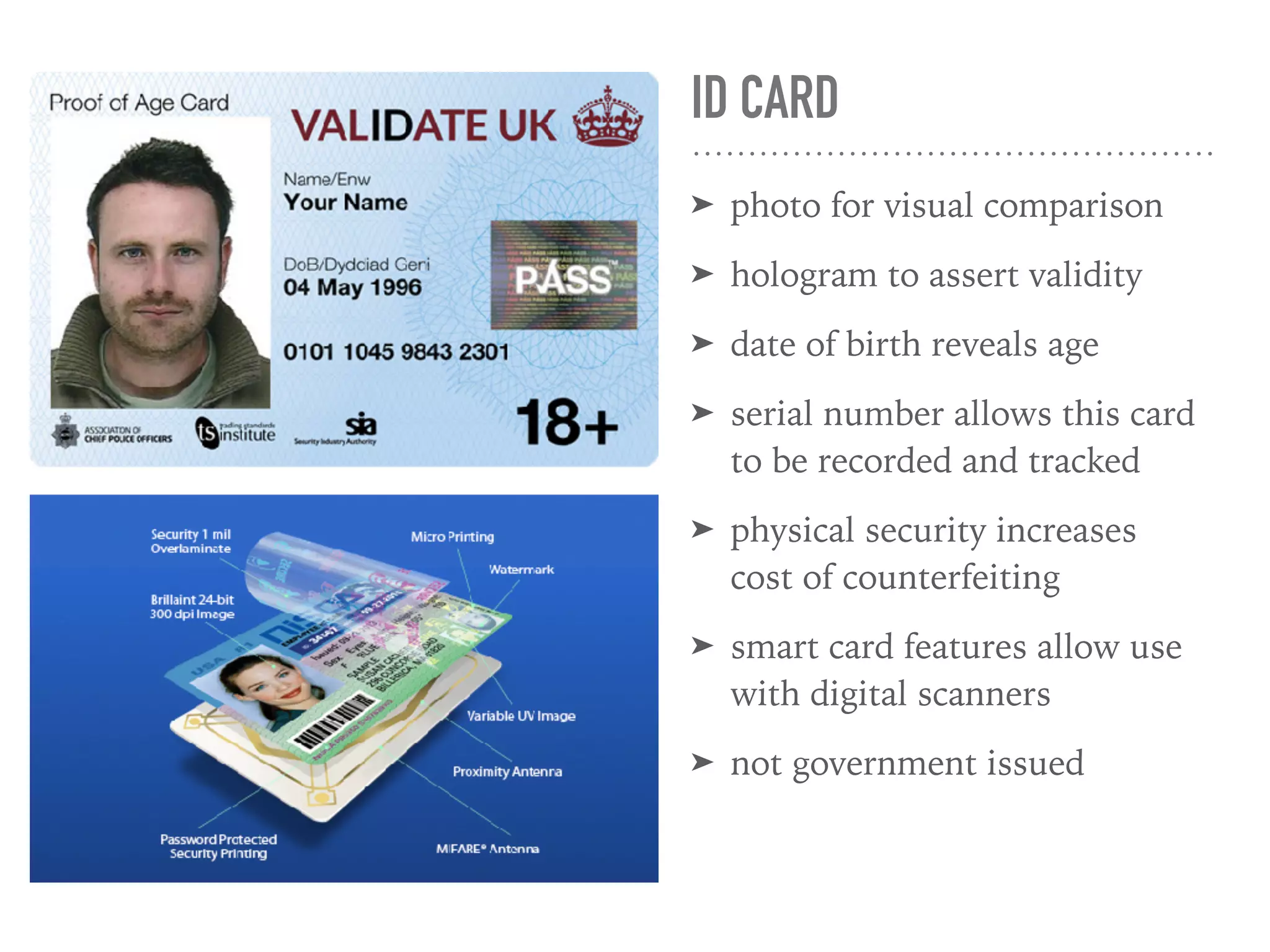
