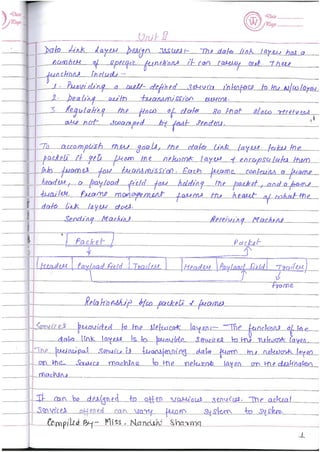
Computer Network Notes (Handwritten) UNIT 2
•
25 likes•7,463 views
Data link layer: flow control, error control, line discipline, stop and wait, sliding window protocol, stop and wait arq, sliding window arq, BSC, HDLC, bit stuffing, elemenary data link protocol etc
Report
Share
Report
Share
Download to read offline
Recommended
CLE Unit - 1 - Introduction to Cyber Law

Evolution of computer Technology, emergence of cyber space. Cyber Jurisprudence, Jurisprudence and law, Doctrinal approach, Consensual approach, Real Approach, Cyber Ethics, Cyber Jurisdiction, Hierarchy of courts, Civil and criminal jurisdictions, Cyberspace-Web space, Web hosting and web Development agreement, Legal and Technological Significance of domain Names, Internet as a tool for global access.
VTU Network & cyber security (1-5 Module) Full notes

Network & cyber security
Transport Level Security: Web Security Considerations, Secure Sockets Layer, Transport
Layer Security, HTTPS, Secure Shell (SSH).
E-mail Security: Pretty Good Privacy, S/MIME, Domain keys identified mail.
IP Security: IP Security Overview, IP Security Policy, Encapsulation Security Payload (ESP),Combining security Associations Internet Key Exchange. Cryptographic Suites
Cyber network security concepts: Security Architecture, antipattern: signature based
malware detection versus polymorphic threads, document driven certification and
accreditation, policy driven security certifications. Refactored solution: reputational,
behavioural and entropy based malware detection.
The problems: cyber antipatterns concept, forces in cyber antipatterns, cyber anti pattern
templates, cyber security antipattern catalog.
Cyber network security concepts contd. :
Enterprise security using Zachman framework
Zachman framework for enterprise architecture, primitive models versus composite
models, architectural problem solving patterns, enterprise workshop, matrix mining, mini
patterns for problem solving meetings.
Case study: cyber security hands on – managing administrations and root accounts,
installing hardware, reimaging OS, installing system protection/ antimalware, configuring
firewalls
CLE Unit - 3 - Cyber law and Related Legislation

Patent Law, Trademark Law, Copyright, Software – Copyright or Patented, Domain Names and Copyright disputes, Electronic Data Base and its Protection, IT Act and Civil Procedure Code, IT Act and Criminal Procedural Code, Relevant Sections of Indian Evidence Act, Relevant Sections of Bankers Book Evidence Act, Relevant Sections of Indian Penal Code, Relevant Sections of Reserve Bank of India Act, Law Relating To Employees And Internet, Alternative Dispute Resolution , Online Dispute Resolution (ODR)
CLE Unit - 2 - Information Technology Act

Overview of IT Act, 2000, Amendments and Limitations of IT Act, Digital Signatures, Cryptographic Algorithm, Public Cryptography, Private Cryptography, Electronic Governance, Legal Recognition of Electronic Records, Legal Recognition of Digital Signature, Certifying Authorities, Cyber Crime and Offences, Network Service Providers Liability, Cyber Regulations Appellate Tribunal, Penalties and Adjudication.
Heap management in Compiler Construction

Heap management in Compiler Construction
Compiler Construction
Compiler Design
Object Oriented Programming with JAVA

