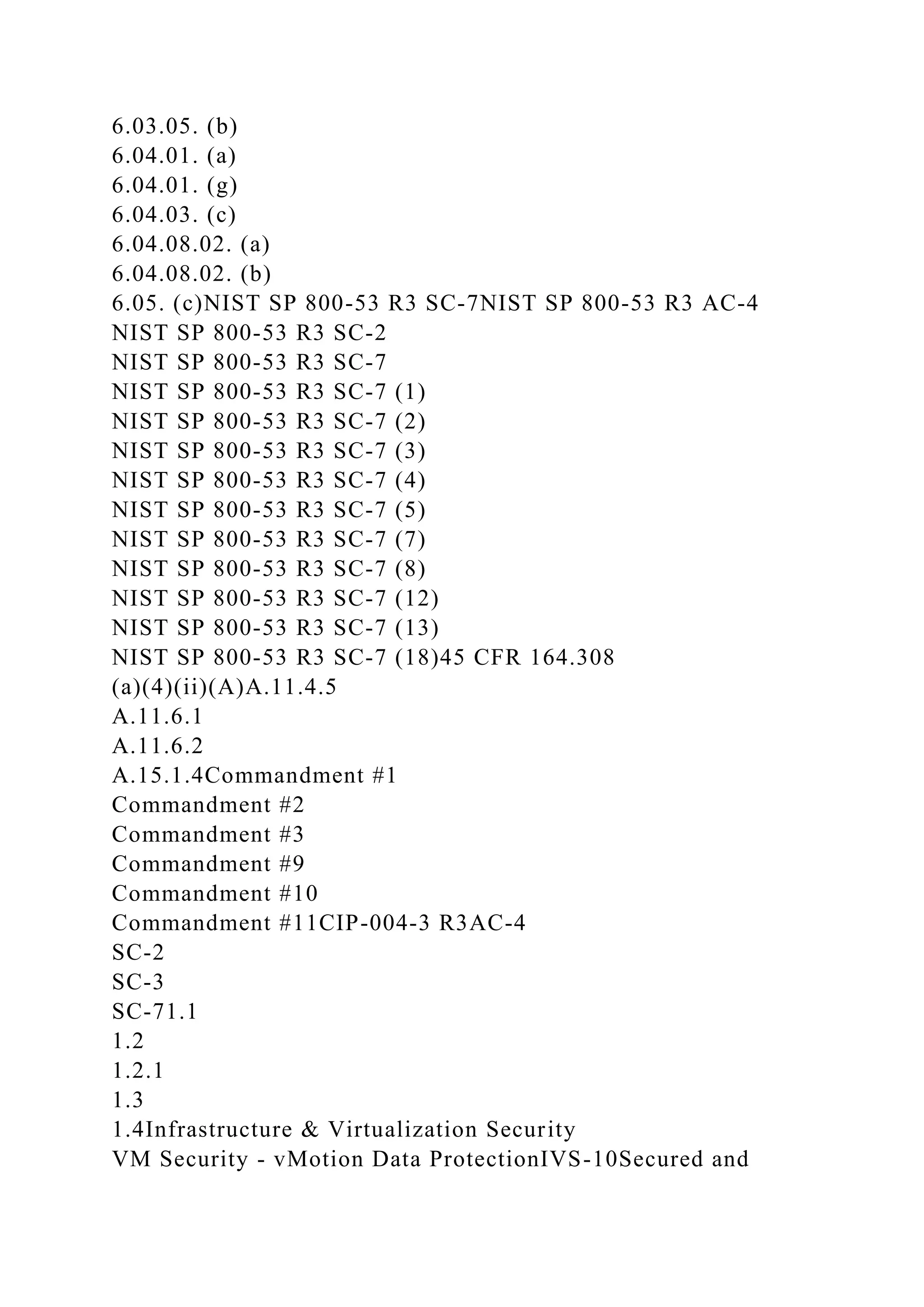
![S4.3.0(S3.1) Procedures exist to (1) identify potential threats of
disruption to systems operation that would impair system
security commitments and (2) assess the risks associated with
the identified threats.
(x3.1.0) Procedures exist to (1) identify potential threats of
disruptions to systems operation that would impair system
[availability, processing integrity, confidenitality] commitments
and (2) assess the risks associated with the identified threats.
(S4.3.0) Environmental, regulatory, and technological changes
