CQI-IRCA 27001:2013 Lead Auditor Course
•
1 like•100 views
Enrol now in our upcoming Virtual classroom ISO27001:2013 Lead Auditor course 24 to 28 August 2020. Only a few seats remaining. contact desmond.muchetu@bureauveritas.com
Report
Share
Report
Share
Download to read offline
Recommended
Security audits & compliance

The document provides an overview of security audits and compliance based on the ISO 27001:2013 standard. It defines key terms, describes the three pillars of information security and types of audits. It introduces ISO 27001, outlines the framework's 13 control domains and objectives. The document explains how to conduct a security audit from initiation to follow up and closure of nonconformities. It stresses that audits are about improvement, not fault finding, and ensuring unbiased reviews.
ISO 27001:2013 Implementation procedure

This document outlines 35 steps to implement an ISO 27001:2013 information security management system (ISMS) from scratch. The steps are divided into four phases: plan, do, check, and act. The planning phase involves obtaining management approval, understanding the organization and its needs, defining the ISMS scope and objectives. The doing phase includes performing risk assessments, selecting controls, and implementing risk treatment plans. The checking phase consists of monitoring performance, auditing, and collecting feedback. The acting phase is for reviewing performance, deciding on improvements, and planning corrective actions.
Iso27001 Audit Services

The document discusses ISO 27001 internal audit requirements and challenges with conducting internal audits. It proposes two approaches for outsourcing ISO 27001 audits to an external firm: 1) co-sourcing where the firm provides audit resources under the organization's direction, or 2) a managed assurance service where the firm develops and runs the entire audit program. The benefits cited include overcoming resourcing challenges, ensuring objectivity, and focusing internal resources on high risk areas.
Presentation on iso 27001-2013, Internal Auditing and BCM

The document is a presentation summarizing an internship at an IT company working on three projects: 1) Creating a roadmap for transitioning to ISO 27001:2013 which involved gap analysis and updating controls. 2) Mapping the internal auditing process which involves scheduling, preparing, conducting, and reporting on audits. 3) Analyzing a specific business continuity scenario which included identifying critical processes, calculating response times, and planning infrastructure and response to incidents. The internship provided learning around differences in standards, assessing controls, conducting audits, and creating business continuity plans.
Iso 27001 metrics and implementation guide

This document provides implementation tips and potential metrics for ISO/IEC 27001 and 27002. It covers tips and metrics for each control objective in ISO/IEC 27002 sections 4 through 15. The tips are meant to help others implementing the ISO information security standards in their organization. The document is collaboratively created and copyrighted but licensed for sharing and derivative works.
Iso 22301 la training

ISO Lead Auditor Certification Training Course has a five-day intensive course that enables participants to develop the necessary expertise to audit a Business Continuity Management System (BCMS) and to manage a team of auditors by applying widely recognized audit principles, procedures, and techniques.
Cloud Computing | Cloud Security | Cloud Computing Audit Checklist | 499 Chec...

In depth and exhaustive ISO 27001 Checklist covers compliance requirements on Cloud Computing. The Checklist on cloud security Contains downloadable file of 3 Excel Sheets having 499 checklist Questions, complete list of Clauses, and list of 114 Information Security Controls, 35 control objectives, and 14 domains. URL link is mentioned below-
https://www.isocertificationtrainingcourse.org/online-store/ISO-27001-Checklist-ISO-27001-Audit-Checklist-ISO-27001-Compliance-checklist-c28241136
A18 compliance

This presentation explains the control A.18 of ISO 27001 : 2013 which is "Compliance".
Courtesy:
http://www.ifour-consultany.com
http://www.ifourtechnolab.com
Recommended
Security audits & compliance

The document provides an overview of security audits and compliance based on the ISO 27001:2013 standard. It defines key terms, describes the three pillars of information security and types of audits. It introduces ISO 27001, outlines the framework's 13 control domains and objectives. The document explains how to conduct a security audit from initiation to follow up and closure of nonconformities. It stresses that audits are about improvement, not fault finding, and ensuring unbiased reviews.
ISO 27001:2013 Implementation procedure

This document outlines 35 steps to implement an ISO 27001:2013 information security management system (ISMS) from scratch. The steps are divided into four phases: plan, do, check, and act. The planning phase involves obtaining management approval, understanding the organization and its needs, defining the ISMS scope and objectives. The doing phase includes performing risk assessments, selecting controls, and implementing risk treatment plans. The checking phase consists of monitoring performance, auditing, and collecting feedback. The acting phase is for reviewing performance, deciding on improvements, and planning corrective actions.
Iso27001 Audit Services

The document discusses ISO 27001 internal audit requirements and challenges with conducting internal audits. It proposes two approaches for outsourcing ISO 27001 audits to an external firm: 1) co-sourcing where the firm provides audit resources under the organization's direction, or 2) a managed assurance service where the firm develops and runs the entire audit program. The benefits cited include overcoming resourcing challenges, ensuring objectivity, and focusing internal resources on high risk areas.
Presentation on iso 27001-2013, Internal Auditing and BCM

The document is a presentation summarizing an internship at an IT company working on three projects: 1) Creating a roadmap for transitioning to ISO 27001:2013 which involved gap analysis and updating controls. 2) Mapping the internal auditing process which involves scheduling, preparing, conducting, and reporting on audits. 3) Analyzing a specific business continuity scenario which included identifying critical processes, calculating response times, and planning infrastructure and response to incidents. The internship provided learning around differences in standards, assessing controls, conducting audits, and creating business continuity plans.
Iso 27001 metrics and implementation guide

This document provides implementation tips and potential metrics for ISO/IEC 27001 and 27002. It covers tips and metrics for each control objective in ISO/IEC 27002 sections 4 through 15. The tips are meant to help others implementing the ISO information security standards in their organization. The document is collaboratively created and copyrighted but licensed for sharing and derivative works.
Iso 22301 la training

ISO Lead Auditor Certification Training Course has a five-day intensive course that enables participants to develop the necessary expertise to audit a Business Continuity Management System (BCMS) and to manage a team of auditors by applying widely recognized audit principles, procedures, and techniques.
Cloud Computing | Cloud Security | Cloud Computing Audit Checklist | 499 Chec...