Lecture Notes
Module-1, Chapter-1
An Overview of Java
Programme: B E (CSE)
Semester: 3
Course Code: BCS306A
Course Instructor: Demian Antony Dmello
2022 Scheme of VTU
An Overview of Java: Object-Oriented Programming (Two Paradigms, Abstraction, The Three OOP Principles), Using Blocks of Code, Lexical Issues (Whitespace, Identifiers, Literals, Comments, Separators, The Java Keywords).
Data Types, Variables, and Arrays: The Primitive Types (Integers, Floating-Point Types, Characters, Booleans), Variables, Type Conversion and Casting, Automatic Type Promotion in Expressions, Arrays, Introducing Type Inference with Local Variables.
Operators: Arithmetic Operators, Relational Operators, Boolean Logical Operators, The Assignment Operator, The ? Operator, Operator Precedence, Using Parentheses.
Control Statements: Java’s Selection Statements (if, The Traditional switch), Iteration Statements (while, do-while, for, The For-Each Version of the for Loop, Local Variable Type Inference in a for Loop, Nested Loops), Jump Statements (Using break, Using continue, return).
An Overview of Java; Data Types, Variables and Arrays; Operators; Control Statements.
Introducing Classes; Methods and Classes.
Inheritance; Interfaces.
Packages; Exceptions.
Multithreaded Programming; Enumerations, Type Wrappers and Autoboxing.
Textbook
Java: The Complete Reference, Twelfth Edition, by Herbert Schildt, November 2021, McGraw-Hill, ISBN: 9781260463422
References:
Programming with Java, 6th Edition, by E Balagurusamy, Mar-2019, McGraw Hill Education, ISBN: 9789353162337
Thinking in Java, Fourth Edition, by Bruce Eckel, Prentice Hall, 2006 (https://sd.blackball.lv/library/thinking_in_java_4th_edition.pdf)
Recommended
CLE Unit - 1 - Introduction to Cyber Law

Evolution of computer Technology, emergence of cyber space. Cyber Jurisprudence, Jurisprudence and law, Doctrinal approach, Consensual approach, Real Approach, Cyber Ethics, Cyber Jurisdiction, Hierarchy of courts, Civil and criminal jurisdictions, Cyberspace-Web space, Web hosting and web Development agreement, Legal and Technological Significance of domain Names, Internet as a tool for global access.
VTU Network & cyber security (1-5 Module) Full notes

Network & cyber security
Transport Level Security: Web Security Considerations, Secure Sockets Layer, Transport
Layer Security, HTTPS, Secure Shell (SSH).
E-mail Security: Pretty Good Privacy, S/MIME, Domain keys identified mail.
IP Security: IP Security Overview, IP Security Policy, Encapsulation Security Payload (ESP),Combining security Associations Internet Key Exchange. Cryptographic Suites
Cyber network security concepts: Security Architecture, antipattern: signature based
malware detection versus polymorphic threads, document driven certification and
accreditation, policy driven security certifications. Refactored solution: reputational,
behavioural and entropy based malware detection.
The problems: cyber antipatterns concept, forces in cyber antipatterns, cyber anti pattern
templates, cyber security antipattern catalog.
Cyber network security concepts contd. :
Enterprise security using Zachman framework
Zachman framework for enterprise architecture, primitive models versus composite
models, architectural problem solving patterns, enterprise workshop, matrix mining, mini
patterns for problem solving meetings.
Case study: cyber security hands on – managing administrations and root accounts,
installing hardware, reimaging OS, installing system protection/ antimalware, configuring
firewalls
CLE Unit - 3 - Cyber law and Related Legislation

Patent Law, Trademark Law, Copyright, Software – Copyright or Patented, Domain Names and Copyright disputes, Electronic Data Base and its Protection, IT Act and Civil Procedure Code, IT Act and Criminal Procedural Code, Relevant Sections of Indian Evidence Act, Relevant Sections of Bankers Book Evidence Act, Relevant Sections of Indian Penal Code, Relevant Sections of Reserve Bank of India Act, Law Relating To Employees And Internet, Alternative Dispute Resolution , Online Dispute Resolution (ODR)
CLE Unit - 2 - Information Technology Act

