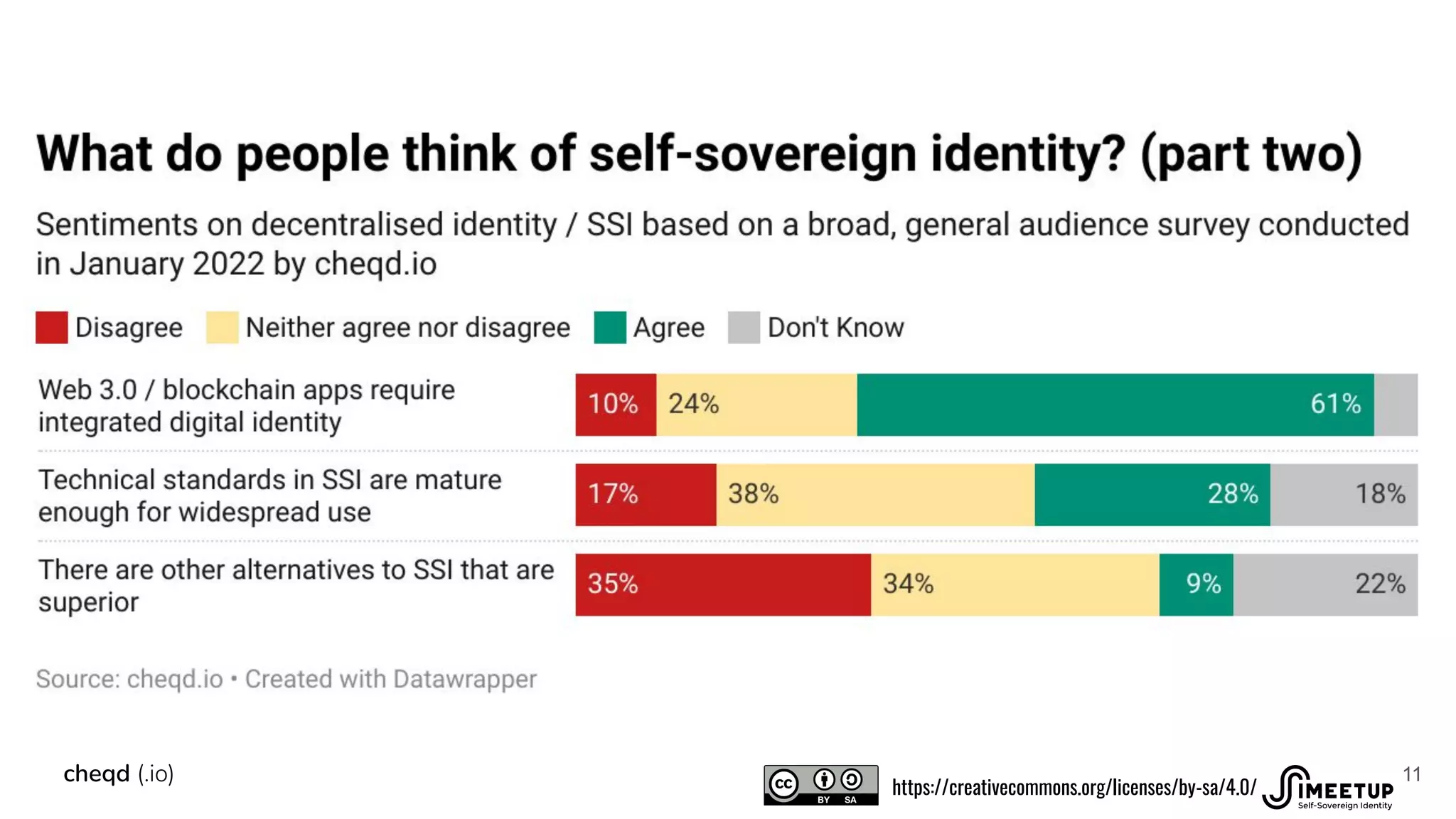
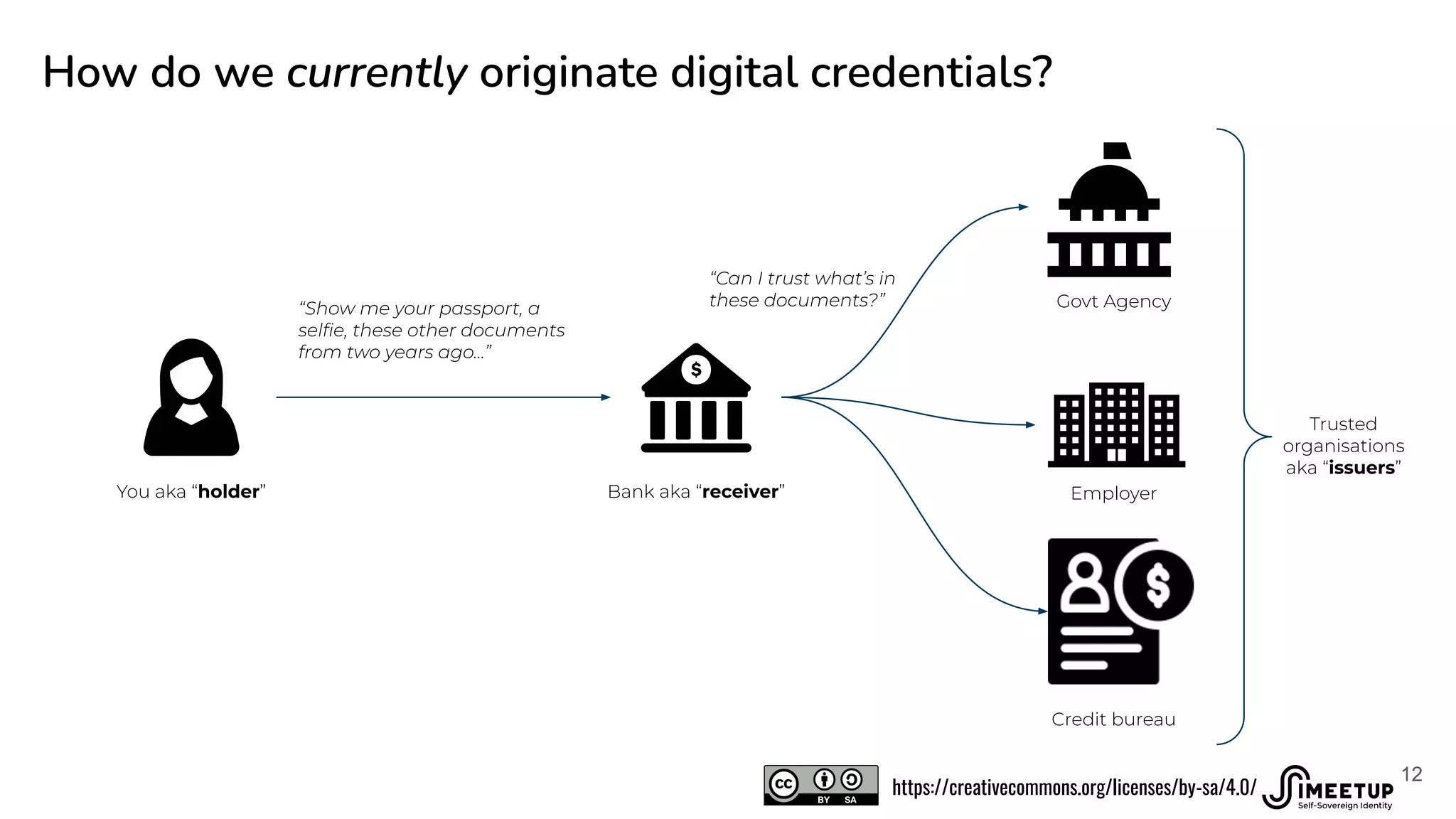
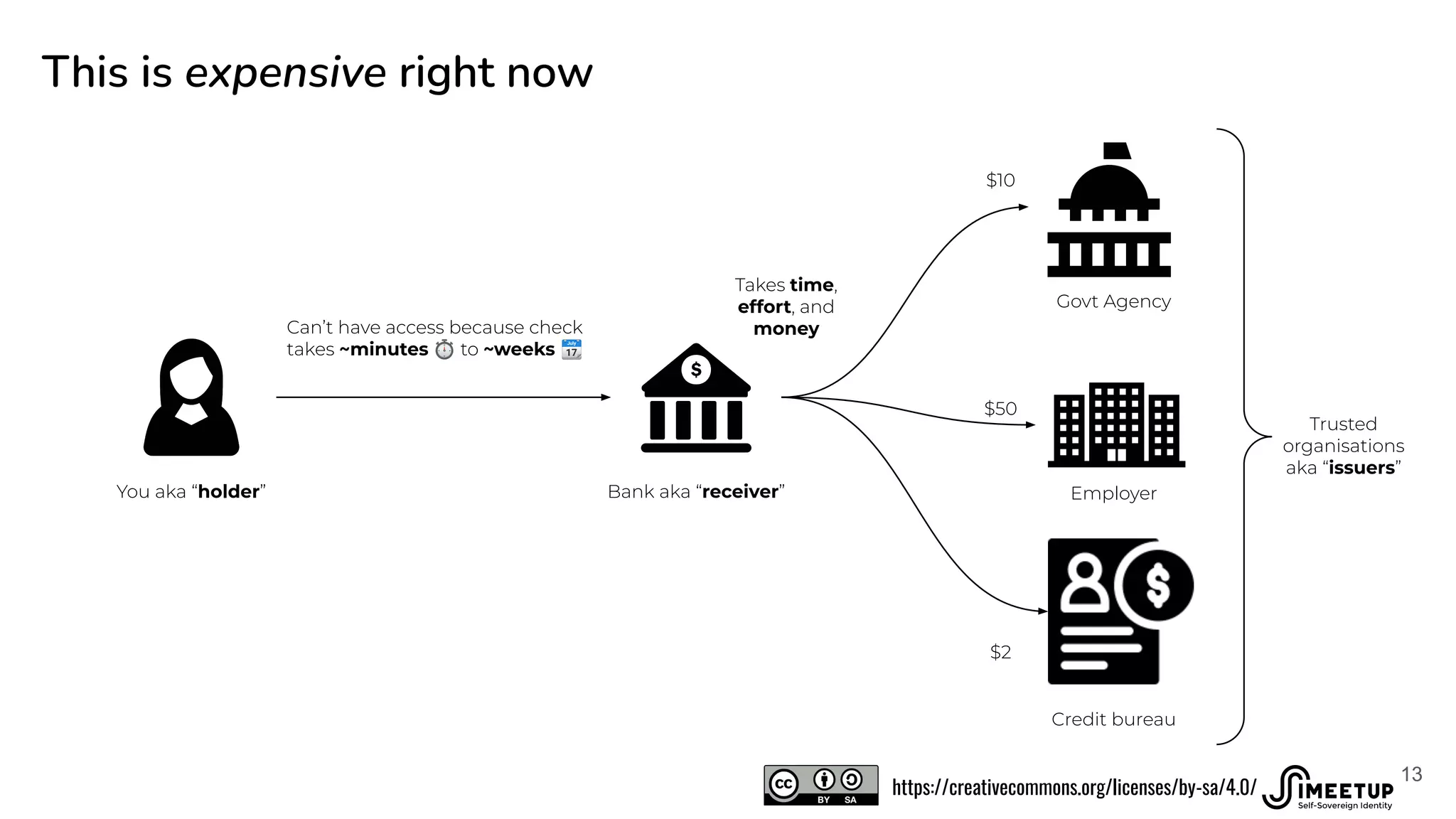
