CIM_E_24.2.12
•
0 likes•163 views
Knowledge IT is a software company that offers various SaaS applications for different industries and business needs. Their solutions include products for intellectual property management, HR strategy, CRM, emergency management, and corporate governance. Their applications can be used by individuals, small businesses, or large enterprises. Knowledge IT's document highlights some of their incident management software, including features for adding and viewing incidents, registering incidents, responding to incidents, categorizing incidents in folders, searching incidents, and escalating incidents via email notifications.
Report
Share
Report
Share
Recommended
IRM_E_24.2.12

Knowledge IT offers a variety of software-as-a-service (SaaS) applications to support different business needs across industries. Their applications include modules for intellectual property management, human resources strategy, customer relationship management, emergency management, and corporate governance management. The applications allow users to access only required functions and integrate with third-party software. Knowledge IT's applications are available at different tiers - Professional, Business, Enterprise, and Ultimate - tailored for organizations of various sizes from sole proprietors to large enterprises.
IEM_E_13.2.12

Knowledge IT offers a variety of software-as-a-service (SaaS) applications for different types of organizations and industries. Their applications include modules for intellectual property management, human resources, emergency response, and corporate governance. The applications allow customers to use only the necessary functions and integrate with third-party software. Knowledge IT's applications are available at different tiers to suit organizations of various sizes, from individual users to large enterprises.
IRM_E_25.2.12

Knowledge IT offers a variety of software-as-a-service (SaaS) applications for different business needs. Their applications include modules for intellectual property management, HR strategy, CRM incident management, emergency incidence management, and corporate governance management. They provide applications tailored for professional individual/small business use, business use, enterprise use, and ultimate/large company use. Their applications integrate easily with third-party software and allow customizing the functions used.
HRCM_E_2FEB2012

The document describes Knowledge IT's software-as-a-service (SaaS) applications for various industries. It offers 6 main applications for intellectual property management, HR management, incident response management, and more. It also lists related products including object, review, and schedule managers. The applications are available at different tiers for individual, small/medium business, enterprise, and ultimate users. Features include search, data import/export, and alert/escalation messages.
CGS_E_1.3.12

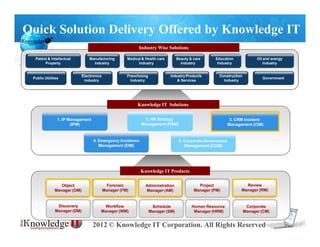
Quick Solution Delivery Offered by Knowledge IT
Knowledge IT offers a variety of software as a service (SaaS) applications to meet different business needs. Their applications include tools for intellectual property management, human resources, customer relationship management, and more. Customers only need to use the specific functions relevant to their business. Knowledge IT also makes it easy to integrate their applications with third party software. They provide applications tailored for individuals, small and medium businesses, large enterprises, and customized solutions for very large companies.
CMS_01.03.12

Quick Solution Delivery Offered by Knowledge IT
Knowledge IT offers a variety of software as a service (SaaS) applications across different industries including manufacturing, healthcare, education, and government. Their applications include intellectual property management, HR strategy management, CRM incident response management, emergency incident management, and corporate governance management. Knowledge IT's products are modular and allow customers to use only the necessary functions, avoiding overuse of applications. Their applications are available at competitive prices without upfront costs and can support organizations of all sizes.
IRM_E_12.03.12

Knowledge IT is a technology solutions provider that offers various SaaS applications for different industries and business needs. Their applications include modules for IP management, HR strategy, CRM, emergency management, and corporate governance. The document highlights Knowledge IT's product categories including professional, business, enterprise, and ultimate applications. It provides examples of how the applications can be used for incident search, registration, follow up, and modification.
IRM_E_14.3.12

The document describes Knowledge IT's incident management software. It offers solutions for various industries and functions for managing incidents from registration through resolution. The software allows users, analysts, and managers to view, assign, update, and close incidents through an online portal. It also enables escalation of incidents by email if response criteria are not met.
Recommended
IRM_E_24.2.12

Knowledge IT offers a variety of software-as-a-service (SaaS) applications to support different business needs across industries. Their applications include modules for intellectual property management, human resources strategy, customer relationship management, emergency management, and corporate governance management. The applications allow users to access only required functions and integrate with third-party software. Knowledge IT's applications are available at different tiers - Professional, Business, Enterprise, and Ultimate - tailored for organizations of various sizes from sole proprietors to large enterprises.
IEM_E_13.2.12

Knowledge IT offers a variety of software-as-a-service (SaaS) applications for different types of organizations and industries. Their applications include modules for intellectual property management, human resources, emergency response, and corporate governance. The applications allow customers to use only the necessary functions and integrate with third-party software. Knowledge IT's applications are available at different tiers to suit organizations of various sizes, from individual users to large enterprises.
IRM_E_25.2.12

Knowledge IT offers a variety of software-as-a-service (SaaS) applications for different business needs. Their applications include modules for intellectual property management, HR strategy, CRM incident management, emergency incidence management, and corporate governance management. They provide applications tailored for professional individual/small business use, business use, enterprise use, and ultimate/large company use. Their applications integrate easily with third-party software and allow customizing the functions used.
HRCM_E_2FEB2012

The document describes Knowledge IT's software-as-a-service (SaaS) applications for various industries. It offers 6 main applications for intellectual property management, HR management, incident response management, and more. It also lists related products including object, review, and schedule managers. The applications are available at different tiers for individual, small/medium business, enterprise, and ultimate users. Features include search, data import/export, and alert/escalation messages.
CGS_E_1.3.12

Quick Solution Delivery Offered by Knowledge IT
Knowledge IT offers a variety of software as a service (SaaS) applications to meet different business needs. Their applications include tools for intellectual property management, human resources, customer relationship management, and more. Customers only need to use the specific functions relevant to their business. Knowledge IT also makes it easy to integrate their applications with third party software. They provide applications tailored for individuals, small and medium businesses, large enterprises, and customized solutions for very large companies.
CMS_01.03.12