Overview of IT Act, 2000, Amendments and Limitations of IT Act, Digital Signatures, Cryptographic Algorithm, Public Cryptography, Private Cryptography, Electronic Governance, Legal Recognition of Electronic Records, Legal Recognition of Digital Signature, Certifying Authorities, Cyber Crime and Offences, Network Service Providers Liability, Cyber Regulations Appellate Tribunal, Penalties and Adjudication.
Heap management in Compiler Construction

Heap management in Compiler Construction
Compiler Construction
Compiler Design
Object Oriented Programming with JAVA

Lecture Notes
Module-1, Chapter-1
An Overview of Java
Programme: B E (CSE)
Semester: 3
Course Code: BCS306A
Course Instructor: Demian Antony Dmello
2022 Scheme of VTU
An Overview of Java: Object-Oriented Programming (Two Paradigms, Abstraction, The Three OOP Principles), Using Blocks of Code, Lexical Issues (Whitespace, Identifiers, Literals, Comments, Separators, The Java Keywords).
Data Types, Variables, and Arrays: The Primitive Types (Integers, Floating-Point Types, Characters, Booleans), Variables, Type Conversion and Casting, Automatic Type Promotion in Expressions, Arrays, Introducing Type Inference with Local Variables.
Operators: Arithmetic Operators, Relational Operators, Boolean Logical Operators, The Assignment Operator, The ? Operator, Operator Precedence, Using Parentheses.
Control Statements: Java’s Selection Statements (if, The Traditional switch), Iteration Statements (while, do-while, for, The For-Each Version of the for Loop, Local Variable Type Inference in a for Loop, Nested Loops), Jump Statements (Using break, Using continue, return).
An Overview of Java; Data Types, Variables and Arrays; Operators; Control Statements.
Introducing Classes; Methods and Classes.
Inheritance; Interfaces.
Packages; Exceptions.
Multithreaded Programming; Enumerations, Type Wrappers and Autoboxing.
Textbook
Java: The Complete Reference, Twelfth Edition, by Herbert Schildt, November 2021, McGraw-Hill, ISBN: 9781260463422
References:
Programming with Java, 6th Edition, by E Balagurusamy, Mar-2019, McGraw Hill Education, ISBN: 9789353162337
Thinking in Java, Fourth Edition, by Bruce Eckel, Prentice Hall, 2006 (https://sd.blackball.lv/library/thinking_in_java_4th_edition.pdf)
4. Internet of Things - Reference Model and Architecture

Architecture Reference Model Introduction, Reference Model and architecture, IoT reference Model, Functional View, Information View, Deployment and Operational View, Real World Design Constraints- Introduction, Technical Design constraints, Data representation and visualization
DBMS Unit - 7 - Transaction Processing

Concurrency control, ACID property, Serializability of scheduling, Locking and timestamp based schedulers, Multi-version and optimistic Concurrency Control schemes, Database recovery.
IEEE 802.11 Architecture and Services

This Presentation is used to create PPT on the topic of "IEEE 802.11 Architecture and Services" in Mobile Computing and Wireless Communication.
Intro. IoT Module 1- 22ETC15H by Dr.Suresha V.pdf

Introduction to IoT for 1st year VTU students for the syllabus 2022-23.
Module 1:Basics of networking and Emergence of IoT examination notes.
Emerging technology course (ETC) for 1st-year students.
prepared by Dr.Suresha V, Professor,KVGCE,Sullia.(d.K)
Leaky Bucket & Tocken Bucket - Traffic shaping

This presentation provides a description about the traffic shaping in computer network like leaky bucket and token bucket and their differences
Transport services

This is about Transport services which is provided by transport layer of Open System Interconnection(OSI).
1. Internet of Things - M2M to IoT