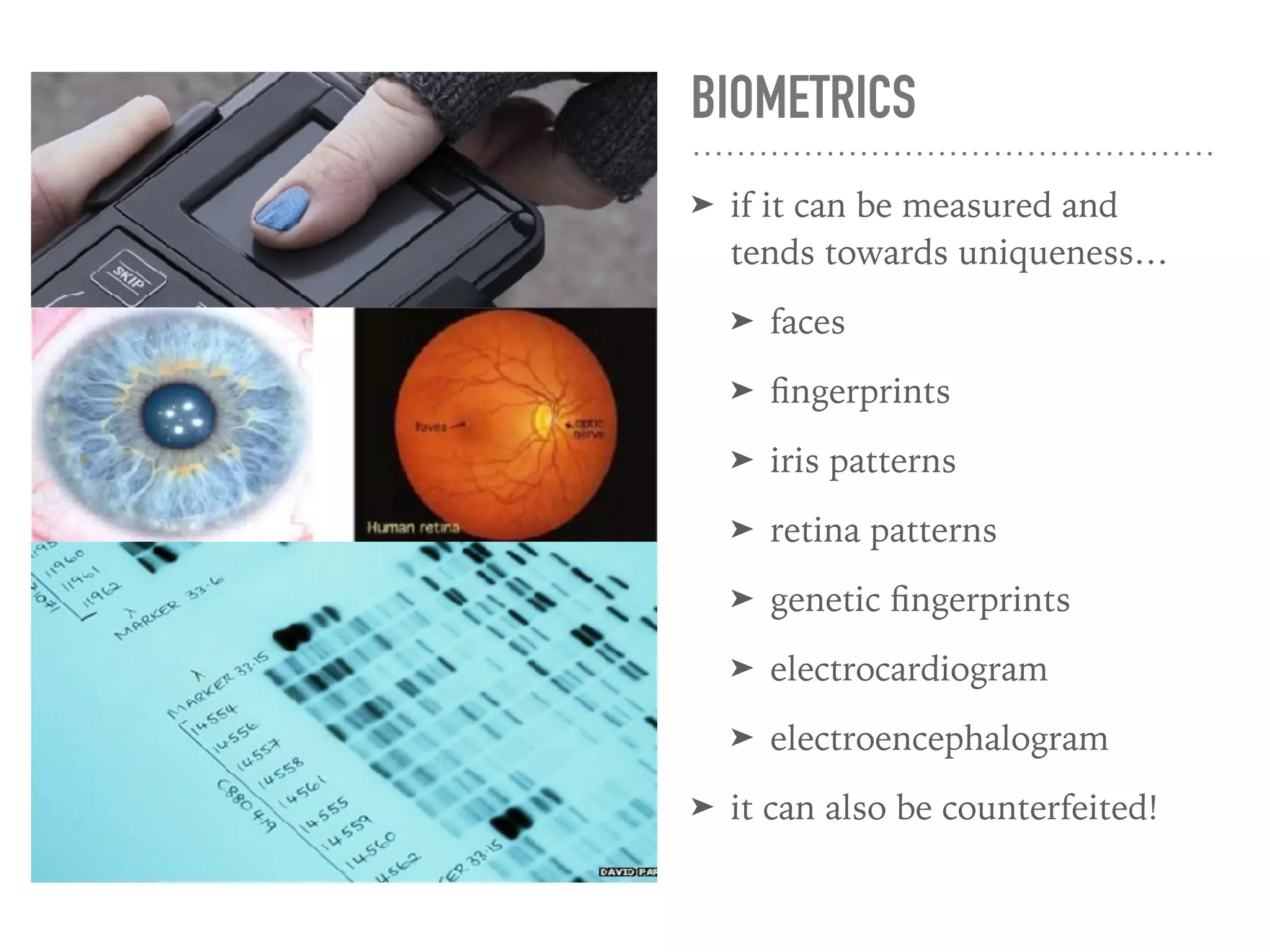
