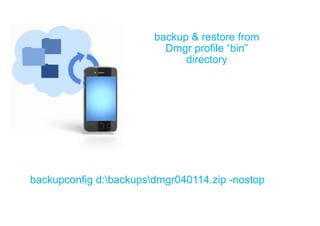
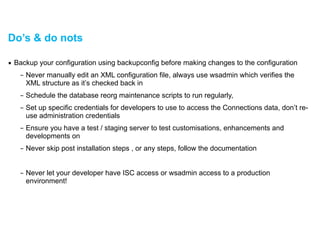
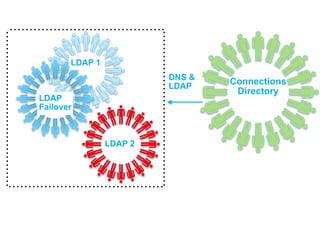
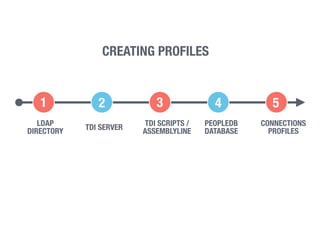
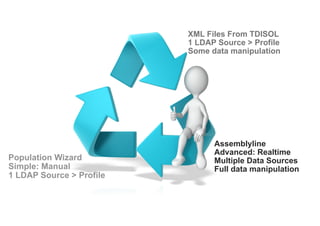
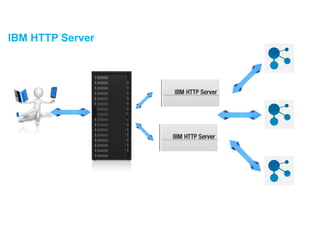
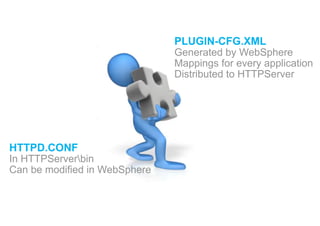
This document provides information about becoming an IBM Connections administrator. It discusses the wide range of skills and technologies required, including CSS, Java, LDAP, databases, IBM HTTP Server configuration, and WebSphere administration. It emphasizes planning resources, verifying configurations, backing up data, monitoring logs, and following documentation to install, customize, and maintain Connections successfully.











![WSAdmin – sending commands
▪ Start in the BIN directory of the deployment manager
– C:IBMWebSphereAppServerprofilesDmgr01bin
!
▪ Call wsadmin by typing
wsadmin(.sh) –lang jython –username [name] –password [password]
▪ Choose which application you want to work with
execfile(“profilesAdmin.py”)
▪ Any changes you make here will be pushed out to all the nodes
– Wsadmin commands are case sensitive regardless of your platform](https://image.slidesharecdn.com/connections-140526144640-phpapp02/85/Becoming-A-Connections-Administrator-38-320.jpg)