The Vision-Introduction, From M2M to IoT, M2M towards IoT the global context, A use case example, Differing Characteristics
MEDIUM ACCESS CONTROL

In the seven-layer OSI model of computer networking, media access control (MAC) data communication protocol is a sublayer of the data link layer (layer 2). The MAC sublayer provides addressing and channel access control mechanisms that make it possible for several terminals or network nodes to communicate within a multiple access network that incorporates a shared medium, e.g. an Ethernet network. The hardware that implements the MAC is referred to as a media access controller.
The MAC sublayer acts as an interface between the logical link control (LLC) sublayer and the network's physical layer. The MAC layer emulates a full-duplex logical communication channel in a multi-point network. This channel may provide unicast, multicast or broadcast communication service.
Computer Network MAC Layer Notes as per RGPV syllabus

Data Link Sublayer Layer MAC Layer, Aloha, Ethernet, CSMA, CSMA/CD, Contention free protocol, High adaptive tree walk, binary back off algorithm etc
CYBERSPACE & CRIMINAL BEHAVIOR

CYBERSPACE
CYBER POWER
INTERNET
CYBER-ATTACK
INDIA AND PAKISTAN CYBER ATTACKS
TYPES OF CYBER CRIME
Hypotheses in the Research
Literature on the Influence of Mass Media on Criminal Behavior
Technology-Related Risk Factors for Criminal Behavior
COPYCAT CRIME:
CYBER SECURITY
SAFETY TIPS FOR CYBER CRIME
Multiplexing in mobile computing

In this I am discuss about the various multiplexing technique used in mobile computing
Cyber Security - Unit - 1 - Systems Vulnerability Scanning Overview of Vulner...

Cyber Security - Unit - 1 - Systems Vulnerability Scanning Overview of Vulner...Gyanmanjari Institute Of Technology
Systems Vulnerability Scanning Overview of vulnerability scanning, Open Port / Service Identification, Banner / Version Check, Traffic Probe, Vulnerability Probe, Vulnerability Examples, OpenVAS, Metasploit. Networks Vulnerability Scanning - Netcat, Socat, understanding Port and Services tools - Datapipe, Fpipe, WinRelay, Network Reconnaissance – Nmap, THC-Amap and System tools. Network Sniffers and Injection tools – Tcpdump and Windump, Wireshark, Ettercap, Hping Kismet.Network sniffers & injection tools

Network sniffers & injection tools
Network Threats Attack
Specific Attack Types
Network Sniffer
How does a Sniffer Work?
How can I detect a packet sniffer?
Packet Sniffer Mitigation
Injection Tools
OSV - Unit - 4 - Inter Process Communication

Inter Process Communication:
Race Conditions, Critical Section, Mutual Exclusion, Hardware Solution, Strict Alternation, Peterson’s Solution, The Producer Consumer Problem, Semaphores, Event Counters, Monitors, Message Passing, Classical IPC Problems: Reader’s & Writer Problem, Dinning Philosopher Problem etc., Scheduling, Scheduling Algorithms.
Function and Recursively defined function

Discrete Structure UNIT 1: Functions, complete notes as per syllabus of AKTU, Lucknow
Relation in Discrete Mathematics 

Discrete Structure UNIT 1: RELATIONS, complete notes as per syllabus of AKTU, Lucknow
More Related Content
What's hot
4. Internet of Things - Reference Model and Architecture

Architecture Reference Model Introduction, Reference Model and architecture, IoT reference Model, Functional View, Information View, Deployment and Operational View, Real World Design Constraints- Introduction, Technical Design constraints, Data representation and visualization
DBMS Unit - 7 - Transaction Processing

Concurrency control, ACID property, Serializability of scheduling, Locking and timestamp based schedulers, Multi-version and optimistic Concurrency Control schemes, Database recovery.
IEEE 802.11 Architecture and Services