In depth and exhaustive ISO 27001 Checklist covers compliance requirements on Cloud Computing. The Checklist on cloud security Contains downloadable file of 3 Excel Sheets having 499 checklist Questions, complete list of Clauses, and list of 114 Information Security Controls, 35 control objectives, and 14 domains. URL link is mentioned below-
https://www.isocertificationtrainingcourse.org/online-store/ISO-27001-Checklist-ISO-27001-Audit-Checklist-ISO-27001-Compliance-checklist-c28241136
A18 compliance

This presentation explains the control A.18 of ISO 27001 : 2013 which is "Compliance".
Courtesy:
http://www.ifour-consultany.com
http://www.ifourtechnolab.com
ISO 27001 Checklist - ISMS Scope - Clause 4.3 - 38 checklist Questions

In depth and exhaustive ISO 27001 Checklist covers compliance requirements on ISMS Scope. ‘Contains downloadable file of 4 Excel Sheets having 38 checklist Questions, 7 dynamic Analytical Graphs, complete list of Clauses, and list of 114 Information Security Controls, 35 control objectives, and 14 domains. To obtain your copy of the ISO 27001 Checklist, click on the url link below:-
https://www.isocertificationtrainingcourse.org/online-store/ISO-27001-Checklist-ISO-27001-Audit-Checklist-ISO-27001-Compliance-checklist-c28241136
Security and Audit Report Sign-Off—Made Easy

View this slideshow to learn how to get your security and audit report processes in line so that you’re ready when the auditors come calling.
Watch the recorded webinar on HelpSystems.com:
http://www.helpsystems.com/rjs/events/recorded-webinars/security-and-audit-report-approvals
ISO 27001 (v2013) Checklist

The checklist identifies in red documentation and records that we believe are explicitly required in the main body of ISO/IEC 27001
Control Standards for Information Security

ISO 27001 is an international information security standard that provides specifications for implementing an effective Information Security Management System (ISMS) through risk management and compliance with regulations like GDPR. SOC 2 is an assessment for technology companies developed by AICPA to protect customer data stored in the cloud and apply to any company using cloud storage. Both standards aim to implement security controls, policies, and procedures to protect valuable assets, but ISO 27001 provides a more comprehensive framework while SOC 2 focuses on verifying data protection controls. Implementing one or both can strengthen security posture, simplify compliance, and improve customer confidence.
Security

The document outlines security policies for the development and maintenance of an information system. It discusses:
1) Integrating information security into the system development lifecycle to protect test data.
2) Requirements for secure development including security controls in the development environment, software lifecycle, and design phases.
3) Restrictions on changes to software packages, requiring support from vendors and ensuring compatibility.
4) The need for secure system engineering principles, security design in all architecture layers, and regular review of security risks and the design.
A11 part 1

This presentation explains control A.11.1 (Secure areas) of ISO 27001 : 2013.
Courtesy:
http://www.ifour-consultancy.com
http://www.ifourtechnolab.com
STAND OUT: Why You Should Become ISO 27001 Certified

ISO 27001 is an international standard for information security management systems (ISMS). It provides requirements for establishing, implementing, maintaining and continually improving an ISMS. Key benefits of ISO 27001 include reducing information security risks, increasing transparency of security risks, and demonstrating assurance to customers through independent third-party certification. While growing in adoption globally, ISO 27001 certification is still only held by around 3.5% of organizations. It is commonly pursued by service providers and sectors involving data privacy like cloud providers and healthcare. The process of obtaining ISO 27001 involves designing and implementing an ISMS, undergoing two stage external audits, and maintaining conformity over the three year certification period.
Best Practices in Auditing ISO/IEC 27001

Due to the dramatic increase of threats worldwide, there is a need for the companies to find ways how to increase the information security. Therefore, one solution is to implement the ISO/IEC 27001 in order to protect information both internally and externally.
Main points that will be covered are:
• The scope of ISO 27001 & associated other standards references
• Information Security and ISIM Terminologies
• ISIM auditing principles
• Managing audit program & audit activities
Presenter:
Eng. Kefah El-Ghobbas is a specialist in ‘Business Process Excellence' through ‘Business Process Re-engineering' with over 20 years of experience.
Link of the recorded session published on YouTube: https://youtu.be/rTxA8PVULUs
Whitepaper iso 27001_isms | All about ISO 27001

ISO 27001 is an international standard that collects requirements for the creation and development of an information security management system.
By and large, it is a collection of "best practices" that allows you to select security controls in such a way as to ensure the protection of information and provide customers with appropriate guarantees.
Steps to iso 27001 implementation

Here are some small steps to achieve ISO 27001 implementation.
I believe ISO 27001/2 is a key to establish security in the organizations and help the companies to keep the whole ISMS program running aligned with continues improvement.
As ISO 27001 has been identified by ICO and recognized by GCHQ/NCSC in the past as the key standard to support GDPR.
ISO/IEC 27001 as a Starting Point for GRC

Learn more about the importance of ISO 27001 and its role on GRC, what the advantages of starting with ISO 27001 are and the importance of its structure.
Main points covered:
• Definition and goals of GRC (Governance, Risk and Compliance)
• How the structure of ISO/IEC 27001 implements GRC
• Advantages of starting with ISO/IEC 27001
Presenter:
This webinar was presented by Jorge Lozano. He is a senior manager at the Cybersecurity & Privacy practice of PwC Mexico. He has over 17 years of experience in information security and holds the CISSP, CISM, CEH, and ISO27001LI certifications. He is an instructor of PECB for the ISO27001 Introduction, Foundation and Lead Implementer courses.
Link of the recorded session published on YouTube: https://youtu.be/sLfAarQ8cf0
ISO 27001 Checklist - Documented Information - Clause 7.5 - 45 checklist Ques...

