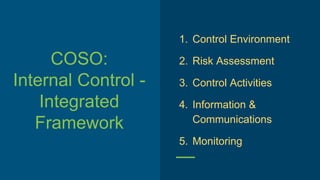
COSO: Internal Control Integrated Framework
- 1. COSO: Internal Control - Integrated Framework 1. Control Environment 2. Risk Assessment 3. Control Activities 4. Information & Communications 5. Monitoring
- 2. Red Flags
- 3. Six Categories of Red Flags Auditors Look For: 1. Unexplained accounting anomalies 2. Exploited internal controls weaknesses 3. Identified analytical anomalies 4. Observed extravagant lifestyle 5. Observed unusual behaviors 6. Anomalies communicated via tips and complaints.
- 4. Withholding information Unexpected fee arrangements Unauthorized Vendors Business w Personal Friends Missing Documentation Unusual requests/ instructions Illogical business case Parallel Systems Unwillingness to relinquish control
- 5. Six Categories of Red Flags Auditors Look For: 1. Unexplained accounting anomalies 2. Exploited internal controls weaknesses 3. Identified analytical anomalies 4. Observed extravagant lifestyle 5. Observed unusual behaviors 6. Anomalies communicated via tips and complaints.
Editor's Notes
- The control environment sets the tone of an organization, influencing the control consciousness of its people. It is the foundation for all other components of internal control, providing discipline and structure. Control environment factors include the integrity, ethical values and competence of the entity's people; management's philosophy and operating style; the way management assigns authority and responsibility, and organizes and develops its people; and the attention and direction provided by the board of directors. How did relationship between Niakan and Thompson affect control environment? Buying from off-list: Werle assumed this was normal Every entity faces a variety of risks from external and internal sources that must be assessed. A precondition to risk assessment is establishment of objectives, linked at different levels and internally consistent. Risk assessment is the identification and analysis of relevant risks to achievement of the objectives, forming a basis for determining how the risks should be managed. Because economic, industry, regulatory and operating conditions will continue to change, mechanisms are needed to identify and deal with the special risks associated with change. Niakan overrode internal controls, Werle discovered it, should have been known by Niakan’s supervisors Control activities are the policies and procedures that help ensure management directives are carried out. They help ensure that necessary actions are taken to address risks to achievement of the entity's objectives. Control activities occur throughout the organization, at all levels and in all functions. They include a range of activities as diverse as approvals, authorizations, verifications, reconciliations, reviews of operating performance, security of assets and segregation of duties. Werle didn’t authorize PGT to return any equipment. Checked Inventory Tracking System, letters database, Infolease system Controls relating to shipping. Tantara had multiple invoices for Venture, only Niakan knew that? Niakan turned in shipping receipts to accounts payable. Why did they pay it? Also relates to communication. Pertinent information must be identified, captured and communicated in a form and timeframe that enable people to carry out their responsibilities. Information systems produce reports, containing operational, financial and compliance-related information, that make it possible to run and control the business. They deal not only with internally generated data, but also information about external events, activities and conditions necessary to informed business decision-making and external reporting. Effective communication also must occur in a broader sense, flowing down, across and up the organization. All personnel must receive a clear message from top management that control responsibilities must be taken seriously. They must understand their own role in the internal control system, as well as how individual activities relate to the work of others. They must have a means of communicating significant information upstream. There also needs to be effective communication with external parties, such as customers, suppliers, regulators and shareholders. After red flag: “I will discuss this with Niakan when he gets back” Shipping should have communicated about where computers were being shipped “Notes like this would cause those working on this account to refer all questions directly to him” Internal control systems need to be monitored--a process that assesses the quality of the system's performance over time. This is accomplished through ongoing monitoring activities, separate evaluations or a combination of the two. Ongoing monitoring occurs in the course of operations. It includes regular management and supervisory activities, and other actions personnel take in performing their duties. The scope and frequency of separate evaluations will depend primarily on an assessment of risks and the effectiveness of ongoing monitoring procedures. Internal control deficiencies should be reported upstream, with serious matters reported to top management and the board. How often is Thompson doing internal audits?
- For each red flag give me an example or scenario from the case. How do these red flags compare to the list we saw before? Let’s look again. Which are covered? Admission of keeping some accounts hidden to keep boss off back at CIT: biggest red flag: PGT called to say it had returned equip as instructed een tho W had not authorized such return and there was no record in the inventory tracking system or other systems of anyone authorizing this. Then she found that the return authorization which had been mysterious faxed had a warehouse name and addy that was not a CIT approved remarketer. Also, N’s friend’s name. CIT equip going to a fitness company: no logical business case. Then another similar case with a different friend. His asking them to notify him when large volume was moving. Wouldn’t let her do it.
- Revisiting this again