are monitored, and their effect on system availability,
confidentiality of data, processing integrity, and system
security is assessed on a timely basis; policies are updated for
that assessment.I.1
I.4C.2.1, I.4.1, I.5, G.15.1.3, I.346 (B)
74 (B)RI-02PO 9.4Domain 2, 46.03. (a)
6.08. (a)NIST SP 800-53 R3 CM-1
NIST SP 800-53 R3 RA-1
NIST SP 800-53 R3 RA-2
NIST SP 800-53 R3 RA-3NIST SP 800-53 R3 RA-1
NIST SP 800-53 R3 RA-2
NIST SP 800-53 R3 RA-3
NIST SP 800-53 R3 SC-301.2.4
1.2.545 CFR 164.308 (a)(1)(ii)(A)Clause 4.2.1 c) through g)
Clause 4.2.3 d)
Clause 5.1 f)
Clause 7.2 & 7.3
A.6.2.1
A.12.5.2
A.12.6.1
A.14.1.2
A.15.1.1
A.15.2.1
A.15.2.2CIP-002-3 - R1.1 - R1.2
CIP-005-3a - R1 - R1.2](https://image.slidesharecdn.com/csaccmv3-230108121115-6a39b129/75/CSA-CCM-V3-0CLOUD-CONTROLS-MATRIX-VERSION-3-0Control-DomainCCM-V3-docx-76-2048.jpg)
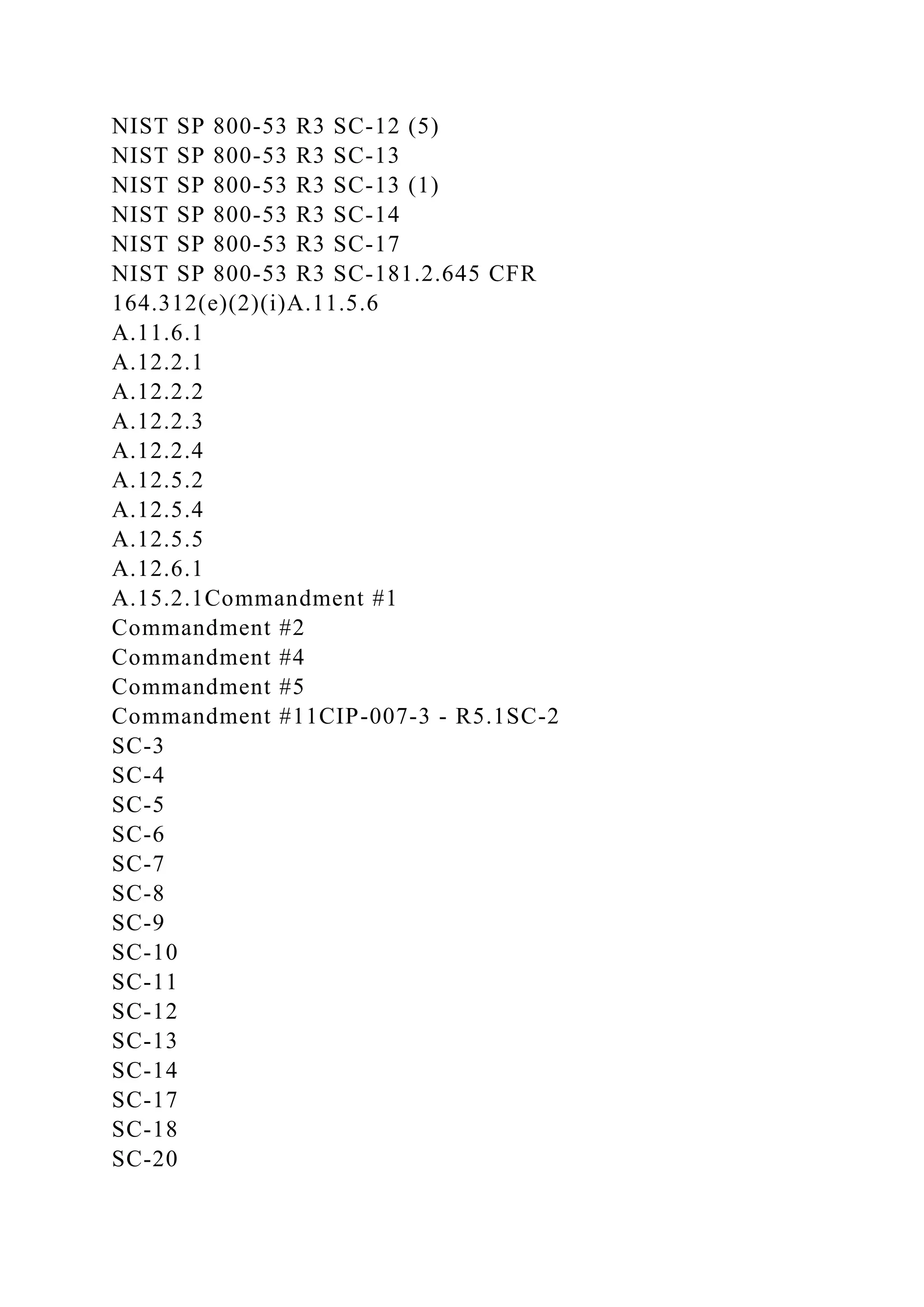
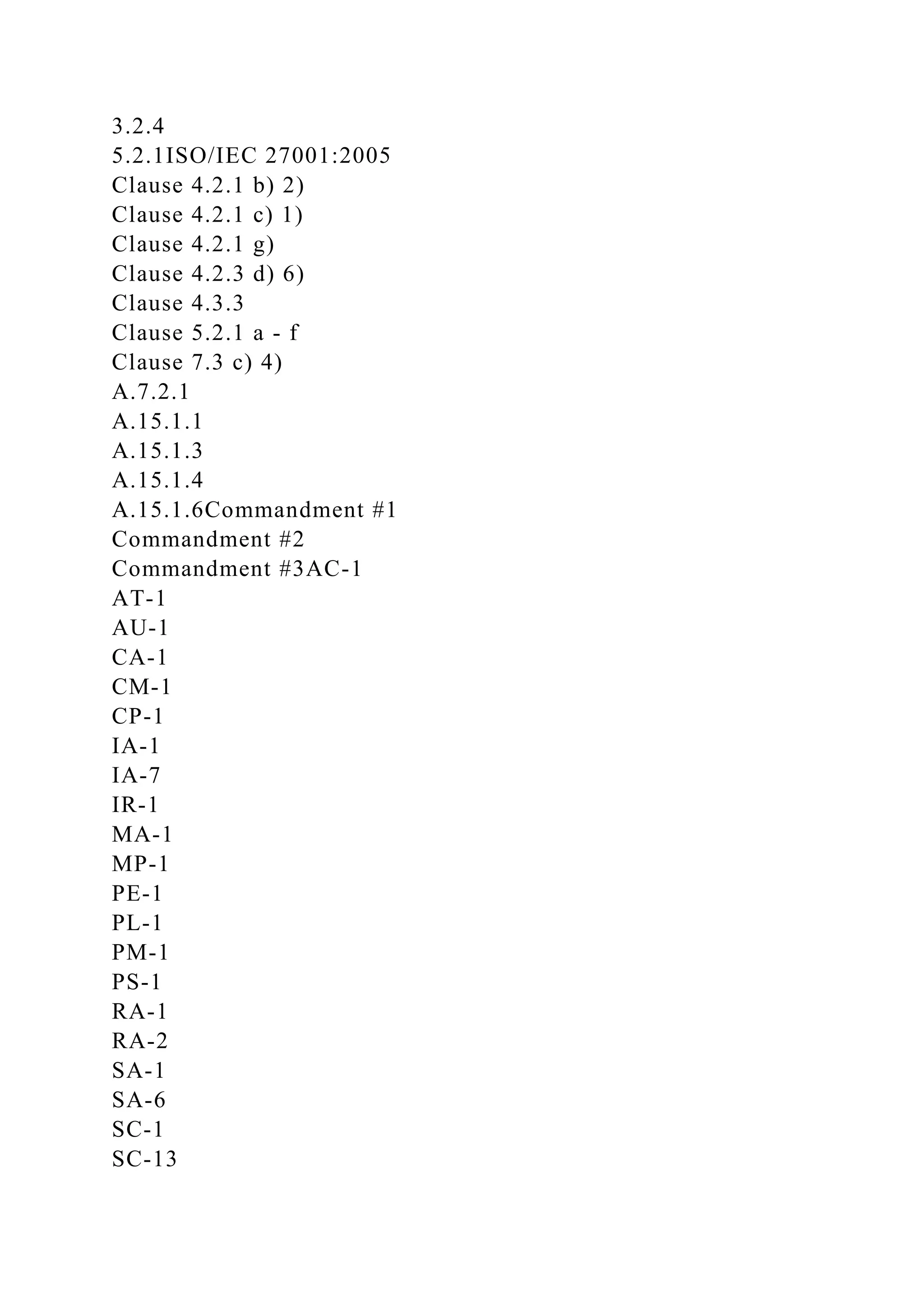
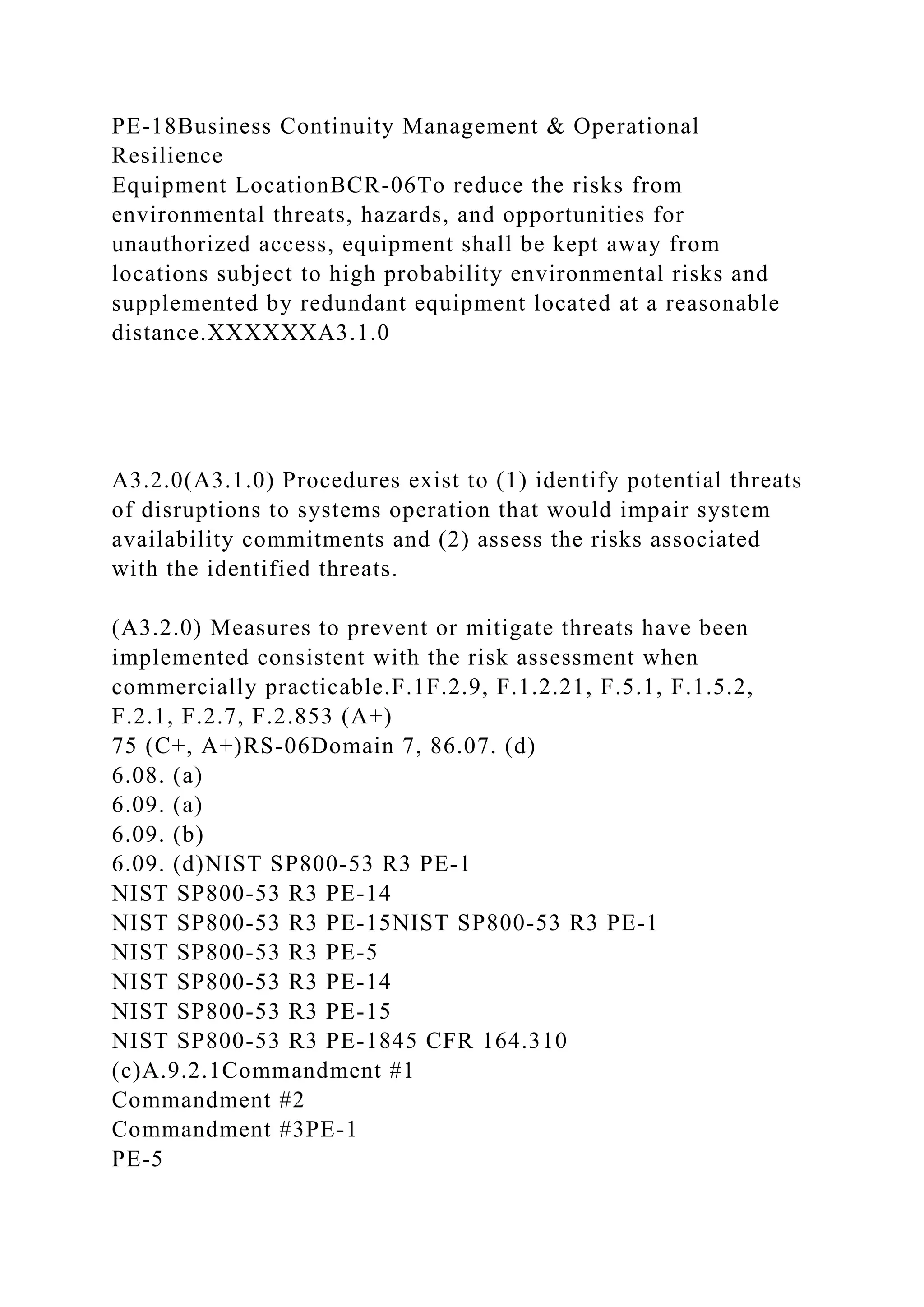
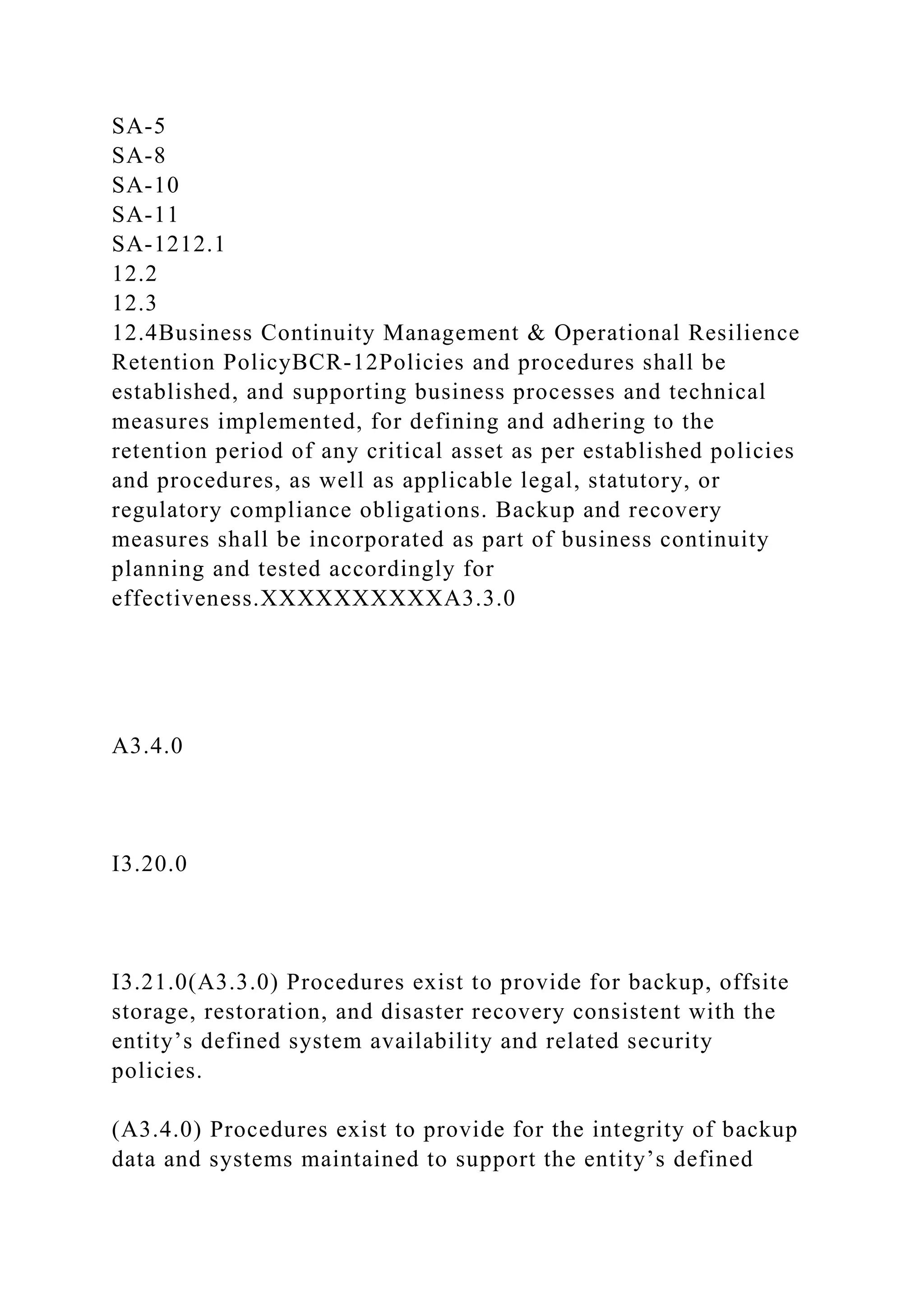
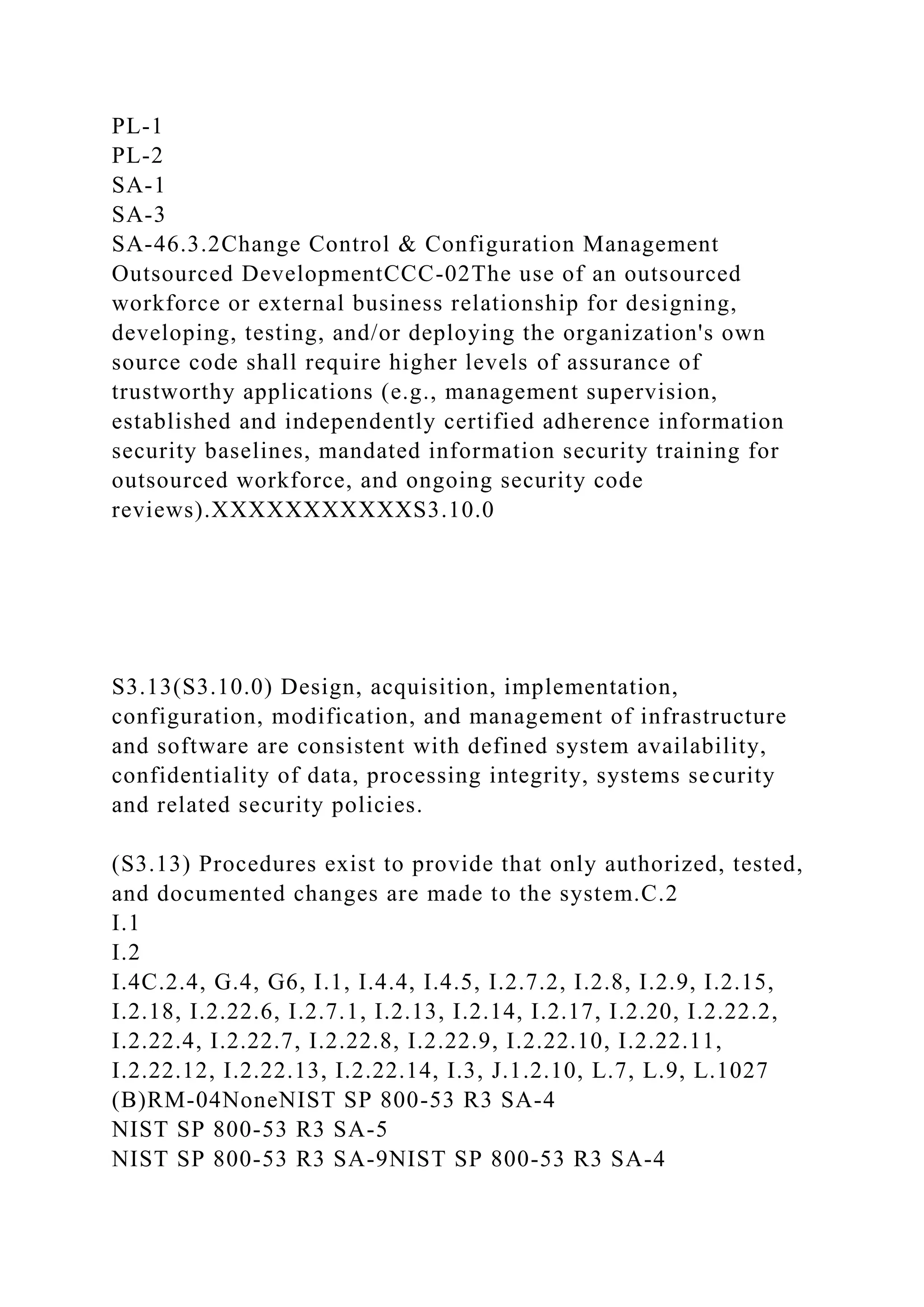
