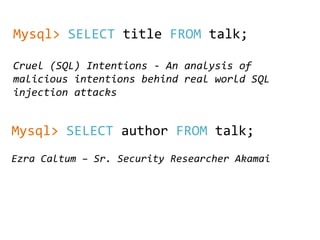
Cruel (SQL) Intentions
•Download as PPTX, PDF•
2 likes•738 views
The document analyzes SQL injection attacks from data collected from Akamai's platform protecting over 167,000 servers. It shows that over 59% of SQL injections were for probing and testing, while over 23% were for credential theft. The summary at the end states that malicious actors use a variety of techniques in SQL injections, including data exfiltration, privilege escalation, executing commands, infecting or corrupting data, and denial of service.
Report
Share
Report
Share
Recommended
Time Series Analysis for Network Secruity

How Endgame is using the scientific computing stack in Python to find anomalies in network flow data.
Everything you always wanted to know about datetime types but didn’t have tim...

How to avoid the most common pitfalls of date and time types in MySQL
Oracle 122 partitioning_in_action_slide_share

Managing data with an RDBMS is probably one of the key IT resources for roughly 40 years. Splitting up logical data structures into physical ones also known as partitioning is a key ingredient. The attached presentation demonstrates examples based on the recently released Oracle 12.2 database.
Update as of May 31st 2017: You might ask yourself: is this any practical? Yes it is. We are currently creating a bit of code to complement the example.
E34 : [JPOUG Presents] Oracle Database の隠されている様々な謎を解くセッション「なーんでだ?」再び @ db tec...![E34 : [JPOUG Presents] Oracle Database の隠されている様々な謎を解くセッション「なーんでだ?」再び @ db tec...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![E34 : [JPOUG Presents] Oracle Database の隠されている様々な謎を解くセッション「なーんでだ?」再び @ db tec...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
E34 : [JPOUG Presents] Oracle Database の隠されている様々な謎を解くセッション「なーんでだ?」再び @ db tech showcase 2015 Tokyo
Perth APAC Groundbreakers tour - SQL Techniques

Get more out of the database by exploiting the rich suite of features available with the SQL language. We cover pivot, unpivot, rollup, pagination, error logging, query block naming
Recommended
Time Series Analysis for Network Secruity

How Endgame is using the scientific computing stack in Python to find anomalies in network flow data.
Everything you always wanted to know about datetime types but didn’t have tim...

How to avoid the most common pitfalls of date and time types in MySQL
Oracle 122 partitioning_in_action_slide_share

Managing data with an RDBMS is probably one of the key IT resources for roughly 40 years. Splitting up logical data structures into physical ones also known as partitioning is a key ingredient. The attached presentation demonstrates examples based on the recently released Oracle 12.2 database.
Update as of May 31st 2017: You might ask yourself: is this any practical? Yes it is. We are currently creating a bit of code to complement the example.
E34 : [JPOUG Presents] Oracle Database の隠されている様々な謎を解くセッション「なーんでだ?」再び @ db tec...![E34 : [JPOUG Presents] Oracle Database の隠されている様々な謎を解くセッション「なーんでだ?」再び @ db tec...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![E34 : [JPOUG Presents] Oracle Database の隠されている様々な謎を解くセッション「なーんでだ?」再び @ db tec...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
E34 : [JPOUG Presents] Oracle Database の隠されている様々な謎を解くセッション「なーんでだ?」再び @ db tech showcase 2015 Tokyo
Perth APAC Groundbreakers tour - SQL Techniques

Get more out of the database by exploiting the rich suite of features available with the SQL language. We cover pivot, unpivot, rollup, pagination, error logging, query block naming
ViSeQR: Etichette come impronte digitali

Una semplice etichetta, equiparabile ad una impronta “digitale” si trasforma in un timbro intelligente anticontraffazione e non riproducibile, a tutela del produttore, del consumatore e della tracciabilità.
Gli ambiti di utilizzo di questa tecnologia, facilmente utilizzabile attraverso app gratuite, spaziano dalla moda all’agroalimentare, dal farmaceutico al documentale e coprono ogni area delle produzioni industriali.
Examples of Required Documents