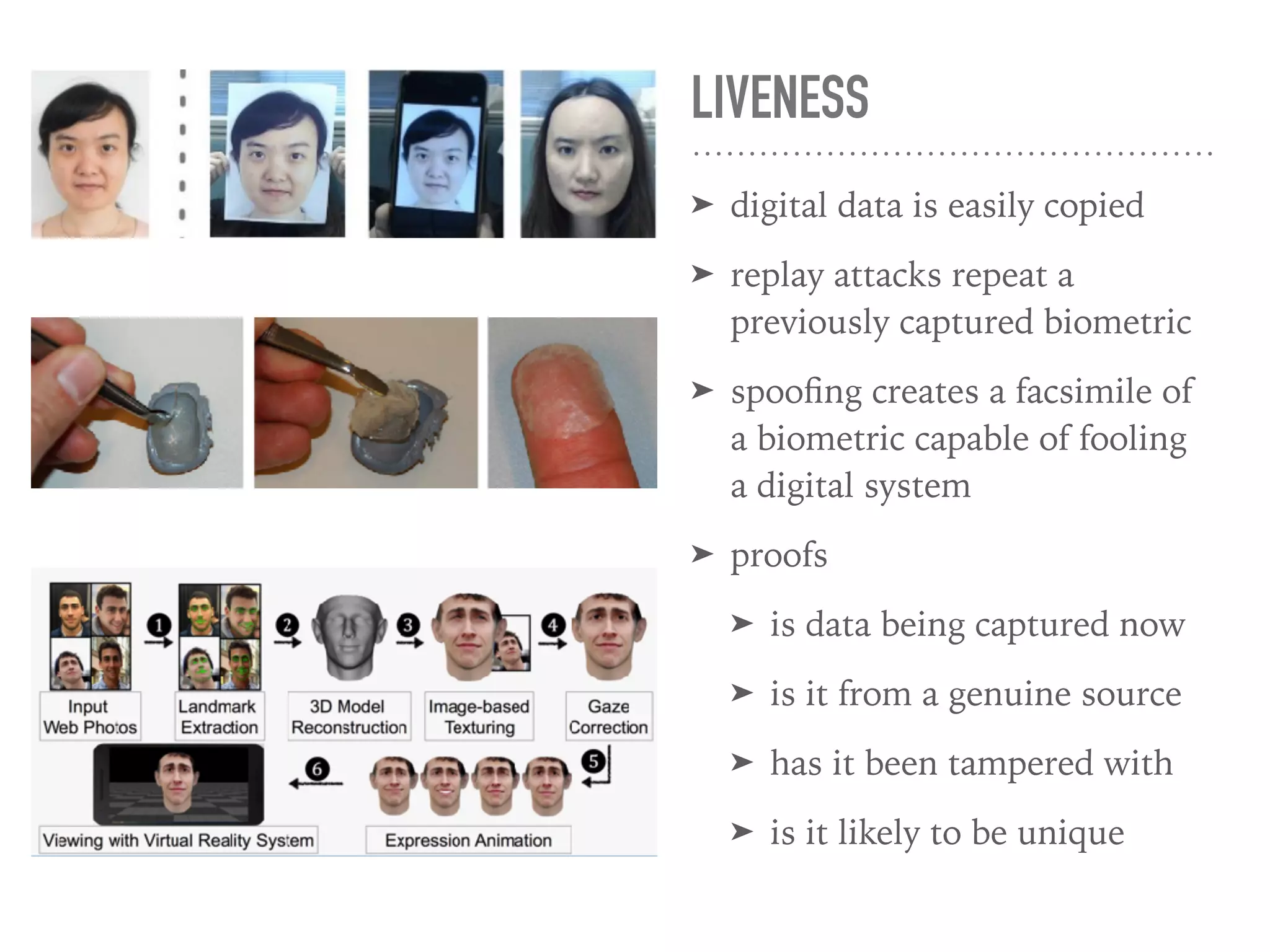