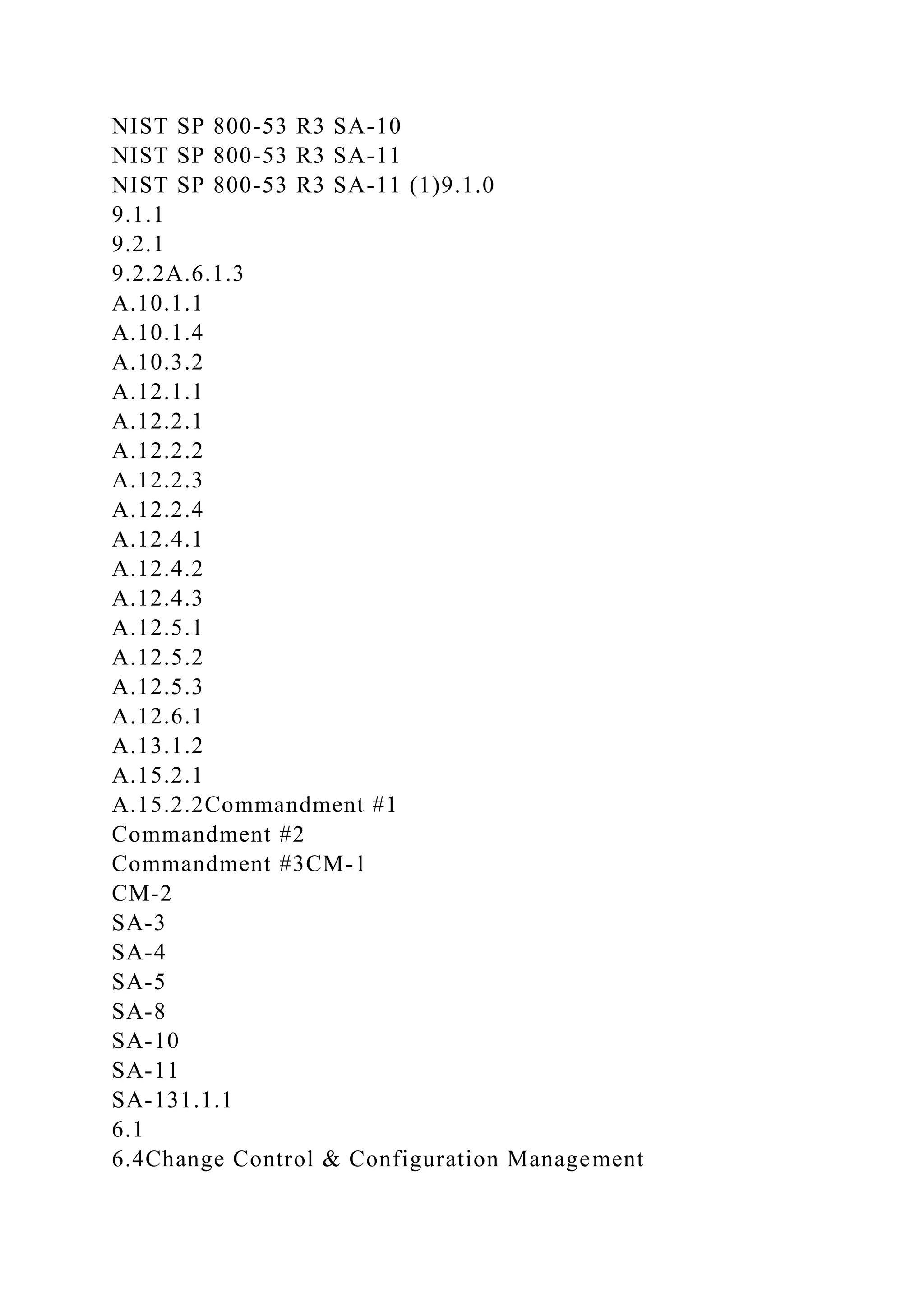
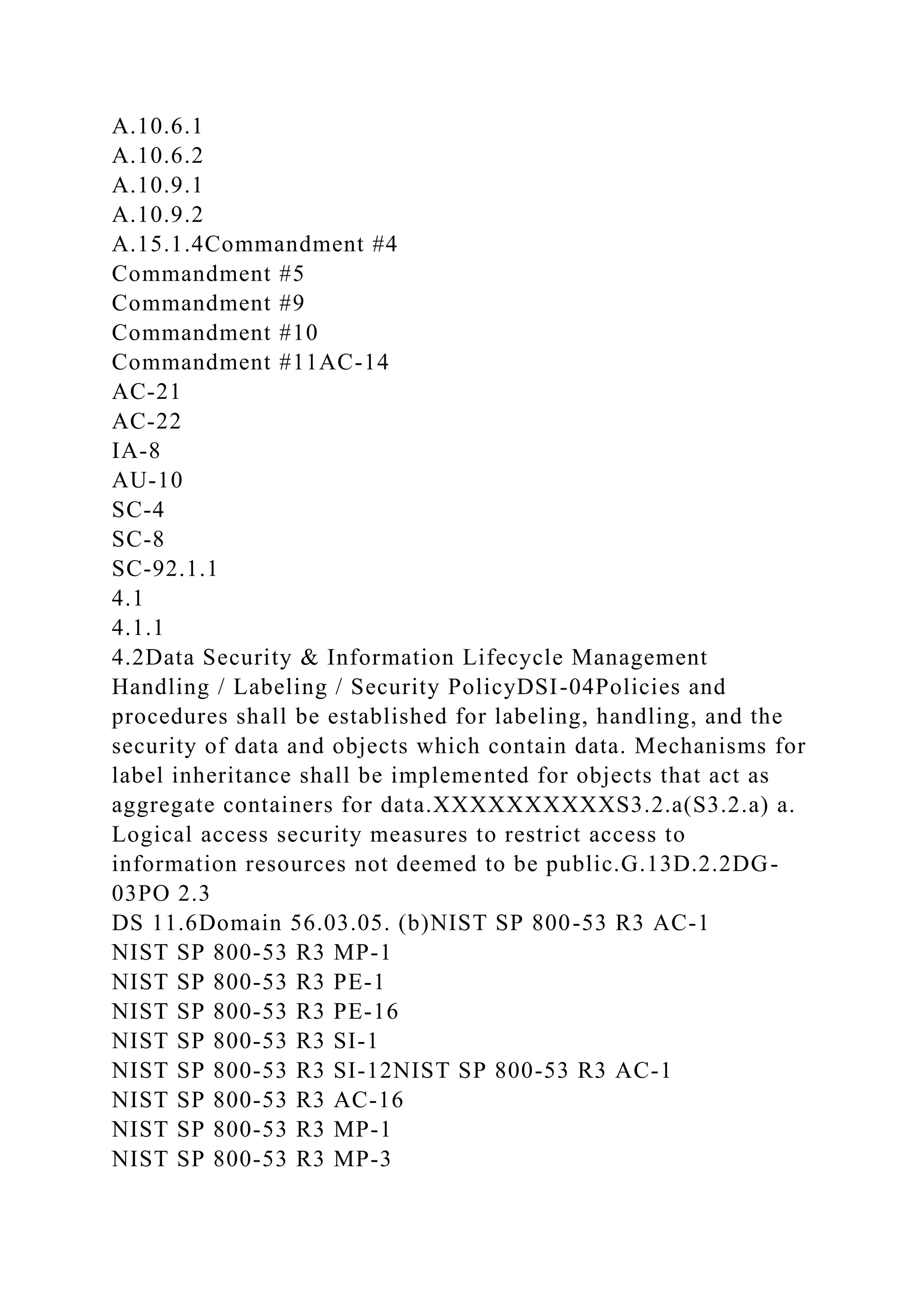
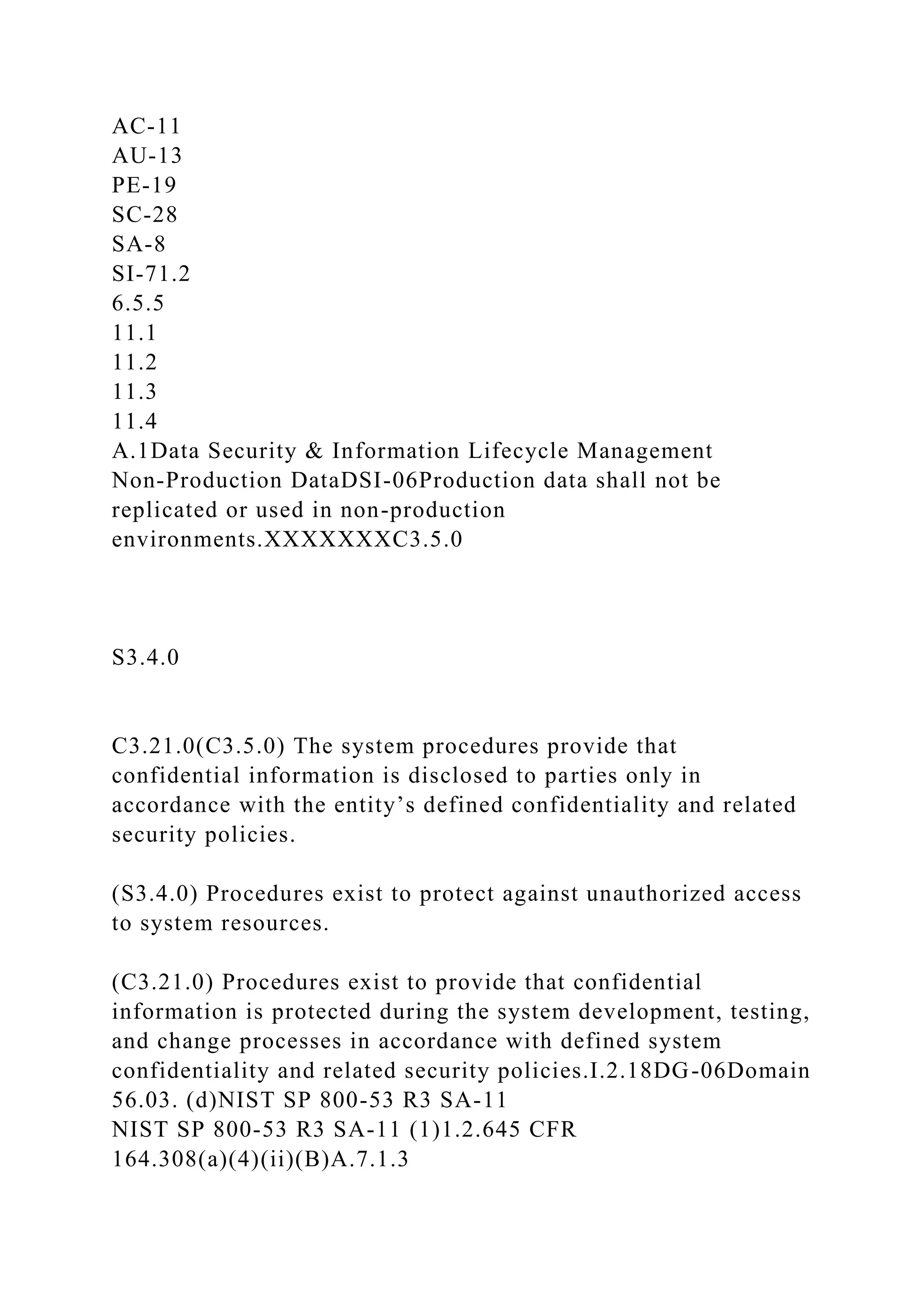
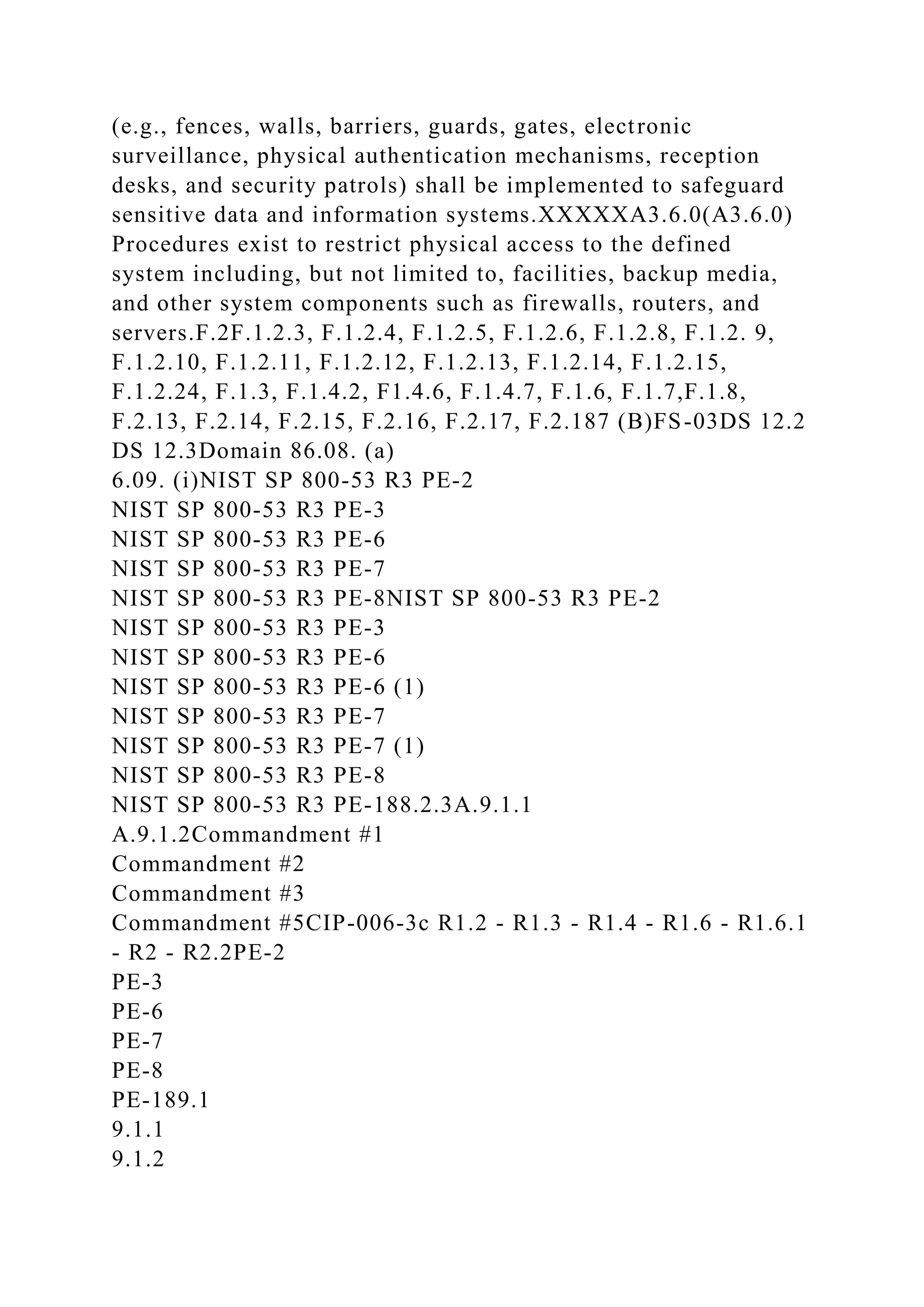
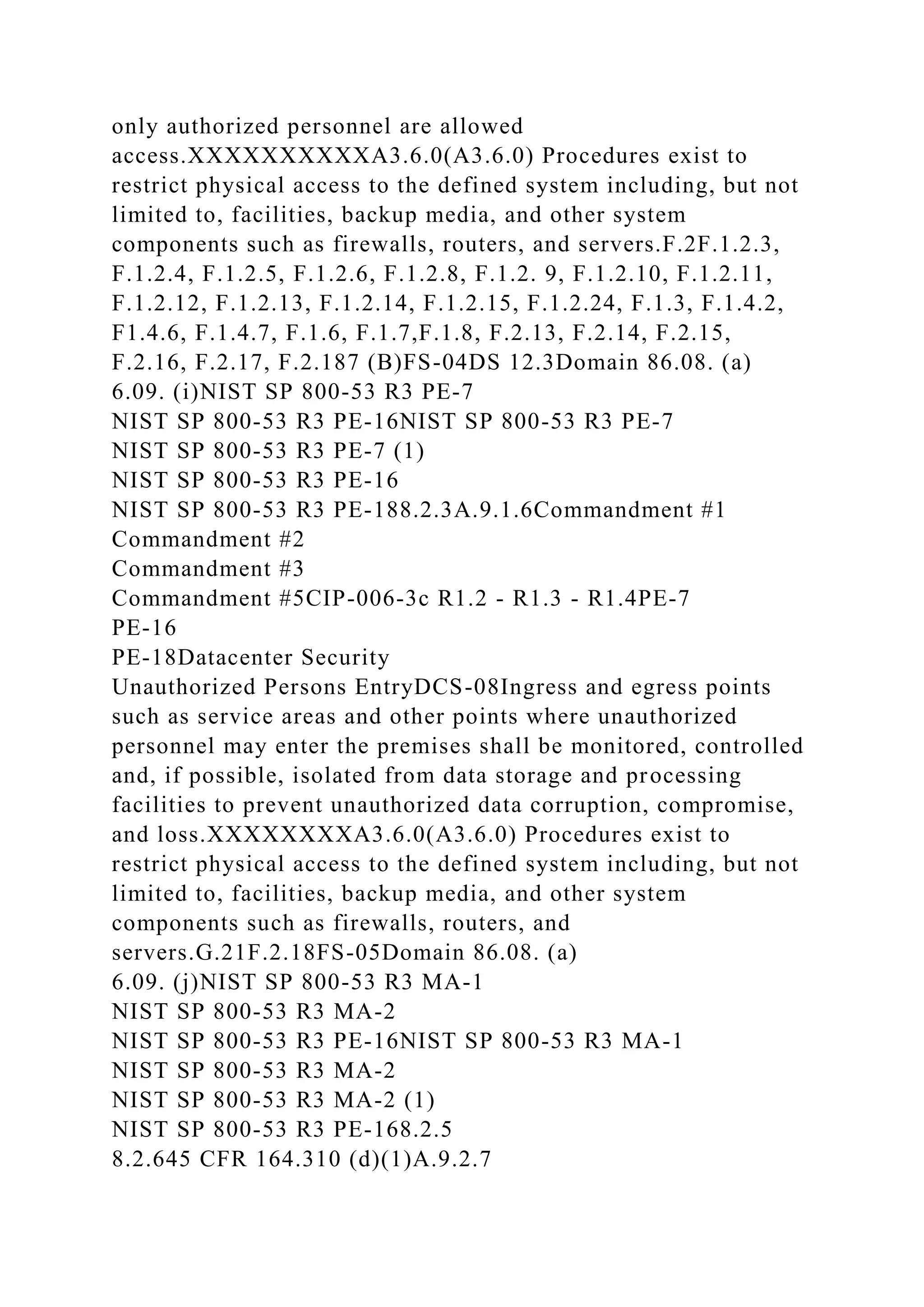
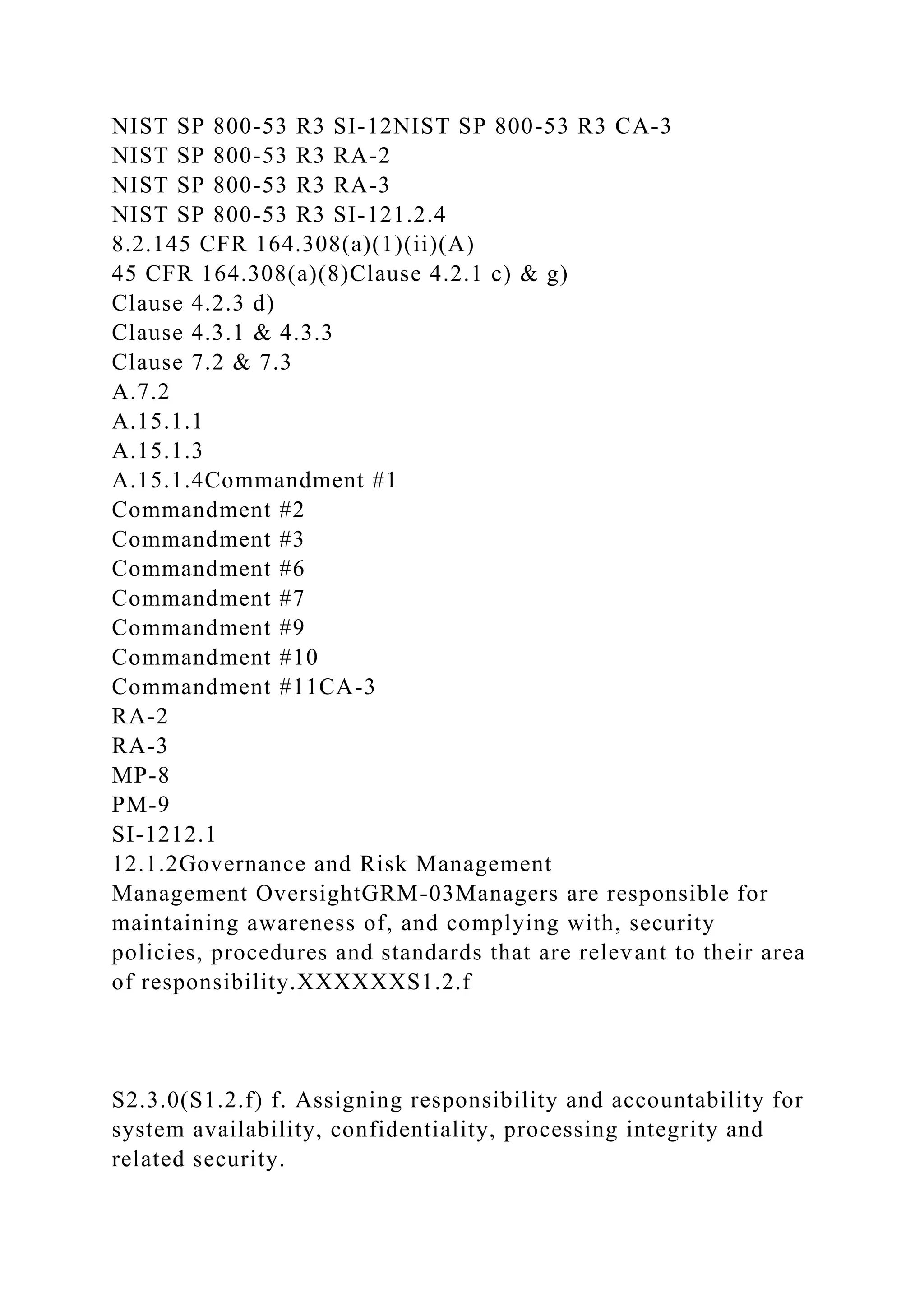
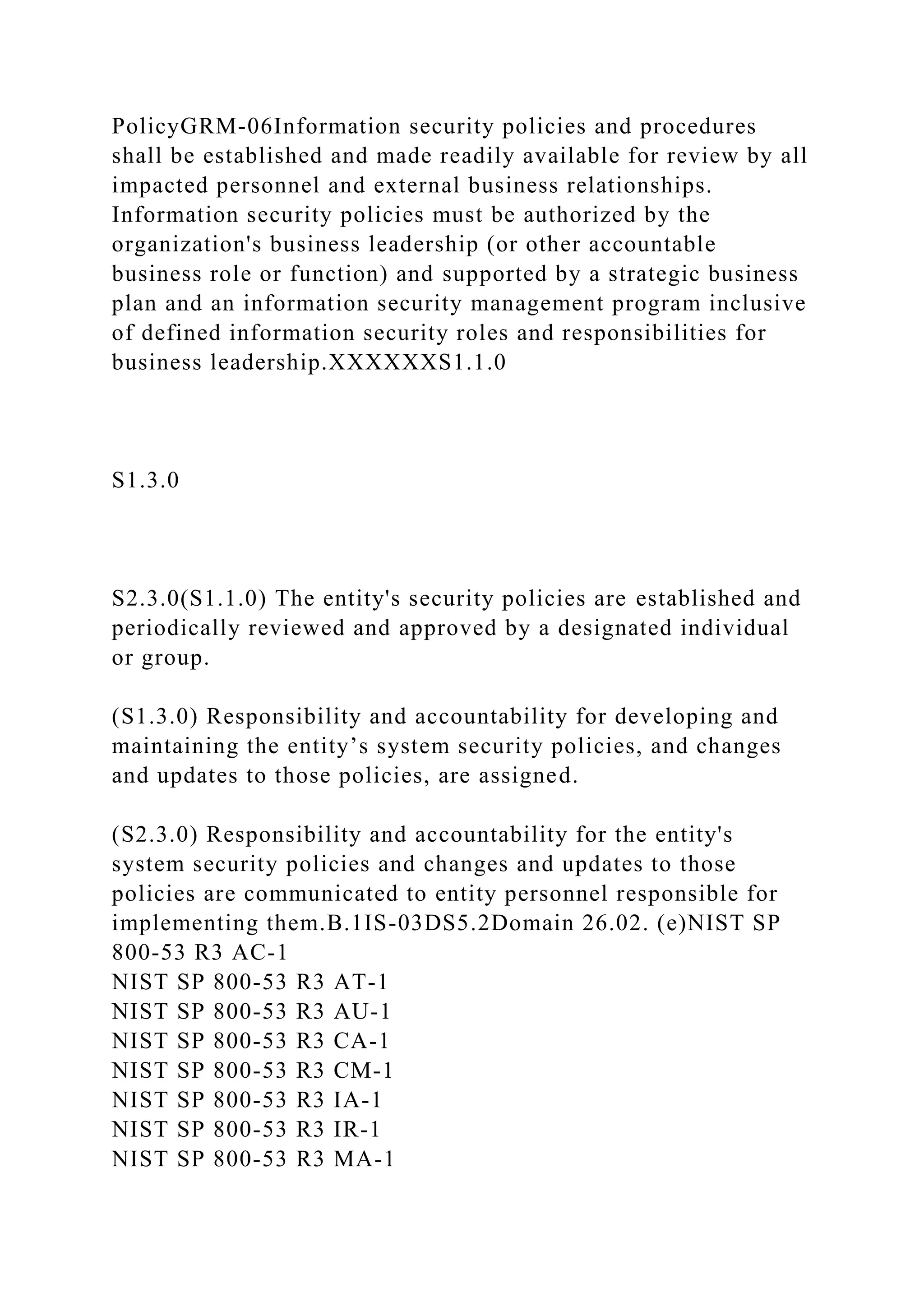
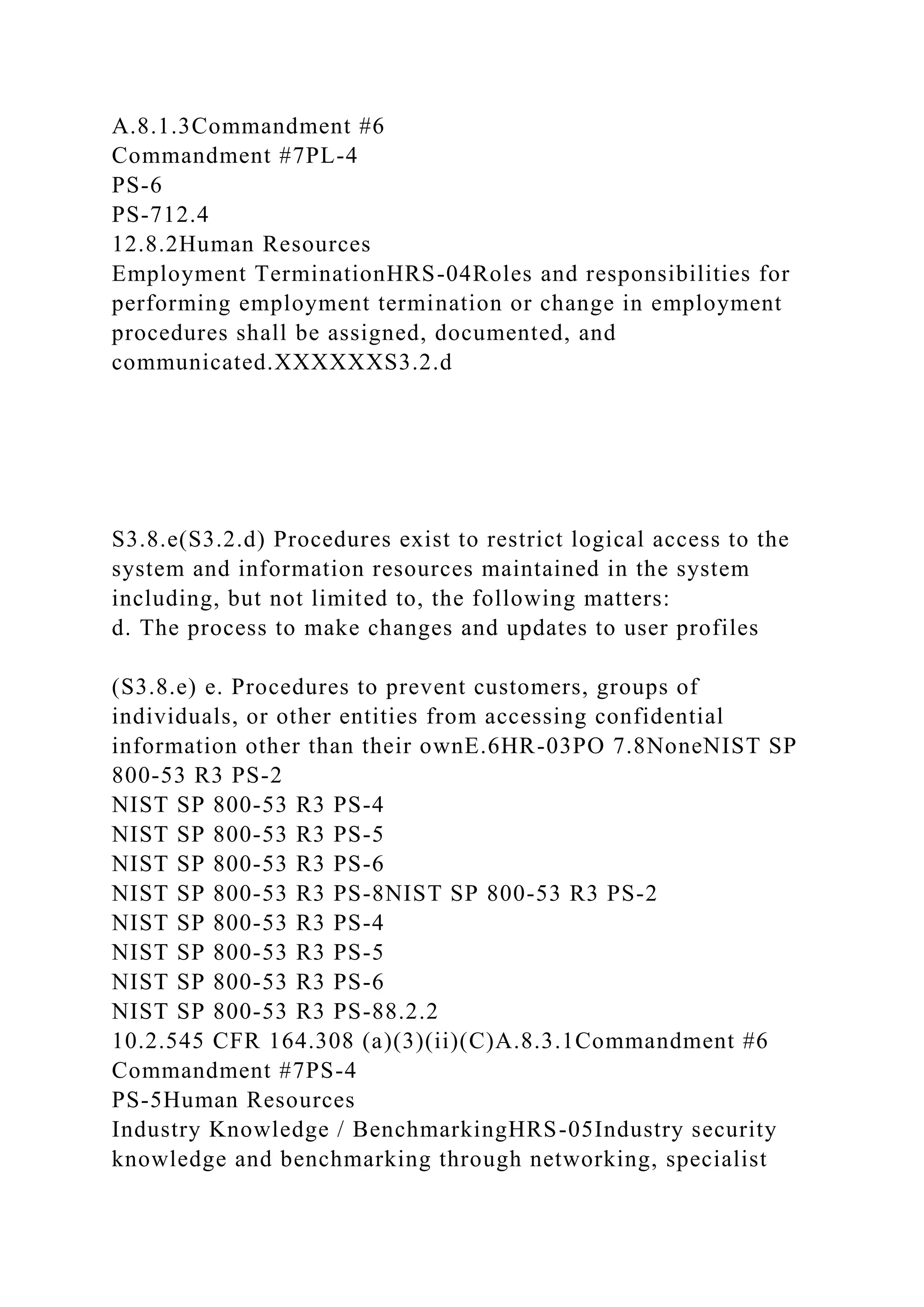
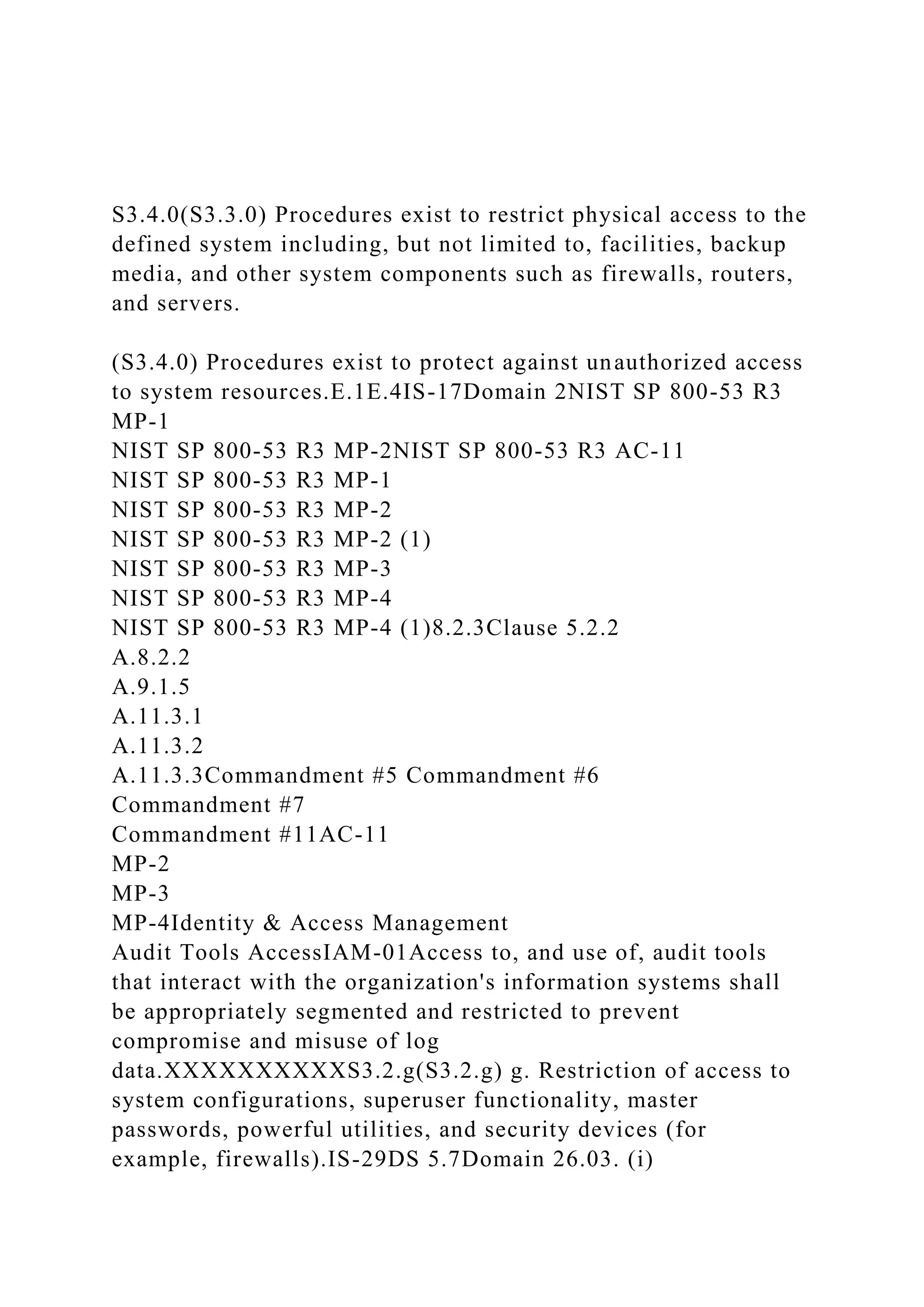
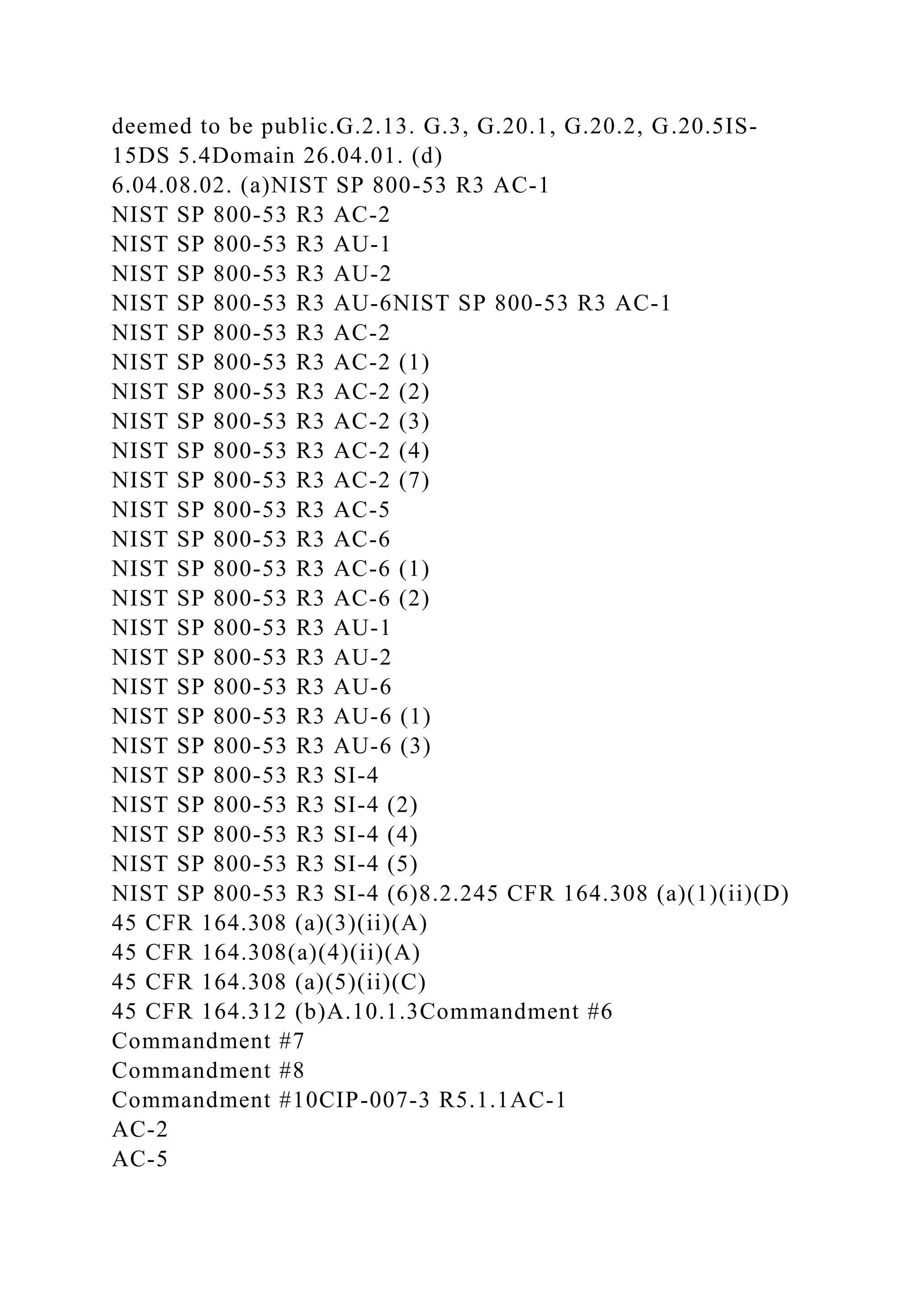
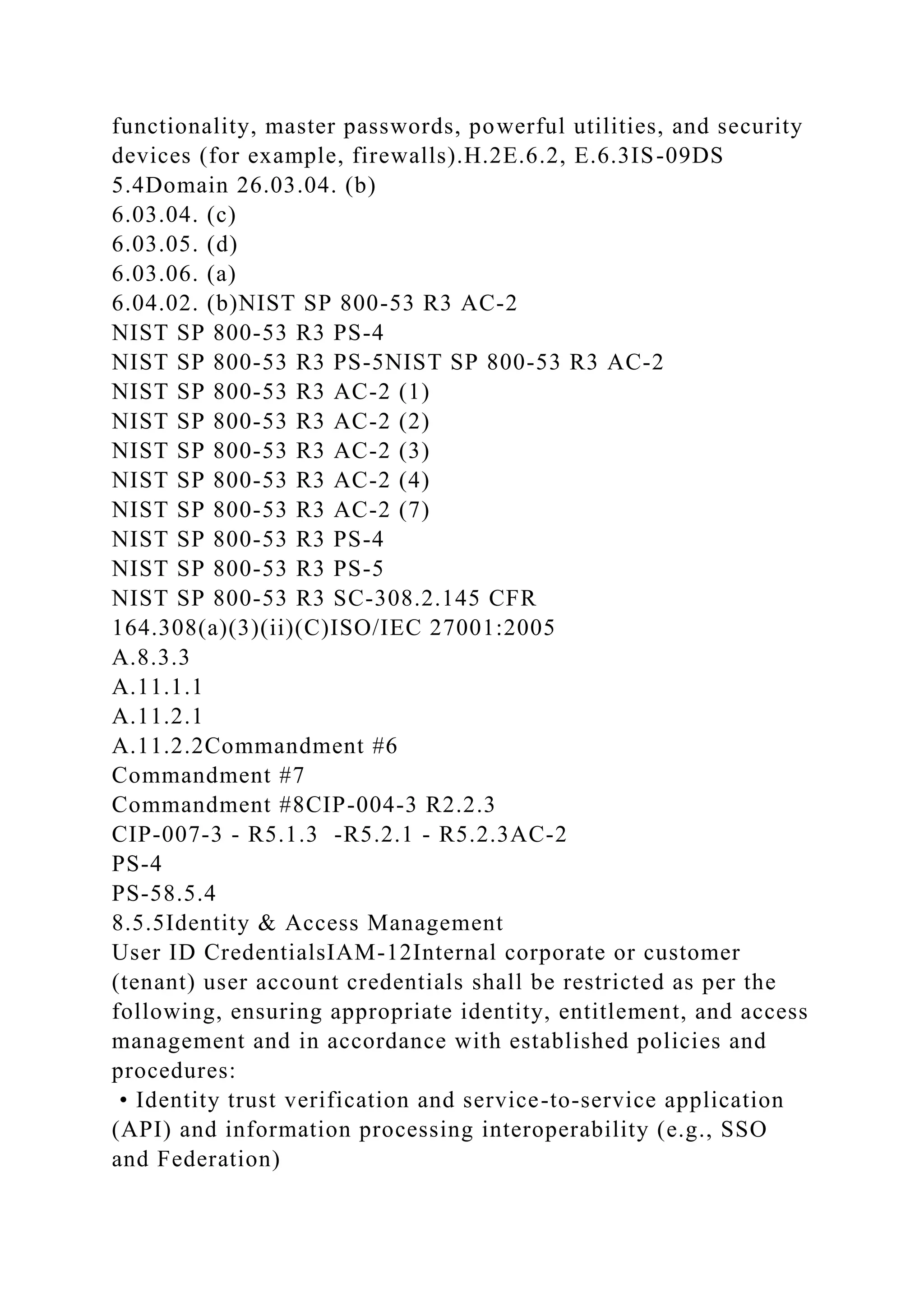
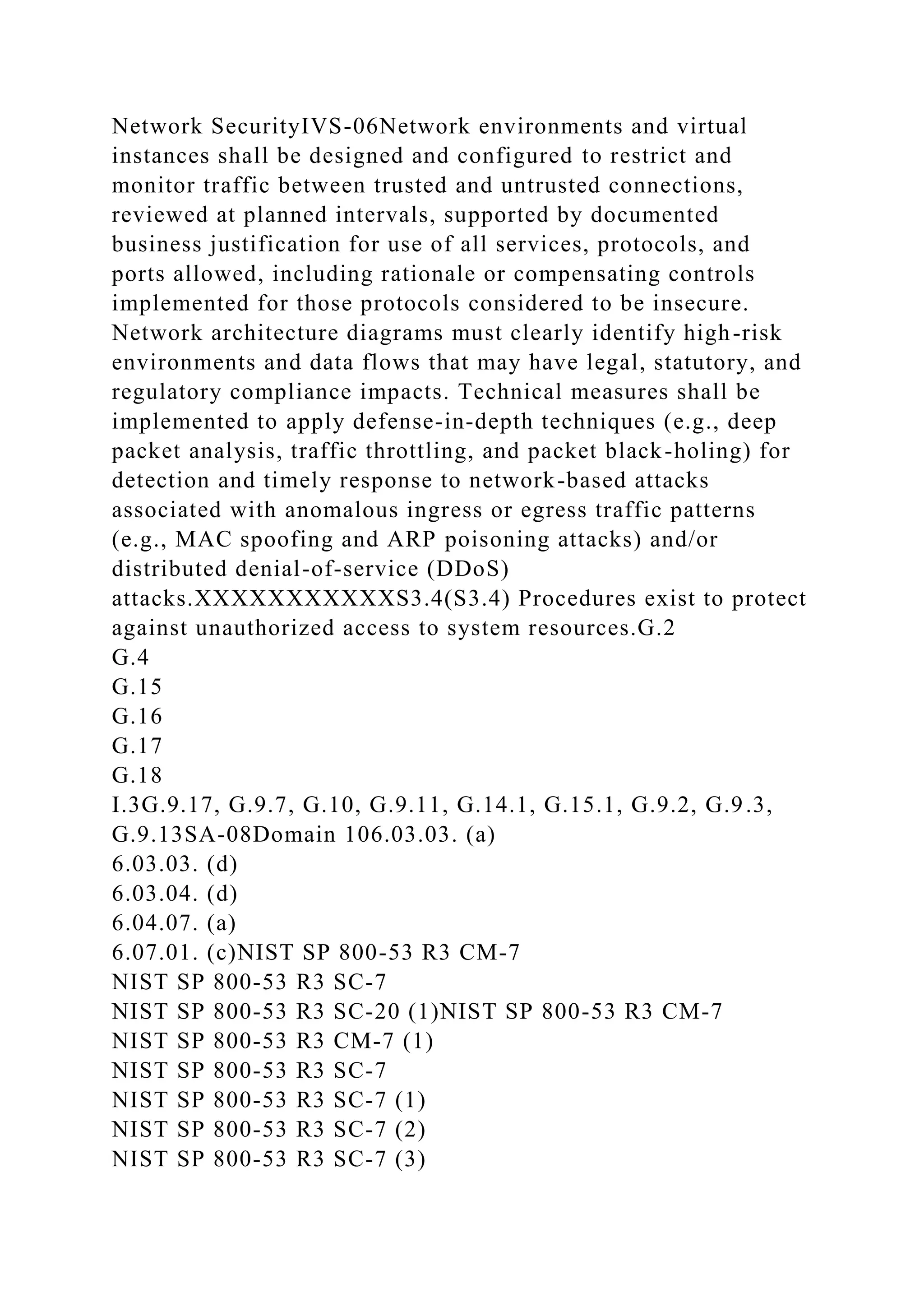
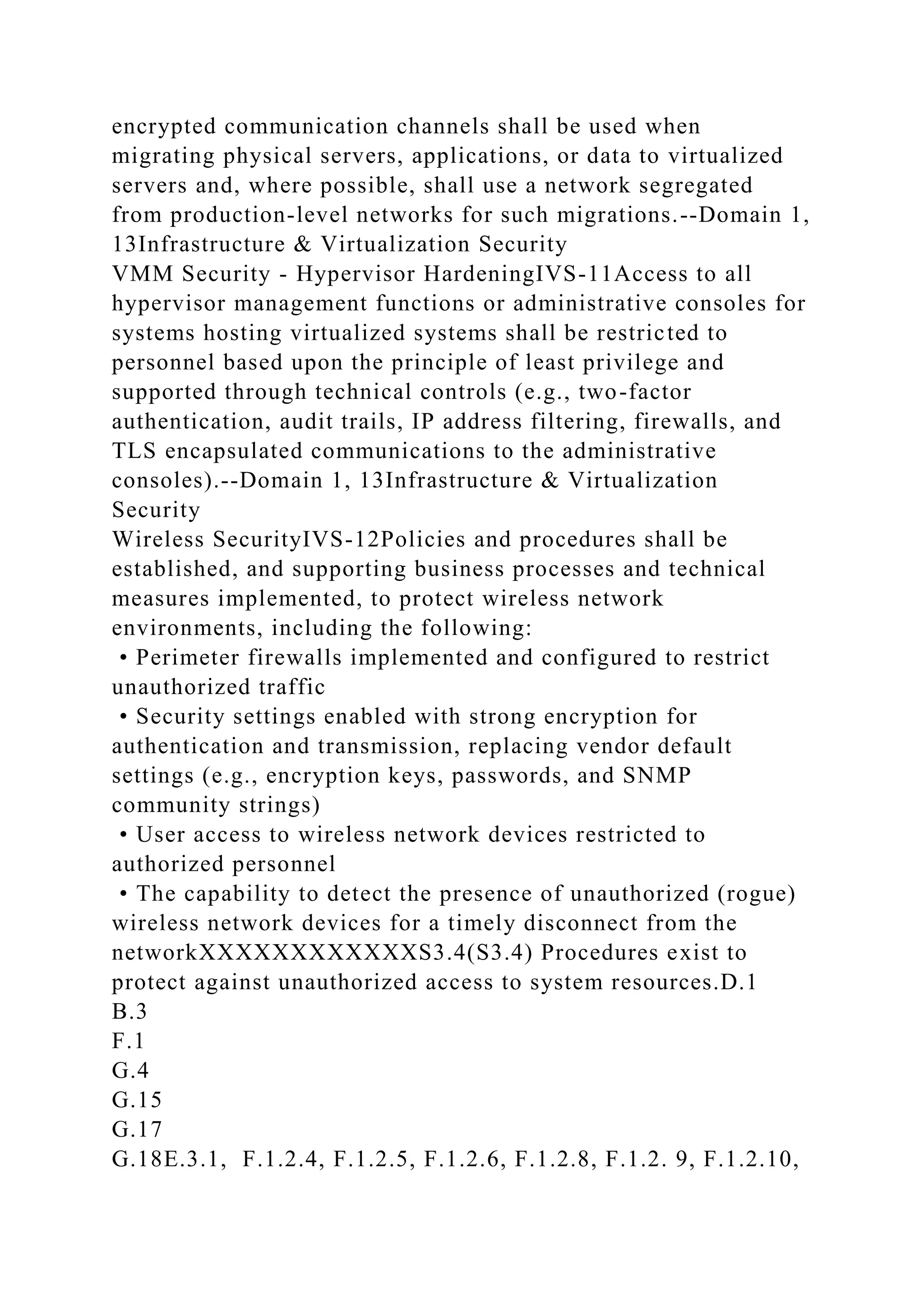
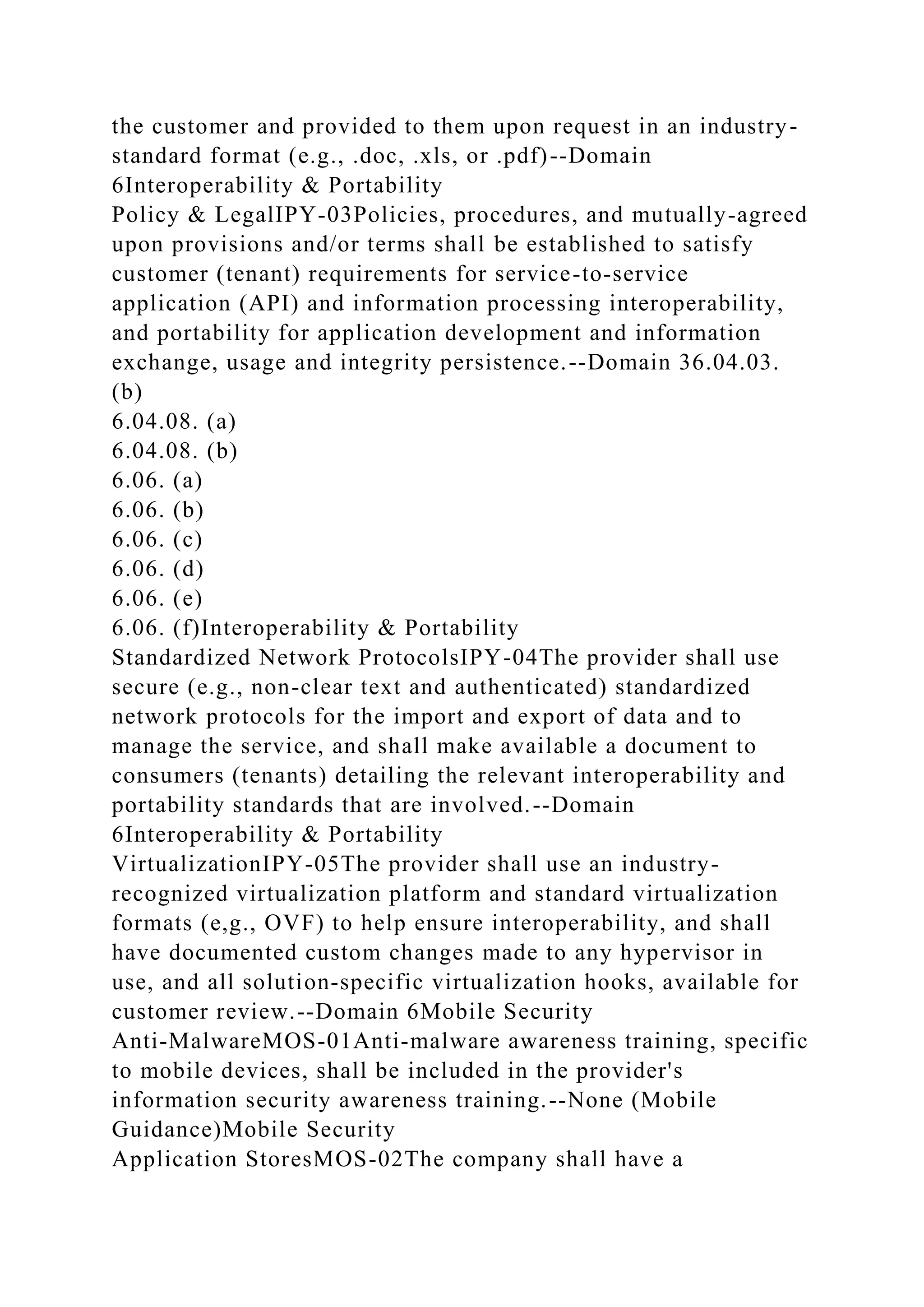
