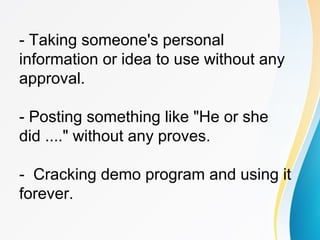
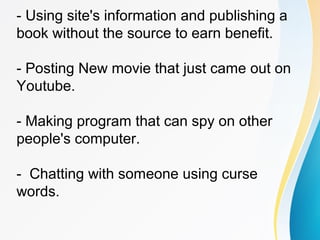
The document discusses various ethical issues related to privacy and the use of technology by IT professionals and young individuals, highlighting questions about surveillance, monitoring online behavior, and handling personal information. It emphasizes the importance of individual ethics and the development of guidelines by professional associations. Additionally, it covers the ethical implications of computer resource abuse, including stealing information and unauthorized access to personal data.