In depth and exhaustive ISO 27001 Checklist covers compliance requirements on ISO 27001 Clause 7.5 w.r.t. Documented Information. ‘Contains downloadable file of 4 Excel Sheets having 45 checklist Questions, 7 dynamic Analytical Graphs, complete list of Clauses, list of 114 Information Security Controls, 35 Information Security control objectives, and 14 Information Security domains. To obtain your copy of the ISO 27001 Checklist, click on the url link below:-
https://www.isocertificationtrainingcourse.org/online-store/ISO-27001-Checklist-ISO-27001-Audit-Checklist-ISO-27001-Compliance-checklist-c28241136
Functional safety-overview

Functional Safety is a holistic analysis that evaluates how a product's hardware and software interact and respond to ensure proper performance, well-being, and security. It involves analyzing safety standards, failure modes, and risk levels. Intertek's Functional Safety services support customers through each step of the process from product development to operations. This results in optimized and secure systems that comply with relevant safety standards and specifications.
ISO 27001 control A17 (Continuity on Information Security), and ISO 22301: co...

The webinar covers:
• ISO27001/ISO22301 differences
• ISO27001/ISO22301 relationship
• Conclusions
Presenter:
This webinar was presented by Michèle COPITET. Prior to founding her company; Michèle has been working for 10 years in CAP GEMINI as consultant and project manager and currently is accredited trainer for PECB and for APMG. Her company EGONA-CONSULTING 0(mc@egona-consulting.eu) provides consultancy, assessment and training in IT security management and in IT services quality management in France and abroad. She is certified against ISO22301 LI/LA, ISO27001 LA, ISO27005 RM, CISM, Expert ITILV3, ISO20000, COBIT5, Assessor, Prince2 practitioner.
Link of the recorded session published on YouTube: https://youtu.be/_z_BAchDQxM
Isms awareness presentation

This document provides an introduction to ISO 27001, an internationally recognized standard for information security management. It defines information security as preserving the confidentiality, integrity and availability of information. ISO 27001 describes a structured methodology for establishing an Information Security Management System (ISMS) based on best practices. The standard takes a holistic approach, balancing physical, technical, procedural and personnel security controls. It outlines five mandatory requirements for an ISMS including management responsibility, internal audits, and management review. The standard also describes 11 domains of information security and the documentation required in an ISMS.
ISO 27001:2013 IS audit plan - by software outsourcing company in india

The document outlines an IS audit plan template that includes the audit objective, scope, criteria, methods, team, and schedule. It defines an audit plan as a strategy for the audit that is prepared by the auditor in consultation with team leaders. The plan establishes what is to be accomplished by the audit and includes details like locations, units, and time periods to be examined, as well as references against which conformity will be determined and the types of audit methods to be used.
Lead Auditor Course on ISO 27001:2013 (ISMS) - IRCA

This document provides details about an ISO 27001:2013 Lead Auditor Course offered by myTectra Learning Solutions. The 5-day course covers the standards, principles, and processes for auditing an Information Security Management System and prepares students to conduct audits and become certified auditors. Successful students will receive an IRCA-approved certificate of completion. The course can be taken in an instructor-led classroom or live virtual format.
Saikiran_CV_Operational Risk_updated

This document provides a summary of Saikiran Konchada's qualifications and experience. It outlines his educational background which includes a post graduate degree in information security management and a bachelor's degree in computer science engineering. It also lists his professional certifications in information security, business continuity management, and other IT domains. Currently, Saikiran works as a consultant in operational risk management at Banque Saudi Fransi in Riyadh, where he is responsible for developing and implementing their operational risk processes. He has previous work experience as a security engineer as well.
Practical IT auditing

IT Auditing – Using Controls to Protect Information Assets (straight to the point)
Under the skillful guidance of ALTUM’s best instructors, participants will learn how to plan and perform complex technical audits. Over a three to six month period, a General Controls Review, Network Audit, several Operating System Audits and a review of the Internet should be able to be completed. Participants will also learn how to effectively report issues to management, while providing the IT administrators and technicians with a working document allowing them to correct existing security issues. This is a 3-day hands-on training and all participants are advised to come along with their laptops.
NQA - ISO 27001 Implementation Guide

The document provides an overview and implementation guide for ISO 27001:2013, an internationally recognized standard for information security management systems (ISMS). It discusses key principles like risk-based thinking, process-based audits, and the PDCA (Plan-Do-Check-Act) cycle. The benefits of ISO 27001 certification include commercial advantages, more robust operational security, and peace of mind. The guide then covers each clause of the ISO 27001 standard in detail to help organizations successfully implement an ISMS.
ISO/IEC 27001:2022 (Information Security Management Systems) Awareness Training

ISO/IEC 27001:2022 (Information Security Management Systems) Awareness TrainingOperational Excellence Consulting
[To download this complete presentation, visit:
https://www.oeconsulting.com.sg/training-presentations]
ISO/IEC 27001:2022 is the latest internationally-recognised standard for Information Security Management Systems (ISMS). An ISMS is a systematic approach to managing sensitive company information so that it remains secure. It provides a robust framework to protect information that can be adapted to all types and sizes of organization. Organizations that have significant exposure to information-security related risks are increasingly choosing to implement an ISMS that complies with ISO/IEC 27001.
This ISMS awareness PPT presentation material is designed for organizations who are embarking on ISO/IEC 27001:2022 implementation and need to create awareness of information security among its employees.
LEARNING OBJECTIVES
1. Acquire knowledge on the fundamentals of information security
2. Describe the ISO/IEC 27001:2022 structure
3. Understand the ISO/ IEC 27001:2022 implementation and certification process
4. Gather useful tips on handling an audit session
english_bok_ismp_202306.pptx

The document provides an overview of ISO/IEC 27001 and risk management principles for information security. It discusses key aspects of risk assessment including identifying assets, threats, vulnerabilities, risks and controls. It emphasizes the importance of a risk-based approach and involving stakeholders in the risk assessment process.
More Related Content
What's hot
ISO 27001 Checklist - ISMS Scope - Clause 4.3 - 38 checklist Questions