Quick Solution Delivery Offered by Knowledge IT
Knowledge IT offers a variety of software as a service (SaaS) applications across different industries including manufacturing, healthcare, education, and government. Their applications include intellectual property management, HR strategy management, CRM incident response management, emergency incident management, and corporate governance management. Knowledge IT's products are modular and allow customers to use only the necessary functions, avoiding overuse of applications. Their applications are available at competitive prices without upfront costs and can support organizations of all sizes.
IRM_E_12.03.12

Knowledge IT is a technology solutions provider that offers various SaaS applications for different industries and business needs. Their applications include modules for IP management, HR strategy, CRM, emergency management, and corporate governance. The document highlights Knowledge IT's product categories including professional, business, enterprise, and ultimate applications. It provides examples of how the applications can be used for incident search, registration, follow up, and modification.
IRM_E_14.3.12

The document describes Knowledge IT's incident management software. It offers solutions for various industries and functions for managing incidents from registration through resolution. The software allows users, analysts, and managers to view, assign, update, and close incidents through an online portal. It also enables escalation of incidents by email if response criteria are not met.
IPM

Knowledge IT offers a variety of software-as-a-service (SaaS) applications to support organizations across different industries. Their applications include tools for human resource strategy management, intellectual property management, incident response management, and corporate governance management. The document discusses Knowledge IT's product offerings and how they are tailored for organizations of different sizes, from individuals and small businesses to large enterprises. Key features include role-based access control, document management and sharing capabilities, and automated email notifications.
IPM_E_10.2.12

1) Knowledge IT offers a variety of software as a service (SaaS) applications for different industries and business needs without requiring upfront investment or installation.
2) Their applications include solutions for intellectual property management, human resources, incident response, and corporate governance that can be used individually or together.
3) Knowledge IT's SaaS model allows customers to pay for only the specific functions they need within each application.
IPM_E_7.4.12

Knowledge IT offers a variety of software-as-a-service (SaaS) applications to support organizations across different industries. Their applications include tools for human resource strategy management, intellectual property management, incident response management, and corporate governance management. The document discusses Knowledge IT's product offerings and how they are tailored for different business sizes, from individual professionals to large enterprises, with customizable access and functionality.
IPM_E_23.4.12

Quick Solution Delivery Offered by Knowledge IT provides concise summaries of its document management solutions in 3 sentences:
Knowledge IT offers a variety of secure document and folder management software as a service applications for organizations of all sizes. The applications allow users to add, modify, search, and comment on documents with role-based access control and automatic email notifications. Customers can integrate these applications and select only the necessary functions to meet their business needs.
IPM_E_17.3.12

Quick Solution Delivery Offered by Knowledge IT provides concise summaries of its industry-specific solutions in 3 sentences:
Knowledge IT offers customized software solutions for various industries including patent/intellectual property, manufacturing, healthcare, beauty/care, education, oil/energy, electronics, franchising, construction, and government. Their solutions include modules for IP management, HR strategy, incident response, and corporate governance management. Knowledge IT's software products are role-based and include object manager, forensic manager, review manager, workflow manager, and other modules to manage projects, schedules, resources, and more.
IRM_E_15.3.12

The document describes Knowledge IT's incident management software solutions. It offers products for professional, business, enterprise, and ultimate users. The software allows users to search, register, and track incidents. Analysts can view assigned incidents, add follow-ups, and modify incidents. Users can view their incident list, follow-ups from analysts, and acknowledge when incidents are resolved. The software also enables copying incidents and on-demand escalation through email.
IRM_E_14.03.2012

The document describes Knowledge IT's incident management software. It offers solutions for various industries and functions for managing incidents from registration through resolution. The software allows users to search, view assigned incidents, add follow-ups, and close incidents. It also enables escalating unresolved incidents through automated emails.
IPM_E_17.3.12

Quick Solution Delivery Offered by Knowledge IT provides concise summaries of its industry-specific solutions in 3 sentences:
Knowledge IT offers customized software solutions for various industries including patent/intellectual property, manufacturing, healthcare, beauty/care, education, oil/energy, electronics, franchising, construction, and government. Their solutions include applications for IP management, HR strategy, incident response, corporate governance, and customized project, review, workflow, and schedule managers. Knowledge IT's software-as-a-service applications can be tailored to business needs and integrate with third-party software.
IPM_E_3.2.12

The document describes Knowledge IT's solutions and products for intellectual property management. It lists various industry verticals Knowledge IT serves and its key solutions: IP Management, HR Collaborative Management, Incidence Response Management, Incidence & Emergency Management, and Corporate Governance Management. It then lists Knowledge IT's products which include tools like Object Manager, Administration Manager, Review Manager, and Project Manager. The document explains Knowledge IT offers applications tailored for different organization sizes from professional to ultimate. It provides examples of folder registration and access management, annotation/comment features, and escalation emails for document operations.
IRM_E_17.03.2012

The document describes an incident management software solution offered by Knowledge IT Corporation. It includes the following key capabilities:
1. Incident registration, assignment to analysts, and tracking of status and resolution through a web interface.
2. Communication features like follow ups, notifications, and feedback between users and analysts to resolve incidents.
3. Flexible configuration options for organizations of different sizes, including user roles and access privileges.
4. Automated escalation workflows that notify managers when incidents meet defined response time thresholds.
IPM_E_19.3.12

Knowledge IT offers a variety of software-as-a-service (SaaS) applications to support organizations across different industries. Their applications include tools for human resource strategy management, intellectual property management, incident response management, and corporate governance management. The document discusses Knowledge IT's product offerings and how they are tailored for different business sizes, from individual professionals to large enterprises, with customizable access and functionality. Security and access controls allow documents and folders to be viewed according to user privileges.
IPM_E_17.3.12

