Embed presentation
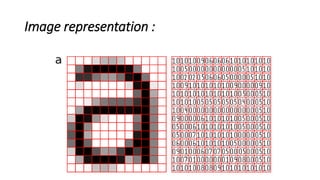
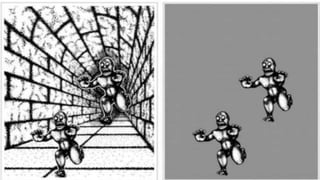
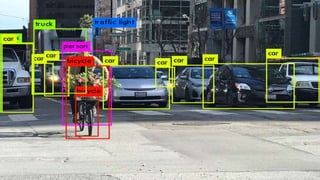
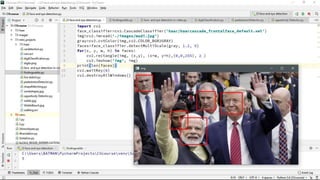

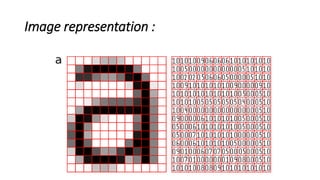
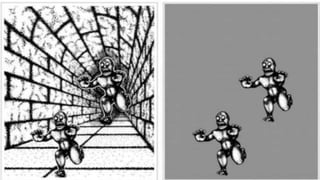
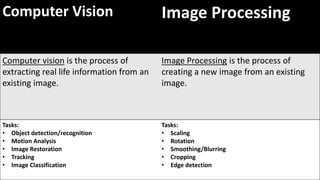
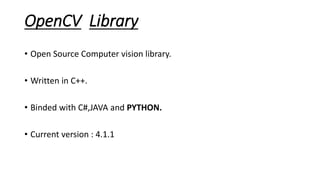
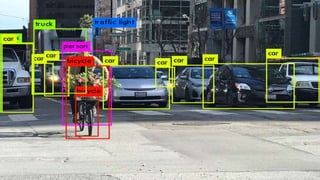
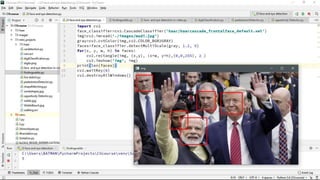
Computer vision is a field of artificial intelligence that uses digital image processing techniques to analyze visual content and understand scenes. The goal is to extract meaningful information from digital images and emulate some of the capabilities of human vision such as object recognition. Computer vision has applications in security, human behavior analysis, optical character recognition, special effects in movies, face filters in social media, autonomous vehicles, and scene formation. OpenCV is a popular open source library for computer vision that is written in C++ but can be used with other languages like C#, Java, and Python.