cloud compute
•
0 likes•27 views
This document contains an examination paper for a course on virtualization and cloud technology. It consists of 5 questions, with students required to answer any 3 questions. Question 1 covers characteristics of cloud computing and cloud service models. Question 2 addresses system availability and measures it for different cluster configurations. Question 3 is about CPU virtualization techniques including hardware-assisted virtualization. Question 4 examines the MapReduce framework functions and execution. Question 5 discusses service-oriented architecture, Representational State Transfer architecture, and REST principles.
Report
Share
Report
Share
Download to read offline
Recommended
Many-Objective Performance Enhancement in Computing Clusters

In a heterogeneous computing cluster, cluster objectives are conflicting to each other. Selecting a right combination of machines is necessary to enhance cluster performance, and to optimize all the cluster objectives. In this paper, we perform empirical performance analyses of a real cluster with our year-long collected data, formulate a new many-objective optimization problem for clusters, and integrate a greedy approach with the existing NSGA-III algorithm to solve this problem. From our experimental results, we find our approach performs better than existing optimization approaches.
A Highly Parallel Semi-Dataflow FPGA Architecture for Large-Scale N-Body Simu...

A Highly Parallel Semi-Dataflow FPGA Architecture for Large-Scale N-Body Simu...NECST Lab @ Politecnico di Milano
NGC17 Talk @ Berkeley Lab - June 5, 2017Fractality of Massive Graphs: Scalable Analysis with Sketch-Based Box-Coverin...

Presentation for ICDM 2016
PRETZEL: Opening the Black Box of Machine Learning Prediction Serving Systems

PRETZEL: Opening the Black Box of Machine Learning Prediction Serving SystemsNECST Lab @ Politecnico di Milano
Machine Learning (ML) models are often composed as pipelines of operators, from “classical” ML operators to pre-processing and featurization operators. Current systems deploy pipelines as "black boxes”, where the same implementation of training is run for inference. This solution is convenient but leaves large room to improve performance and resource usage. This talk presents Pretzel, a framework for deployment of ML pipelines that is inspired to Database Systems: Pretzel inspects and optimizes pipelines end-to-end much like queries, and manages resources common to multiple pipelines such as operators' state. Pretzel is joint work with University of Seoul and Microsoft Research and has recently been presented at OSDI ’18. After the overview, this talk also shows experimental results of Pretzel against state-of-art ML solutions and discusses limitations and extensions.Recommended
Many-Objective Performance Enhancement in Computing Clusters

In a heterogeneous computing cluster, cluster objectives are conflicting to each other. Selecting a right combination of machines is necessary to enhance cluster performance, and to optimize all the cluster objectives. In this paper, we perform empirical performance analyses of a real cluster with our year-long collected data, formulate a new many-objective optimization problem for clusters, and integrate a greedy approach with the existing NSGA-III algorithm to solve this problem. From our experimental results, we find our approach performs better than existing optimization approaches.
A Highly Parallel Semi-Dataflow FPGA Architecture for Large-Scale N-Body Simu...

A Highly Parallel Semi-Dataflow FPGA Architecture for Large-Scale N-Body Simu...NECST Lab @ Politecnico di Milano
NGC17 Talk @ Berkeley Lab - June 5, 2017Fractality of Massive Graphs: Scalable Analysis with Sketch-Based Box-Coverin...

Presentation for ICDM 2016
PRETZEL: Opening the Black Box of Machine Learning Prediction Serving Systems

PRETZEL: Opening the Black Box of Machine Learning Prediction Serving SystemsNECST Lab @ Politecnico di Milano
Machine Learning (ML) models are often composed as pipelines of operators, from “classical” ML operators to pre-processing and featurization operators. Current systems deploy pipelines as "black boxes”, where the same implementation of training is run for inference. This solution is convenient but leaves large room to improve performance and resource usage. This talk presents Pretzel, a framework for deployment of ML pipelines that is inspired to Database Systems: Pretzel inspects and optimizes pipelines end-to-end much like queries, and manages resources common to multiple pipelines such as operators' state. Pretzel is joint work with University of Seoul and Microsoft Research and has recently been presented at OSDI ’18. After the overview, this talk also shows experimental results of Pretzel against state-of-art ML solutions and discusses limitations and extensions.Quantization and Training of Neural Networks for Efficient Integer-Arithmetic...

