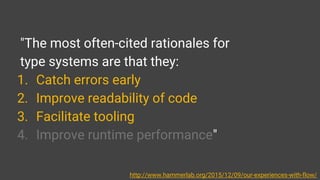
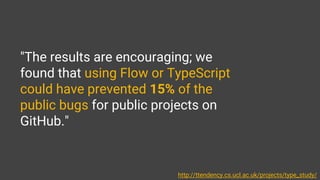
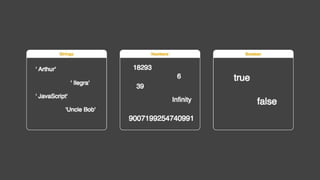
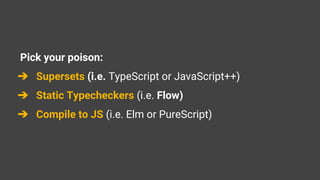
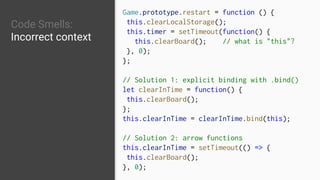
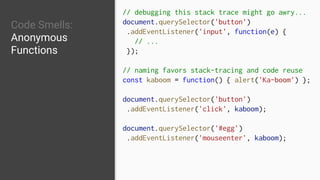
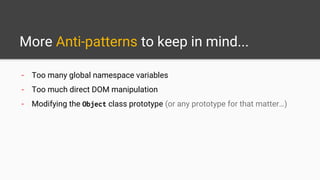
The document is a presentation by Arthur Reis on improving JavaScript code quality through type systems like Flow and TypeScript, emphasizing benefits such as early error detection and improved code readability. It discusses various concepts including type annotation, generics, and code smells, while providing examples of common JavaScript anti-patterns and best practices for clean code. The presentation encourages developers to adopt better coding practices to enhance maintainability and clarity in their projects.







![Type Annotation Basics
let isOpen: boolean = true;
const answer: number = 42; // includes Infinity and NaN
let company: string = 'ilegra';
const hope: null = null;
let theQuestion: void = undefined; // uncompatible with null!
const words: Array<string> = ['I', 'am', 'groot']; // Array<T>
let iCanBeAnything: any = 'es' + 2016; // wildcard, DON'T USE IT
// "Using any is completely unsafe, and should be avoided whenever
possible" - https://flow.org/en/docs/types/any/](https://image.slidesharecdn.com/clean-typechecked-js-tdc1-171121022327/85/Clean-Typechecked-JS-17-320.jpg)
![Object & Function Typing
let proplessObject: Object = {}; // works, but loses typechecking goodness
const identity: { name: string, age: number } = {
name: 'Arthur',
age: 26,
};
let booksPageCounts: { [name: string]: number } = {
Javascript: 999,
JSGoodParts: 100,
};
const calculateArea = (radius: number): number => { // return type is optional
return 3.14 * radius * radius;
};](https://image.slidesharecdn.com/clean-typechecked-js-tdc1-171121022327/85/Clean-Typechecked-JS-18-320.jpg)

![Generics, Maybe and Optionals
type Password<T> = { key: T };
let numberKey: Password<number> = { key: 12345678 };
let stringKey: Password<string> = { key: "shhhhh" };
let arrayKey: Password<Array<number>> = { key: [4, 2] }
var message: ?string = null; // accepts string, null or undefined
function acceptsOptString(value?: string) {} // accepts string or undefined](https://image.slidesharecdn.com/clean-typechecked-js-tdc1-171121022327/85/Clean-Typechecked-JS-20-320.jpg)

![Code Smells:
Non-strict Equality
// All of these evaluate to 'true'
console.log(false == '0');
console.log(null == undefined);
console.log(" trn" == 0);
console.log('' == 0);
console.log(0 == '0');
if ({}) {...}
if ([]) {...}
// Always go for strict equality/inequality
console.log(0 === '0'); // false
// random gotcha: NaN comparison
console.log(NaN == NaN); // false
console.log(NaN === NaN); // false
console.log(isNaN(NaN)); // true, but beware
console.log(NaN != NaN); // true](https://image.slidesharecdn.com/clean-typechecked-js-tdc1-171121022327/85/Clean-Typechecked-JS-26-320.jpg)
![Code Smells:
Variable scoping
and handling
for (var i = 0; i < 10; i++) {
elements[i].onclick = function() {
console.log("This is element #" + i); // 10
};
}
console.log(i); // = 10; i "leaks" out of scope
// solution: let (ES6) is block-level scoped
function () {
var a = 1;
let b = 2;
}
console.log(a); // 1
console.log(b); // undefined
/* const is NOT for scope hoisting: it is for
read-only/immutable values! */](https://image.slidesharecdn.com/clean-typechecked-js-tdc1-171121022327/85/Clean-Typechecked-JS-28-320.jpg)
![JS Clean Code:
Avoid Side Effects
src: github.com/ryanmcdermott/clean-code-javascript
function splitIntoFirstAndLastName(name) {
return name.split(' ');
}
const name = 'Ryan McDermott';
const newName =
splitIntoFirstAndLastName(name);
console.log(name); // 'Ryan McDermott';
console.log(newName); // ['Ryan', 'McDermott'];
// Special care when working with arrays/obj
const addItemToCart = (cart, item) => {
return [...cart, { item, date: Date.now() }];
};](https://image.slidesharecdn.com/clean-typechecked-js-tdc1-171121022327/85/Clean-Typechecked-JS-32-320.jpg)
![JS Clean Code:
Favor Functional
src: github.com/ryanmcdermott/clean-code-javascript
const programmers = [
{name: 'Uncle Bobby', linesOfCode: 500},
{name: 'Gracie Hopper', linesOfCode: 1000}];
// BAD
let totalOutput = 0;
for (let i = 0; i < programmerOutput.length;
i++) {
totalOutput += programmers[i].linesOfCode;
}
// GOOD
const totalOutput = programmers
.map((programmer) => programmer.linesOfCode)
.reduce((acc, linesOfCode) => acc +
linesOfCode, INITIAL_VALUE);](https://image.slidesharecdn.com/clean-typechecked-js-tdc1-171121022327/85/Clean-Typechecked-JS-33-320.jpg)