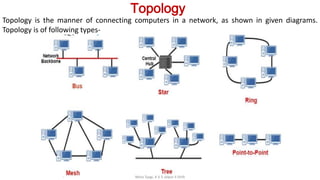
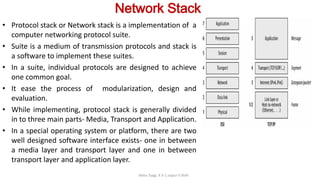
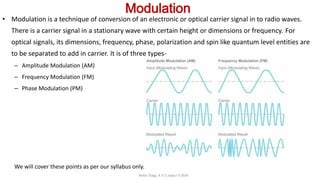
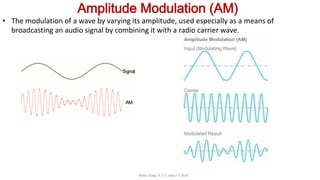
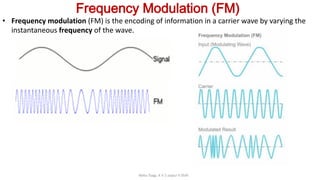
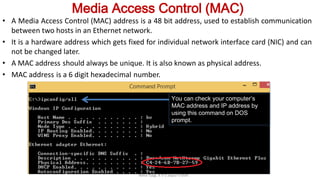
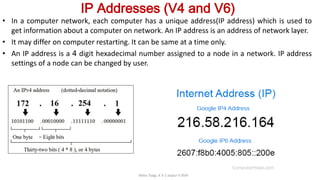
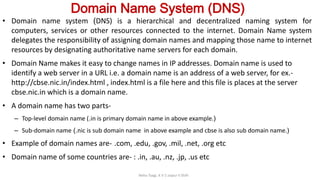
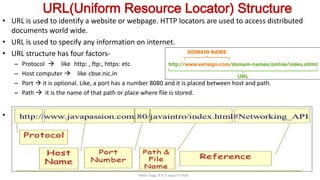
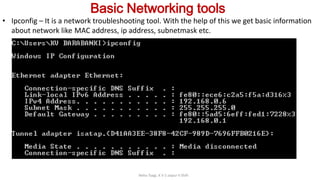
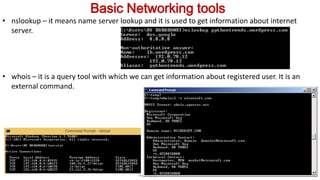
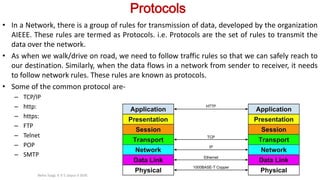
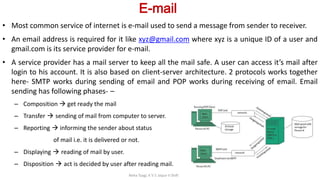
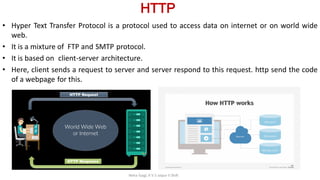
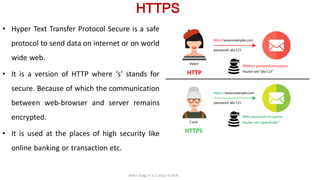
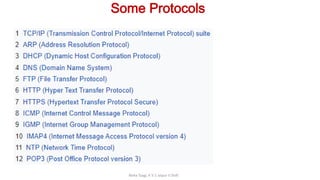
The document provides an overview of key topics in computer networks that will be discussed in Part 2, including topology, network stack, modulation, collision, error checking and correction codes, MAC, routing, DNS, URL structure, basic networking tools, protocols, HTTP, email, HTTPS, and some common network applications. It also provides brief definitions and explanations of several of these topics, such as defining topology as the manner of connecting computers in a network, describing network stack implementation of networking protocol suites, and explaining modulation as the conversion of carrier signals.