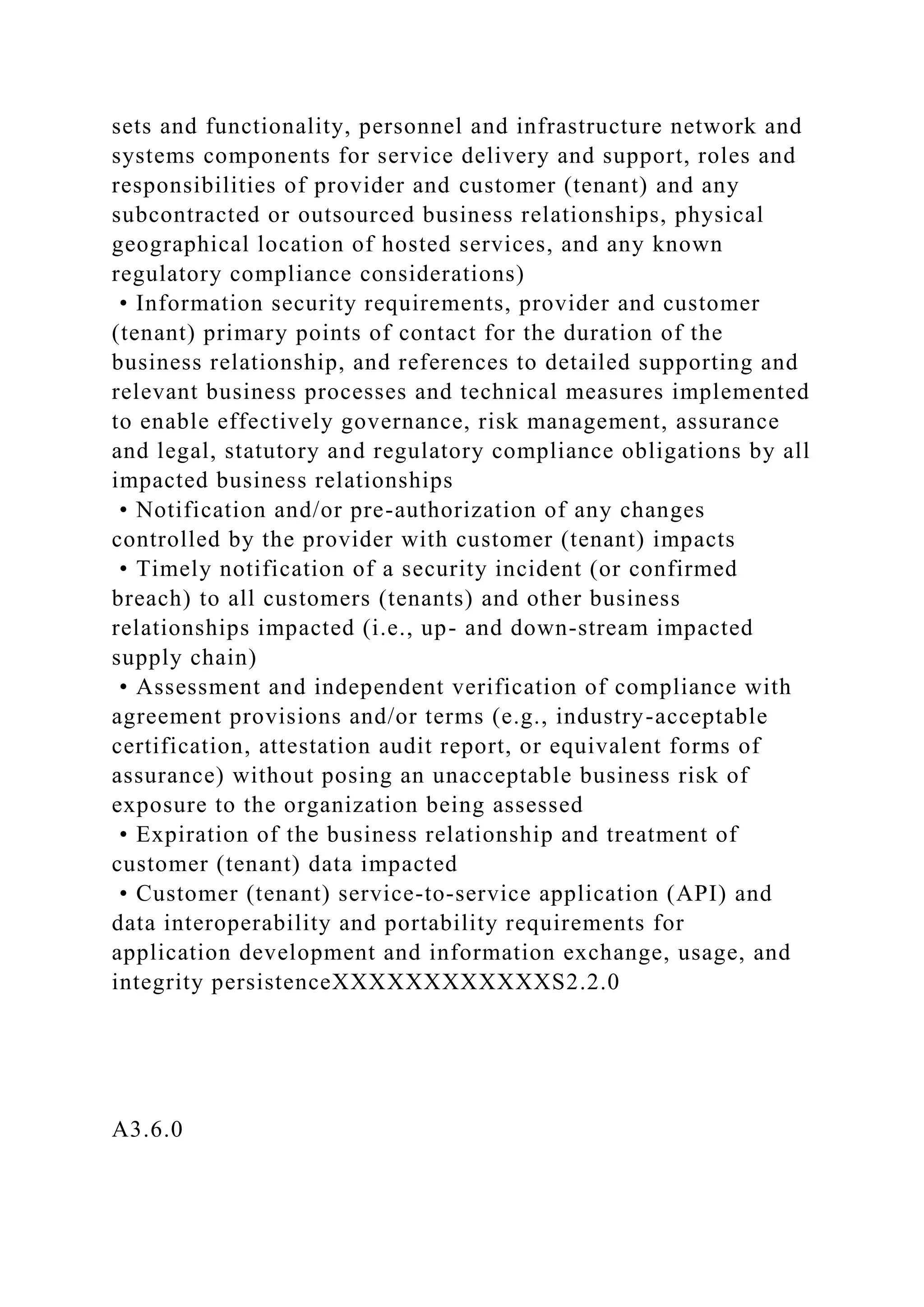
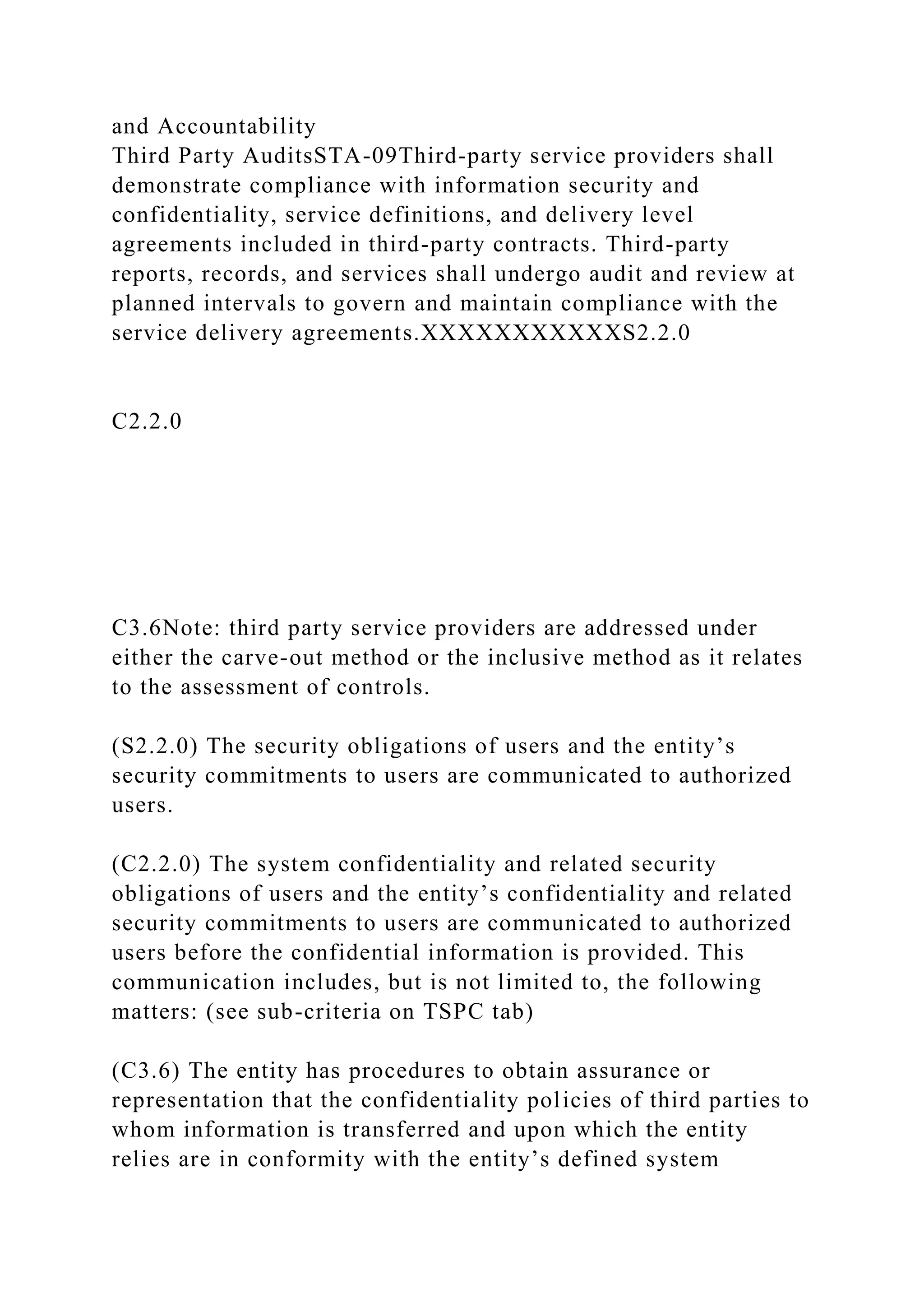
![CIP-009-3 - R.1.1PL-5
RA-2
RA-312.1.2Governance and Risk Management
Risk Management FrameworkGRM-11Organizations shall
develop and maintain an enterprise risk management framework
to mitigate risk to an acceptable level.XXXXXXXXXXXXS3.1
x3.1.0(S3.1) Procedures exist to (1) identify potential threats of
disruption to systems operation that would impair system
security commitments and (2) assess the risks associated with
the identified threats.