Contains examples of required documents for submission to film permitting authorities. You can check us out at www.dronetechaerial.com . Los Angeles Legal drone Company FAA 333 Exempt, Drone Tech Aerial Cinematography
100 preguntas-sobre-sexualidad-adolescente

Libro de la I.Municipalidad de Santiago que busca responder dudas de los adolescentes sobre sexualidad.
Lean Innovation: l’opportunità concreta di dare nuovo valore all’impresa 

Ottimizzare tempi, spazi e risorse implica da una parte la ricerca costante di nuove soluzioni, dall’altra conduce al miglioramento netto della propria attività, è una delle sfide epocali più importanti non solo per il vantaggio della singola impresa, ma per quello più generale di una economia che necessariamente deve rendersi sempre più responsabile e sostenibile.
Advance MySQL Training by Pratyush Majumdar

MySQL training on advance topics like Stored Procedures, Triggers, Partition, Indexing, Replication and Monitoring.
Streaming ETL - from RDBMS to Dashboard with KSQL

Apache Kafka is a massively scalable message queue that is being used at more and more places connecting more and more data sources. This presentation will introduce Kafka from the perspective of a mere mortal DBA and share the experience of (and challenges with) getting events from the database to Kafka using Kafka connect including poor-man’s CDC using flashback query and traditional logical replication tools. To demonstrate how and why this is a good idea, we will build an end-to-end data processing pipeline. We will discuss how to turn changes in database state into events and stream them into Apache Kafka. We will explore the basic concepts of streaming transformations using windows and KSQL before ingesting the transformed stream in a dashboard application.
Performance Schema for MySQL Troubleshooting

Percona Live (https://www.percona.com/live/data-performance-conference-2016/sessions/performance-schema-mysql-troubleshooting)
The performance schema in MySQL version 5.6, released in February, 2013, is a very powerful tool that can help DBAs discover why even the trickiest performance issues occur. Version 5.7 introduces even more instruments and tables. And while all these give you great power, you can get stuck choosing which instrument to use.
In this session, I will start with a description of a typical problem, then guide you how to use the performance schema to find out what causes the issue, the reason for unwanted behavior and how the received information can help you solve a particular problem.
Traditionally, performance schema sessions teach what is in contained in tables. I will, in contrast, start from a performance issue, then demonstrate which instruments and tables can help solve it. We will discuss how to setup the performance schema so that it has minimal impact on your server.
5 Cool Things About SQL

The AskTOM Archive - selected presentations from Tom Kyte from Oracle 2000-2015
MySQL Kitchen : spice up your everyday SQL queries

A journey into lesser known MySQL functions, that will help you make the most out of your data and tables.
More Related Content
Viewers also liked
ViSeQR: Etichette come impronte digitali

Una semplice etichetta, equiparabile ad una impronta “digitale” si trasforma in un timbro intelligente anticontraffazione e non riproducibile, a tutela del produttore, del consumatore e della tracciabilità.
Gli ambiti di utilizzo di questa tecnologia, facilmente utilizzabile attraverso app gratuite, spaziano dalla moda all’agroalimentare, dal farmaceutico al documentale e coprono ogni area delle produzioni industriali.
Examples of Required Documents

Contains examples of required documents for submission to film permitting authorities. You can check us out at www.dronetechaerial.com . Los Angeles Legal drone Company FAA 333 Exempt, Drone Tech Aerial Cinematography
100 preguntas-sobre-sexualidad-adolescente

Libro de la I.Municipalidad de Santiago que busca responder dudas de los adolescentes sobre sexualidad.
Lean Innovation: l’opportunità concreta di dare nuovo valore all’impresa 

Ottimizzare tempi, spazi e risorse implica da una parte la ricerca costante di nuove soluzioni, dall’altra conduce al miglioramento netto della propria attività, è una delle sfide epocali più importanti non solo per il vantaggio della singola impresa, ma per quello più generale di una economia che necessariamente deve rendersi sempre più responsabile e sostenibile.
Viewers also liked (13)
Lean Innovation: l’opportunità concreta di dare nuovo valore all’impresa 