In depth and exhaustive ISO 27001 Checklist covers compliance requirements on ISMS Scope. ‘Contains downloadable file of 4 Excel Sheets having 38 checklist Questions, 7 dynamic Analytical Graphs, complete list of Clauses, and list of 114 Information Security Controls, 35 control objectives, and 14 domains. To obtain your copy of the ISO 27001 Checklist, click on the url link below:-
https://www.isocertificationtrainingcourse.org/online-store/ISO-27001-Checklist-ISO-27001-Audit-Checklist-ISO-27001-Compliance-checklist-c28241136
Security and Audit Report Sign-Off—Made Easy

View this slideshow to learn how to get your security and audit report processes in line so that you’re ready when the auditors come calling.
Watch the recorded webinar on HelpSystems.com:
http://www.helpsystems.com/rjs/events/recorded-webinars/security-and-audit-report-approvals
ISO 27001 (v2013) Checklist

The checklist identifies in red documentation and records that we believe are explicitly required in the main body of ISO/IEC 27001
Control Standards for Information Security

ISO 27001 is an international information security standard that provides specifications for implementing an effective Information Security Management System (ISMS) through risk management and compliance with regulations like GDPR. SOC 2 is an assessment for technology companies developed by AICPA to protect customer data stored in the cloud and apply to any company using cloud storage. Both standards aim to implement security controls, policies, and procedures to protect valuable assets, but ISO 27001 provides a more comprehensive framework while SOC 2 focuses on verifying data protection controls. Implementing one or both can strengthen security posture, simplify compliance, and improve customer confidence.
Security

The document outlines security policies for the development and maintenance of an information system. It discusses:
1) Integrating information security into the system development lifecycle to protect test data.
2) Requirements for secure development including security controls in the development environment, software lifecycle, and design phases.
3) Restrictions on changes to software packages, requiring support from vendors and ensuring compatibility.
4) The need for secure system engineering principles, security design in all architecture layers, and regular review of security risks and the design.
A11 part 1

This presentation explains control A.11.1 (Secure areas) of ISO 27001 : 2013.
Courtesy:
http://www.ifour-consultancy.com
http://www.ifourtechnolab.com
STAND OUT: Why You Should Become ISO 27001 Certified

ISO 27001 is an international standard for information security management systems (ISMS). It provides requirements for establishing, implementing, maintaining and continually improving an ISMS. Key benefits of ISO 27001 include reducing information security risks, increasing transparency of security risks, and demonstrating assurance to customers through independent third-party certification. While growing in adoption globally, ISO 27001 certification is still only held by around 3.5% of organizations. It is commonly pursued by service providers and sectors involving data privacy like cloud providers and healthcare. The process of obtaining ISO 27001 involves designing and implementing an ISMS, undergoing two stage external audits, and maintaining conformity over the three year certification period.
Best Practices in Auditing ISO/IEC 27001

Due to the dramatic increase of threats worldwide, there is a need for the companies to find ways how to increase the information security. Therefore, one solution is to implement the ISO/IEC 27001 in order to protect information both internally and externally.
Main points that will be covered are:
• The scope of ISO 27001 & associated other standards references
• Information Security and ISIM Terminologies
• ISIM auditing principles
• Managing audit program & audit activities
Presenter:
Eng. Kefah El-Ghobbas is a specialist in ‘Business Process Excellence' through ‘Business Process Re-engineering' with over 20 years of experience.
Link of the recorded session published on YouTube: https://youtu.be/rTxA8PVULUs
Whitepaper iso 27001_isms | All about ISO 27001

ISO 27001 is an international standard that collects requirements for the creation and development of an information security management system.
By and large, it is a collection of "best practices" that allows you to select security controls in such a way as to ensure the protection of information and provide customers with appropriate guarantees.
Steps to iso 27001 implementation

Here are some small steps to achieve ISO 27001 implementation.
I believe ISO 27001/2 is a key to establish security in the organizations and help the companies to keep the whole ISMS program running aligned with continues improvement.
As ISO 27001 has been identified by ICO and recognized by GCHQ/NCSC in the past as the key standard to support GDPR.
ISO/IEC 27001 as a Starting Point for GRC

Learn more about the importance of ISO 27001 and its role on GRC, what the advantages of starting with ISO 27001 are and the importance of its structure.
Main points covered:
• Definition and goals of GRC (Governance, Risk and Compliance)
• How the structure of ISO/IEC 27001 implements GRC
• Advantages of starting with ISO/IEC 27001
Presenter:
This webinar was presented by Jorge Lozano. He is a senior manager at the Cybersecurity & Privacy practice of PwC Mexico. He has over 17 years of experience in information security and holds the CISSP, CISM, CEH, and ISO27001LI certifications. He is an instructor of PECB for the ISO27001 Introduction, Foundation and Lead Implementer courses.
Link of the recorded session published on YouTube: https://youtu.be/sLfAarQ8cf0
ISO 27001 Checklist - Documented Information - Clause 7.5 - 45 checklist Ques...

In depth and exhaustive ISO 27001 Checklist covers compliance requirements on ISO 27001 Clause 7.5 w.r.t. Documented Information. ‘Contains downloadable file of 4 Excel Sheets having 45 checklist Questions, 7 dynamic Analytical Graphs, complete list of Clauses, list of 114 Information Security Controls, 35 Information Security control objectives, and 14 Information Security domains. To obtain your copy of the ISO 27001 Checklist, click on the url link below:-
https://www.isocertificationtrainingcourse.org/online-store/ISO-27001-Checklist-ISO-27001-Audit-Checklist-ISO-27001-Compliance-checklist-c28241136
Functional safety-overview

Functional Safety is a holistic analysis that evaluates how a product's hardware and software interact and respond to ensure proper performance, well-being, and security. It involves analyzing safety standards, failure modes, and risk levels. Intertek's Functional Safety services support customers through each step of the process from product development to operations. This results in optimized and secure systems that comply with relevant safety standards and specifications.
ISO 27001 control A17 (Continuity on Information Security), and ISO 22301: co...