Sumary of [arXiv:1712.05877]
DataXDay - Tensors in the sky with CloudML 

Out of curiosity, ask the other people in the conference room who has already developped neural networks: you will see a lot of hands up. Then ask them how many of those models run in production: epic fail.
Come and see a solution to train and deploy TensorFlow models in the cloud using Google CloudML.
Sylvain Lequeux - Xebia
https://dataxday.fr/
Video available: https://www.youtube.com/watch?v=oDpBRdjwNik
Large data with Scikit-learn - Boston Data Mining Meetup - Alex Perrier

A presentation of adaptive classification and regression algorithms available in scikit-learn with a Focus on Stochastic Gradient Descent and KNN. Performance examples on 2 Large datasets are presented for SGD, Multinomial Naive Bayes, Perceptron and Passive Aggressive Algorithms.
MongoDB Project: Relational databases to Document-Oriented databases

Avaliable at: https://github.com/dbsmasters/bdsmasters
The current project is implemented in the context of the course "Big Data Management Systems" taught by Prof. Chatziantoniou in the Department of Management Science and Technology (AUEB). The aim of the project is to familiarize the students with big data management systems such as Hadoop, Redis, MongoDB and Azure Stream Analytics.
Exploiting a Synergy between Greedy Approach and NSGA for Scheduling in Compu...

Computing clusters are evaluated using different performance metrics, which often appear to be conflicting while being attempted to be optimized. For such conflicting cases along with frequently having an existence of heterogeneous environment, it is difficult for the cluster administrators to efficiently schedule machines, i.e., to select the right number and right combination of machines. In this paper, we develop a technique through which cluster administrators can select the right set of machines to enhance energy efficiency and cluster performance. To do so, first, we perform extensive laboratory experiments for a period of more than one year. Based on empirical analyses of data collected from the experiments, we formulate a many-objective optimization problem for clusters and integrate a greedy approach with Non-dominated Sorting Genetic Algorithm (NSGA-III) to solve this problem. We demonstrate that our approach mostly performs better than existing approaches in the literature through both real experimentation and simulation.
Graph Regularised Hashing

Hashing has witnessed an increase in popularity over the
past few years due to the promise of compact encoding and fast query
time. In order to be effective hashing methods must maximally preserve
the similarity between the data points in the underlying binary representation.
The current best performing hashing techniques have utilised
supervision. In this paper we propose a two-step iterative scheme, Graph
Regularised Hashing (GRH), for incrementally adjusting the positioning
of the hashing hypersurfaces to better conform to the supervisory signal:
in the first step the binary bits are regularised using a data similarity
graph so that similar data points receive similar bits. In the second
step the regularised hashcodes form targets for a set of binary classifiers
which shift the position of each hypersurface so as to separate opposite
bits with maximum margin. GRH exhibits superior retrieval accuracy to
competing hashing methods.
Model compression

Model Compression (NanheeKim)
@NanheeKim @nh9k
질문이 있으면 언제든지 연락주세요!
공부한 것을 바탕으로 작성한 ppt입니다.
출처는 슬라이드 마지막에 있습니다!
Please, feel free to contact me, if you have any questions!
github: https://github.com/nh9k
email: kimnanhee97@gmail.com
Hanjun Dai, PhD Student, School of Computational Science and Engineering, Geo...

Graph Representation Learning with Deep Embedding Approach:
Graphs are commonly used data structure for representing the real-world relationships, e.g., molecular structure, knowledge graphs, social and communication networks. The effective encoding of graphical information is essential to the success of such applications. In this talk I’ll first describe a general deep learning framework, namely structure2vec, for end to end graph feature representation learning. Then I’ll present the direct application of this model on graph problems on different scales, including community detection and molecule graph classification/regression. We then extend the embedding idea to temporal evolving user-product interaction graph for recommendation. Finally I’ll present our latest work on leveraging the reinforcement learning technique for graph combinatorial optimization, including vertex cover problem for social influence maximization and traveling salesman problem for scheduling management.
A Scalable Dataflow Implementation of Curran's Approximation Algorithm

