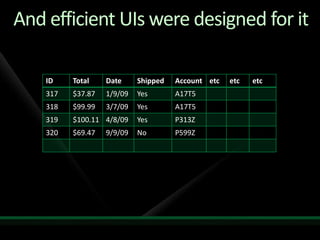
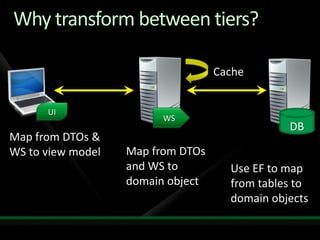
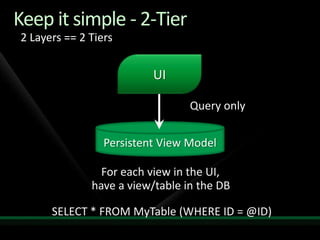
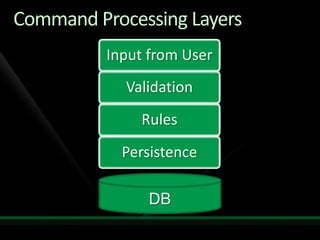
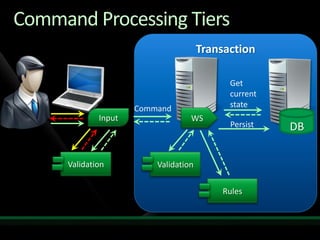
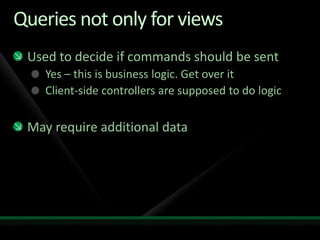
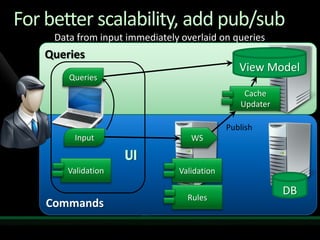
1. The document discusses the Command Query Responsibility Segregation (CQRS) pattern for separating queries from commands in distributed systems. It advocates keeping queries simple with a two-tier architecture without data transfer objects.
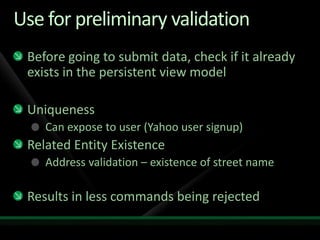
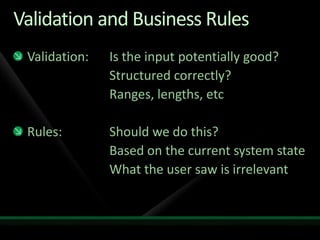
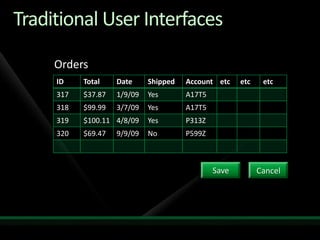
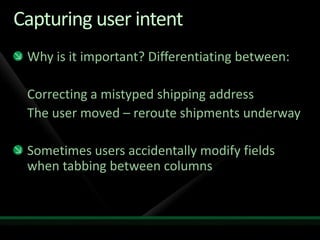
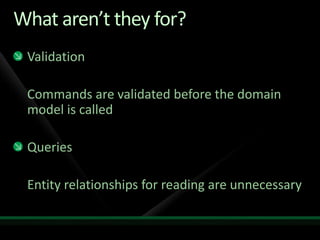
2. It also recommends designing user interfaces to capture user intent, having commands reflect that intent. Validation should be simple and business rules focused.
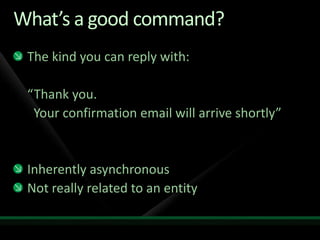
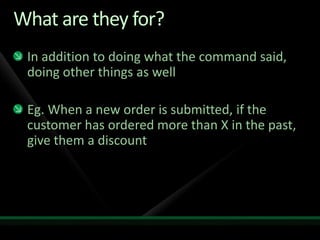
3. The CQRS pattern publishes commands asynchronously to improve scalability. Domain models only persist needed data and implement business logic rather than queries or validation.