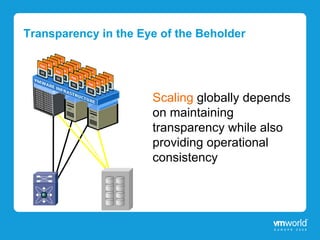
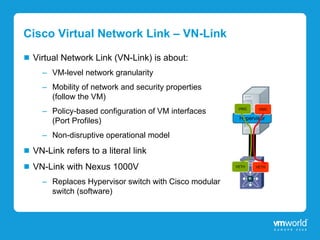
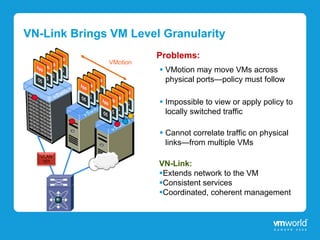
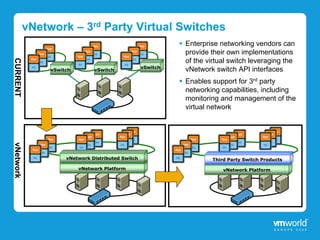
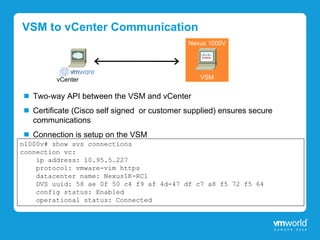
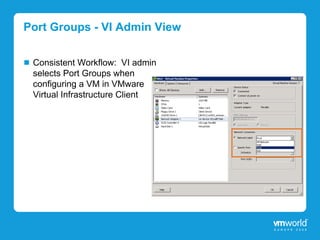
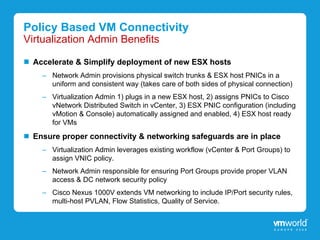
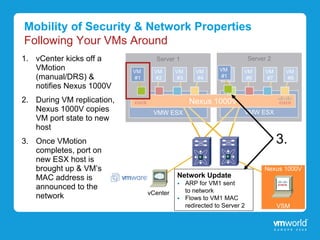
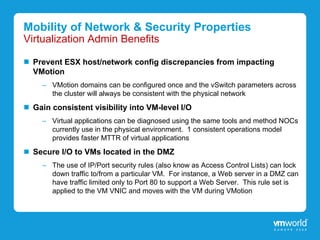
This document discusses the Cisco Nexus 1000V virtual switch, which provides virtual machine-level network visibility and policy enforcement within VMware vSphere environments. The Nexus 1000V replaces the hypervisor virtual switch with Cisco's modular software switch. It extends the network to each virtual machine and allows consistent network and security policies to follow VMs during live migration. The Nexus 1000V integrates tightly with VMware vCenter and leverages Cisco's NX-OS operating system, providing familiar CLI management of the virtual switch.