The webinar covers:
• ISO27001/ISO22301 differences
• ISO27001/ISO22301 relationship
• Conclusions
Presenter:
This webinar was presented by Michèle COPITET. Prior to founding her company; Michèle has been working for 10 years in CAP GEMINI as consultant and project manager and currently is accredited trainer for PECB and for APMG. Her company EGONA-CONSULTING 0(mc@egona-consulting.eu) provides consultancy, assessment and training in IT security management and in IT services quality management in France and abroad. She is certified against ISO22301 LI/LA, ISO27001 LA, ISO27005 RM, CISM, Expert ITILV3, ISO20000, COBIT5, Assessor, Prince2 practitioner.
Link of the recorded session published on YouTube: https://youtu.be/_z_BAchDQxM
Isms awareness presentation

This document provides an introduction to ISO 27001, an internationally recognized standard for information security management. It defines information security as preserving the confidentiality, integrity and availability of information. ISO 27001 describes a structured methodology for establishing an Information Security Management System (ISMS) based on best practices. The standard takes a holistic approach, balancing physical, technical, procedural and personnel security controls. It outlines five mandatory requirements for an ISMS including management responsibility, internal audits, and management review. The standard also describes 11 domains of information security and the documentation required in an ISMS.
ISO 27001:2013 IS audit plan - by software outsourcing company in india

The document outlines an IS audit plan template that includes the audit objective, scope, criteria, methods, team, and schedule. It defines an audit plan as a strategy for the audit that is prepared by the auditor in consultation with team leaders. The plan establishes what is to be accomplished by the audit and includes details like locations, units, and time periods to be examined, as well as references against which conformity will be determined and the types of audit methods to be used.
Lead Auditor Course on ISO 27001:2013 (ISMS) - IRCA

This document provides details about an ISO 27001:2013 Lead Auditor Course offered by myTectra Learning Solutions. The 5-day course covers the standards, principles, and processes for auditing an Information Security Management System and prepares students to conduct audits and become certified auditors. Successful students will receive an IRCA-approved certificate of completion. The course can be taken in an instructor-led classroom or live virtual format.
Saikiran_CV_Operational Risk_updated

This document provides a summary of Saikiran Konchada's qualifications and experience. It outlines his educational background which includes a post graduate degree in information security management and a bachelor's degree in computer science engineering. It also lists his professional certifications in information security, business continuity management, and other IT domains. Currently, Saikiran works as a consultant in operational risk management at Banque Saudi Fransi in Riyadh, where he is responsible for developing and implementing their operational risk processes. He has previous work experience as a security engineer as well.
Practical IT auditing

IT Auditing – Using Controls to Protect Information Assets (straight to the point)
Under the skillful guidance of ALTUM’s best instructors, participants will learn how to plan and perform complex technical audits. Over a three to six month period, a General Controls Review, Network Audit, several Operating System Audits and a review of the Internet should be able to be completed. Participants will also learn how to effectively report issues to management, while providing the IT administrators and technicians with a working document allowing them to correct existing security issues. This is a 3-day hands-on training and all participants are advised to come along with their laptops.
NQA - ISO 27001 Implementation Guide

The document provides an overview and implementation guide for ISO 27001:2013, an internationally recognized standard for information security management systems (ISMS). It discusses key principles like risk-based thinking, process-based audits, and the PDCA (Plan-Do-Check-Act) cycle. The benefits of ISO 27001 certification include commercial advantages, more robust operational security, and peace of mind. The guide then covers each clause of the ISO 27001 standard in detail to help organizations successfully implement an ISMS.
What's hot (20)
ISO 27001 Checklist - ISMS Scope - Clause 4.3 - 38 checklist Questions

ISO 27001 Checklist - ISMS Scope - Clause 4.3 - 38 checklist Questions
STAND OUT: Why You Should Become ISO 27001 Certified

STAND OUT: Why You Should Become ISO 27001 Certified
ISO 27001 Checklist - Documented Information - Clause 7.5 - 45 checklist Ques...

ISO 27001 Checklist - Documented Information - Clause 7.5 - 45 checklist Ques...
ISO 27001 control A17 (Continuity on Information Security), and ISO 22301: co...

ISO 27001 control A17 (Continuity on Information Security), and ISO 22301: co...
ISO 27001:2013 IS audit plan - by software outsourcing company in india

ISO 27001:2013 IS audit plan - by software outsourcing company in india
Lead Auditor Course on ISO 27001:2013 (ISMS) - IRCA

Lead Auditor Course on ISO 27001:2013 (ISMS) - IRCA
Similar to CQI-IRCA 27001:2013 Lead Auditor Course
ISO/IEC 27001:2022 (Information Security Management Systems) Awareness Training

ISO/IEC 27001:2022 (Information Security Management Systems) Awareness TrainingOperational Excellence Consulting
[To download this complete presentation, visit:
https://www.oeconsulting.com.sg/training-presentations]
ISO/IEC 27001:2022 is the latest internationally-recognised standard for Information Security Management Systems (ISMS). An ISMS is a systematic approach to managing sensitive company information so that it remains secure. It provides a robust framework to protect information that can be adapted to all types and sizes of organization. Organizations that have significant exposure to information-security related risks are increasingly choosing to implement an ISMS that complies with ISO/IEC 27001.
This ISMS awareness PPT presentation material is designed for organizations who are embarking on ISO/IEC 27001:2022 implementation and need to create awareness of information security among its employees.
LEARNING OBJECTIVES
1. Acquire knowledge on the fundamentals of information security
2. Describe the ISO/IEC 27001:2022 structure
3. Understand the ISO/ IEC 27001:2022 implementation and certification process
4. Gather useful tips on handling an audit session
english_bok_ismp_202306.pptx

The document provides an overview of ISO/IEC 27001 and risk management principles for information security. It discusses key aspects of risk assessment including identifying assets, threats, vulnerabilities, risks and controls. It emphasizes the importance of a risk-based approach and involving stakeholders in the risk assessment process.
ISO/IEC 27001:2013 An Overview 