(x3.1.0) Procedures exist to (1) identify potential threats of
disruptions to systems operation that would impair system
[availability, processing integrity, confidenitality] commitments
and (2) assess the risks associated with the identified
threats.L.2A.1, L.1RI-01PO 9.1Domain 2, 4NIST SP 800-53 R3
AC-1
NIST SP 800-53 R3 AT-1
NIST SP 800-53 R3 AU-1
NIST SP 800-53 R3 CA-1
NIST SP 800-53 R3 CA-6
NIST SP 800-53 R3 CA-7
NIST SP 800-53 R3 PL-1
NIST SP 800-53 R3 RA-1
NIST SP 800-53 R3 RA-2
NIST SP 800-53 R3 RA-3NIST SP 800-53 R3 AC-1
NIST SP 800-53 R3 AT-1
NIST SP 800-53 R3 AU-1
NIST SP 800-53 R3 CA-1
NIST SP 800-53 R3 CA-6
NIST SP 800-53 R3 CA-7
NIST SP 800-53 R3 PL-1](https://image.slidesharecdn.com/csaccmv3-230108121115-6a39b129/75/CSA-CCM-V3-0CLOUD-CONTROLS-MATRIX-VERSION-3-0Control-DomainCCM-V3-docx-77-2048.jpg)
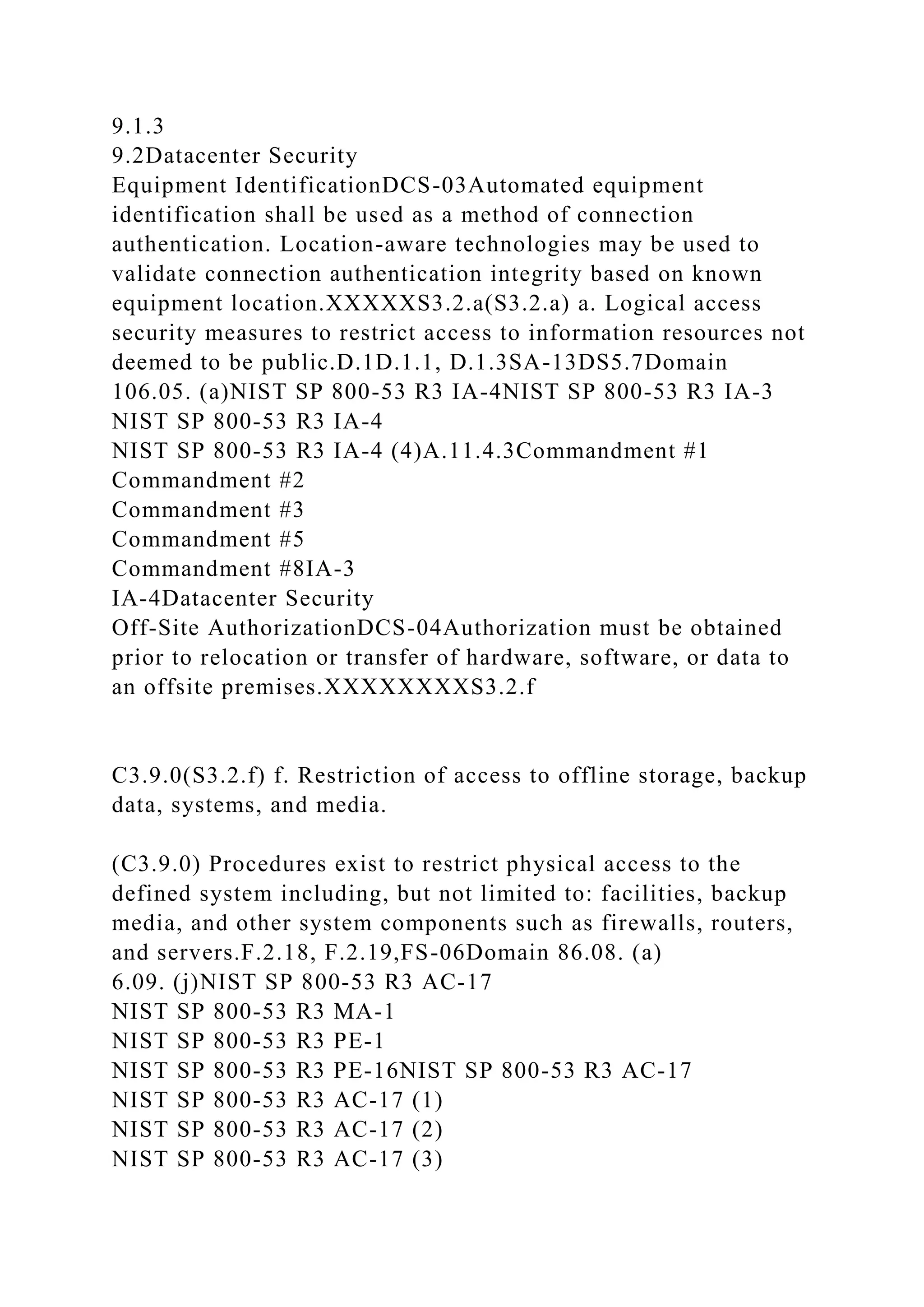
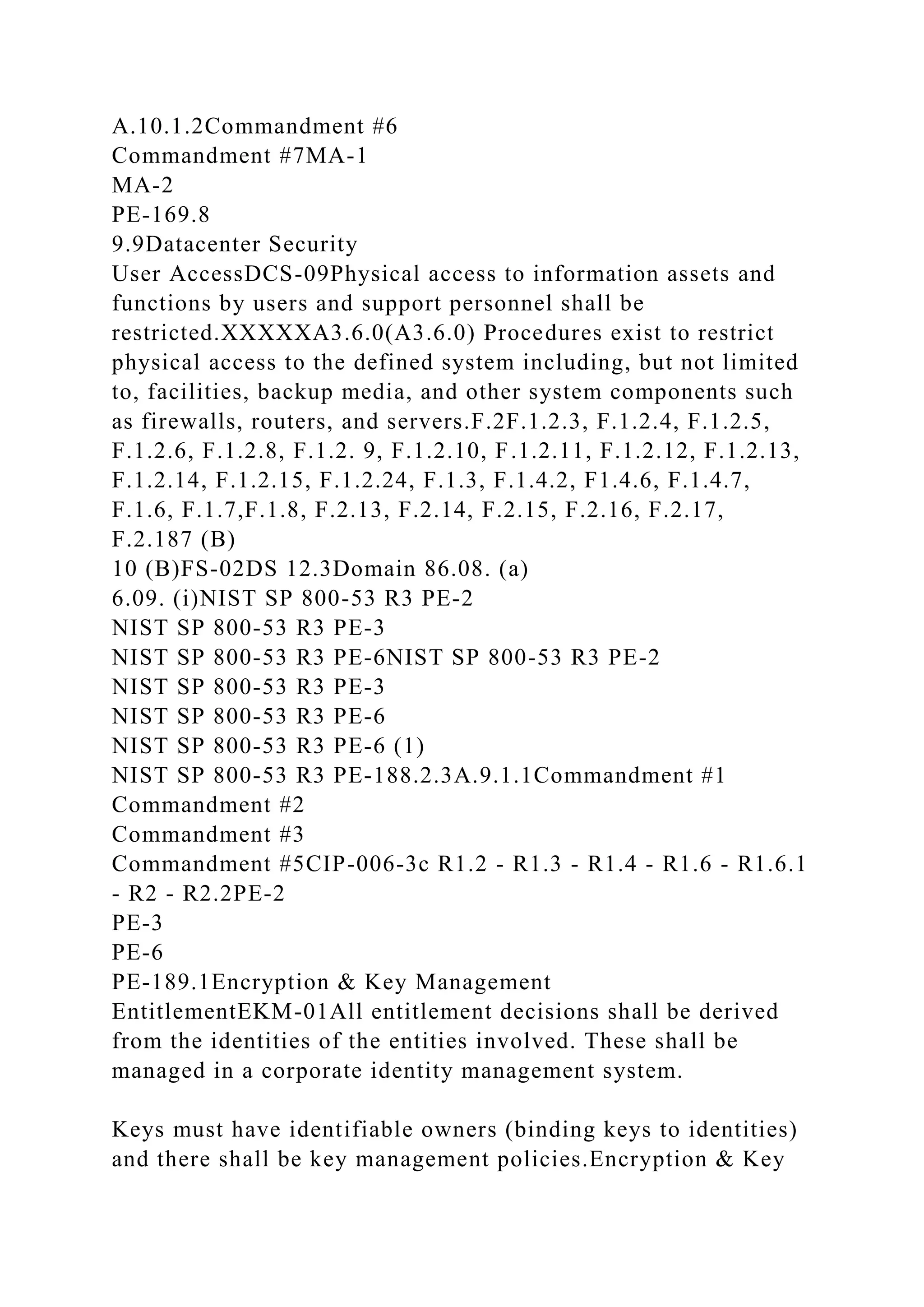
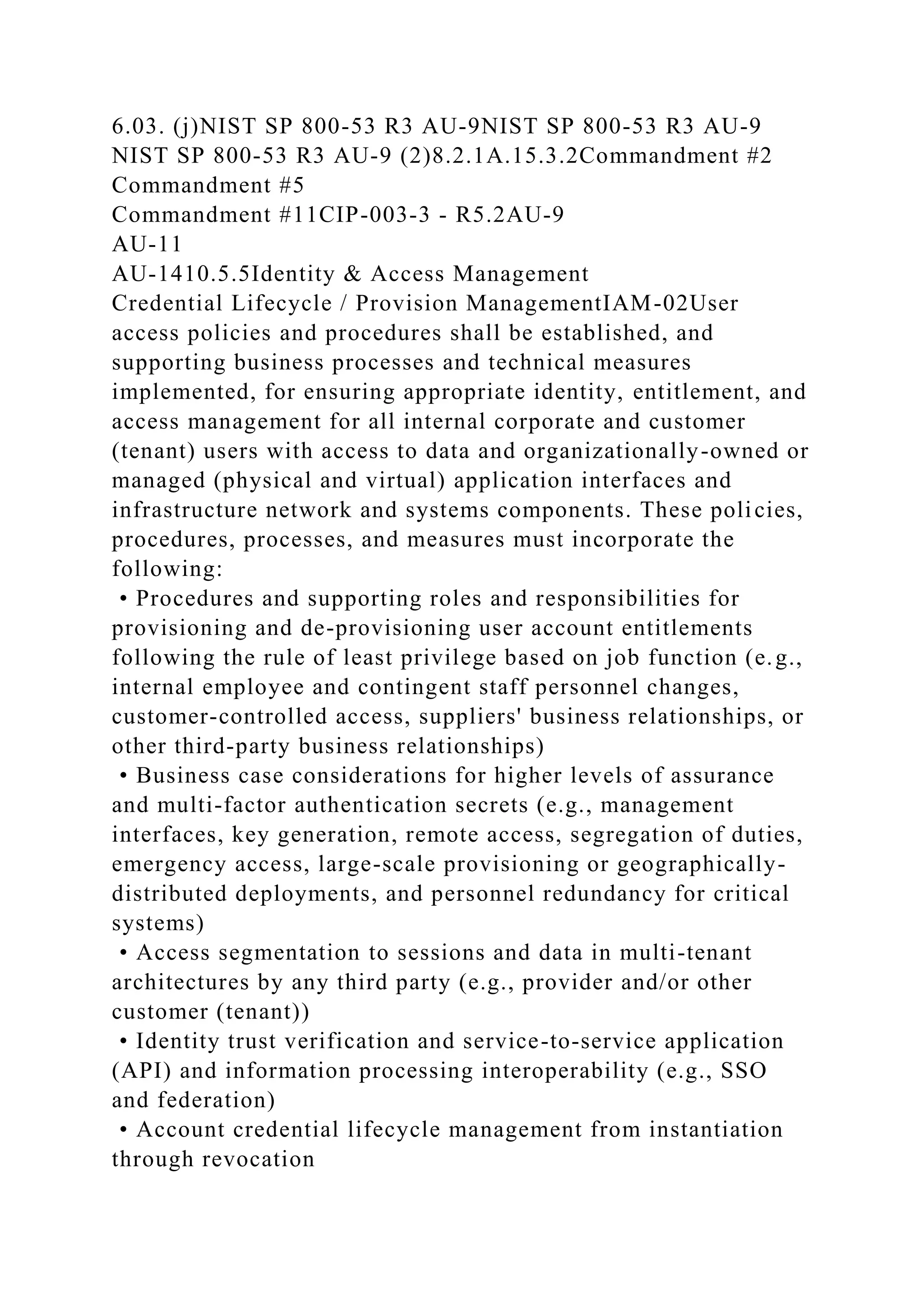
![the identified threats.