Quick Solution Delivery Offered by Knowledge IT provides concise summaries of its industry-specific solutions in 3 sentences:
Knowledge IT offers customized software solutions for various industries including patent/intellectual property, manufacturing, healthcare, education, and oil/energy. Their solutions include applications for IP management, HR strategy, incident response, corporate governance, and customized project, review, and workflow managers. Knowledge IT's software-as-a-service applications can be tailored to fit the needs of individual users, small businesses, or large enterprises through access privileges and integrated third-party software.
IRM_E_7.4.12

This document summarizes the incident management software offered by Knowledge IT. The software allows users to register, track, and resolve incidents. Key features include the ability to assign incidents, add follow-ups, notify users of status updates, and copy incidents to reuse resolved issues. The software provides role-based access and integrates with third party tools.
HSM_E_17.3.12

Quick Solution Delivery Offered by Knowledge IT summarizes Knowledge IT's offerings in 3 sentences:
Knowledge IT provides industry-specific software solutions across various industries including manufacturing, healthcare, education, and energy. They offer customizable software products that include modules for functions like IP management, HR strategy, and corporate governance. Customers can choose which modules they need rather than being required to use all functions of an application.
CGM_E_8.2.2012

Knowledge IT is a software company that offers industry-specific solutions including intellectual property management, HR management, and emergency response management. It provides 5 main products: Object Manager, Administration Manager, Review Manager, Schedule Manager, and Corporate Manager. These products each have additional modules like Forensic Manager, Workflow Manager, and Billing Manager. Knowledge IT takes a software-as-a-service approach, allowing customers to use only the necessary functions. It offers 4 types of applications - Professional, Business, Enterprise, and Ultimate - tailored for organizations of different sizes. The document provides examples of login screens, data import/export, and escalation mail views within Knowledge IT's software products.
IRM_E_13.03.2012

Knowledge IT is a company that offers various IT solutions and products for different industries. It provides solutions for intellectual property management, HR strategy, and incident response management. Its products include modules for object management, forensic management, review management, and others. Knowledge IT also offers different types of applications - Professional, Business, Enterprise, and Ultimate - tailored to organizations of different sizes. The document provides details on Knowledge IT's solutions, products, application types and incident management workflow.
IRM_E_1.4.12

This document summarizes the incident management software offered by Knowledge IT. The software allows users to register, track, and resolve incidents. Key features include the ability to assign incidents, add follow-ups, notify users of status updates, and escalate incidents that meet certain criteria. The software provides role-based access and is available in various tiers to suit organizations of different sizes.
CGS_E_1.4.12

Knowledge IT offers a variety of solutions and products for different industries including patent & intellectual property, manufacturing, medical & health care, beauty & care, education, oil and energy, electronics, franchising, construction, and government. Their solutions include HR strategy management, intellectual property management, incident response management, and corporate governance management. Their products include object manager, forensic manager, review manager, workflow manager, human resource manager, administration manager, project manager, discovery manager, and schedule manager. Knowledge IT provides applications tailored to professional, business, enterprise, and ultimate users with flexible integration and customization options.
IRM_E_17.3.12

Quick Solution Delivery Offered by Knowledge IT provides industry-specific solutions for patent/intellectual property, manufacturing, healthcare, beauty/care, education, oil/energy, and other industries. It offers 4 types of applications - Professional, Business, Enterprise, and Ultimate - tailored to organizations of different sizes. Key features include incident management, folder organization, user login and access controls, and notification escalation.
HSM_E_17.3.12

Quick Solution Delivery Offered by Knowledge IT summarizes Knowledge IT's offerings in 3 sentences:
Knowledge IT provides industry-specific software solutions across various industries including manufacturing, healthcare, education, and energy. They offer 4 types of applications - Professional, Business, Enterprise, and Ultimate - tailored to business needs from individual use to large enterprises. Knowledge IT's products include features like IP management, HR strategy management, incidence response management, and more that can be customized and integrated with third party software.
IRM_E_13.03.12

The document describes an incident management system where users can register incidents, help desk managers are notified and assign incidents to analysts, analysts can add follow ups, users can see follow ups and provide feedback, and incidents can be modified, copied or escalated through the workflow.
IEM_E_3.3.12

The document describes Knowledge IT's products and services for different types of organizations. It includes descriptions of 4 types of applications suited for different user sizes: Professional for 1-5 users, Business for 2-100 users, Enterprise for 50-1000 users, and Ultimate for 100s to 1000s of users. It also provides overviews of various Knowledge IT products that address areas like incidence response management, HR collaborative management, and corporate governance management. Screenshots demonstrate features for incidence registration, annotation, search, and escalation.
More Related Content
What's hot
IPM

Knowledge IT offers a variety of software-as-a-service (SaaS) applications to support organizations across different industries. Their applications include tools for human resource strategy management, intellectual property management, incident response management, and corporate governance management. The document discusses Knowledge IT's product offerings and how they are tailored for organizations of different sizes, from individuals and small businesses to large enterprises. Key features include role-based access control, document management and sharing capabilities, and automated email notifications.
IPM_E_10.2.12

1) Knowledge IT offers a variety of software as a service (SaaS) applications for different industries and business needs without requiring upfront investment or installation.
2) Their applications include solutions for intellectual property management, human resources, incident response, and corporate governance that can be used individually or together.
3) Knowledge IT's SaaS model allows customers to pay for only the specific functions they need within each application.
IPM_E_7.4.12

Knowledge IT offers a variety of software-as-a-service (SaaS) applications to support organizations across different industries. Their applications include tools for human resource strategy management, intellectual property management, incident response management, and corporate governance management. The document discusses Knowledge IT's product offerings and how they are tailored for different business sizes, from individual professionals to large enterprises, with customizable access and functionality.
IPM_E_23.4.12