In this article I will provide an Overview of A new Information Security Management System
Standard ISO/IEC 27001:2013 , The new standard just Published from a few Days Earlier .
ISO/IEC 27001:2013 Provides requirements for Establishing, Implementing, Maintaining
and Continually Improving an Information Security Management System.
ISO/IEC 27001:2013 gives Organization a Perfect Information Security management framework for implementing
and maintaining security.
In this Article, I tried to shed some light on new standard and its Mandatory Requirements, Optional Requirements ,
Structure , Benefits , Certification Process and Estimated time for Implementation and Certification.
Iso 27001 awareness

The security of information systems and business-critical information needs constant managing to ensure your operational continuity and data protection. ISO 27001 Information Security Management Systems certification allows you to stand out from the competition through strong information security measurement.
Planning for-and implementing ISO 27001

This document discusses planning and implementing the ISO 27001 information security standard. It provides guidance on costs, project length, and implementation steps. Key points include:
- Implementation can take 4-9 months depending on factors like organization size and existing security practices. It follows the PDCA (plan-do-check-act) cycle.
- Costs include internal resources, external consultants, certification fees, and addressing security gaps. Existing frameworks can reduce costs by providing existing security policies and controls.
- Implementation involves defining the scope, assessing risks, managing risks, selecting controls, and preparing for audits to achieve certification. Careful planning is needed to manage costs and implementation.
Qsys Profile

A quality consultant, just a call away 9810059019
we help you to attain world class certification like
-----------------------------------------
ISO9001:2008- Quality Management System
ISO/TS 16949:2009- QMS for automotive
ISO 14001:2004- Environmental Management System
ISO 27001: 2005 - Information Security
OHSAS 18001:2007- Occupational Health and Safety
SA8000- Social Accountability
ISO 10001- Customer satisfaction Measurement
CMMI for software and Services
--------------------------------------------------
Export management, advisory, coaching, export marketing plan, export audit, international trade fair preparation and participation
---------------------------------------------------
We provide training on -------------------
--------------------------------------------------
Internal Audutors for Quality, EMS, OHSAS
Problem solving techniques
Statistical Process Control
Lean Manufacturing
5S, KANBAN, JIT, TPM, Total quality Management
Customer Satisfaction Measurement
Productvity Improvement
Cost of Quality
Client: Government, Public and Private Sectors, Institutes
SpecialtiesISO System Development and Certification, Coaching, Counselling,Support and Certifications. Export Marketing, Intercultural Communication, Institutional Capacity Building, Trade Promotion to European Union, Sustainable Development, Process Improvement and Chane Management
Resume_IshitaKundu_CISA

This document provides a summary of Ishita Kundu's professional experience and qualifications. She has over 5 years of experience in information security, risk and compliance domains including implementation of ISO 27001 and SSAE 16 standards. She has conducted vulnerability assessments, penetration testing, and internal audits for clients in various industries. She is certified in CISA, ISO 27001 Lead Auditor, CEH, and ITIL and is currently preparing for CISSP. She has received recognition awards for her work at Accenture from 2011 to 2015.
ISO 27004- Information Security Metrics Implementation

ISO 27004 provides guidance and describes a set of best practices for measuring the result of ISMS in an organization. The standard specifies how to set up a measurement program, what parameters to measure, when to measure, how to measure and helps organizations to decide on how to set performance targets and success criteria.
ISO 27001 2002 Update Webinar.pdf

The document summarizes updates to ISO 27001:2022. Key points include:
- The structure and grouping of controls in ISO 27002 have been updated, with controls now organized under four main domains and reduced in number from 114 to 93.
- New controls have been introduced related to threat intelligence, information security for cloud services, and ICT readiness for business continuity.
- The mandatory clauses of ISO 27001 remain unchanged, while some controls from ISO 27002 have been merged or reorganized under the new domain structure.
Training brochure la isms

Internationally recognized ISO 27001 is an
excellent framework which helps organizations
manage and protect their information assets
so that they remain safe and secure.
Implementing of a Cyber Security Program Framework from ISO 27032 to ISO 55001

This webinar gives an idea of what is the relation of ISO 27032 with ISO 55001, and how these two standards cover one another. Get more information on Cybersecurity as the importance is given more to the security industry nowadays.
Main points covered:
• Protection assets in Cyberspace
• Covering ISO 27032 in ISO 55001 and ISO 55001 in ISO 27032
• Sample of Cybersecurity Risks in Assets
• Highlights of the Implementation of the Cyber Security program Framework
Presenter:
This webinar was presented by PECB Partner and Trainer Mr. Claude Essomba, who is a Managing Director at GETSEC SARL, and has more than 9 years of experience in IT and Information Security.
Link of the recorded session published on YouTube: https://youtu.be/_280jG77iKY
Implementing ISO 27001: A Step-by-Step Guide

ISO 27001 is an international standard for managing information security. It sets out the criteria for establishing, implementing, maintaining, and continuously improving an Information Security Management System (ISMS). This standard ensures that companies protect their data systematically and effectively.
Information Systems Audit-Related Designations

In this slidecast, Michael Lin provides an overview on the role of information systems (IS) audits, available IS audit-related designations, and the benefits of attaining or hiring individuals with these designations. He also attempts to provide some guidelines on how an IS audit professional should pursue such designations.
Information Security Management System with ISO/IEC 27000:2018

The document provides an agenda for a workshop on ISO/IEC 27000:2018 Information Security Management Systems. The agenda covers understanding ISMS, an overview of ISO/IEC 27000:2018, exploring the requirements, navigating the controls, planning implementation, deploying ISMS, monitoring and evaluation, and continual improvement. The workshop will help participants understand how to establish, implement, and improve an organization's information security using the ISO standard.
ISO/IEC 27001 and ISO/IEC 27035: Building a Resilient Cybersecurity Strategy ...