This Presentation is used to create PPT on the topic of "IEEE 802.11 Architecture and Services" in Mobile Computing and Wireless Communication.
Intro. IoT Module 1- 22ETC15H by Dr.Suresha V.pdf

Introduction to IoT for 1st year VTU students for the syllabus 2022-23.
Module 1:Basics of networking and Emergence of IoT examination notes.
Emerging technology course (ETC) for 1st-year students.
prepared by Dr.Suresha V, Professor,KVGCE,Sullia.(d.K)
Leaky Bucket & Tocken Bucket - Traffic shaping

This presentation provides a description about the traffic shaping in computer network like leaky bucket and token bucket and their differences
Transport services

This is about Transport services which is provided by transport layer of Open System Interconnection(OSI).
1. Internet of Things - M2M to IoT

The Vision-Introduction, From M2M to IoT, M2M towards IoT the global context, A use case example, Differing Characteristics
MEDIUM ACCESS CONTROL

In the seven-layer OSI model of computer networking, media access control (MAC) data communication protocol is a sublayer of the data link layer (layer 2). The MAC sublayer provides addressing and channel access control mechanisms that make it possible for several terminals or network nodes to communicate within a multiple access network that incorporates a shared medium, e.g. an Ethernet network. The hardware that implements the MAC is referred to as a media access controller.
The MAC sublayer acts as an interface between the logical link control (LLC) sublayer and the network's physical layer. The MAC layer emulates a full-duplex logical communication channel in a multi-point network. This channel may provide unicast, multicast or broadcast communication service.
Computer Network MAC Layer Notes as per RGPV syllabus

Data Link Sublayer Layer MAC Layer, Aloha, Ethernet, CSMA, CSMA/CD, Contention free protocol, High adaptive tree walk, binary back off algorithm etc
CYBERSPACE & CRIMINAL BEHAVIOR

CYBERSPACE
CYBER POWER
INTERNET
CYBER-ATTACK
INDIA AND PAKISTAN CYBER ATTACKS
TYPES OF CYBER CRIME
Hypotheses in the Research
Literature on the Influence of Mass Media on Criminal Behavior
Technology-Related Risk Factors for Criminal Behavior
COPYCAT CRIME:
CYBER SECURITY
SAFETY TIPS FOR CYBER CRIME
Multiplexing in mobile computing

In this I am discuss about the various multiplexing technique used in mobile computing
Cyber Security - Unit - 1 - Systems Vulnerability Scanning Overview of Vulner...

Cyber Security - Unit - 1 - Systems Vulnerability Scanning Overview of Vulner...Gyanmanjari Institute Of Technology
Systems Vulnerability Scanning Overview of vulnerability scanning, Open Port / Service Identification, Banner / Version Check, Traffic Probe, Vulnerability Probe, Vulnerability Examples, OpenVAS, Metasploit. Networks Vulnerability Scanning - Netcat, Socat, understanding Port and Services tools - Datapipe, Fpipe, WinRelay, Network Reconnaissance – Nmap, THC-Amap and System tools. Network Sniffers and Injection tools – Tcpdump and Windump, Wireshark, Ettercap, Hping Kismet.Network sniffers & injection tools

Network sniffers & injection tools
Network Threats Attack
Specific Attack Types
Network Sniffer
How does a Sniffer Work?
How can I detect a packet sniffer?
Packet Sniffer Mitigation
Injection Tools
OSV - Unit - 4 - Inter Process Communication

Inter Process Communication:
Race Conditions, Critical Section, Mutual Exclusion, Hardware Solution, Strict Alternation, Peterson’s Solution, The Producer Consumer Problem, Semaphores, Event Counters, Monitors, Message Passing, Classical IPC Problems: Reader’s & Writer Problem, Dinning Philosopher Problem etc., Scheduling, Scheduling Algorithms.
What's hot (20)
4. Internet of Things - Reference Model and Architecture

4. Internet of Things - Reference Model and Architecture
Computer Network MAC Layer Notes as per RGPV syllabus

Computer Network MAC Layer Notes as per RGPV syllabus
Cyber Security - Unit - 1 - Systems Vulnerability Scanning Overview of Vulner...