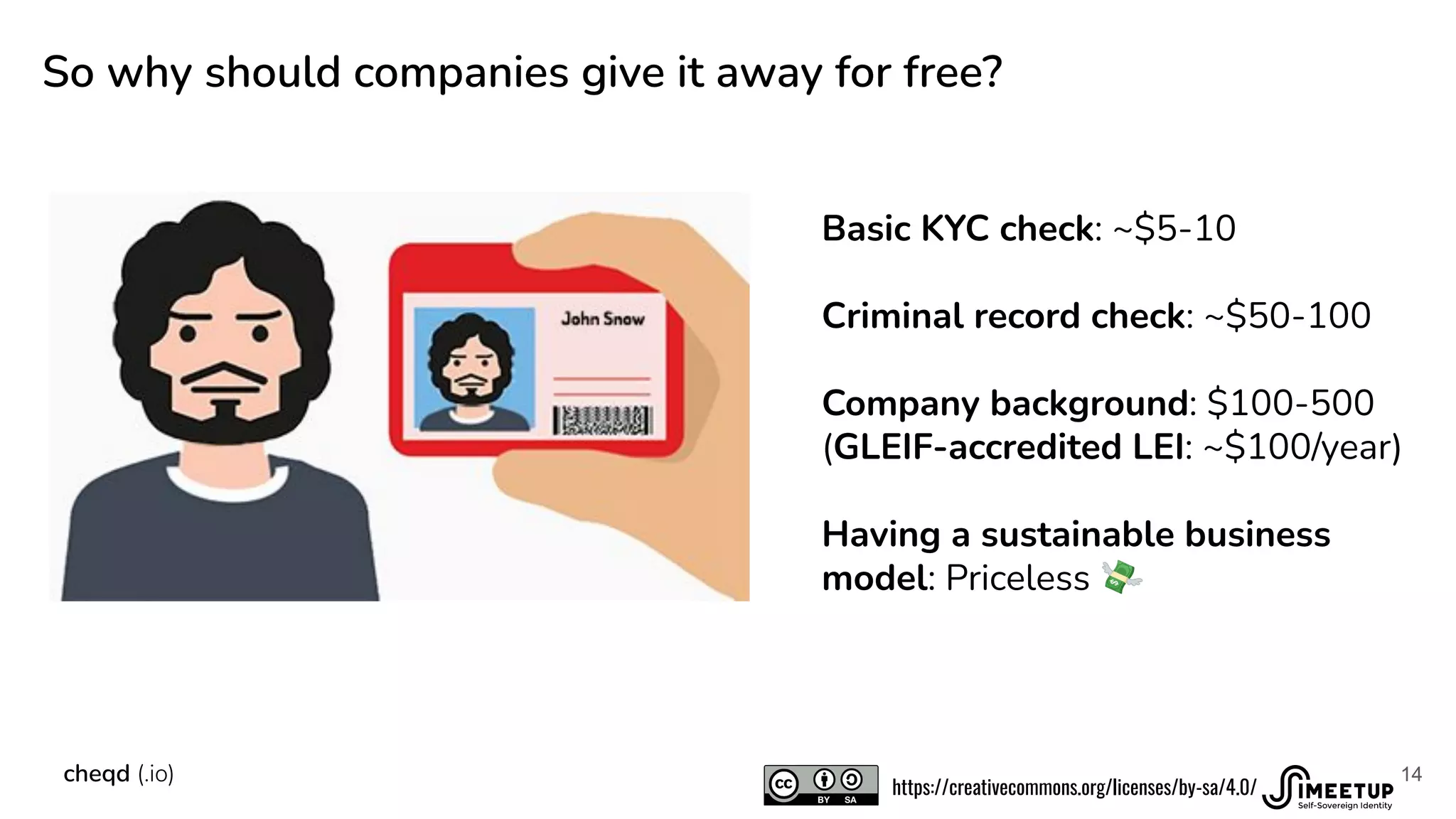
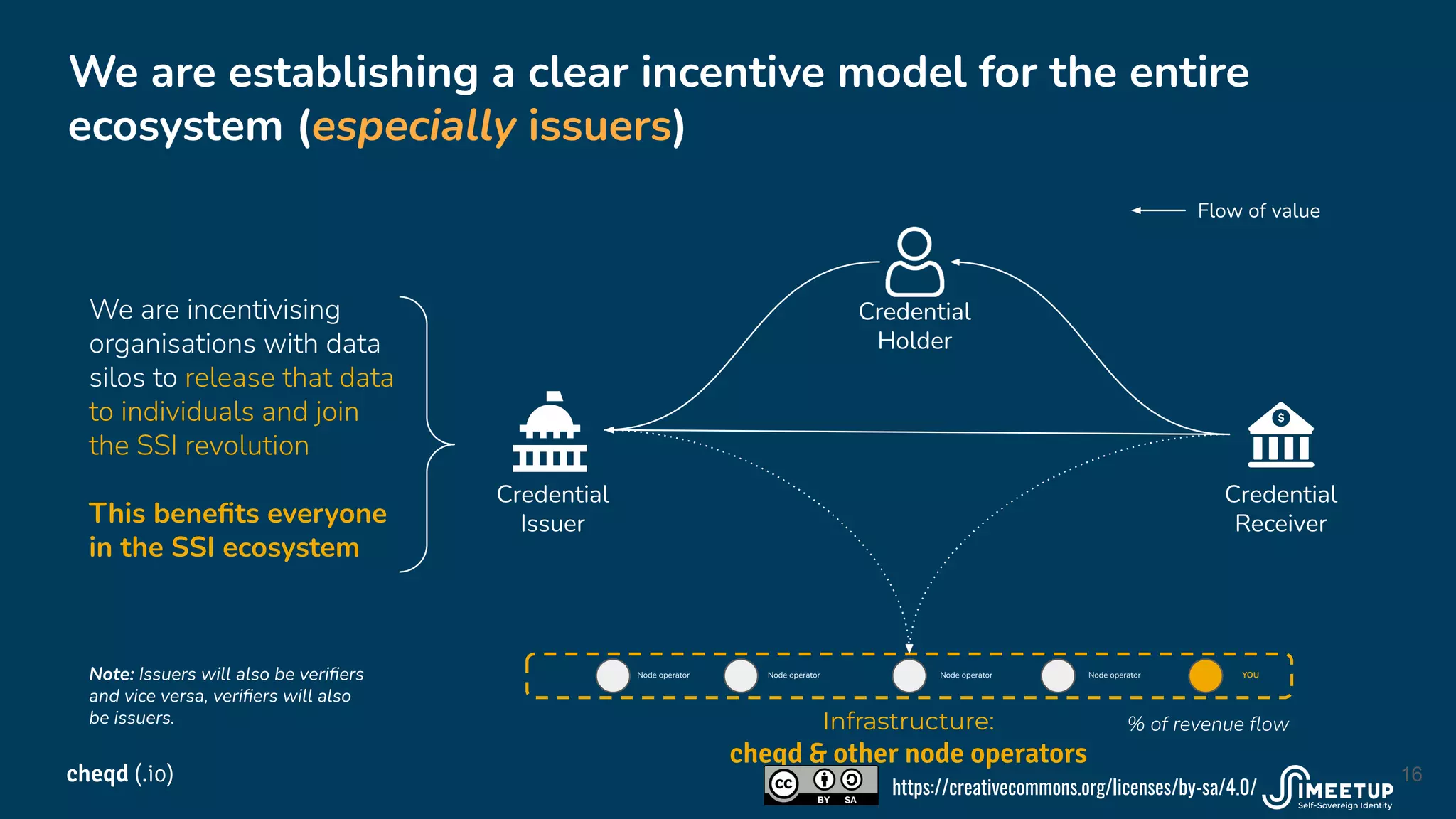
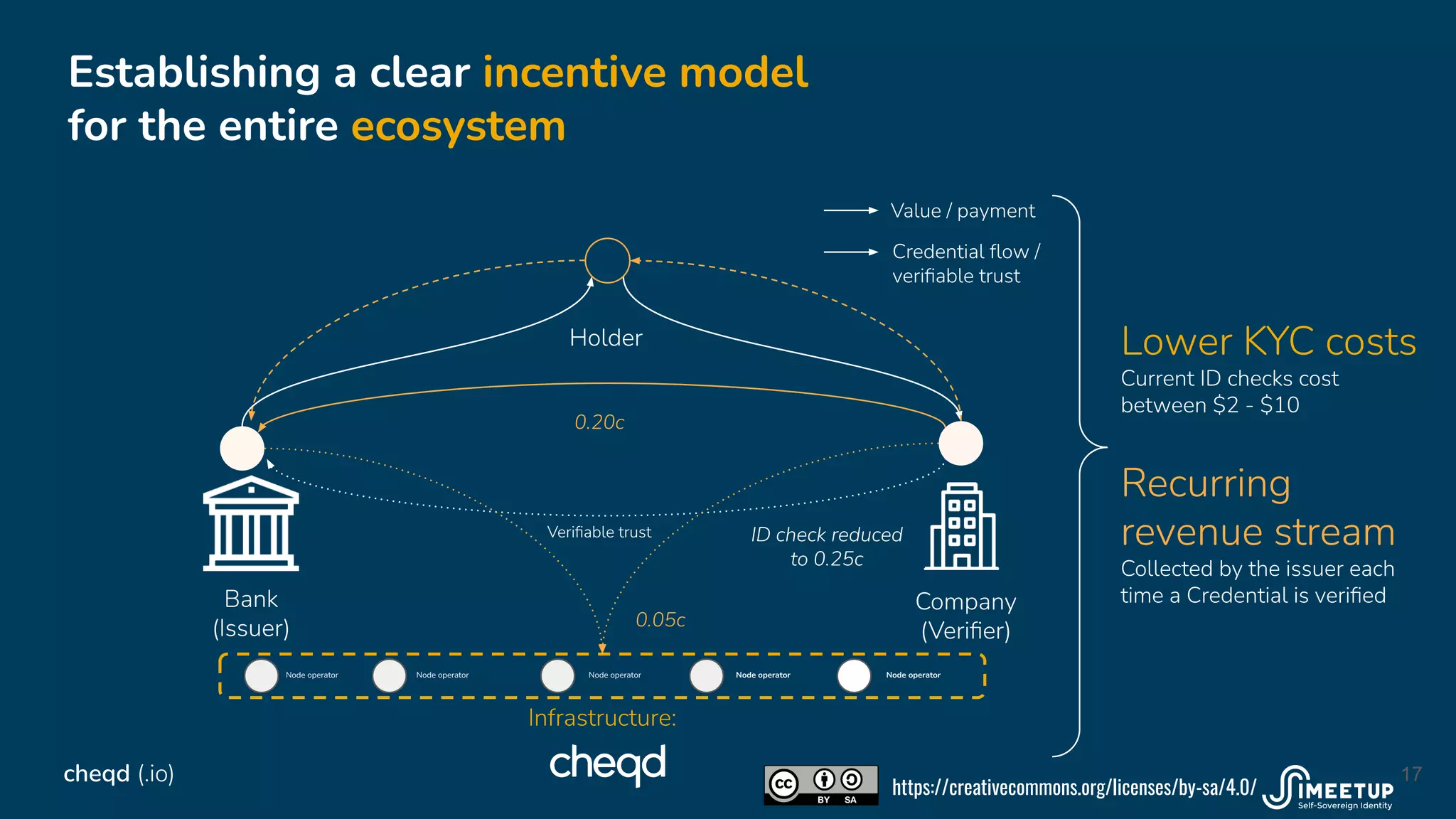