Quick Solution Delivery Offered by Knowledge IT provides concise summaries of its document management solutions in 3 sentences:
Knowledge IT offers a variety of secure document and folder management software as a service applications for organizations of all sizes. The applications allow users to add, modify, search, and comment on documents with role-based access control and automatic email notifications. Customers can integrate these applications and select only the necessary functions to meet their business needs.
IPM_E_17.3.12

Quick Solution Delivery Offered by Knowledge IT provides concise summaries of its industry-specific solutions in 3 sentences:
Knowledge IT offers customized software solutions for various industries including patent/intellectual property, manufacturing, healthcare, beauty/care, education, oil/energy, electronics, franchising, construction, and government. Their solutions include modules for IP management, HR strategy, incident response, and corporate governance management. Knowledge IT's software products are role-based and include object manager, forensic manager, review manager, workflow manager, and other modules to manage projects, schedules, resources, and more.
IRM_E_15.3.12

The document describes Knowledge IT's incident management software solutions. It offers products for professional, business, enterprise, and ultimate users. The software allows users to search, register, and track incidents. Analysts can view assigned incidents, add follow-ups, and modify incidents. Users can view their incident list, follow-ups from analysts, and acknowledge when incidents are resolved. The software also enables copying incidents and on-demand escalation through email.
IRM_E_14.03.2012

The document describes Knowledge IT's incident management software. It offers solutions for various industries and functions for managing incidents from registration through resolution. The software allows users to search, view assigned incidents, add follow-ups, and close incidents. It also enables escalating unresolved incidents through automated emails.
IPM_E_17.3.12

Quick Solution Delivery Offered by Knowledge IT provides concise summaries of its industry-specific solutions in 3 sentences:
Knowledge IT offers customized software solutions for various industries including patent/intellectual property, manufacturing, healthcare, beauty/care, education, oil/energy, electronics, franchising, construction, and government. Their solutions include applications for IP management, HR strategy, incident response, corporate governance, and customized project, review, workflow, and schedule managers. Knowledge IT's software-as-a-service applications can be tailored to business needs and integrate with third-party software.
IPM_E_3.2.12

The document describes Knowledge IT's solutions and products for intellectual property management. It lists various industry verticals Knowledge IT serves and its key solutions: IP Management, HR Collaborative Management, Incidence Response Management, Incidence & Emergency Management, and Corporate Governance Management. It then lists Knowledge IT's products which include tools like Object Manager, Administration Manager, Review Manager, and Project Manager. The document explains Knowledge IT offers applications tailored for different organization sizes from professional to ultimate. It provides examples of folder registration and access management, annotation/comment features, and escalation emails for document operations.
IRM_E_17.03.2012

The document describes an incident management software solution offered by Knowledge IT Corporation. It includes the following key capabilities:
1. Incident registration, assignment to analysts, and tracking of status and resolution through a web interface.
2. Communication features like follow ups, notifications, and feedback between users and analysts to resolve incidents.
3. Flexible configuration options for organizations of different sizes, including user roles and access privileges.
4. Automated escalation workflows that notify managers when incidents meet defined response time thresholds.
IPM_E_19.3.12

Knowledge IT offers a variety of software-as-a-service (SaaS) applications to support organizations across different industries. Their applications include tools for human resource strategy management, intellectual property management, incident response management, and corporate governance management. The document discusses Knowledge IT's product offerings and how they are tailored for different business sizes, from individual professionals to large enterprises, with customizable access and functionality. Security and access controls allow documents and folders to be viewed according to user privileges.
IPM_E_17.3.12

Quick Solution Delivery Offered by Knowledge IT provides concise summaries of its industry-specific solutions in 3 sentences:
Knowledge IT offers customized software solutions for various industries including patent/intellectual property, manufacturing, healthcare, education, and oil/energy. Their solutions include applications for IP management, HR strategy, incident response, corporate governance, and customized project, review, and workflow managers. Knowledge IT's software-as-a-service applications can be tailored to fit the needs of individual users, small businesses, or large enterprises through access privileges and integrated third-party software.
IRM_E_7.4.12

This document summarizes the incident management software offered by Knowledge IT. The software allows users to register, track, and resolve incidents. Key features include the ability to assign incidents, add follow-ups, notify users of status updates, and copy incidents to reuse resolved issues. The software provides role-based access and integrates with third party tools.
HSM_E_17.3.12

Quick Solution Delivery Offered by Knowledge IT summarizes Knowledge IT's offerings in 3 sentences:
Knowledge IT provides industry-specific software solutions across various industries including manufacturing, healthcare, education, and energy. They offer customizable software products that include modules for functions like IP management, HR strategy, and corporate governance. Customers can choose which modules they need rather than being required to use all functions of an application.
CGM_E_8.2.2012

Knowledge IT is a software company that offers industry-specific solutions including intellectual property management, HR management, and emergency response management. It provides 5 main products: Object Manager, Administration Manager, Review Manager, Schedule Manager, and Corporate Manager. These products each have additional modules like Forensic Manager, Workflow Manager, and Billing Manager. Knowledge IT takes a software-as-a-service approach, allowing customers to use only the necessary functions. It offers 4 types of applications - Professional, Business, Enterprise, and Ultimate - tailored for organizations of different sizes. The document provides examples of login screens, data import/export, and escalation mail views within Knowledge IT's software products.
IRM_E_13.03.2012

Knowledge IT is a company that offers various IT solutions and products for different industries. It provides solutions for intellectual property management, HR strategy, and incident response management. Its products include modules for object management, forensic management, review management, and others. Knowledge IT also offers different types of applications - Professional, Business, Enterprise, and Ultimate - tailored to organizations of different sizes. The document provides details on Knowledge IT's solutions, products, application types and incident management workflow.
IRM_E_1.4.12

This document summarizes the incident management software offered by Knowledge IT. The software allows users to register, track, and resolve incidents. Key features include the ability to assign incidents, add follow-ups, notify users of status updates, and escalate incidents that meet certain criteria. The software provides role-based access and is available in various tiers to suit organizations of different sizes.
CGS_E_1.4.12