A Scalable Dataflow Implementation of Curran's Approximation AlgorithmNECST Lab @ Politecnico di Milano
A Scalable Dataflow Implementation of Curran's Approximation Algorithm, by Anna Maria Nestorov, MSc student in CE at Politecnico di MilanoMis 589 Success Begins / snaptutorial.com

1. (TCO A) A ___ defines the format and the order of messages exchanged between 2 or more communicating entities.
2. (TCO A) While the job of the link layer is to move entire frames from one network element to another, The job of the physical layer is to do what?
3. (TCO A) Which of the following is not true about ISO:
4. (TCO A) What are the two fundamental approaches to moving data through a network of links and
Mis 589 Massive Success / snaptutorial.com

. (TCO A) A ___ defines the format and the order of messages exchanged between 2 or more communicating entities.
2. (TCO A) While the job of the link layer is to move entire frames from one network element to another, The job of the physical layer is to do what?
3. (TCO A) Which of the following is not true about ISO:
4. (TCO A) What are the two fundamental approaches to moving data through a network of links and switches?
5. (TCO A) The IP protocol works at which layer of the OSI model?
BPSC Previous Year Question for AP, ANE, AME, ADA, AE 

BPSC Previous Year Question for Assistant Programmer, Assistant Maintenance Engineer, Assistant Network Engineer by Stack IT job Solution
Book : Stack IT job Solution (A pattern Based IT job solution)
বুয়েট, কুয়েট, রুয়েট, ডুয়েট, পিএসসি, টেলিকম, আইবিএ, এমআইএস
সহ যেকোন প্যার্টানে জব প্রস্তুতির একমাত্র বই।
Order Link: https://stackvaly.com/product/stack-it-job-solution-p3qxo
WhatsApp: 01789741518
More Related Content
What's hot
Quantization and Training of Neural Networks for Efficient Integer-Arithmetic...

Sumary of [arXiv:1712.05877]
DataXDay - Tensors in the sky with CloudML 

Out of curiosity, ask the other people in the conference room who has already developped neural networks: you will see a lot of hands up. Then ask them how many of those models run in production: epic fail.
Come and see a solution to train and deploy TensorFlow models in the cloud using Google CloudML.
Sylvain Lequeux - Xebia
https://dataxday.fr/
Video available: https://www.youtube.com/watch?v=oDpBRdjwNik
Large data with Scikit-learn - Boston Data Mining Meetup - Alex Perrier

A presentation of adaptive classification and regression algorithms available in scikit-learn with a Focus on Stochastic Gradient Descent and KNN. Performance examples on 2 Large datasets are presented for SGD, Multinomial Naive Bayes, Perceptron and Passive Aggressive Algorithms.
MongoDB Project: Relational databases to Document-Oriented databases

Avaliable at: https://github.com/dbsmasters/bdsmasters
The current project is implemented in the context of the course "Big Data Management Systems" taught by Prof. Chatziantoniou in the Department of Management Science and Technology (AUEB). The aim of the project is to familiarize the students with big data management systems such as Hadoop, Redis, MongoDB and Azure Stream Analytics.
Exploiting a Synergy between Greedy Approach and NSGA for Scheduling in Compu...

Computing clusters are evaluated using different performance metrics, which often appear to be conflicting while being attempted to be optimized. For such conflicting cases along with frequently having an existence of heterogeneous environment, it is difficult for the cluster administrators to efficiently schedule machines, i.e., to select the right number and right combination of machines. In this paper, we develop a technique through which cluster administrators can select the right set of machines to enhance energy efficiency and cluster performance. To do so, first, we perform extensive laboratory experiments for a period of more than one year. Based on empirical analyses of data collected from the experiments, we formulate a many-objective optimization problem for clusters and integrate a greedy approach with Non-dominated Sorting Genetic Algorithm (NSGA-III) to solve this problem. We demonstrate that our approach mostly performs better than existing approaches in the literature through both real experimentation and simulation.
Graph Regularised Hashing