(x3.1.0) Procedures exist to (1) identify potential threats of
disruptions to systems operation that would impair system
[availability, processing integrity, confidenitality] commitments
and (2) assess the risks associated with the identified threats.I.4
L.2I.3, L.9, L.1043 (C+, A+)RI-03PO 9.5Domain 2, 4NIST SP
800-53 R3 CA-5
NIST SP 800-53 R3 CP-1
NIST SP 800-53 R3 RA-1NIST SP 800-53 R3 CA-5
NIST SP 800-53 R3 CP-1
NIST SP 800-53 R3 RA-145 CFR 164.308 (a)(1)(ii)(B)Clause
4.2.1 c) through g)
Clause 4.2.2 b)
Clause 4.3.1
Clause 5.1 f)
Clause 7.3
A.6.2.1
A.12.5.2
A.12.6.1
A.15.1.1
A.15.2.1
A.15.2.2CIP-009-3 - R1.2CA-5
CM-4Human Resources
Asset ReturnsHRS-01Upon termination of workforce personnel
and/or expiration of external business relationships, all
organizationally-owned assets shall be returned within an
established period.XXXXXXXXXXXXS3.4(S3.4) Procedures
exist to protect against unauthorized access to system
resources.D.1E.6.4IS-27Domain 2NIST SP 800-53 R3 PS-
4NIST SP 800-53 R3 PS-45.2.3
7.2.2
8.2.1
8.2.645 CFR 164.308 (a)(3)(ii)(C)A.7.1.1
A.7.1.2
A.8.3.2PS-4Human Resources](https://image.slidesharecdn.com/csaccmv3-230108121115-6a39b129/75/CSA-CCM-V3-0CLOUD-CONTROLS-MATRIX-VERSION-3-0Control-DomainCCM-V3-docx-79-2048.jpg)
![x3.1.0(S3.1) Procedures exist to (1) identify potential threats of
disruption to systems operation that would impair system
security commitments and (2) assess the risks associated with
the identified threats.
(x3.1.0) Procedures exist to (1) identify potential threats of
disruptions to systems operation that would impair system
[availability, processing integrity, confidenitality] commitments
and (2) assess the risks associated with the identified
threats.B.1
H.2B.1.1, B.1.2, D.1.1, E.1, F.1.1, H.1.1, K.1.1, E.6.2, E.6.3RI-
05DS 2.3Domain 2, 46.02. (a)
6.02. (b)
6.03. (a)NIST SP 800-53 R3 AC-1
NIST SP 800-53 R3 AT-1
NIST SP 800-53 R3 AU-1
NIST SP 800-53 R3 CA-1
NIST SP 800-53 R3 CM-1
NIST SP 800-53 R3 CP-1
NIST SP 800-53 R3 IA-1
NIST SP 800-53 R3 IA-5
NIST SP 800-53 R3 IA-5 (1)
NIST SP 800-53 R3 IR-1
NIST SP 800-53 R3 MA-1
NIST SP 800-53 R3 MP-1
NIST SP 800-53 R3 PE-1
NIST SP 800-53 R3 PL-1
NIST SP 800-53 R3 PS-1
NIST SP 800-53 R3 RA-1
NIST SP 800-53 R3 SA-1
NIST SP 800-53 R3 SC-1
NIST SP 800-53 R3 SI-1NIST SP 800-53 R3 AC-1
NIST SP 800-53 R3 AT-1
NIST SP 800-53 R3 AU-1
NIST SP 800-53 R3 CA-1](https://image.slidesharecdn.com/csaccmv3-230108121115-6a39b129/75/CSA-CCM-V3-0CLOUD-CONTROLS-MATRIX-VERSION-3-0Control-DomainCCM-V3-docx-95-2048.jpg)
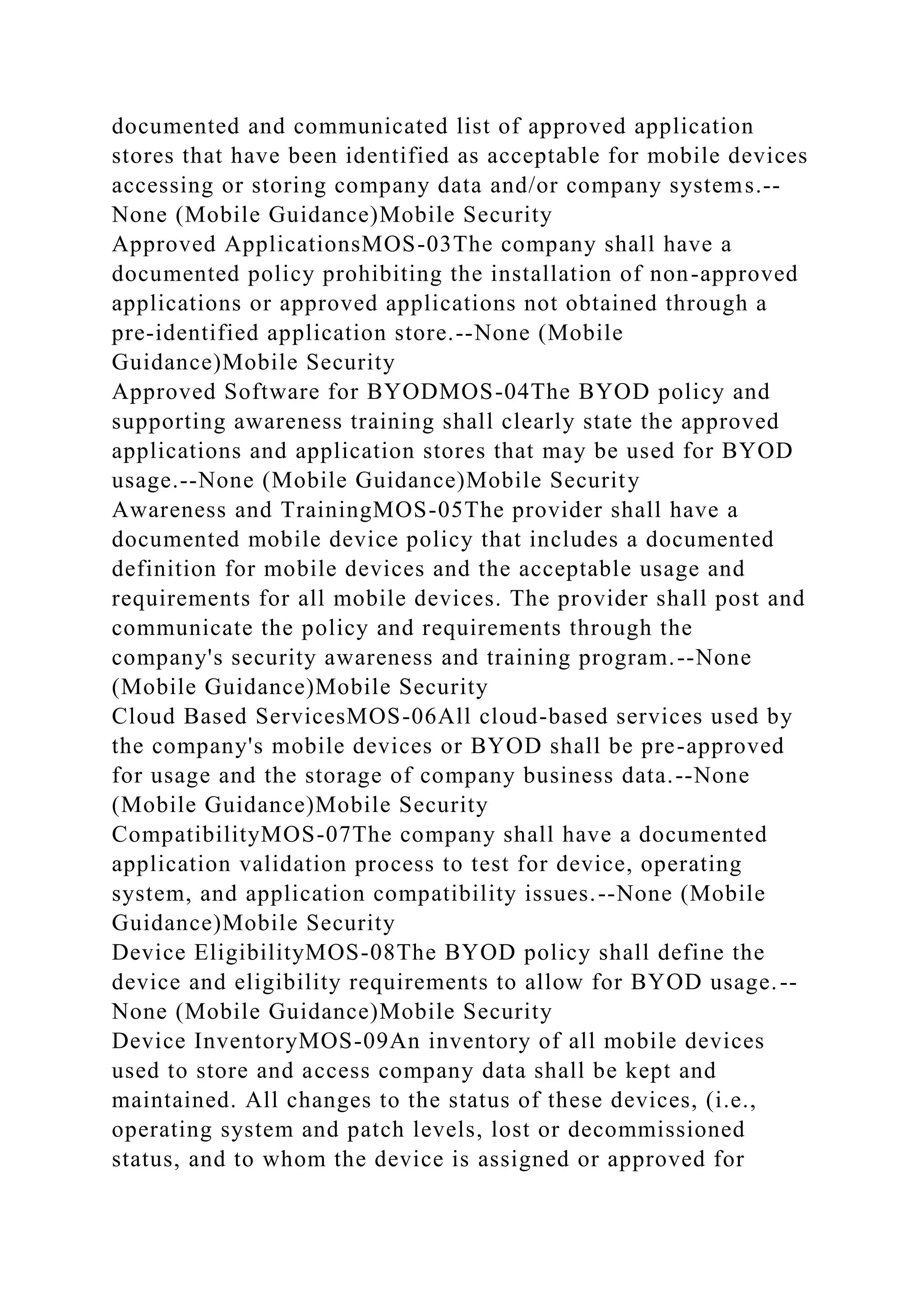
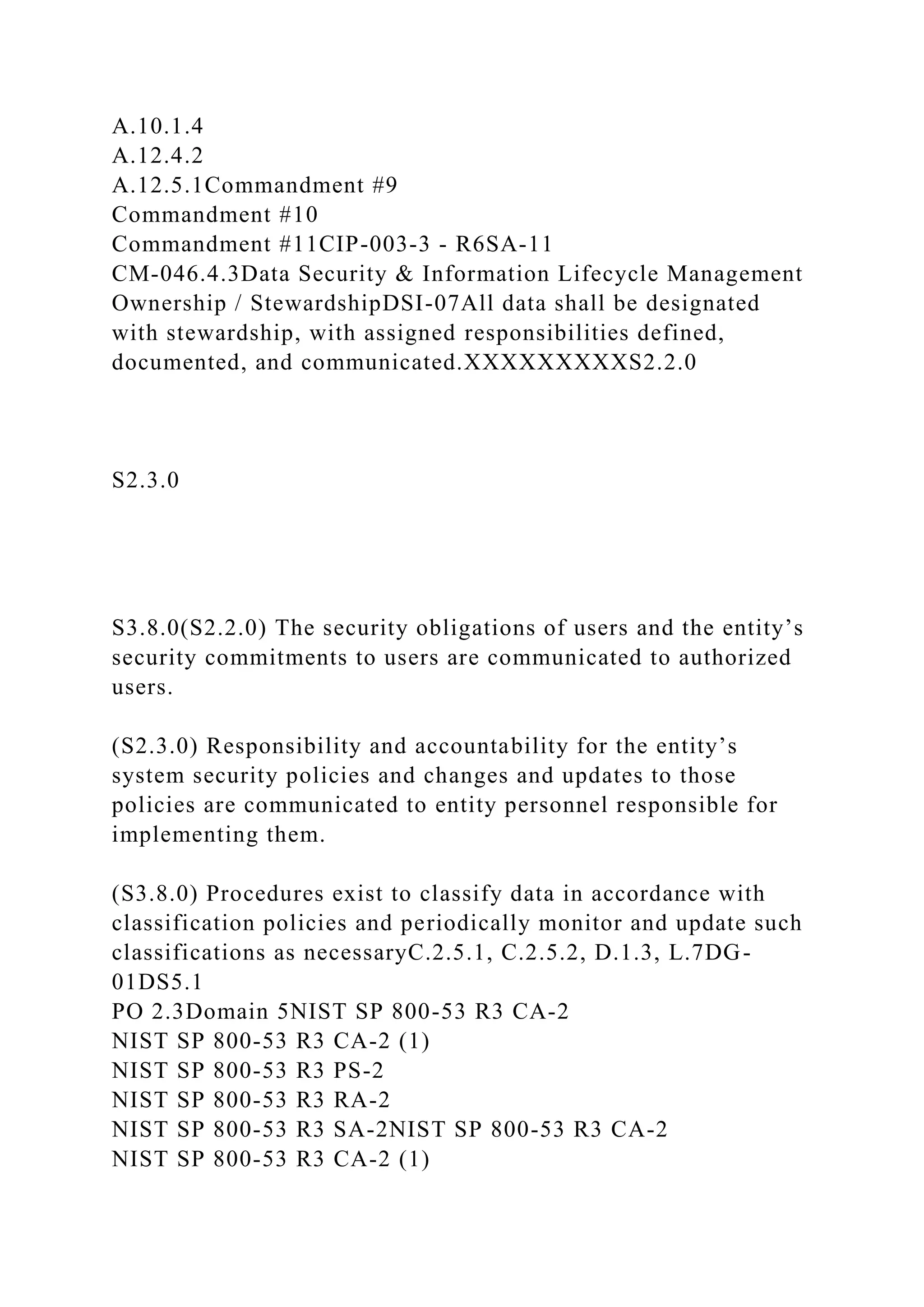
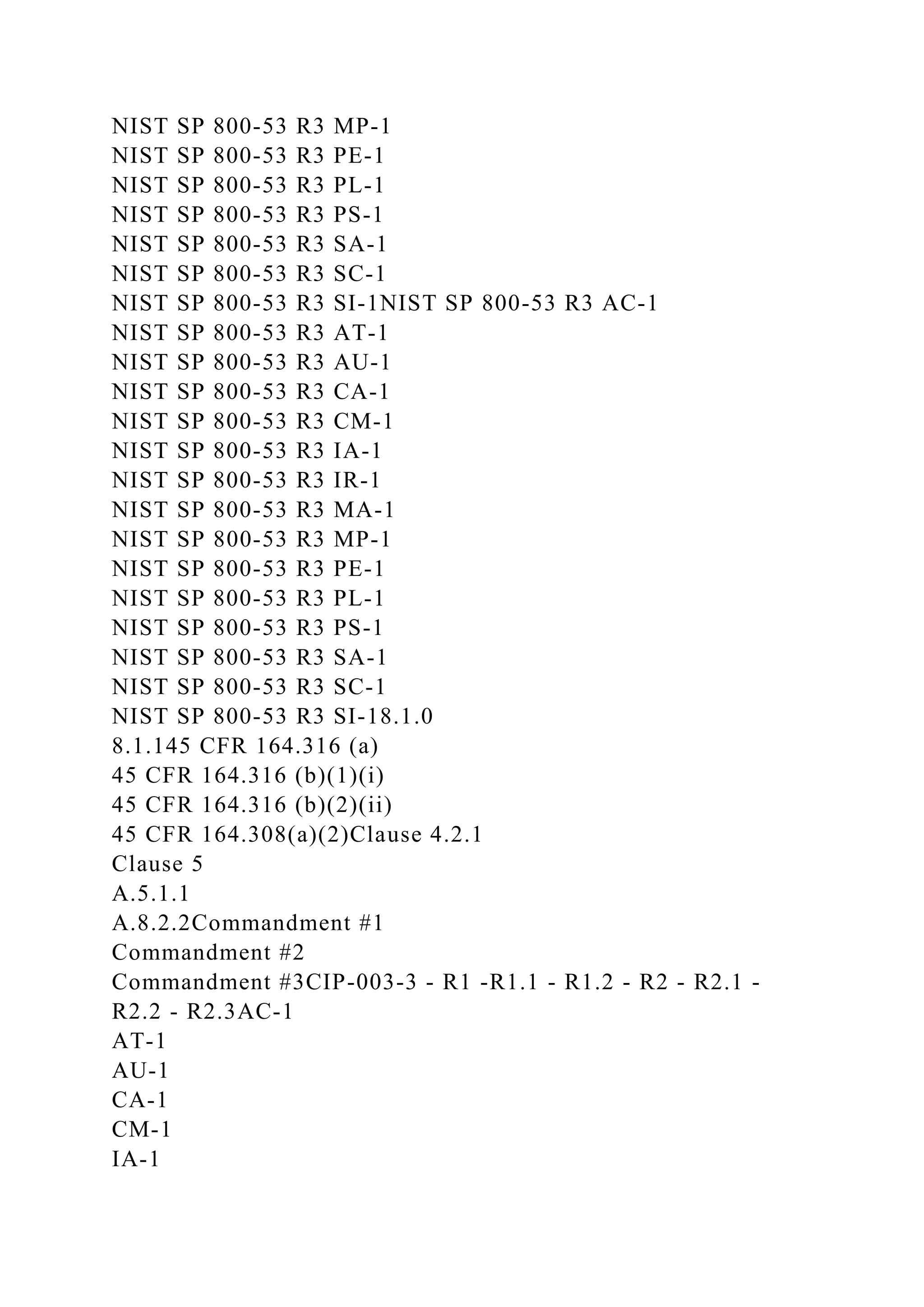
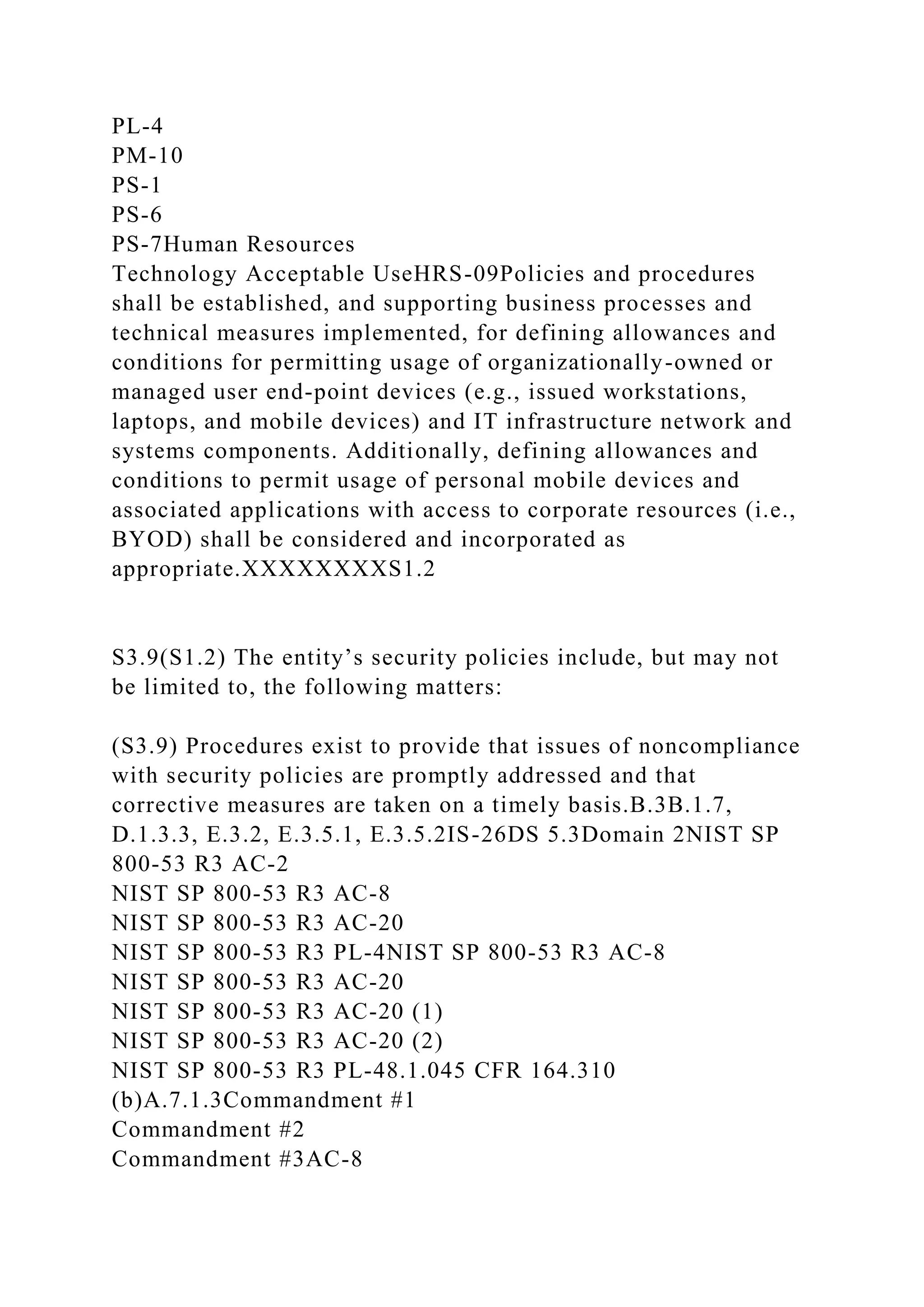
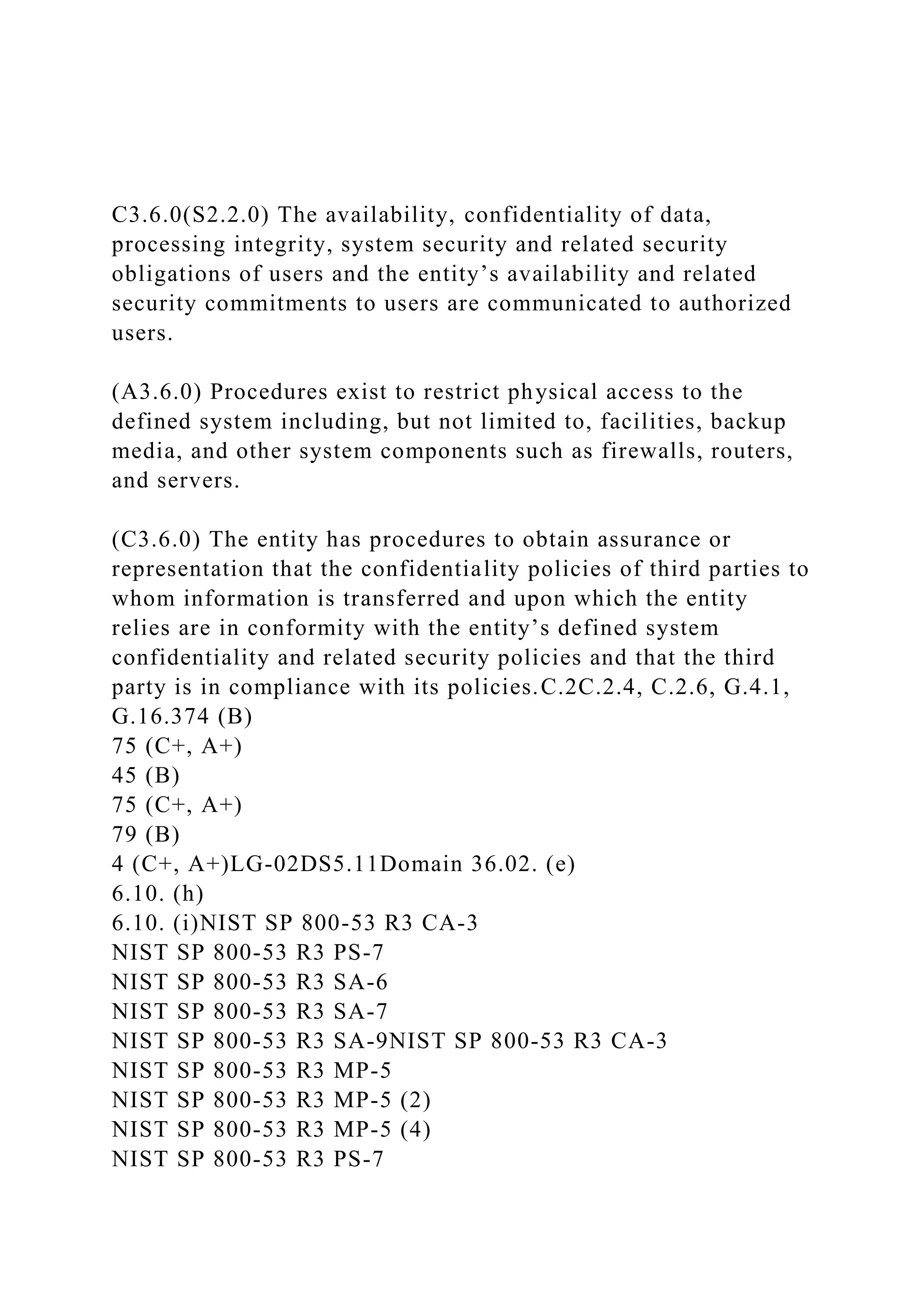
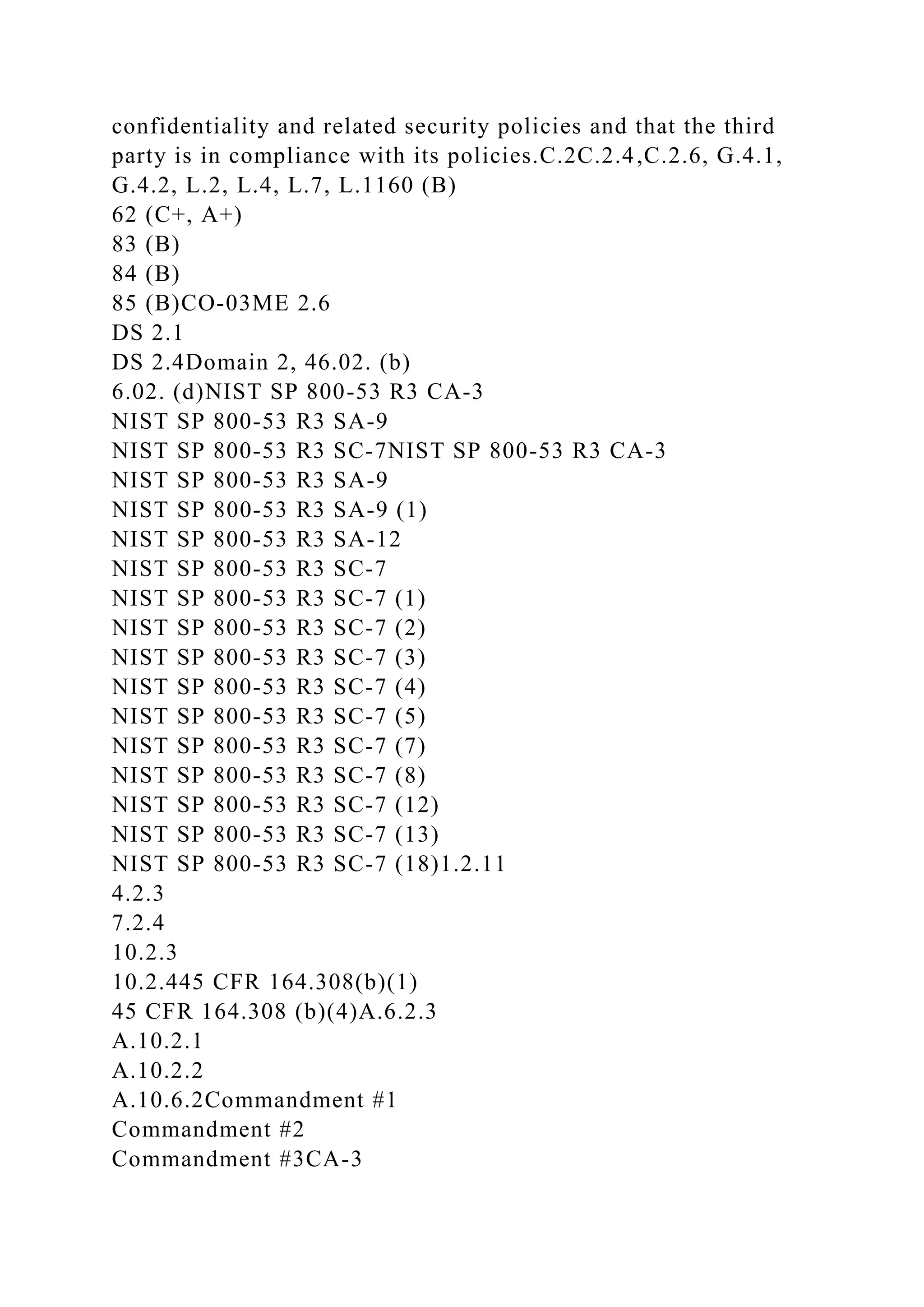
![x4.4.0(S4.3.0) Environmental, regulatory, and technological
changes are monitored and their effect on system security is
assessed on a timely basis and policies are updated for that
assessment.
(x4.4.0) Environmental, regulatory, and technological changes