Knowledge IT offers a variety of solutions and products for different industries including patent & intellectual property, manufacturing, medical & health care, beauty & care, education, oil and energy, electronics, franchising, construction, and government. Their solutions include HR strategy management, intellectual property management, incident response management, and corporate governance management. Their products include object manager, forensic manager, review manager, workflow manager, human resource manager, administration manager, project manager, discovery manager, and schedule manager. Knowledge IT provides applications tailored to professional, business, enterprise, and ultimate users with flexible integration and customization options.
IRM_E_17.3.12

Quick Solution Delivery Offered by Knowledge IT provides industry-specific solutions for patent/intellectual property, manufacturing, healthcare, beauty/care, education, oil/energy, and other industries. It offers 4 types of applications - Professional, Business, Enterprise, and Ultimate - tailored to organizations of different sizes. Key features include incident management, folder organization, user login and access controls, and notification escalation.
HSM_E_17.3.12

Quick Solution Delivery Offered by Knowledge IT summarizes Knowledge IT's offerings in 3 sentences:
Knowledge IT provides industry-specific software solutions across various industries including manufacturing, healthcare, education, and energy. They offer 4 types of applications - Professional, Business, Enterprise, and Ultimate - tailored to business needs from individual use to large enterprises. Knowledge IT's products include features like IP management, HR strategy management, incidence response management, and more that can be customized and integrated with third party software.
What's hot (20)
Viewers also liked
IRM_E_13.03.12

The document describes an incident management system where users can register incidents, help desk managers are notified and assign incidents to analysts, analysts can add follow ups, users can see follow ups and provide feedback, and incidents can be modified, copied or escalated through the workflow.
IEM_E_3.3.12

The document describes Knowledge IT's products and services for different types of organizations. It includes descriptions of 4 types of applications suited for different user sizes: Professional for 1-5 users, Business for 2-100 users, Enterprise for 50-1000 users, and Ultimate for 100s to 1000s of users. It also provides overviews of various Knowledge IT products that address areas like incidence response management, HR collaborative management, and corporate governance management. Screenshots demonstrate features for incidence registration, annotation, search, and escalation.
Viewers also liked (7)
Similar to CIM_E_24.2.12
HSM_E_21.4.12

Quick Solution Delivery Offered by Knowledge IT summarizes Knowledge IT's offerings in 3 sentences:
Knowledge IT provides industry-specific software solutions and products for functions like HR, intellectual property management, and incident response. Their software-as-a-service applications can be used by small businesses, large corporations, and governments and require no upfront installation. Knowledge IT's applications support configurable search forms, data migration management, annotation capabilities, and automated escalation emails.
HSM_E_7.4.12

Quick Solution Delivery Offered by Knowledge IT summarizes Knowledge IT's offerings in 3 sentences:
Knowledge IT provides a variety of industry-specific and functional SaaS solutions to meet different business needs. Their applications include HR strategy, intellectual property, incident response, and corporate governance management and can be customized using only required functions. Knowledge IT aims to offer easy-to-deploy software services at competitive pricing to help small and large businesses improve efficiency and reduce costs.
IRM_E_19.3.12

This document summarizes the incident management software offered by Knowledge IT. The software allows users to register, track, and resolve incidents. Key features include the ability to assign incidents, add follow-ups, view incident history, and integrate with other third-party software. The software is offered in various tiers to suit organizations of different sizes, from individual use to enterprise-level systems managing hundreds of users.
IPM_E_8.2.2012

This document summarizes the services offered by Knowledge IT, including industry-specific solutions and products for intellectual property management, HR management, emergency management, and other functions. It describes Knowledge IT's SaaS application offerings for professional, business, enterprise, and ultimate users. Key capabilities highlighted include document management with folder structure and security, annotation and search features, and automated email notifications.
IPM_E_8.2.2012

Quick Solution delivery offered by Knowledge IT provides industry-specific solutions including patent & intellectual property, manufacturing, medical & health care, beauty & care, education, oil and energy, and government. It offers 5 solutions: IP Management, HR Collaborative Management, Incidence Response Management, Incidence & Emergency Management, and Corporate Governance Management. It also provides various productivity applications that can be customized for professional, business, enterprise, and ultimate users.
IPM_E_8.2.2012

This document discusses Knowledge IT's quick solution delivery offerings across various industries. It provides an overview of 5 solutions - IP Management, HR Collaborative Management, Incidence Response Management, Incidence & Emergency Management, and Corporate Governance Management. It also describes Knowledge IT's product suite which includes tools like Object Manager, Administration Manager, Review Manager, and others. Finally, it discusses Knowledge IT's 4 types of applications - Professional, Business, Enterprise, and Ultimate - which are tailored for customers based on needs and user demand.
HSM_E_23.2.12

Knowledge IT offers a variety of software-as-a-service (SaaS) applications for different industries and business needs. Their applications include tools for intellectual property management, human resources strategy, customer relationship management, emergency incident management, and corporate governance management. The applications are role-based and allow customization so users only access needed functions. Knowledge IT's solutions range from individual professional plans to enterprise-level offerings for large organizations. They allow easy third-party integration and data migration management between different application modules. The platforms also include features for annotations, escalation workflows, and automated email notifications.
HSM_E_19.3.12

Quick Solution Delivery Offered by Knowledge IT summarizes Knowledge IT's offerings in 3 sentences:
Knowledge IT provides a variety of industry-specific and functional SaaS solutions to meet different business needs. Their customizable applications include features for HR management, intellectual property management, incident response management, and corporate governance management. Knowledge IT's solutions are designed to increase effectiveness and reduce expenses for businesses of all sizes.
CGS_E_23.4.12

Knowledge IT offers industry-specific solutions using their SaaS products which only utilize necessary functions. Their applications support various organization sizes from individuals to large corporations. The document describes their 4 types of applications - Professional, Business, Enterprise, and Ultimate - which differ based on needs, users, and control offered. It also outlines some key features including customer search, registration, mail escalation, and follow up functions.
HSM_E_24.2.12