Hashing has witnessed an increase in popularity over the
past few years due to the promise of compact encoding and fast query
time. In order to be effective hashing methods must maximally preserve
the similarity between the data points in the underlying binary representation.
The current best performing hashing techniques have utilised
supervision. In this paper we propose a two-step iterative scheme, Graph
Regularised Hashing (GRH), for incrementally adjusting the positioning
of the hashing hypersurfaces to better conform to the supervisory signal:
in the first step the binary bits are regularised using a data similarity
graph so that similar data points receive similar bits. In the second
step the regularised hashcodes form targets for a set of binary classifiers
which shift the position of each hypersurface so as to separate opposite
bits with maximum margin. GRH exhibits superior retrieval accuracy to
competing hashing methods.
Model compression

Model Compression (NanheeKim)
@NanheeKim @nh9k
질문이 있으면 언제든지 연락주세요!
공부한 것을 바탕으로 작성한 ppt입니다.
출처는 슬라이드 마지막에 있습니다!
Please, feel free to contact me, if you have any questions!
github: https://github.com/nh9k
email: kimnanhee97@gmail.com
Hanjun Dai, PhD Student, School of Computational Science and Engineering, Geo...

Graph Representation Learning with Deep Embedding Approach:
Graphs are commonly used data structure for representing the real-world relationships, e.g., molecular structure, knowledge graphs, social and communication networks. The effective encoding of graphical information is essential to the success of such applications. In this talk I’ll first describe a general deep learning framework, namely structure2vec, for end to end graph feature representation learning. Then I’ll present the direct application of this model on graph problems on different scales, including community detection and molecule graph classification/regression. We then extend the embedding idea to temporal evolving user-product interaction graph for recommendation. Finally I’ll present our latest work on leveraging the reinforcement learning technique for graph combinatorial optimization, including vertex cover problem for social influence maximization and traveling salesman problem for scheduling management.
A Scalable Dataflow Implementation of Curran's Approximation Algorithm

A Scalable Dataflow Implementation of Curran's Approximation AlgorithmNECST Lab @ Politecnico di Milano
A Scalable Dataflow Implementation of Curran's Approximation Algorithm, by Anna Maria Nestorov, MSc student in CE at Politecnico di MilanoWhat's hot (18)
Optimal Virtual Machine Placement across Multiple Cloud Providers

Optimal Virtual Machine Placement across Multiple Cloud Providers
Quantization and Training of Neural Networks for Efficient Integer-Arithmetic...

Quantization and Training of Neural Networks for Efficient Integer-Arithmetic...
Large data with Scikit-learn - Boston Data Mining Meetup - Alex Perrier

Large data with Scikit-learn - Boston Data Mining Meetup - Alex Perrier
Large Scale Kernel Learning using Block Coordinate Descent

Large Scale Kernel Learning using Block Coordinate Descent
06 how to write a map reduce version of k-means clustering

06 how to write a map reduce version of k-means clustering
MongoDB Project: Relational databases to Document-Oriented databases

MongoDB Project: Relational databases to Document-Oriented databases
Exploiting a Synergy between Greedy Approach and NSGA for Scheduling in Compu...

Exploiting a Synergy between Greedy Approach and NSGA for Scheduling in Compu...
Hanjun Dai, PhD Student, School of Computational Science and Engineering, Geo...

Hanjun Dai, PhD Student, School of Computational Science and Engineering, Geo...
A Scalable Dataflow Implementation of Curran's Approximation Algorithm

A Scalable Dataflow Implementation of Curran's Approximation Algorithm
Similar to cloud compute
Mis 589 Success Begins / snaptutorial.com

1. (TCO A) A ___ defines the format and the order of messages exchanged between 2 or more communicating entities.
2. (TCO A) While the job of the link layer is to move entire frames from one network element to another, The job of the physical layer is to do what?
3. (TCO A) Which of the following is not true about ISO:
4. (TCO A) What are the two fundamental approaches to moving data through a network of links and
Mis 589 Massive Success / snaptutorial.com

. (TCO A) A ___ defines the format and the order of messages exchanged between 2 or more communicating entities.
2. (TCO A) While the job of the link layer is to move entire frames from one network element to another, The job of the physical layer is to do what?
3. (TCO A) Which of the following is not true about ISO:
4. (TCO A) What are the two fundamental approaches to moving data through a network of links and switches?
5. (TCO A) The IP protocol works at which layer of the OSI model?
BPSC Previous Year Question for AP, ANE, AME, ADA, AE 