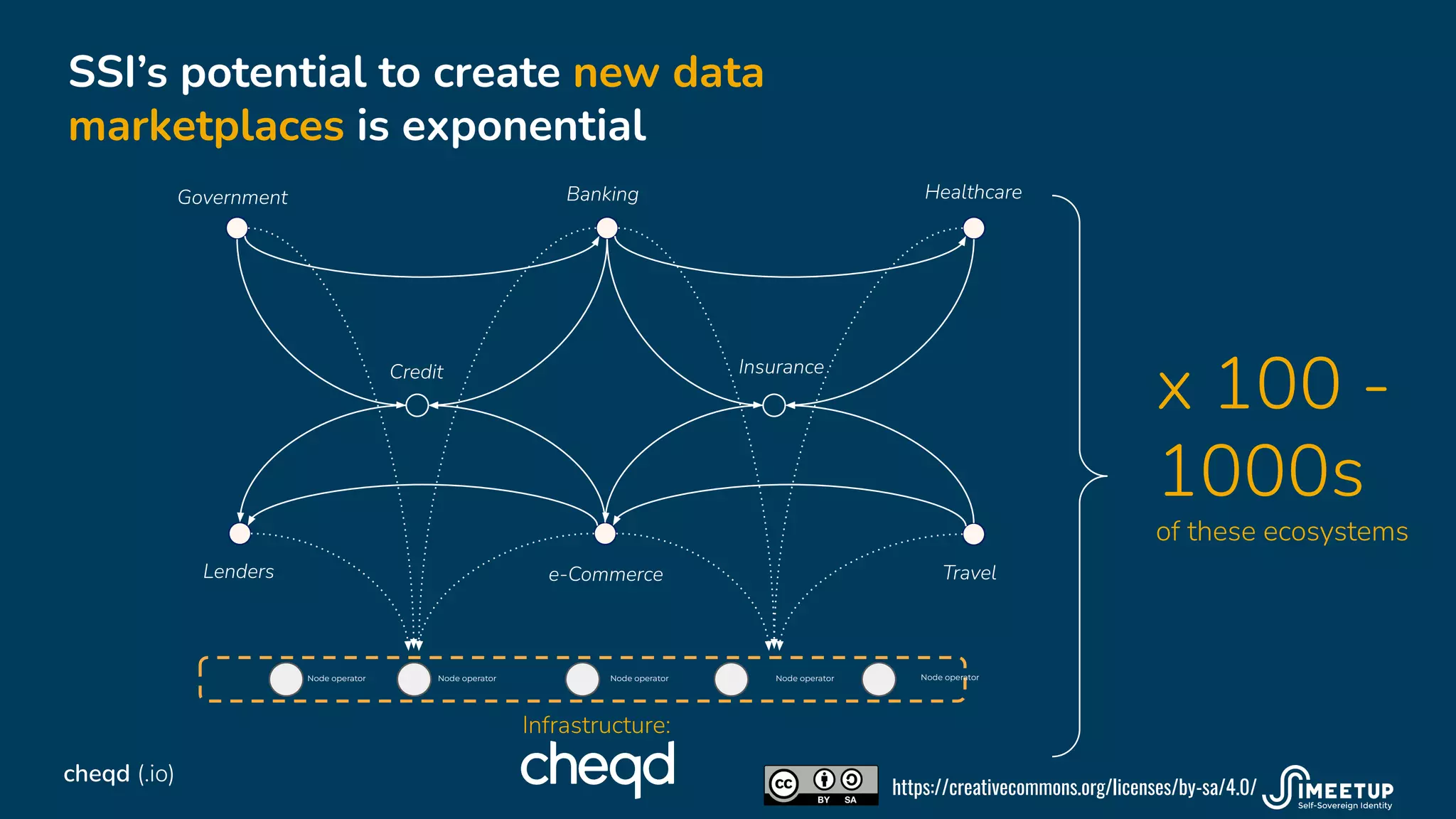
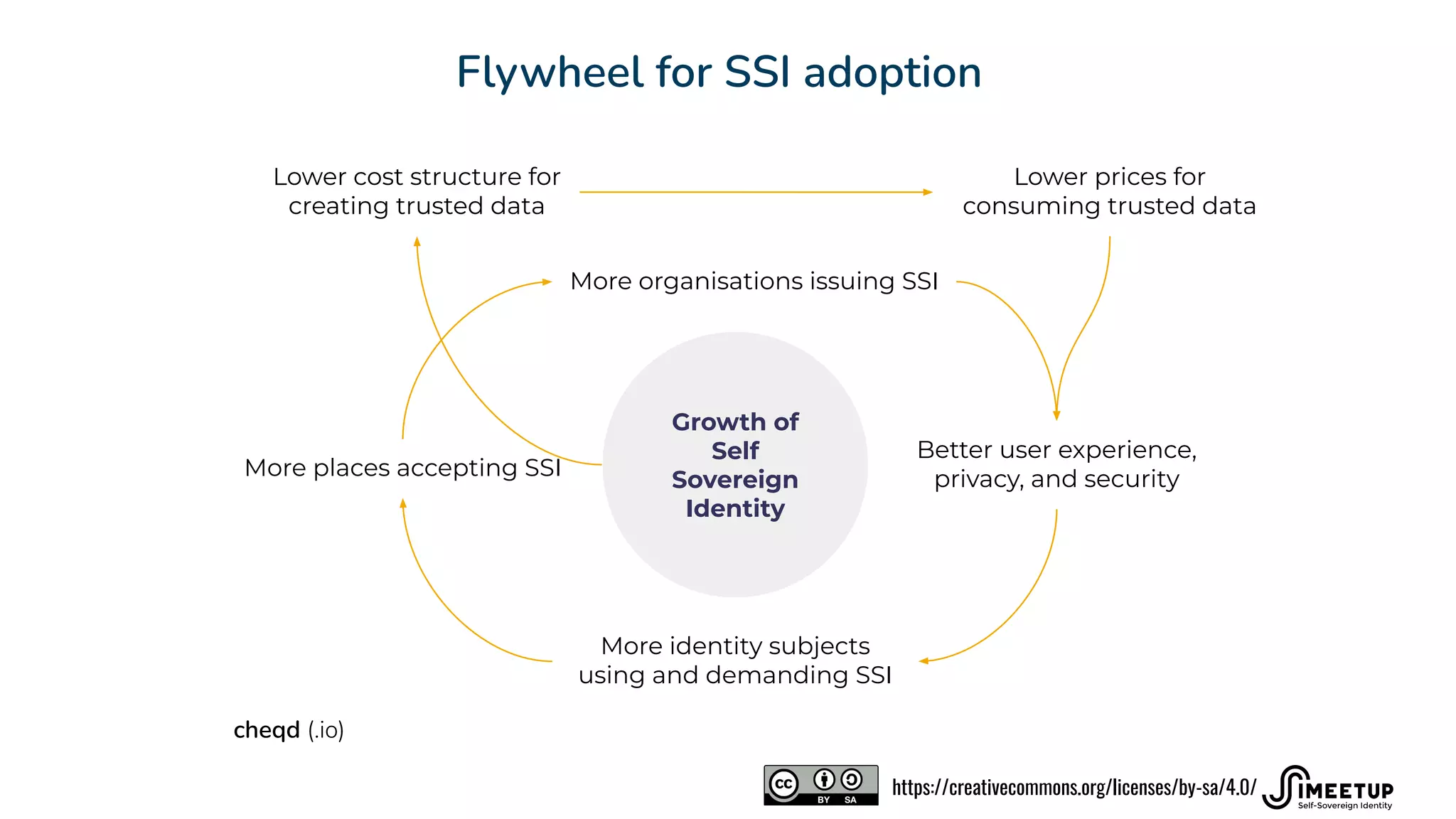