Knowledge IT is a software company that offers various SaaS applications for different industries and business needs. Their applications include solutions for intellectual property management, HR strategy, CRM, emergency management, and corporate governance. They provide customizable applications that allow users to only use necessary functions. Knowledge IT's applications support small businesses and large corporations by increasing effectiveness and reducing expenses. Their applications have different tiers for individual, small business, enterprise, and large company needs.
CGS_E_7.4.12

Knowledge IT offers a variety of software solutions tailored for different industries and business needs. Their products include applications for HR strategy management, intellectual property management, incident response management, and corporate governance management. The document then describes their customizable software products which include object manager, forensic manager, review manager, and others. It explains that their applications are cloud-based and users only access the specific functions they require. Knowledge IT provides solutions for organizations of all sizes, from individuals and small businesses to large enterprises.
Similar to CIM_E_24.2.12 (11)
More from Hemant_Kumar_Setya
HSM_E_1.4.12

Quick Solution Delivery Offered by Knowledge IT
Knowledge IT offers a variety of software-as-a-service (SaaS) applications across multiple industries that provide quick solutions without requiring initial investment or complex installation. Their applications support small and large businesses and can increase effectiveness while reducing expenses. Key features include customizable search forms, data migration management tools, annotation capabilities, and automatic escalation and email notifications.
More from Hemant_Kumar_Setya (18)
Recently uploaded
20240605 QFM017 Machine Intelligence Reading List May 2024

Everything I found interesting about machines behaving intelligently during May 2024
Climate Impact of Software Testing at Nordic Testing Days

My slides at Nordic Testing Days 6.6.2024
Climate impact / sustainability of software testing discussed on the talk. ICT and testing must carry their part of global responsibility to help with the climat warming. We can minimize the carbon footprint but we can also have a carbon handprint, a positive impact on the climate. Quality characteristics can be added with sustainability, and then measured continuously. Test environments can be used less, and in smaller scale and on demand. Test techniques can be used in optimizing or minimizing number of tests. Test automation can be used to speed up testing.
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Discover how MongoDB Atlas and vector search technology can revolutionize your application's search capabilities. This comprehensive presentation covers:
* What is Vector Search?
* Importance and benefits of vector search
* Practical use cases across various industries
* Step-by-step implementation guide
* Live demos with code snippets
* Enhancing LLM capabilities with vector search
* Best practices and optimization strategies
Perfect for developers, AI enthusiasts, and tech leaders. Learn how to leverage MongoDB Atlas to deliver highly relevant, context-aware search results, transforming your data retrieval process. Stay ahead in tech innovation and maximize the potential of your applications.
#MongoDB #VectorSearch #AI #SemanticSearch #TechInnovation #DataScience #LLM #MachineLearning #SearchTechnology
みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...

ここ3000字までしか入らないけどタイトルの方がたくさん文字入ると思います。
20 Comprehensive Checklist of Designing and Developing a Website

Dive into the world of Website Designing and Developing with Pixlogix! Looking to create a stunning online presence? Look no further! Our comprehensive checklist covers everything you need to know to craft a website that stands out. From user-friendly design to seamless functionality, we've got you covered. Don't miss out on this invaluable resource! Check out our checklist now at Pixlogix and start your journey towards a captivating online presence today.
Removing Uninteresting Bytes in Software Fuzzing

Imagine a world where software fuzzing, the process of mutating bytes in test seeds to uncover hidden and erroneous program behaviors, becomes faster and more effective. A lot depends on the initial seeds, which can significantly dictate the trajectory of a fuzzing campaign, particularly in terms of how long it takes to uncover interesting behaviour in your code. We introduce DIAR, a technique designed to speedup fuzzing campaigns by pinpointing and eliminating those uninteresting bytes in the seeds. Picture this: instead of wasting valuable resources on meaningless mutations in large, bloated seeds, DIAR removes the unnecessary bytes, streamlining the entire process.
In this work, we equipped AFL, a popular fuzzer, with DIAR and examined two critical Linux libraries -- Libxml's xmllint, a tool for parsing xml documents, and Binutil's readelf, an essential debugging and security analysis command-line tool used to display detailed information about ELF (Executable and Linkable Format). Our preliminary results show that AFL+DIAR does not only discover new paths more quickly but also achieves higher coverage overall. This work thus showcases how starting with lean and optimized seeds can lead to faster, more comprehensive fuzzing campaigns -- and DIAR helps you find such seeds.
- These are slides of the talk given at IEEE International Conference on Software Testing Verification and Validation Workshop, ICSTW 2022.
UiPath Test Automation using UiPath Test Suite series, part 6

Welcome to UiPath Test Automation using UiPath Test Suite series part 6. In this session, we will cover Test Automation with generative AI and Open AI.
UiPath Test Automation with generative AI and Open AI webinar offers an in-depth exploration of leveraging cutting-edge technologies for test automation within the UiPath platform. Attendees will delve into the integration of generative AI, a test automation solution, with Open AI advanced natural language processing capabilities.
Throughout the session, participants will discover how this synergy empowers testers to automate repetitive tasks, enhance testing accuracy, and expedite the software testing life cycle. Topics covered include the seamless integration process, practical use cases, and the benefits of harnessing AI-driven automation for UiPath testing initiatives. By attending this webinar, testers, and automation professionals can gain valuable insights into harnessing the power of AI to optimize their test automation workflows within the UiPath ecosystem, ultimately driving efficiency and quality in software development processes.
What will you get from this session?
1. Insights into integrating generative AI.
2. Understanding how this integration enhances test automation within the UiPath platform
3. Practical demonstrations
4. Exploration of real-world use cases illustrating the benefits of AI-driven test automation for UiPath
Topics covered:
What is generative AI
Test Automation with generative AI and Open AI.
UiPath integration with generative AI
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Why You Should Replace Windows 11 with Nitrux Linux 3.5.0 for enhanced perfor...

