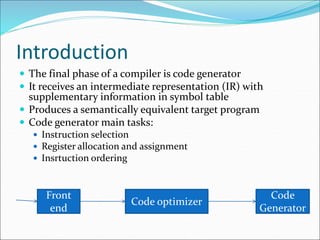
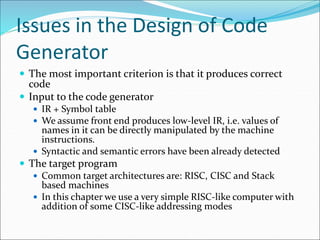
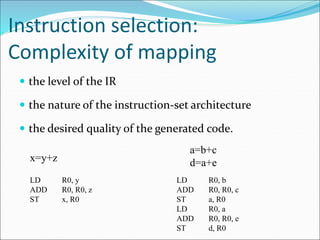
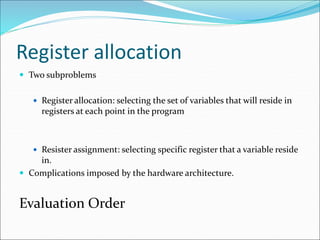
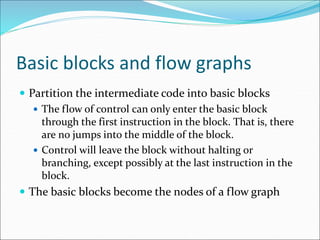
The document discusses code generation in compilers. It covers topics like instruction selection, register allocation, basic blocks, peephole optimizations, and global register allocation. The final phase of a compiler is code generation, which takes an intermediate representation and symbol table and produces target code. Key tasks include instruction selection, register allocation and assignment, and instruction ordering.