Cyber Security - Unit - 1 - Systems Vulnerability Scanning Overview of Vulner...
More from NANDINI SHARMA
Function and Recursively defined function

Discrete Structure UNIT 1: Functions, complete notes as per syllabus of AKTU, Lucknow
Relation in Discrete Mathematics 

Discrete Structure UNIT 1: RELATIONS, complete notes as per syllabus of AKTU, Lucknow
Mathematical Induction in Discrete Structure

Discrete Structure UNIT 1: Mathematical Induction, complete notes as per syllabus of AKTU, Lucknow
SETS in Discrete Structure

Discrete Structure UNIT 1: SETS, complete notes as per syllabus of AKTU, Lucknow
Predicate logic

Discrete Structure UNIT 4: Predicate Logic, complete notes as per syllabus of AKTU, Lucknow
Rules of Inference in Discrete Structure

Discrete Structure UNIT 4: Rules of Inference, complete notes as per syllabus of AKTU, Lucknow
Proposition Logic in Discrete Structure

Discrete Structure UNIT 4: Propositional Logic, complete notes as per syllabus of AKTU, Lucknow
Algebraic Structure Part 2 DSTL

Discrete Structure: Algebraic Structure PART 2 complete notes as per syllabus of AKTU, Lucknow
FIELD in Discrete Structure

Field in Discrete Structure, part of Algebraic Structure, complete notes as per syllabus of AKTU, Lucknow
Algebraic Structure

Discrete Structure UNIT 2 Algebraic Structure complete notes as per syllabus of AKTU, Lucknow
LATTICE in Discrete Structure

LATTICE: UNIT 3 complete notes as per AKTU, LUCKNOW
Discrete Structure & Theory of Logic
DSTL: TREES AND GRAPH

Unit 5 of DSTL (Discrete Structure & Theory of Logic) as per AKTU, Lucknow Syllabus, complete notes.
Computer Graphics

Introduction of Computer Graphics, Basic Terminology, Cathode Ray Tube, Raster Scan Display Vs Random Scan Display, Applications
Computer Architecture & Organization

Boolean Algebra, Logic gates, combinational and sequential logic gates, Flynn's Classification, RISC Vs CISC, address modes, registers, memory, operating system etc
Database Management System

Introduction, DBA, types of Keys, Data Models, Three level architecture, E-R models into tables etc
Multimedia 

Introduction, architecture of multimedia, multimedia input and output devices, ADSL, ATM, multimedia database, animation techniques, aliasing and anti-aliasing, morphing, video on demand
Number System (Computer)

Number System, Positional and non-positional number system, conversion number system from binary to another base and vice versa, decimal to another base and vice versa, convert another base than 10 to another base than 10, binary arithmetic operation such as binary addition, subtraction, multiplication, division
More from NANDINI SHARMA (20)
Recently uploaded
Building Electrical System Design & Installation

Guide for Building Electrical System Design & Installation
Nuclear Power Economics and Structuring 2024

Title: Nuclear Power Economics and Structuring - 2024 Edition
Produced by: World Nuclear Association Published: April 2024
Report No. 2024/001
© 2024 World Nuclear Association.
Registered in England and Wales, company number 01215741
This report reflects the views
of industry experts but does not
necessarily represent those
of World Nuclear Association’s
individual member organizations.
在线办理(ANU毕业证书)澳洲国立大学毕业证录取通知书一模一样

学校原件一模一样【微信:741003700 】《(ANU毕业证书)澳洲国立大学毕业证》【微信:741003700 】学位证,留信认证(真实可查,永久存档)原件一模一样纸张工艺/offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原。
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
【主营项目】
一.毕业证【q微741003700】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【q/微741003700】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
Immunizing Image Classifiers Against Localized Adversary Attacks