The choice of an operating system plays a pivotal role in shaping our computing experience. For decades, Microsoft's Windows has dominated the market, offering a familiar and widely adopted platform for personal and professional use. However, as technological advancements continue to push the boundaries of innovation, alternative operating systems have emerged, challenging the status quo and offering users a fresh perspective on computing.
One such alternative that has garnered significant attention and acclaim is Nitrux Linux 3.5.0, a sleek, powerful, and user-friendly Linux distribution that promises to redefine the way we interact with our devices. With its focus on performance, security, and customization, Nitrux Linux presents a compelling case for those seeking to break free from the constraints of proprietary software and embrace the freedom and flexibility of open-source computing.
Video Streaming: Then, Now, and in the Future

In his public lecture, Christian Timmerer provides insights into the fascinating history of video streaming, starting from its humble beginnings before YouTube to the groundbreaking technologies that now dominate platforms like Netflix and ORF ON. Timmerer also presents provocative contributions of his own that have significantly influenced the industry. He concludes by looking at future challenges and invites the audience to join in a discussion.
20240607 QFM018 Elixir Reading List May 2024

Everything I found interesting about the Elixir programming ecosystem in May 2024
GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024

Neha Bajwa, Vice President of Product Marketing, Neo4j
Join us as we explore breakthrough innovations enabled by interconnected data and AI. Discover firsthand how organizations use relationships in data to uncover contextual insights and solve our most pressing challenges – from optimizing supply chains, detecting fraud, and improving customer experiences to accelerating drug discoveries.
“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...

“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...Edge AI and Vision Alliance
For the full video of this presentation, please visit: https://www.edge-ai-vision.com/2024/06/building-and-scaling-ai-applications-with-the-nx-ai-manager-a-presentation-from-network-optix/
Robin van Emden, Senior Director of Data Science at Network Optix, presents the “Building and Scaling AI Applications with the Nx AI Manager,” tutorial at the May 2024 Embedded Vision Summit.
In this presentation, van Emden covers the basics of scaling edge AI solutions using the Nx tool kit. He emphasizes the process of developing AI models and deploying them globally. He also showcases the conversion of AI models and the creation of effective edge AI pipelines, with a focus on pre-processing, model conversion, selecting the appropriate inference engine for the target hardware and post-processing.
van Emden shows how Nx can simplify the developer’s life and facilitate a rapid transition from concept to production-ready applications.He provides valuable insights into developing scalable and efficient edge AI solutions, with a strong focus on practical implementation.“I’m still / I’m still / Chaining from the Block”

“An Outlook of the Ongoing and Future Relationship between Blockchain Technologies and Process-aware Information Systems.” Invited talk at the joint workshop on Blockchain for Information Systems (BC4IS) and Blockchain for Trusted Data Sharing (B4TDS), co-located with with the 36th International Conference on Advanced Information Systems Engineering (CAiSE), 3 June 2024, Limassol, Cyprus.
Enchancing adoption of Open Source Libraries. A case study on Albumentations.AI

Enchancing adoption of Open Source Libraries. A case study on Albumentations.AIVladimir Iglovikov, Ph.D.
Presented by Vladimir Iglovikov:
- https://www.linkedin.com/in/iglovikov/
- https://x.com/viglovikov
- https://www.instagram.com/ternaus/
This presentation delves into the journey of Albumentations.ai, a highly successful open-source library for data augmentation.
Created out of a necessity for superior performance in Kaggle competitions, Albumentations has grown to become a widely used tool among data scientists and machine learning practitioners.
This case study covers various aspects, including:
People: The contributors and community that have supported Albumentations.
Metrics: The success indicators such as downloads, daily active users, GitHub stars, and financial contributions.
Challenges: The hurdles in monetizing open-source projects and measuring user engagement.
Development Practices: Best practices for creating, maintaining, and scaling open-source libraries, including code hygiene, CI/CD, and fast iteration.
Community Building: Strategies for making adoption easy, iterating quickly, and fostering a vibrant, engaged community.
Marketing: Both online and offline marketing tactics, focusing on real, impactful interactions and collaborations.
Mental Health: Maintaining balance and not feeling pressured by user demands.
Key insights include the importance of automation, making the adoption process seamless, and leveraging offline interactions for marketing. The presentation also emphasizes the need for continuous small improvements and building a friendly, inclusive community that contributes to the project's growth.
Vladimir Iglovikov brings his extensive experience as a Kaggle Grandmaster, ex-Staff ML Engineer at Lyft, sharing valuable lessons and practical advice for anyone looking to enhance the adoption of their open-source projects.
Explore more about Albumentations and join the community at:
GitHub: https://github.com/albumentations-team/albumentations
Website: https://albumentations.ai/
LinkedIn: https://www.linkedin.com/company/100504475
Twitter: https://x.com/albumentationsMicrosoft - Power Platform_G.Aspiotis.pdf

Revolutionizing Application Development
with AI-powered low-code, presentation by George Aspiotis, Sr. Partner Development Manager, Microsoft
Full-RAG: A modern architecture for hyper-personalization

Mike Del Balso, CEO & Co-Founder at Tecton, presents "Full RAG," a novel approach to AI recommendation systems, aiming to push beyond the limitations of traditional models through a deep integration of contextual insights and real-time data, leveraging the Retrieval-Augmented Generation architecture. This talk will outline Full RAG's potential to significantly enhance personalization, address engineering challenges such as data management and model training, and introduce data enrichment with reranking as a key solution. Attendees will gain crucial insights into the importance of hyperpersonalization in AI, the capabilities of Full RAG for advanced personalization, and strategies for managing complex data integrations for deploying cutting-edge AI solutions.
Uni Systems Copilot event_05062024_C.Vlachos.pdf

Unlocking Productivity: Leveraging the Potential of Copilot in Microsoft 365, a presentation by Christoforos Vlachos, Senior Solutions Manager – Modern Workplace, Uni Systems
Introducing Milvus Lite: Easy-to-Install, Easy-to-Use vector database for you...