Lean Innovation: l’opportunità concreta di dare nuovo valore all’impresa
Similar to Cruel (SQL) Intentions
Advance MySQL Training by Pratyush Majumdar

MySQL training on advance topics like Stored Procedures, Triggers, Partition, Indexing, Replication and Monitoring.
Streaming ETL - from RDBMS to Dashboard with KSQL

Apache Kafka is a massively scalable message queue that is being used at more and more places connecting more and more data sources. This presentation will introduce Kafka from the perspective of a mere mortal DBA and share the experience of (and challenges with) getting events from the database to Kafka using Kafka connect including poor-man’s CDC using flashback query and traditional logical replication tools. To demonstrate how and why this is a good idea, we will build an end-to-end data processing pipeline. We will discuss how to turn changes in database state into events and stream them into Apache Kafka. We will explore the basic concepts of streaming transformations using windows and KSQL before ingesting the transformed stream in a dashboard application.
Performance Schema for MySQL Troubleshooting

Percona Live (https://www.percona.com/live/data-performance-conference-2016/sessions/performance-schema-mysql-troubleshooting)
The performance schema in MySQL version 5.6, released in February, 2013, is a very powerful tool that can help DBAs discover why even the trickiest performance issues occur. Version 5.7 introduces even more instruments and tables. And while all these give you great power, you can get stuck choosing which instrument to use.
In this session, I will start with a description of a typical problem, then guide you how to use the performance schema to find out what causes the issue, the reason for unwanted behavior and how the received information can help you solve a particular problem.
Traditionally, performance schema sessions teach what is in contained in tables. I will, in contrast, start from a performance issue, then demonstrate which instruments and tables can help solve it. We will discuss how to setup the performance schema so that it has minimal impact on your server.
5 Cool Things About SQL

The AskTOM Archive - selected presentations from Tom Kyte from Oracle 2000-2015
MySQL Kitchen : spice up your everyday SQL queries

A journey into lesser known MySQL functions, that will help you make the most out of your data and tables.
Beyond php - it's not (just) about the code

Most PHP developers focus on writing code. But creating Web applications is about much more than just wrting PHP. Take a step outside the PHP cocoon and into the big PHP ecosphere to find out how small code changes can make a world of difference on servers and network. This talk is an eye-opener for developers who spend over 80% of their time coding, debugging and testing.
A few things about the Oracle optimizer - 2013

The AskTOM Archive - selected presentations from Tom Kyte from Oracle Corporation 2010-2015.
Checking clustering factor to detect row migration

Checking clustering factor to detect row migration
Performance schema and sys schema

The MySQL sys schema was integrated fully into MySQL Server from version 5.7.7 and has been improved in MySQL 8.0. Whether you are a DBA trying to determine where the resources are being used on your database instance and by whom, or a developer trying to figure out why your MySQL statements are running too slowly, the MySQL sys schema can help. Join this session to learn how to better use the MySQL sys schema to answer your day-to-day questions—from the original developer of the MySQL sys schema.
Fulltext engine for non fulltext searches

Or better said when Sphinx can help MySQL on queries that at first look they don’t involve any fulltext searching.
Sphinx was build in mind to help the DB on fulltext queries. But it can also help on where there is no text search. That is everyday used queries with combined filtering,grouping and sorting used for various analytics, reporting of simply general usage.
In Sphinx, the fulltext query is executed first, creating a result set that is passed to the remaining operations ( filters, groups, sorts). By reducing the size of the set that is interogated, the whole query will not be only faster, but it will consume less resources.
Because of design for speed, Sphinx can group and sort a lot faster and can do easy segmentations or getting top-N best group matches in a single query.
The result will be offloading heavy work done by database nodes to even a single Sphinx server.
Slides were presented at PerconaLive London 2013
Similar to Cruel (SQL) Intentions (20)
Using Optimizer Hints to Improve MySQL Query Performance

Using Optimizer Hints to Improve MySQL Query Performance
MySQL Kitchen : spice up your everyday SQL queries