BPSC Previous Year Question for Assistant Programmer, Assistant Maintenance Engineer, Assistant Network Engineer by Stack IT job Solution
Book : Stack IT job Solution (A pattern Based IT job solution)
বুয়েট, কুয়েট, রুয়েট, ডুয়েট, পিএসসি, টেলিকম, আইবিএ, এমআইএস
সহ যেকোন প্যার্টানে জব প্রস্তুতির একমাত্র বই।
Order Link: https://stackvaly.com/product/stack-it-job-solution-p3qxo
WhatsApp: 01789741518
IFSM 310 Software and Hardware Infrastructure ConceptsComputer.docx

IFSM 310 Software and Hardware Infrastructure Concepts
Computer and Number Systems
1.
(10 pt)
You have been hired to develop a website-based sales system for a large international retail firm. List and describe at least four features that are specific to the Web design of your system and customer service important to consider if your system is to be successful at attracting and keeping customers living outside of the US. Include not only characteristics of the user interface, but those issues that must be uniquely addressed to successfully service your non-US customers.
2.
(2.5 pt each)
In order to receive credit for these problems, you must show all of the steps you took to arrive at your answers.
(c) Convert the following decimal number to binary:
21842
(d) Convert the following binary number to decimal:
11000111011.101
(c) Convert the following hexadecimal number to decimal:
CA97
(d) Convert the following binary number to hexadecimal:
1110011111011010100
CPU and Memory
3.
(10 pt)
ASCII, Unicode, and EBCDIC are, of course, not the only numeric / character codes. The Sophomites from the planet Collegium use the rather strange code shown in the Figure below. There are only thirteen characters in the Sophomite alphabet, and each character uses a 5-bit code. In addition, there are four numeric digits, since the Sophomites use base 4 for their arithmetic. Given the following Sophomite sequence, what is the corresponding binary message being sent by the Sophomites?
(HINT: Decode the sequence reading from left to right then write the corresponding binary sequence, leaving a space between each binary sequence.)
4.
(10 pt)
Define memory cache write-through and write-back techniques and describe the advantages and disadvantages of each.
Input / Output
5. Answer the follow questions about interrupts.
a.
(5 pt)
Describe in detail the steps that occur when a system receives an interrupt.
b.
(5 pt)
Describe how these steps differ in the case when a system receives multiple interrupts
Computer Systems
6. Answer the following questions about clusters.
a.
(5 pt)
Describe how you might use a cluster to provide fault-tolerant computing
b.
(5 pt)
Describe how you might use a cluster architecture to provide rapid scalability for a Web-based company experiencing rapid growth.
Networks
7. Answer the following questions about communication protocols.
a.
(5 pt)
Using the operations of UDP (User Datagram Protocol) and TCP (Transmission Control Protocol) as a basis, carefully explain the difference between connectionless and connection-oriented communication.
b.
(5 pt)
If you were ordering a number of items from an online seller, such as amazon.com, which Protocol (TCP or UDP) would you recommend and explain why
.
8. In the context of network security,
a.
(3 pt)
exp.
Evolutionary Multi-Goal Workflow Progress in Shade

https://irjet.net/archives/V4/i3/IRJET-V4I3416.pdf
Srushti_M.E_PPT.ppt

Three types of service model: SAAS, PAAS, IAAS
Four types of deployment model: Public, Private, Hybrid And community Cloud.
During the load balancing process, few issues are yet to be fully addressed. Couple of them are:
Some of the nodes are overutilized or some of the nodes are underutilized
Improper workload in Cloud environment results into overhead in resource utilization and in turn inefficient usage of energy
response time of jobs
communication cost of servers
maintain cost of VMs,
throughput and overload of any single node.
By addressing the concern of load balancing, we aim to address multiple facets of Cloud viz. (a) resource utilization (b) CPU time (c) Migration time.
Problem statement
Problem raised while dealing with load balancing
How to minimize the CPU time
How to increase the resource utilization &
How to decrease the energy consumption and Migration time etc.
Review and comparison of tasks scheduling in cloud computing