As we approach the new year, the importance of a robust cybersecurity strategy cannot be overstated. Learning on the effective measures to be taken and tools needed to navigate the evolving cybersecurity landscape successfully is essential.
Amongst others, the webinar covers:
• ISO/IEC 27001 and ISO/IEC 27035 and their key components
• Key Components of a Resilient Cybersecurity Strategy
• Best practices for building a resilient cybersecurity strategy in 2024
Presenters:
Rinske Geerlings
Rinske is an internationally known consultant, speaker and certified Business Continuity, Information Security & Risk Management trainer.
She was awarded Alumnus of the Year 2012 of Delft University, Australian Business Woman of the Year 2010-13 by BPW, Risk Consultant of the Year 2017 (RMIA/Australasia) and Outstanding Security Consultant 2019 Finalist (OSPAs)
Rinske has consulted to the Department of Prime Minister & Cabinet, 15 Central Banks, APEC, BBC, Shell, Fuji Xerox, NIB Health Funds, ASIC, Departments of Defense, Immigration, Health, Industry, Education, Foreign Affairs and 100s of other public and private organizations across 5 continents.
She has been changing the way organizations ‘plan for the unexpected’. Her facilitation skills enable organizations to achieve their own results and simplify their processes. She applies a fresh, energetic, fun, practical, easy-to-apply, innovative approach to BCM, Security, and Risk.
Her 'alter ego' includes being a lead singer in SophieG Music and contributing to the global charity playing for Change, which provides music education to children in disadvantaged regions.
Loris Mansiamina
A Senior GRC Professional consultant for Small, Medium and large companies. Over 10 years, Loris has been assisting clients in both public and private sectors about various matters relating to Gouvernance, Risk Management and Compliance (GRC), Digital transformation, cyber security program management, ISO 27k & ISO 20k implementation, COBIT & ITIL implementation, etc.
Date: December 19, 2023
Tags: ISO, ISO/IEC 27001, ISO/IEC 27035, Cybersecurity, Information Security
-------------------------------------------------------------------------------
Find out more about ISO training and certification services
Training: https://pecb.com/en/education-and-certification-for-individuals/iso-iec-27001
ISO/IEC 27035 Information Security Incident Management - EN | PECB
Webinars: https://pecb.com/webinars
Article: https://pecb.com/article
Whitepaper: https://pecb.com/whitepaper
-------------------------------------------------------------------------------
For more information about PECB:
Website: https://pecb.com/
LinkedIn: https://www.linkedin.com/company/pecb/
Facebook: https://www.facebook.com/PECBInternational/
Slideshare: http://www.slideshare.net/PECBCERTIFICATION
YouTube video: https://youtu.be/yT8gxRZD_4c
Integrating sms and isms

The document discusses implementing an integrated IT service management system (SMS) and information security management system (ISMS) based on ISO/IEC 20000-1 and ISO/IEC 27000 standards. It describes how ISO/IEC 27001 fits into the information security requirements of ISO/IEC 20000. There are key benefits to an integrated system, including providing credible and secure services, lower implementation costs, reduced timelines by developing common processes together, and eliminating duplication between the standards. An integrated system also promotes understanding between service and security personnel.
ISO27k ISMS implementation and certification process overview v2.pptx

This document provides an overview of the ISO27001 Information Security Management System (ISMS) implementation and certification process. It describes establishing the ISMS scope, conducting a risk assessment, developing necessary documentation like the Statement of Applicability and Risk Treatment Plan, implementing controls, conducting internal audits and management reviews, completing a pre-certification assessment, and undergoing a certification audit to obtain ISO27001 certification. Certification verifies the organization has properly implemented an ISMS to systematically manage its information security risks.
Cyber-Security Certifications

This document provides information on various cyber security certifications, including ISO 27001 Lead Auditor, EC Council CEH v8, CCSK, CHFI, RHCSS, CCIE Security, CRISC, ISMS LA, COBIT, BS25999, ISO 27001, BS 7799, ISO 20000, CeISB, JNCP, CS-MARS, Check Point Certified Security Administrator, CSSLP, ITIL, CASP, QSA, PA-QSA, ASV, Trend Micro Certified Professional, IT Management, GIAC Penetration Tester (GPEN), and Offensive Security Certified Professional. Each certification is briefly described in one or two
Gs Us Roadmap For A World Class Information Security Management System– Isoie...

GSU is developing an Information Security Management System (ISMS) based on the ISO/IEC 27001 standard to protect the university's reputation, ensure security and availability of information, and reduce risks. The roadmap involves strategic planning, continuous reviews and improvements, and incremental implementation of controls. It will align information security with business goals and provide comprehensive, auditable best practices for managing risks through plans, implementation, monitoring, and improvements.
A Comprehensive Guide To Information Security Excellence ISO 27001 Certificat...

ISO 27001 provides a comprehensive set of guidelines for organizations to implement, maintain, and continually improve their ISMS. The standard outlines a systematic approach to identifying, analysing, and managing information security risks, ensuring that appropriate controls are in place to protect the confidentiality, integrity, and availability of information assets.
Similar to CQI-IRCA 27001:2013 Lead Auditor Course (20)
ISO/IEC 27001:2022 (Information Security Management Systems) Awareness Training

ISO/IEC 27001:2022 (Information Security Management Systems) Awareness Training
ISO 27004- Information Security Metrics Implementation

ISO 27004- Information Security Metrics Implementation
Implementing of a Cyber Security Program Framework from ISO 27032 to ISO 55001

Implementing of a Cyber Security Program Framework from ISO 27032 to ISO 55001
Information Security Management System with ISO/IEC 27000:2018

Information Security Management System with ISO/IEC 27000:2018
ISO/IEC 27001 and ISO/IEC 27035: Building a Resilient Cybersecurity Strategy ...

ISO/IEC 27001 and ISO/IEC 27035: Building a Resilient Cybersecurity Strategy ...
ISO27k ISMS implementation and certification process overview v2.pptx

ISO27k ISMS implementation and certification process overview v2.pptx
Gs Us Roadmap For A World Class Information Security Management System– Isoie...

Gs Us Roadmap For A World Class Information Security Management System– Isoie...
A Comprehensive Guide To Information Security Excellence ISO 27001 Certificat...

A Comprehensive Guide To Information Security Excellence ISO 27001 Certificat...
Recently uploaded
The Six Working Genius Short Explanation

Working Genius is based on premise that in the task continuum each of us have pain point.
The Secret Warrior - Help Share a Parent or Loved Ones’ Cancer Diagnosis with...