MySQL Kitchen : spice up your everyday SQL queries
Applied Partitioning And Scaling Your Database System Presentation

Applied Partitioning And Scaling Your Database System Presentation
Checking clustering factor to detect row migration

Checking clustering factor to detect row migration
Recently uploaded
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI)
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

Reflecting on new architectures for knowledge based systems in light of generative ai
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic (NeSy) AI is on the rise. However, simply machine learning on just any symbolic structure is not sufficient to really harvest the gains of NeSy. These will only be gained when the symbolic structures have an actual semantics. I give an operational definition of semantics as “predictable inference”.
All of this illustrated with link prediction over knowledge graphs, but the argument is general.
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of Product, Slack
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

In this session I delve into the encryption technology used in Microsoft 365 and Microsoft Purview. Including the concepts of Customer Key and Double Key Encryption.
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovation With Your Product by VP of Product Design, Warner Music Group
Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality

In this insightful webinar, Inflectra explores how artificial intelligence (AI) is transforming software development and testing. Discover how AI-powered tools are revolutionizing every stage of the software development lifecycle (SDLC), from design and prototyping to testing, deployment, and monitoring.
Learn about:
• The Future of Testing: How AI is shifting testing towards verification, analysis, and higher-level skills, while reducing repetitive tasks.
• Test Automation: How AI-powered test case generation, optimization, and self-healing tests are making testing more efficient and effective.
• Visual Testing: Explore the emerging capabilities of AI in visual testing and how it's set to revolutionize UI verification.
• Inflectra's AI Solutions: See demonstrations of Inflectra's cutting-edge AI tools like the ChatGPT plugin and Azure Open AI platform, designed to streamline your testing process.
Whether you're a developer, tester, or QA professional, this webinar will give you valuable insights into how AI is shaping the future of software delivery.
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase Enterprise-Wide Efficiency by VP Data Platform, American Express
Recently uploaded (20)
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

To Graph or Not to Graph Knowledge Graph Architectures and LLMs
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic is not enough, we need neuro-*semantic*
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

Encryption in Microsoft 365 - ExpertsLive Netherlands 2024
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
Monitoring Java Application Security with JDK Tools and JFR Events

Monitoring Java Application Security with JDK Tools and JFR Events
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality

Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase E...
Cruel (SQL) Intentions
- 1. Cruel (SQL) Intentions - An analysis of malicious intentions behind real world SQL injection attacks Ezra Caltum – Sr. Security Researcher Akamai Mysql> SELECT title FROM talk; Mysql> SELECT author FROM talk;
- 2. • The Platform • 167,000+ Servers • 2,300+ Locations • 750+ Cities • 92 Countries • 1,227+ Networks • The Data • 2 trillion hits per day • 780 million unique IPv4 addresses seen quarterly • 13+ trillion log lines per day • 260+ terabytes of compressed daily logs 15 - 30% of all web traffic
- 3. Mysql> SELECT COUNT(DISTINCT days) FROM research_data; +-------+ | days | +-------+ | 7 | +-------+
- 4. Mysql> SELECT COUNT(DISTINCT apps) FROM research_data; +-------+ | apps | +-------+ | 2000 | +-------+
- 5. Mysql> SELECT COUNT(DISTINCT injections) FROM research_data; +--------------+ | injections | +--------------+ | 8,425,489 | +--------------+
- 6. Mysql> SELECT COUNT(DISTINCT injections) as injections, COUNT(DISTINCT injections)/8425489 as percentage FROM research_data WHERE category = 'SQL INJECTION PROBING AND INJECTION TESTING'; +------------+-----------------------+ |injections | percentage | +------------+-----------------------+ | 5,021,240 | 59.59% | +------------+-----------------------+
- 7. Mysql> SELECT COUNT(DISTINCT injections) as injections, COUNT(DISTINCT injections)/8425489 as percentage, COUNT(DISTINCT injections)/3406249 as norm_perc FROM research_data WHERE category = 'ENVIROMENT PROBING AND TESTING'; +------------+-----------------------+ | injections | percentage | norm_perc| +------------+-----------------------+ | 1,308,681 | 15.5% | 38.42% | +------------+------------+----------+
- 8. Mysql> SELECT COUNT(DISTINCT injections) as injections, COUNT(DISTINCT injections)/8425489 as percentage, COUNT(DISTINCT injections)/3406249 as norm_perc FROM research_data WHERE category = 'DATABASE CONTENT RETRIEVAL'; +------------+-----------------------+ | injections | percentage | norm_perc| +------------+-----------------------+ | 129,814 | 1.5403% | 3.811054%| +------------+-----------------------+
- 9. Mysql> SELECT COUNT(DISTINCT injections) as injections, COUNT(DISTINCT injections)/8425489 as percentage, COUNT(DISTINCT injections)/3406249 as norm_perc FROM research_data WHERE category = 'CREDENTIAL THEFT'; +------------+-----------------------+ | injections | percentage | norm_perc| +------------+-----------------------+ | 1,950,749 | 23.14745% |57.269712%| +------------+-----------------------+
- 10. Mysql> SELECT COUNT(DISTINCT injections) as injections, COUNT(DISTINCT injections)/8425489 as percentage, COUNT(DISTINCT injections)/3406249 as norm_perc FROM research_data WHERE category = 'LOGIN BYPASS'; +------------+-----------------------+ | injections | percentage | norm_perc| +------------+-----------------------+ | 5,467 | 00.064871%|00.160499%| +------------+-----------------------+
- 11. Mysql> SELECT COUNT(DISTINCT injections) as injections, COUNT(DISTINCT injections)/8425489 as percentage, COUNT(DISTINCT injections)/3406249 as norm_perc FROM research_data WHERE category = 'DATA FILE EXTRACTION'; +------------+-----------------------+ | injections | percentage | norm_perc| +------------+-----------------------+ | 24 | 0.00028% |0.0007% | +------------+-----------------------+
- 12. Mysql> SELECT COUNT(DISTINCT injections) as injections, COUNT(DISTINCT injections)/8425489 as percentage, COUNT(DISTINCT injections)/3406249 as norm_perc FROM research_data WHERE category = 'DENIAL OF SERVICE'; +------------+-----------------------+ | injections | percentage | norm_perc| +------------+-----------------------+ | 326 | 0.00387% | 0.009571%| +------------+-----------------------+
- 13. Mysql> SELECT COUNT(DISTINCT injections) as injections, COUNT(DISTINCT injections)/8425489 as percentage, COUNT(DISTINCT injections)/3406249 as norm_perc FROM research_data WHERE category = 'DATA CORRUPTION'; +------------+-----------------------+ | injections | percentage | norm_perc| +------------+-----------------------+ | 2,238 | 0.026556% | 0.065702%| +------------+-----------------------+
- 14. Mysql> SELECT COUNT(DISTINCT injections) as injections, COUNT(DISTINCT injections)/8425489 as percentage, COUNT(DISTINCT injections)/3406249 as norm_perc FROM research_data WHERE category = 'DEFACEMENT AND CONTENT INJECTION'; +------------+-----------------------+ | injections | percentage | norm_perc| +------------+-----------------------+ |8,156 | 0.096778% |0.239442% | +------------+-----------------------+
- 15. Mysql> SELECT COUNT(DISTINCT injections) as injections, COUNT(DISTINCT injections)/8425489 as percentage, COUNT(DISTINCT injections)/3406249 as norm_perc FROM research_data WHERE category = 'RCE'; +------------+-----------------------+ | injections | percentage | norm_perc| +------------+-----------------------+ | 794 | 0.00942% | 0.023310%| +------------+-----------------------+
- 16. Mysql> SELECT summary FROM talk +------------+-----------------------+ | summary +------------+-----------------------+ |Malicious actors use a variety of | |of techniques. | |Not only data exfiltration, but: | |Elevate privileges, execute commands,| |infect or corrupt data, deny service | +------------+-----------------------+
- 17. DROP /**/ TABLE talk; Twitter: @aCaltum http://ezra.c.com.mx http://www.stateoftheinternet.com
- 18. SELECT questions FROM attendees WHERE (used_time + question_time) <= 15;