Recently, there has been a dramatic increase in the popularity of cloud computing systems that rent
computing resources on-demand, bill on a pay-as-you-go basis, and multiplex many users on the same
physical infrastructure. It is a virtual pool of resources which are provided to users via Internet. It gives
users virtually unlimited pay-per-use computing resources without the burden of managing the underlying
infrastructure. One of the goals is to use the resources efficiently and gain maximum profit. Scheduling is a
critical problem in Cloud computing, because a cloud provider has to serve many users in Cloud
computing system. So scheduling is the major issue in establishing Cloud computing systems. The
scheduling algorithms should order the jobs in a way where balance between improving the performance
and quality of service and at the same time maintaining the efficiency and fairness among the jobs. This
paper introduces and explores some of the methods provided for in cloud computing has been scheduled.
Finally the waiting time and time to implement some of the proposed algorithm is evaluated
Review and Comparison of Tasks Scheduling in Cloud Computing 

Recently, there has been a dramatic increase in the popularity of cloud computing systems that rent
computing resources on-demand, bill on a pay-as-you-go basis, and multiplex many users on the same
physical infrastructure. It is a virtual pool of resources which are provided to users via Internet. It gives
users virtually unlimited pay-per-use computing resources without the burden of managing the underlying
infrastructure. One of the goals is to use the resources efficiently and gain maximum profit. Scheduling is a
critical problem in Cloud computing, because a cloud provider has to serve many users in Cloud
computing system. So scheduling is the major issue in establishing Cloud computing systems. The
scheduling algorithms should order the jobs in a way where balance between improving the performance
and quality of service and at the same time maintaining the efficiency and fairness among the jobs. This
paper introduces and explores some of the methods provided for in cloud computing has been scheduled.
Finally the waiting time and time to implement some of the proposed algorithm is evaluated.
Optimizing Task Scheduling in Mobile Cloud Computing Using Particle Swarm Opt...

https://www.irjet.net/archives/V10/i4/IRJET-V10I4131.pdf
VTU 5TH SEM CSE OPERATING SYSTEMS SOLVED PAPERS

FOR FREE DOWNLOADING, OPEN THIS LINK: http://oke.io/oeMuOX
VIRTUAL MACHINE SCHEDULING IN CLOUD COMPUTING ENVIRONMENT

Cloud computing is an upcoming technology in dispersed computing facilitating paying for each model as
for each user demand and need. Cloud incorporates a set of virtual machine which comprises both storage
and computational facility. The fundamental goal of cloud computing is to offer effective access to isolated
and geographically circulated resources. Cloud is growing every day and experiences numerous problems
such as scheduling. Scheduling means a collection of policies to regulate the order of task to be executed
by a computer system. An excellent scheduler derives its scheduling plan in accordance with the type of
work and the varying environment. This research paper demonstrates a generalized precedence algorithm
for effective performance of work and contrast with Round Robin and FCFS Scheduling. Algorithm needs
to be tested within CloudSim toolkit and outcome illustrates that it provide good presentation compared
some customary scheduling algorithm.
An Optimized-Throttled Algorithm for Distributing Load in Cloud Computing

https://www.irjet.net/archives/V10/i12/IRJET-V10I1201.pdf
Similar to cloud compute (20)
BPSC Previous Year Question for AP, ANE, AME, ADA, AE 

BPSC Previous Year Question for AP, ANE, AME, ADA, AE
IFSM 310 Software and Hardware Infrastructure ConceptsComputer.docx

IFSM 310 Software and Hardware Infrastructure ConceptsComputer.docx
Evolutionary Multi-Goal Workflow Progress in Shade

Evolutionary Multi-Goal Workflow Progress in Shade
Review and comparison of tasks scheduling in cloud computing

Review and comparison of tasks scheduling in cloud computing
Iaetsd pinpointing performance deviations of subsystems in distributed

Iaetsd pinpointing performance deviations of subsystems in distributed
Review and Comparison of Tasks Scheduling in Cloud Computing 

Review and Comparison of Tasks Scheduling in Cloud Computing
Optimizing Task Scheduling in Mobile Cloud Computing Using Particle Swarm Opt...