are monitored, and their impact on system [availability,
processing integrity, confidentiality] and security is assessed on
a timely basis. System [availability, processing integrity,
confidentiality] policies and procedures are updated for such
changes as required.L1CO-04ME 3.1Domain 2, 4NIST SP 800-
53 R3 IR-6
NIST SP 800-53 R3 SI-5NIST SP 800-53 R3 IR-6
NIST SP 800-53 R3 IR-6 (1)
NIST SP 800-53 R3 SI-51.2.7
10.1.1
10.2.4A.6.1.6
A.6.1.7Commandment #1
Commandment #2
Commandment #3CIP-001-1a R3 - R4AT-5
IR-6
SI-511.1.e
12.5.3
12.9Security Incident Management, E-Discovery & Cloud
Forensics
Incident ManagementSEF-02Policies and procedures shall be
established, and supporting business processes and technical
measures implemented, to triage security-related events and
ensure timely and thorough incident management, as per
established IT service management policies and
procedures.XXXXXXXXXXXXIS3.7.0](https://image.slidesharecdn.com/csaccmv3-230108121115-6a39b129/75/CSA-CCM-V3-0CLOUD-CONTROLS-MATRIX-VERSION-3-0Control-DomainCCM-V3-docx-121-2048.jpg)
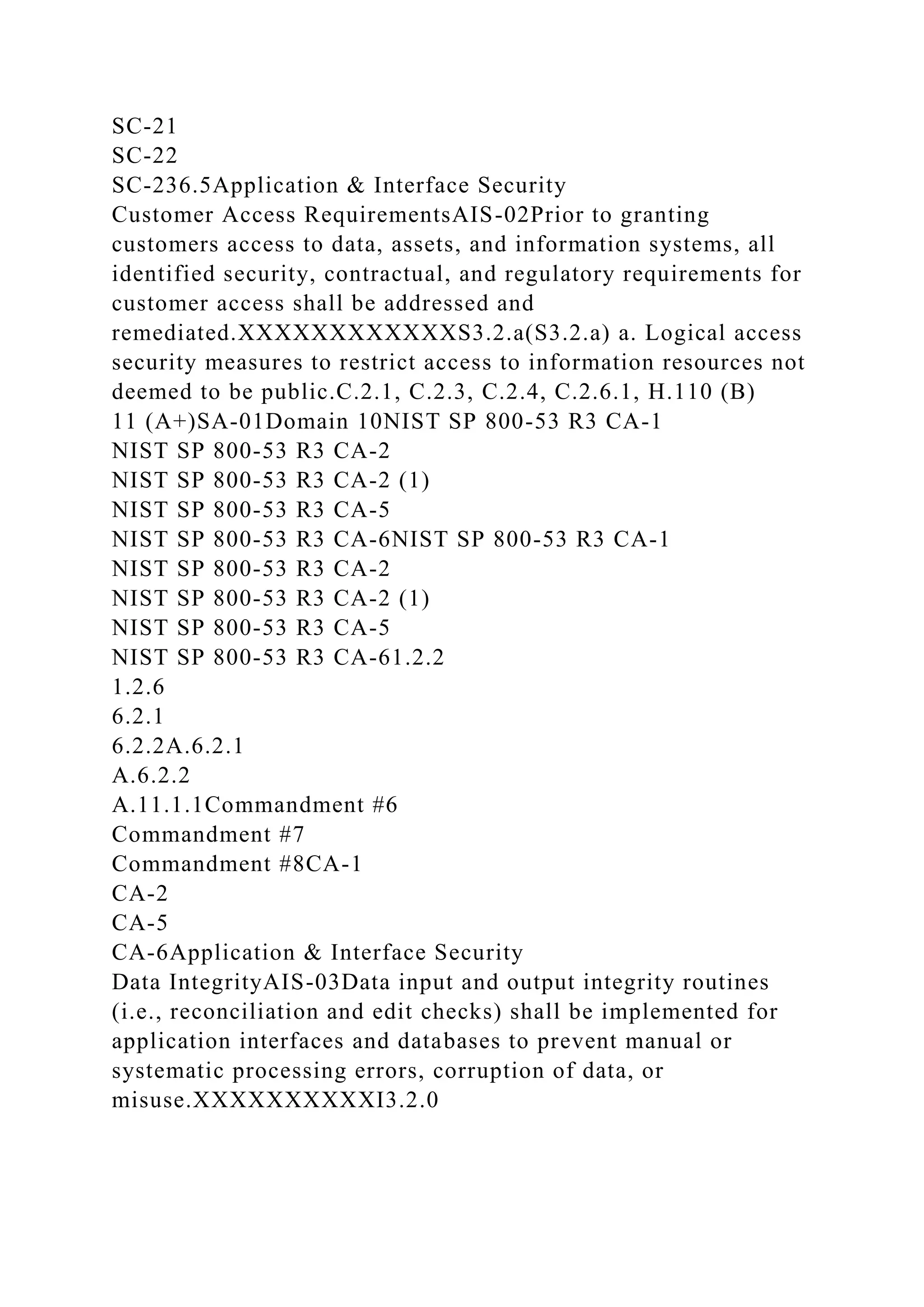
![system without explicit installation or execution by the
recipient, on organizationally-owned or managed user end-point
devices (e.g., issued workstations, laptops, and mobile devices)
and IT infrastructure network and systems
components.XXXXXXXXXS3.4.0
S3.10.0(S3.4.0) Procedures exist to protect against infection by
computer viruses, malicious code, and unauthorized software.
(S3.10.0) Design, acquisition, implementation, configuration,
modification, and management of infrastructure and software
are consistent with defined system security policies to enable
authorized access and to prevent unauthorized access.G.20.12,
I.2.5SA-15Domain 106.03. (g)A.10.4.2
A.12.2.2Commandment #1
Commandment #2
Commandment #3
Commandment #5
Commandment #11SC-18Copyright © 2013 Cloud Security
Alliance. All rights reserved. You may download, store, display
on your computer, view, print, and link to the Cloud Security
Alliance “Cloud Controls Matrix (CCM) Version 3.0” at
http://www.cloudsecurityalliance.org subject to the following:
(a) the Cloud Controls Matrix v3.0 may be used solely for your
personal, informational, non-commercial use; (b) the Cloud
Controls Matrix v3.0 may not be modified or altered in any
way; (c) the Cloud Controls Matrix v3.0 may not be
redistributed; and (d) the trademark, copyright or other notices
may not be removed. You may quote portions of the Cloud
Controls Matrix v3.0 as permitted by the Fair Use provisions of
the United States Copyright Act, provided that you attribute the
portions to the Cloud Security Alliance Cloud Controls Matrix
Version 3.0 (2013). If you are interested in obtaining a license
to this material for other usages not addressed in the copyright
notice, please contact [email protected]](https://image.slidesharecdn.com/csaccmv3-230108121115-6a39b129/75/CSA-CCM-V3-0CLOUD-CONTROLS-MATRIX-VERSION-3-0Control-DomainCCM-V3-docx-139-2048.jpg)