This paper addresses the vulnerability of deep learning models, particularly convolutional neural networks
(CNN)s, to adversarial attacks and presents a proactive training technique designed to counter them. We
introduce a novel volumization algorithm, which transforms 2D images into 3D volumetric representations.
When combined with 3D convolution and deep curriculum learning optimization (CLO), itsignificantly improves
the immunity of models against localized universal attacks by up to 40%. We evaluate our proposed approach
using contemporary CNN architectures and the modified Canadian Institute for Advanced Research (CIFAR-10
and CIFAR-100) and ImageNet Large Scale Visual Recognition Challenge (ILSVRC12) datasets, showcasing
accuracy improvements over previous techniques. The results indicate that the combination of the volumetric
input and curriculum learning holds significant promise for mitigating adversarial attacks without necessitating
adversary training.
CW RADAR, FMCW RADAR, FMCW ALTIMETER, AND THEIR PARAMETERS

It consists of cw radar and fmcw radar ,range measurement,if amplifier and fmcw altimeterThe CW radar operates using continuous wave transmission, while the FMCW radar employs frequency-modulated continuous wave technology. Range measurement is a crucial aspect of radar systems, providing information about the distance to a target. The IF amplifier plays a key role in signal processing, amplifying intermediate frequency signals for further analysis. The FMCW altimeter utilizes frequency-modulated continuous wave technology to accurately measure altitude above a reference point.
Governing Equations for Fundamental Aerodynamics_Anderson2010.pdf

Governing Equations for Fundamental Aerodynamics
Final project report on grocery store management system..pdf

In today’s fast-changing business environment, it’s extremely important to be able to respond to client needs in the most effective and timely manner. If your customers wish to see your business online and have instant access to your products or services.
Online Grocery Store is an e-commerce website, which retails various grocery products. This project allows viewing various products available enables registered users to purchase desired products instantly using Paytm, UPI payment processor (Instant Pay) and also can place order by using Cash on Delivery (Pay Later) option. This project provides an easy access to Administrators and Managers to view orders placed using Pay Later and Instant Pay options.
In order to develop an e-commerce website, a number of Technologies must be studied and understood. These include multi-tiered architecture, server and client-side scripting techniques, implementation technologies, programming language (such as PHP, HTML, CSS, JavaScript) and MySQL relational databases. This is a project with the objective to develop a basic website where a consumer is provided with a shopping cart website and also to know about the technologies used to develop such a website.
This document will discuss each of the underlying technologies to create and implement an e- commerce website.
Heap Sort (SS).ppt FOR ENGINEERING GRADUATES, BCA, MCA, MTECH, BSC STUDENTS

HEAP SORT ILLUSTRATED WITH HEAPIFY, BUILD HEAP FOR DYNAMIC ARRAYS.
Heap sort is a comparison-based sorting technique based on Binary Heap data structure. It is similar to the selection sort where we first find the minimum element and place the minimum element at the beginning. Repeat the same process for the remaining elements.
Gen AI Study Jams _ For the GDSC Leads in India.pdf

Gen AI Study Jams _ For the GDSC Leads in India.pdf
Design and Analysis of Algorithms-DP,Backtracking,Graphs,B&B

Dynamic Programming
Backtracking
Techniques for Graphs
Branch and Bound
6th International Conference on Machine Learning & Applications (CMLA 2024)

6th International Conference on Machine Learning & Applications (CMLA 2024) will provide an excellent international forum for sharing knowledge and results in theory, methodology and applications of on Machine Learning & Applications.
Water billing management system project report.pdf

