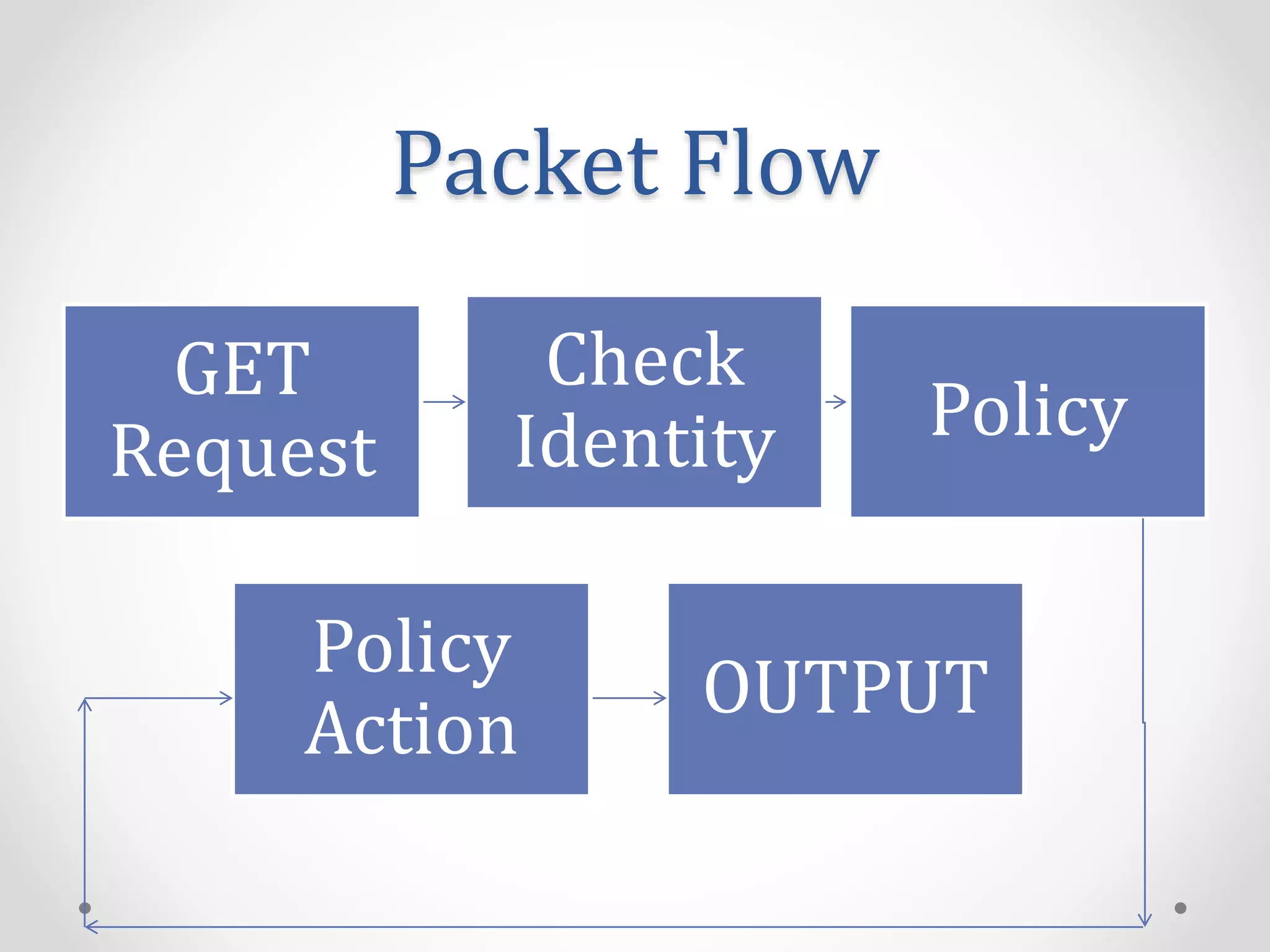
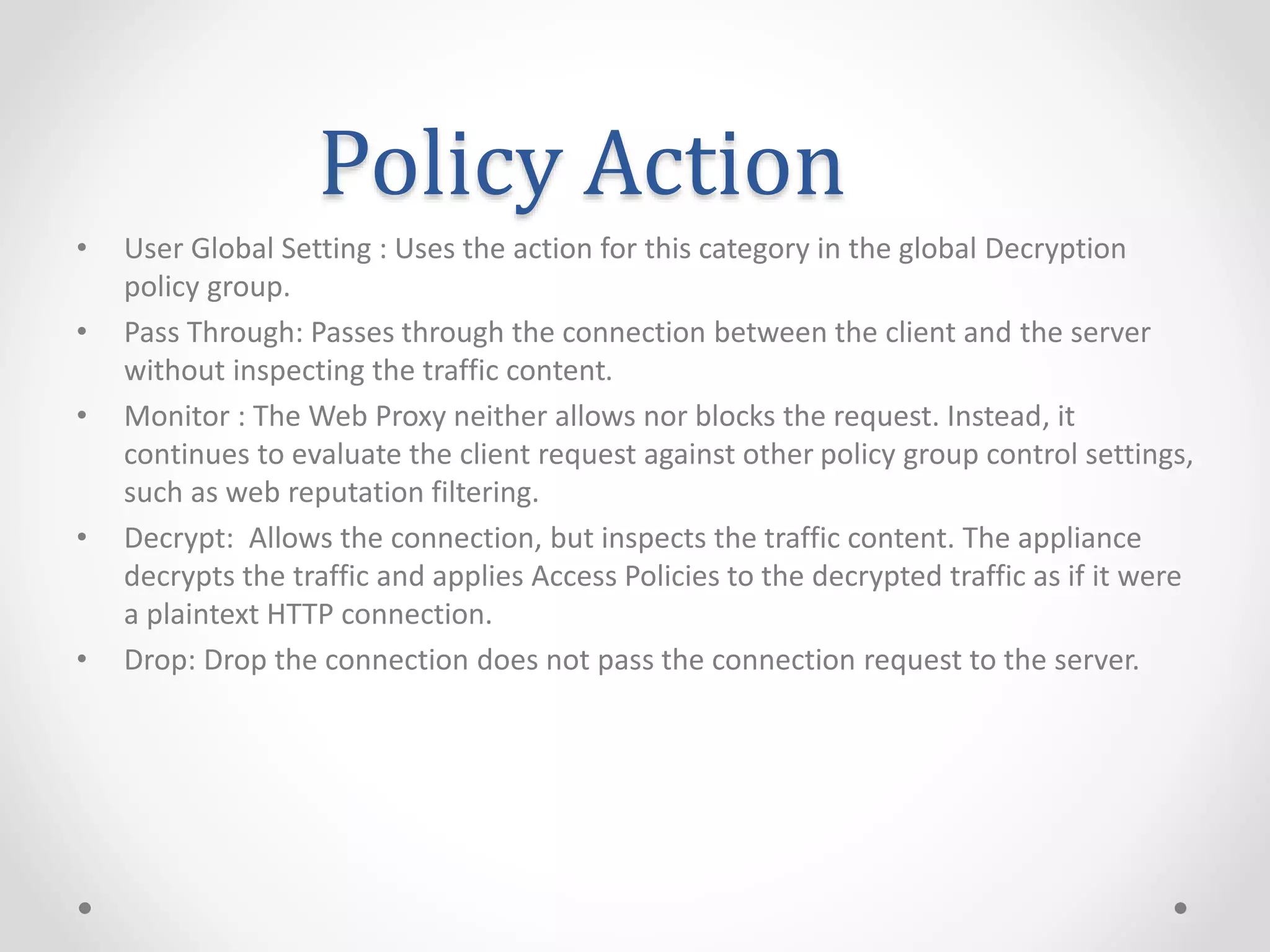
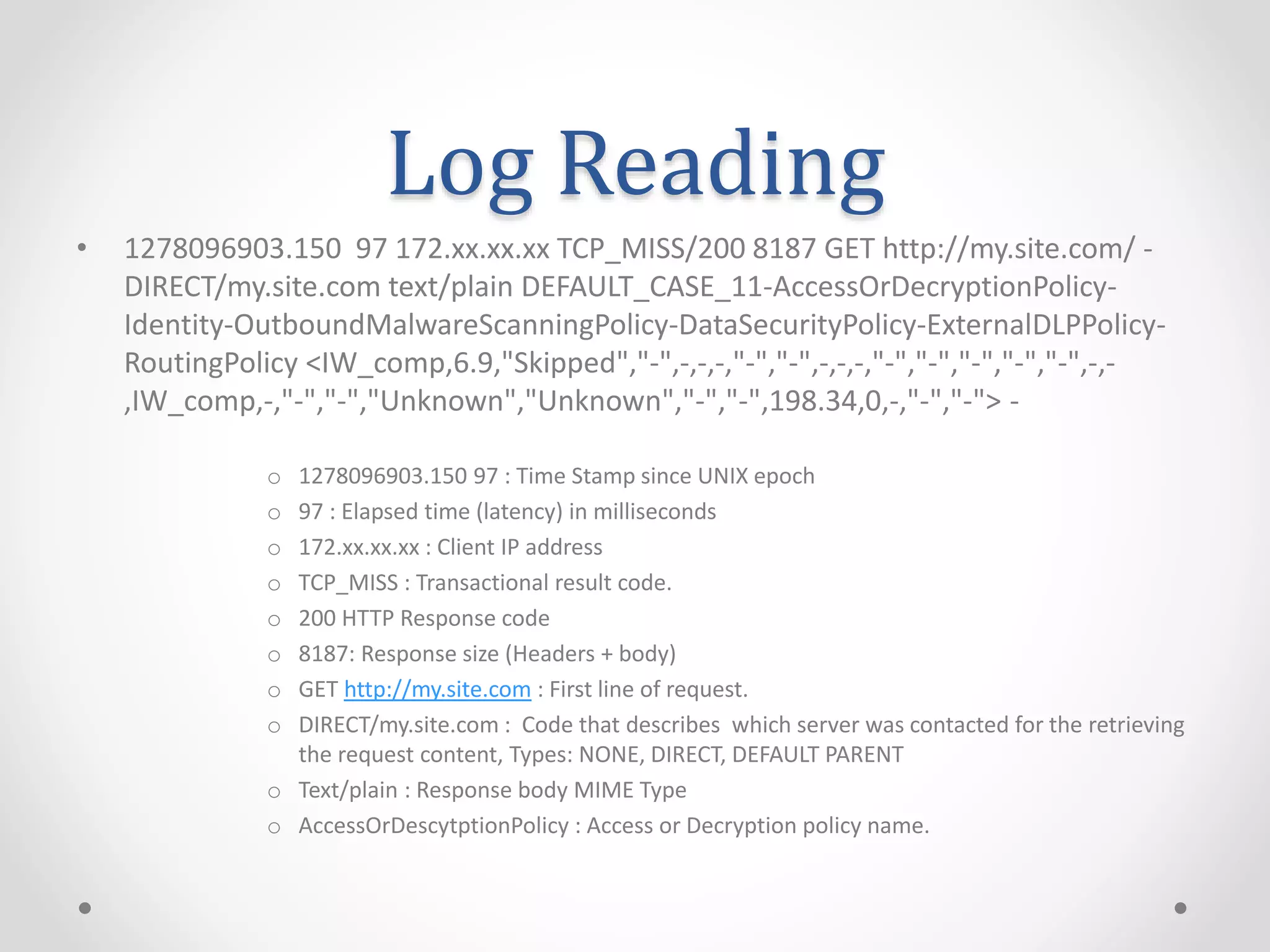
The document provides an overview of Cisco IronPort Web Security Appliance (WSA) device series specifications, including user capacity and architecture based on AsyncOS. It describes various modes of operation such as explicit and transparent modes, alongside packet flow and policy actions like monitoring, decrypting, and dropping connections. Additionally, it includes an example of log reading, detailing the information captured during a web request cycle.