Optimizing Task Scheduling in Mobile Cloud Computing Using Particle Swarm Opt...
VIRTUAL MACHINE SCHEDULING IN CLOUD COMPUTING ENVIRONMENT

VIRTUAL MACHINE SCHEDULING IN CLOUD COMPUTING ENVIRONMENT
An Optimized-Throttled Algorithm for Distributing Load in Cloud Computing

An Optimized-Throttled Algorithm for Distributing Load in Cloud Computing
Recently uploaded
The Art of the Pitch: WordPress Relationships and Sales

Clients don’t know what they don’t know. What web solutions are right for them? How does WordPress come into the picture? How do you make sure you understand scope and timeline? What do you do if sometime changes?
All these questions and more will be explored as we talk about matching clients’ needs with what your agency offers without pulling teeth or pulling your hair out. Practical tips, and strategies for successful relationship building that leads to closing the deal.
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
Key Trends Shaping the Future of Infrastructure.pdf

Keynote at DIGIT West Expo, Glasgow on 29 May 2024.
Cheryl Hung, ochery.com
Sr Director, Infrastructure Ecosystem, Arm.
The key trends across hardware, cloud and open-source; exploring how these areas are likely to mature and develop over the short and long-term, and then considering how organisations can position themselves to adapt and thrive.
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

The publishing industry has been selling digital audiobooks and ebooks for over a decade and has found its groove. What’s changed? What has stayed the same? Where do we go from here? Join a group of leading sales peers from across the industry for a conversation about the lessons learned since the popularization of digital books, best practices, digital book supply chain management, and more.
Link to video recording: https://bnctechforum.ca/sessions/selling-digital-books-in-2024-insights-from-industry-leaders/
Presented by BookNet Canada on May 28, 2024, with support from the Department of Canadian Heritage.
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP of Product, Amplitude
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

“AGI should be open source and in the public domain at the service of humanity and the planet.”
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI)
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality

In this insightful webinar, Inflectra explores how artificial intelligence (AI) is transforming software development and testing. Discover how AI-powered tools are revolutionizing every stage of the software development lifecycle (SDLC), from design and prototyping to testing, deployment, and monitoring.
Learn about:
• The Future of Testing: How AI is shifting testing towards verification, analysis, and higher-level skills, while reducing repetitive tasks.
• Test Automation: How AI-powered test case generation, optimization, and self-healing tests are making testing more efficient and effective.
• Visual Testing: Explore the emerging capabilities of AI in visual testing and how it's set to revolutionize UI verification.
• Inflectra's AI Solutions: See demonstrations of Inflectra's cutting-edge AI tools like the ChatGPT plugin and Azure Open AI platform, designed to streamline your testing process.
Whether you're a developer, tester, or QA professional, this webinar will give you valuable insights into how AI is shaping the future of software delivery.
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic (NeSy) AI is on the rise. However, simply machine learning on just any symbolic structure is not sufficient to really harvest the gains of NeSy. These will only be gained when the symbolic structures have an actual semantics. I give an operational definition of semantics as “predictable inference”.
All of this illustrated with link prediction over knowledge graphs, but the argument is general.
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scalable Platform by VP of Product, The New York Times
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
Recently uploaded (20)
The Art of the Pitch: WordPress Relationships and Sales

The Art of the Pitch: WordPress Relationships and Sales
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
Key Trends Shaping the Future of Infrastructure.pdf

Key Trends Shaping the Future of Infrastructure.pdf
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

Transcript: Selling digital books in 2024: Insights from industry leaders - T...
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...
Monitoring Java Application Security with JDK Tools and JFR Events

Monitoring Java Application Security with JDK Tools and JFR Events
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...
Leading Change strategies and insights for effective change management pdf 1.pdf

Leading Change strategies and insights for effective change management pdf 1.pdf
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality

Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality
Neuro-symbolic is not enough, we need neuro-*semantic*