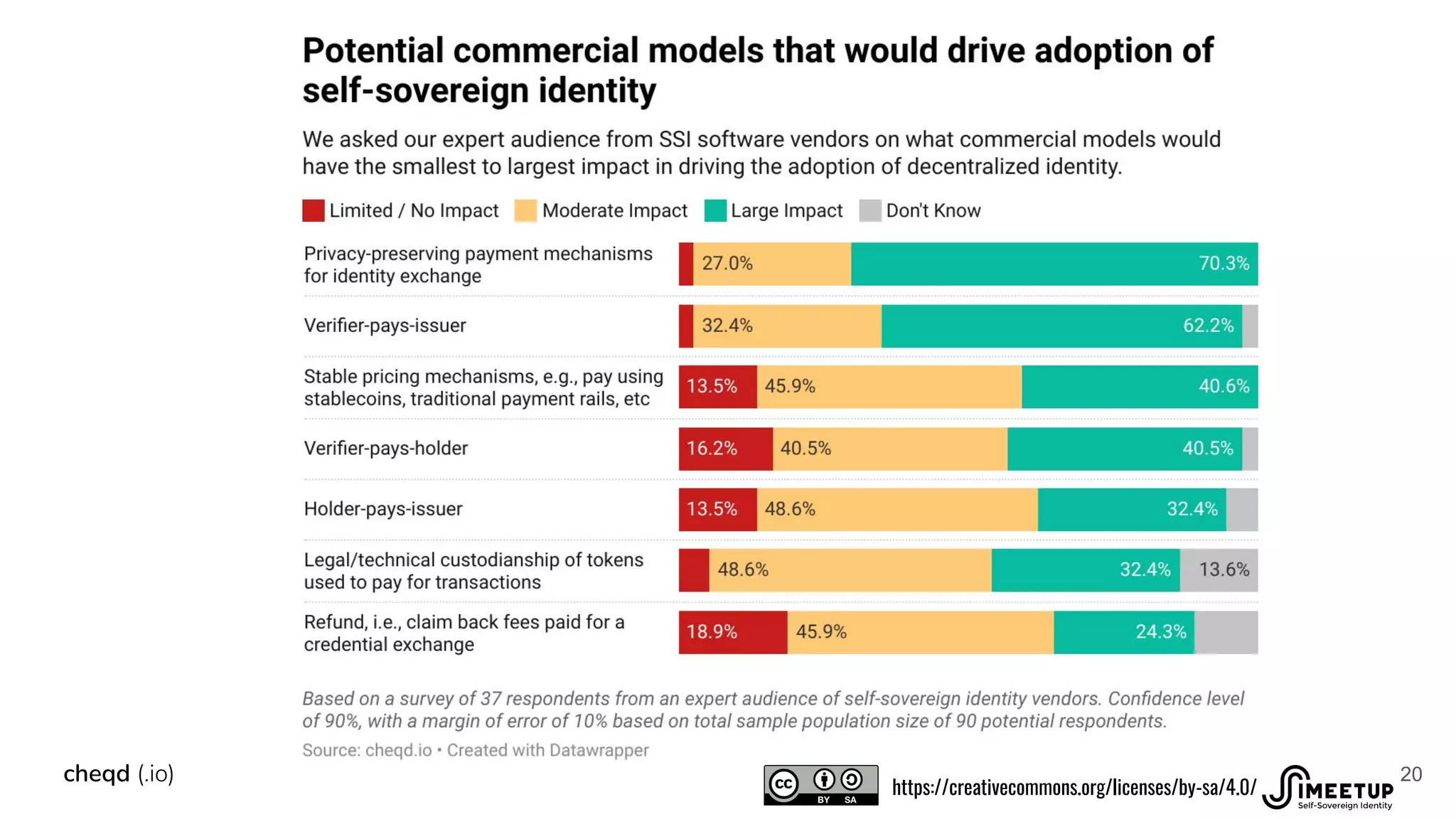
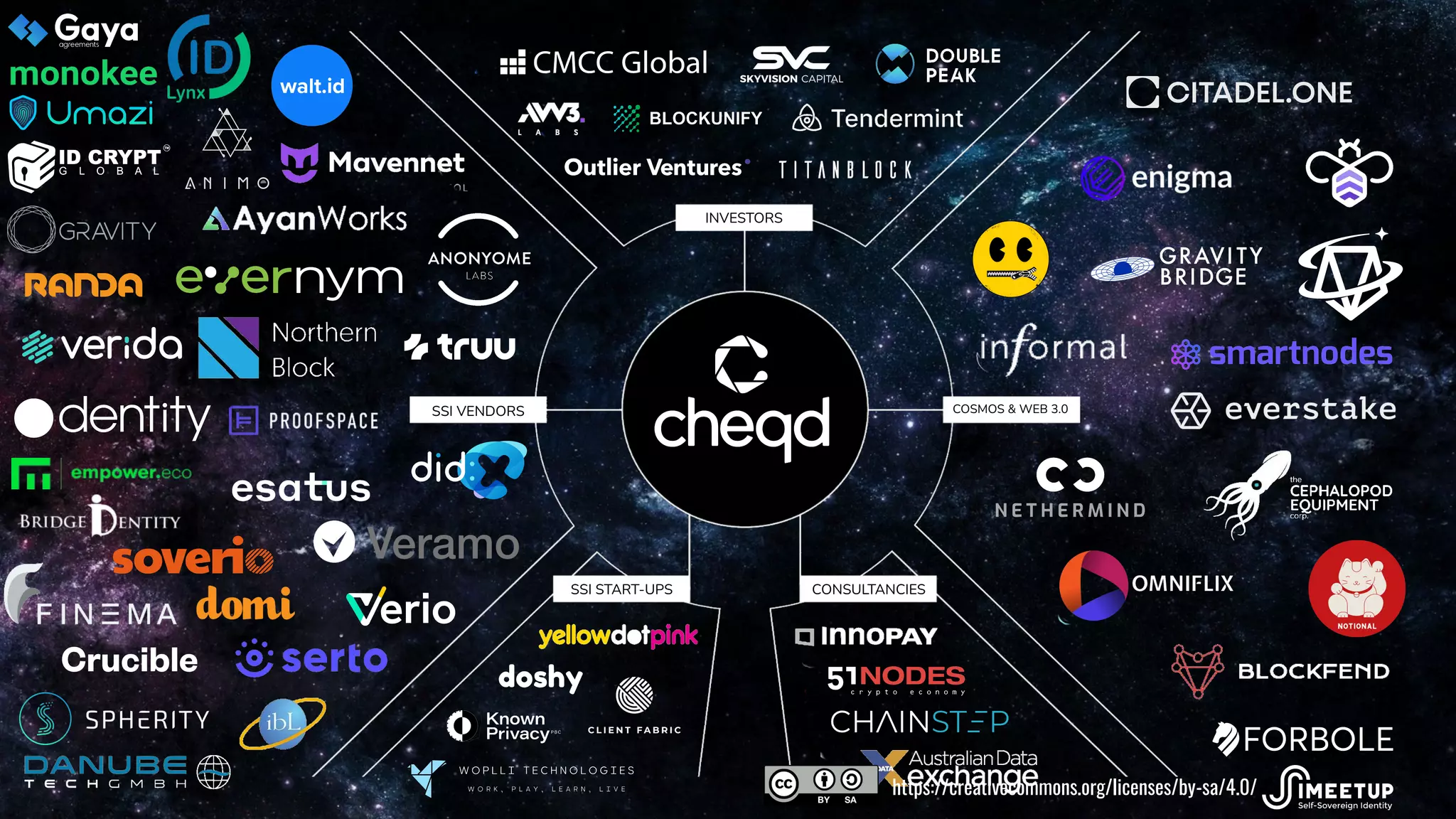
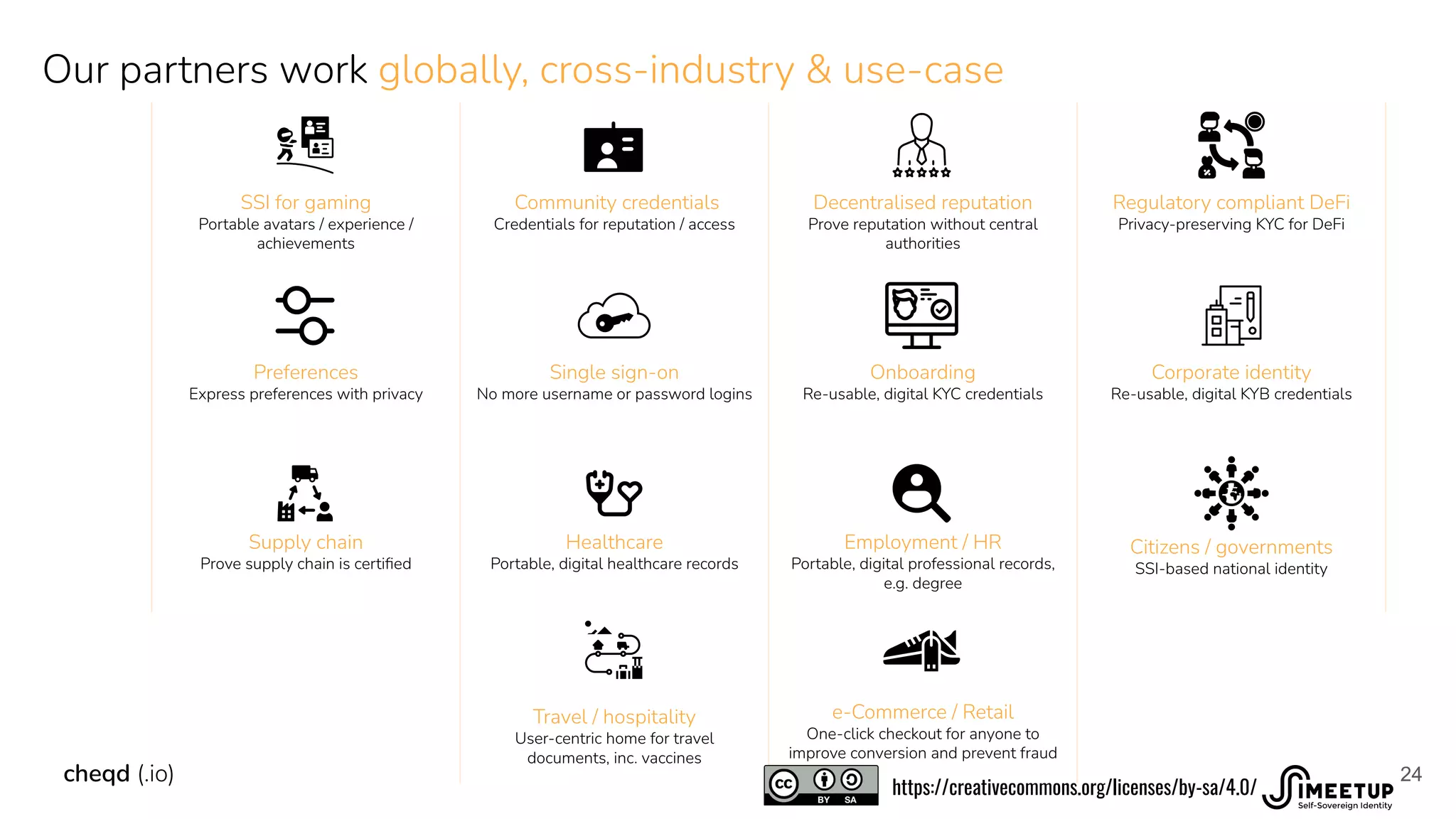
The document discusses the creation of a trusted data economy through Self-Sovereign Identity (SSI) and digital credentials. It emphasizes empowering global SSI communities, lowering verification costs, and incentivizing data-sharing among organizations to enhance user privacy and ease of access. Cheqd aims to revolutionize the digital credential ecosystem by establishing a sustainable business model and creating better user experiences across various industries.