Join us to introduce Milvus Lite, a vector database that can run on notebooks and laptops, share the same API with Milvus, and integrate with every popular GenAI framework. This webinar is perfect for developers seeking easy-to-use, well-integrated vector databases for their GenAI apps.
National Security Agency - NSA mobile device best practices

Threats to mobile devices are more prevalent and increasing in scope and complexity. Users of mobile devices desire to take full advantage of the features
available on those devices, but many of the features provide convenience and capability but sacrifice security. This best practices guide outlines steps the users can take to better protect personal devices and information.
Recently uploaded (20)
20240605 QFM017 Machine Intelligence Reading List May 2024

20240605 QFM017 Machine Intelligence Reading List May 2024
Climate Impact of Software Testing at Nordic Testing Days

Climate Impact of Software Testing at Nordic Testing Days
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf
みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...

みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...
20 Comprehensive Checklist of Designing and Developing a Website

20 Comprehensive Checklist of Designing and Developing a Website
UiPath Test Automation using UiPath Test Suite series, part 6

UiPath Test Automation using UiPath Test Suite series, part 6
Why You Should Replace Windows 11 with Nitrux Linux 3.5.0 for enhanced perfor...

Why You Should Replace Windows 11 with Nitrux Linux 3.5.0 for enhanced perfor...
GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024

GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024
“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...

“Building and Scaling AI Applications with the Nx AI Manager,” a Presentation...
Enchancing adoption of Open Source Libraries. A case study on Albumentations.AI

Enchancing adoption of Open Source Libraries. A case study on Albumentations.AI
Full-RAG: A modern architecture for hyper-personalization

Full-RAG: A modern architecture for hyper-personalization
Introducing Milvus Lite: Easy-to-Install, Easy-to-Use vector database for you...

Introducing Milvus Lite: Easy-to-Install, Easy-to-Use vector database for you...
National Security Agency - NSA mobile device best practices

National Security Agency - NSA mobile device best practices
CIM_E_24.2.12
- 1. Quick Solution Delivery Offered by Knowledge IT Industry Wise Solutions Patent & Intellectual Manufacturing Medical & Health care Beauty & care Education Oil and energy Property Industry Industry Industry Industry Industry Electronics Franchising Industry Products Construction Public Utilities Government Industry Industry & Services Industry Knowledge IT Solutions 1. IP Management 2. HR Strategy 3. CRM Incident (IPM) Management (HSM) Management (CIM) 4. Emergency Incidence 5. Corporate Governance Management (EIM) Management (CGM) Knowledge IT Products Object Forensic Administration Project Review Manager (OM) Manager (FM) Manager (AM) Manager (PM) Manager (RM) Discovery Workflow Schedule Human Resource Corporate Manager (DM) Manager (WM) Manager (SM) Manager (HRM) Manager (CM) 2012 © Knowledge IT Corporation. All Rights Reserved
- 2. Pick and Use Functions that you Need With any application, you effectively use only 10% of the application. But with Knowledge IT’s SaaS applications, you use only those functions that you need. The Knowledge IT Products Object Forensic Manager (OM) Manager (FM) Review Workflow Manager (RM) Manager (WM) Project Administration Manager (PM) Manager (AM) Human Resource Discovery (RM) Manager (HRM) Manager (DM) Corporate Schedule Manager (CM) Manager (SM) Easy Third Party Software Integration 2012 © Knowledge IT Corporation. All Rights Reserved
- 3. Knowledge IT’s 4 Types of Application Based on Needs & User Demand Knowledge IT offers a variety of SaaS applications which do not require initial investment and installation effort, by providing easy-to-deploy software services at competitive pricing. The applications supports small businesses and large corporations, contributing to increasing effectiveness and reducing expenses. Professional Business Enterprise Ultimate Individuals・SOHO Small and Medium Small and Medium For large companies Personal Offices enterprises or Enterprises or looking for full control or Small Offices Shop owners Enterprise Subcontractors and autonomy Best for individual Suitable for system ranging Ideal for organizations and Highly specialized set of use and smaller from two to multiple users. businesses with large groups. administration tools in an businesses Data access for packaged Security, access privileges as application is ideal for large groups predetermined privilege based. well as functions can be of people in an organization. This Typical Usage Secure user access. determined by the customer and Ultimate set comes with the freedom Size: 1-5 Users Typical Usage set/added per category of users to build a solution view and dig- Size: 2-100s of Users from Packaged Solution. down feature according to each Typical Usage customer’s need. Role based as well Size: 50-1000s of Users as privilege based access control can be set by the Business and above. Typical Usage Size: 100s – 1000s of Users and above 2012 © Knowledge IT Corporation. All Rights Reserved
- 4. Incident List and Incident Registration By this function you can add, modify or delete the Add Incident from Options are provided to folder/ subfolder here search your incidents You can view all or latest versions of the incidents added Incident Registration 2012 © Knowledge IT Corporation. All Rights Reserved
- 5. Incident Registration Notification Auto mail Notification of Incident added to Analyst Manager 2012 © Knowledge IT Corporation. All Rights Reserved
- 6. Responses to Incident Incident Response Icon Content as the response to the incident 2012 © Knowledge IT Corporation. All Rights Reserved
- 7. Categorizing Incident by Folders Folder Register with security Folder Modify 2012 © Knowledge IT Corporation. All Rights Reserved
- 8. Different Search Criteria Search screen Different Search Forms Search Result 2012 © Knowledge IT Corporation. All Rights Reserved
- 9. Escalation Mail and Views Escalation mail is observed in Review Manager Escalation mails can be viewed by clicking on subject link 2012 © Knowledge IT Corporation. All Rights Reserved