The Secret Warrior - Help Share a Parent or Loved Ones’ Cancer Diagnosis with...CANSA The Cancer Association of South Africa
You may be stressed about revealing your cancer diagnosis to your child or children.
Children love stories and these often provide parents with a means of broaching tricky subjects and so the ‘The Secret Warrior’ book was especially written for CANSA TLC, by creative writer and social worker, Sally Ann Carter.
Find out more:
https://cansa.org.za/resources-to-help-share-a-parent-or-loved-ones-cancer-diagnosis-with-a-child/7 Habits of Highly Effective People.pptx

Covey says most people look for quick fixes. They see a big success and want to know how he did it, believing (and hoping) they can do the same following a quick bullet list.
But real change, the author says, comes not from the outside in, but from the inside out. And the most fundamental way of changing yourself is through a paradigm shift.
That paradigm shift is a new way of looking at the world. The 7 Habits of Highly Effective People presents an approach to effectiveness based on character and principles.
The first three habits indeed deal with yourself because it all starts with you. The first three habits move you from dependence from the world to the independence of making your own world.
Habits 4, 5 and 6 are about people and relationships. The will move you from independence to interdependence. Such, cooperating to achieve more than you could have by yourself.
The last habit, habit number 7, focuses on continuous growth and improvement.
ProSocial Behaviour - Applied Social Psychology - Psychology SuperNotes

A proprietary approach developed by bringing together the best of learning theories from Psychology, design principles from the world of visualization, and pedagogical methods from over a decade of training experience, that enables you to: Learn better, faster!
Assignment 1 (Introductions to Microsoft Power point 2019) kiran.pptx

its for fresers to microsoft joiner
Understanding of Self - Applied Social Psychology - Psychology SuperNotes

A proprietary approach developed by bringing together the best of learning theories from Psychology, design principles from the world of visualization, and pedagogical methods from over a decade of training experience, that enables you to: Learn better, faster!
Aggression - Applied Social Psychology - Psychology SuperNotes

A proprietary approach developed by bringing together the best of learning theories from Psychology, design principles from the world of visualization, and pedagogical methods from over a decade of training experience, that enables you to: Learn better, faster!
Recently uploaded (9)
The Secret Warrior - Help Share a Parent or Loved Ones’ Cancer Diagnosis with...

The Secret Warrior - Help Share a Parent or Loved Ones’ Cancer Diagnosis with...
1-CIE-IGCSE-Additional-Mathematics-Topical-Past-Paper-Functions.pdf

1-CIE-IGCSE-Additional-Mathematics-Topical-Past-Paper-Functions.pdf
ProSocial Behaviour - Applied Social Psychology - Psychology SuperNotes

ProSocial Behaviour - Applied Social Psychology - Psychology SuperNotes
Assignment 1 (Introductions to Microsoft Power point 2019) kiran.pptx

Assignment 1 (Introductions to Microsoft Power point 2019) kiran.pptx
Understanding of Self - Applied Social Psychology - Psychology SuperNotes

Understanding of Self - Applied Social Psychology - Psychology SuperNotes
Aggression - Applied Social Psychology - Psychology SuperNotes

Aggression - Applied Social Psychology - Psychology SuperNotes
CQI-IRCA 27001:2013 Lead Auditor Course
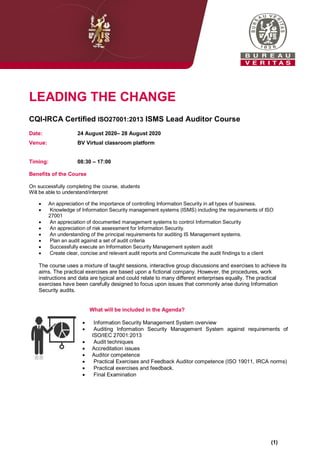
- 1. LEADING THE CHANGE CQI-IRCA Certified ISO27001:2013 ISMS Lead Auditor Course Date: 24 August 2020– 28 August 2020 Venue: BV Virtual classroom platform Timing: 08:30 – 17:00 Benefits of the Course On successfully completing the course, students Will be able to understand/interpret An appreciation of the importance of controlling Information Security in all types of business. Knowledge of Information Security management systems (ISMS) including the requirements of ISO 27001 An appreciation of documented management systems to control Information Security An appreciation of risk assessment for Information Security. An understanding of the principal requirements for auditing IS Management systems. Plan an audit against a set of audit criteria Successfully execute an Information Security Management system audit Create clear, concise and relevant audit reports and Communicate the audit findings to a client The course uses a mixture of taught sessions, interactive group discussions and exercises to achieve its aims. The practical exercises are based upon a fictional company. However, the procedures, work instructions and data are typical and could relate to many different enterprises equally. The practical exercises have been carefully designed to focus upon issues that commonly arise during Information Security audits. What will be included in the Agenda? Information Security Management System overview Auditing Information Security Management System against requirements of ISO/IEC 27001:2013 Audit techniques Accreditation issues Auditor competence Practical Exercises and Feedback Auditor competence (ISO 19011, IRCA norms) Practical exercises and feedback. Final Examination (1)
- 2. Prerequisites: Delegates are expected to have prior knowledge of the following: Management systems: Understand the Plan-Do-Check-Act (PDCA) cycle Information Security Management: Knowledge of the following information security management principles and concepts: awareness of the need for information security; the assignment of responsibility for information security; incorporating management commitment and the interests of stakeholders; enhancing societal values; using the results of risk assessments to determine appropriate controls to reach acceptable levels of risk; incorporating security as an essential element of information networks and systems; the active prevention and detection of information security incidents; ensuring a comprehensive approach to information security management; Continual reassessment of information security and making of modifications as appropriate. ISO/IEC 27001 Knowledge of the requirements of ISO/IEC 27001 (with ISO/IEC 27002) and the commonly used information security management terms and definitions, as given in ISO/IEC 27000, which may be gained by completing an IRCA certified ISMS. How to register: Kindly send confirmation email to desmond.muchetu@bureauveritas.com OR Telephone +27 71 862 2959 Desmond Muchetu (2)