Our project entitled “Water Billing Management System” aims is to generate Water bill with all the charges and penalty. Manual system that is employed is extremely laborious and quite inadequate. It only makes the process more difficult and hard.
The aim of our project is to develop a system that is meant to partially computerize the work performed in the Water Board like generating monthly Water bill, record of consuming unit of water, store record of the customer and previous unpaid record.
We used HTML/PHP as front end and MYSQL as back end for developing our project. HTML is primarily a visual design environment. We can create a android application by designing the form and that make up the user interface. Adding android application code to the form and the objects such as buttons and text boxes on them and adding any required support code in additional modular.
MySQL is free open source database that facilitates the effective management of the databases by connecting them to the software. It is a stable ,reliable and the powerful solution with the advanced features and advantages which are as follows: Data Security.MySQL is free open source database that facilitates the effective management of the databases by connecting them to the software.
Top 10 Oil and Gas Projects in Saudi Arabia 2024.pdf

Saudi Arabia stands as a titan in the global energy landscape, renowned for its abundant oil and gas resources. It's the largest exporter of petroleum and holds some of the world's most significant reserves. Let's delve into the top 10 oil and gas projects shaping Saudi Arabia's energy future in 2024.
Recycled Concrete Aggregate in Construction Part III

Using recycled concrete aggregates (RCA) for pavements is crucial to achieving sustainability. Implementing RCA for new pavement can minimize carbon footprint, conserve natural resources, reduce harmful emissions, and lower life cycle costs. Compared to natural aggregate (NA), RCA pavement has fewer comprehensive studies and sustainability assessments.
Technical Drawings introduction to drawing of prisms

Method of technical Drawing of prisms,and cylinders.
一比一原版(SFU毕业证)西蒙菲莎大学毕业证成绩单如何办理

SFU毕业证原版定制【微信:176555708】【西蒙菲莎大学毕业证成绩单-学位证】【微信:176555708】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
学历顾问:微信:176555708
Investor-Presentation-Q1FY2024 investor presentation document.pptx

this is the investor presemtaiton document for qurrter 1 2024
Recently uploaded (20)
Pile Foundation by Venkatesh Taduvai (Sub Geotechnical Engineering II)-conver...

Pile Foundation by Venkatesh Taduvai (Sub Geotechnical Engineering II)-conver...
Immunizing Image Classifiers Against Localized Adversary Attacks

Immunizing Image Classifiers Against Localized Adversary Attacks
CW RADAR, FMCW RADAR, FMCW ALTIMETER, AND THEIR PARAMETERS

CW RADAR, FMCW RADAR, FMCW ALTIMETER, AND THEIR PARAMETERS
Governing Equations for Fundamental Aerodynamics_Anderson2010.pdf

Governing Equations for Fundamental Aerodynamics_Anderson2010.pdf
Final project report on grocery store management system..pdf

Final project report on grocery store management system..pdf
Heap Sort (SS).ppt FOR ENGINEERING GRADUATES, BCA, MCA, MTECH, BSC STUDENTS

Heap Sort (SS).ppt FOR ENGINEERING GRADUATES, BCA, MCA, MTECH, BSC STUDENTS
Gen AI Study Jams _ For the GDSC Leads in India.pdf

Gen AI Study Jams _ For the GDSC Leads in India.pdf
Design and Analysis of Algorithms-DP,Backtracking,Graphs,B&B

Design and Analysis of Algorithms-DP,Backtracking,Graphs,B&B
6th International Conference on Machine Learning & Applications (CMLA 2024)

6th International Conference on Machine Learning & Applications (CMLA 2024)
Water billing management system project report.pdf

Water billing management system project report.pdf
Top 10 Oil and Gas Projects in Saudi Arabia 2024.pdf

Top 10 Oil and Gas Projects in Saudi Arabia 2024.pdf
Recycled Concrete Aggregate in Construction Part III

Recycled Concrete Aggregate in Construction Part III
Technical Drawings introduction to drawing of prisms

Technical Drawings introduction to drawing of prisms
Investor-Presentation-Q1FY2024 investor presentation document.pptx

Investor-Presentation-Q1FY2024 investor presentation document.pptx