Neuro-symbolic is not enough, we need neuro-*semantic*
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
cloud compute
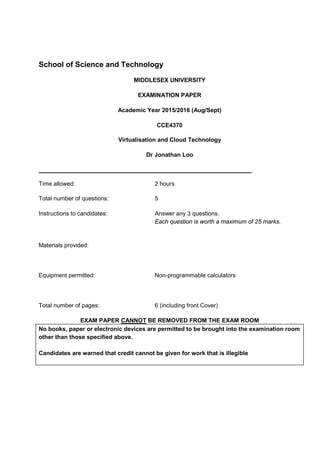
- 1. School of Science and Technology MIDDLESEX UNIVERSITY EXAMINATION PAPER Academic Year 2015/2016 (Aug/Sept) CCE4370 Virtualisation and Cloud Technology Dr Jonathan Loo Time allowed: 2 hours Total number of questions: 5 Instructions to candidates: Answer any 3 questions. Each question is worth a maximum of 25 marks. Materials provided: Equipment permitted: Non-programmable calculators Total number of pages: 6 (including front Cover) EXAM PAPER CANNOT BE REMOVED FROM THE EXAM ROOM No books, paper or electronic devices are permitted to be brought into the examination room other than those specified above. Candidates are warned that credit cannot be given for work that is illegible
- 2. Question 1 An increasing number of organisations in industry and business are now adopting cloud systems. Answer the following questions regarding cloud computing: a) List the main characteristics of cloud computing systems. [5 marks] b) Discuss different ways for cloud service providers to maximise their revenues. [5 marks] c) Characterise the following three cloud computing models: i) Describe Infrastructure as a Service (IaaS). [5 marks] ii) Describe Platform as a Service (PaaS). [5 marks] iii) Describe Software as a Service (SaaS). [5 marks]
- 3. Question 2 a) Define how system availability is measured. [5 marks] b) Consider a computer cluster that has little availability support. Upon a node failure, the following sequence of events takes place: • Step 1: The entire system is shut down and powered off. • Step 2: The faulty node is replaced if the failure is in hardware. • Step 3: The system is powered on and rebooted. • Step 4: The user application is reloaded and rerun from the start. c) Assume one of the cluster nodes fails every 100 hours. Other parts of the cluster never fail. Steps 1 through 3 take two hours. On average, the mean time for step 4 is two hours. What is the availability of the cluster? What is the yearly failure cost if each one-hour downtime costs £2000? [10 marks] d) Following Part (b), assume that the cluster now has much increased availability support. Upon a node failure, its workload automatically fails over to other nodes. The failover time is only six minutes. Meanwhile, the cluster has hot swap capability: The faulty node is taken off the cluster, repaired, replugged, and rebooted, and it rejoins the cluster, all without impacting the rest of the cluster. What is the availability of this ideal cluster, and what is the yearly failure cost? [10 marks]
- 4. Question 3 a) Describe CPU virtualisation. [5 marks] b) Hardware-assisted CPU virtualisation is a technique that attempts to simplify virtualisation. i) Describe the fundamental of hardware-assisted CPU virtualisation. [5 marks] ii) Why the hardware-assisted CPU virtualisation is important? [5 marks] iii) What is Intel VT-x technology? Briefly describe the technology. [5 marks] c) Which virtualisation technique is shown in Figure Q3? Explain the operation of such technique. [5 marks] Figure Q3
- 5. Question 4 a) MapReduce is a software framework which supports parallel and distributed computing on large data sets. Explain the following 2 important functions of the MapReduce framework. i) Map function [2.5 marks] ii) Reduce function [2.5 marks] b) Figure Q4 shows an execution of a practical MapReduce programme called WebVisCounter. The program counts the number of times users connect to or visit a given website using a particular operating system (e.g. Windows or Mac). A single line of a typical web server log file is fed into the MapReduce framework, which is shown in the “Line offset” column. Here, you are required to demonstrate your understanding of MapReduce execution by working out the outcome of each task/box shown in Figure Q4 (e.g. MAP1, MAP2, PAR1, PAR2, etc.) where the final outcome should match the expected result at the Output stage. [20 marks] Figure Q4
- 6. Question 5 a) OpenStack cloud platform was built based on the Service-oriented Architecture (SOA). i) Describe the service-oriented architecture (SOA). [5 marks] ii) Explain the operational nature of SOA. [3 marks] b) Describe the Representational State Transfer (REST) architecture. [5 marks] c) With the aid of Figure Q5, discuss the following four important principles of REST architecture. Figure Q5 i) Resource identification through URIs [3 marks] ii) Uniform, Constrained Interface [3 marks] iii) Self-Descriptive Message [3 marks] iv) Stateless interactions [3 marks]