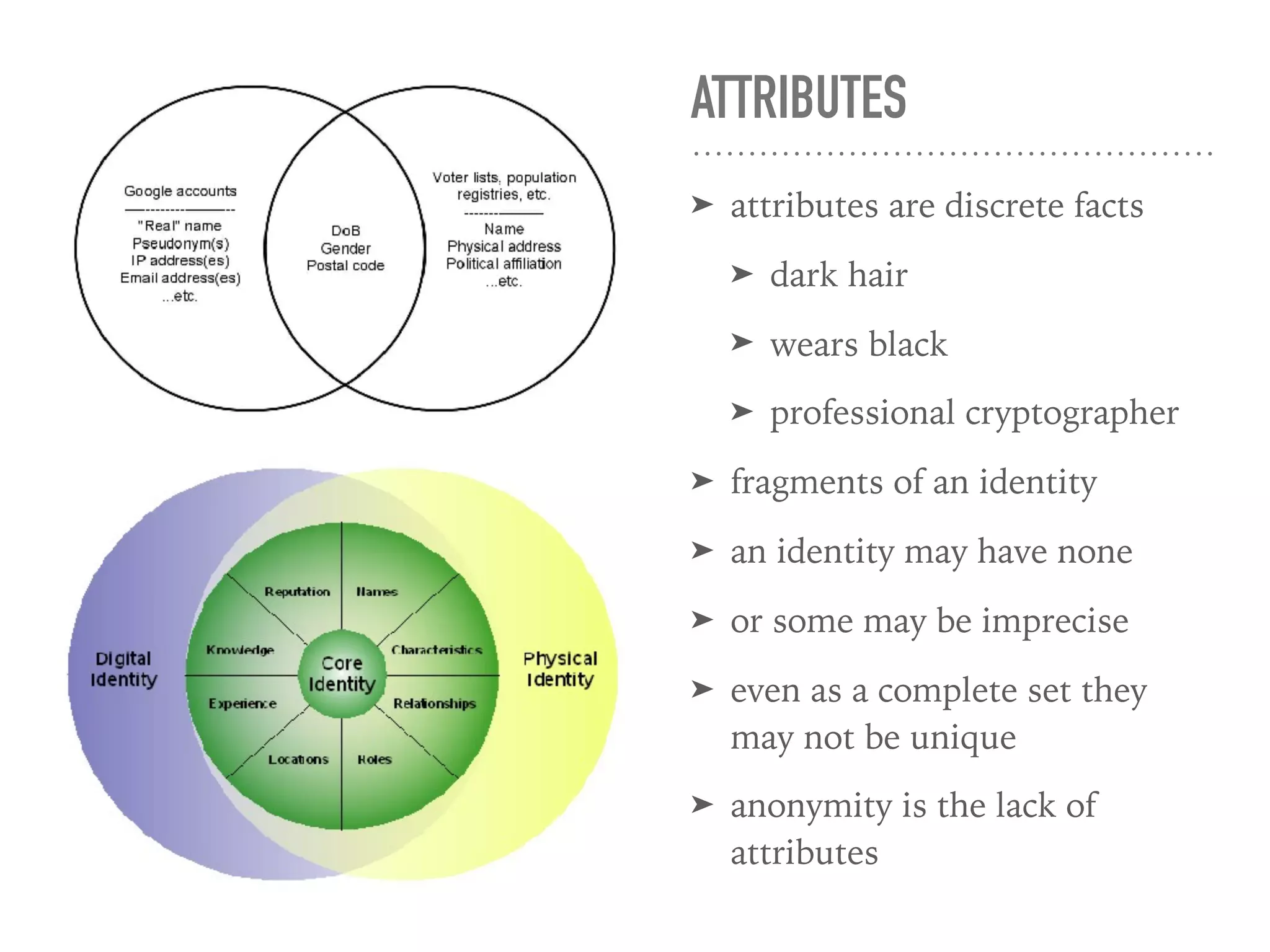
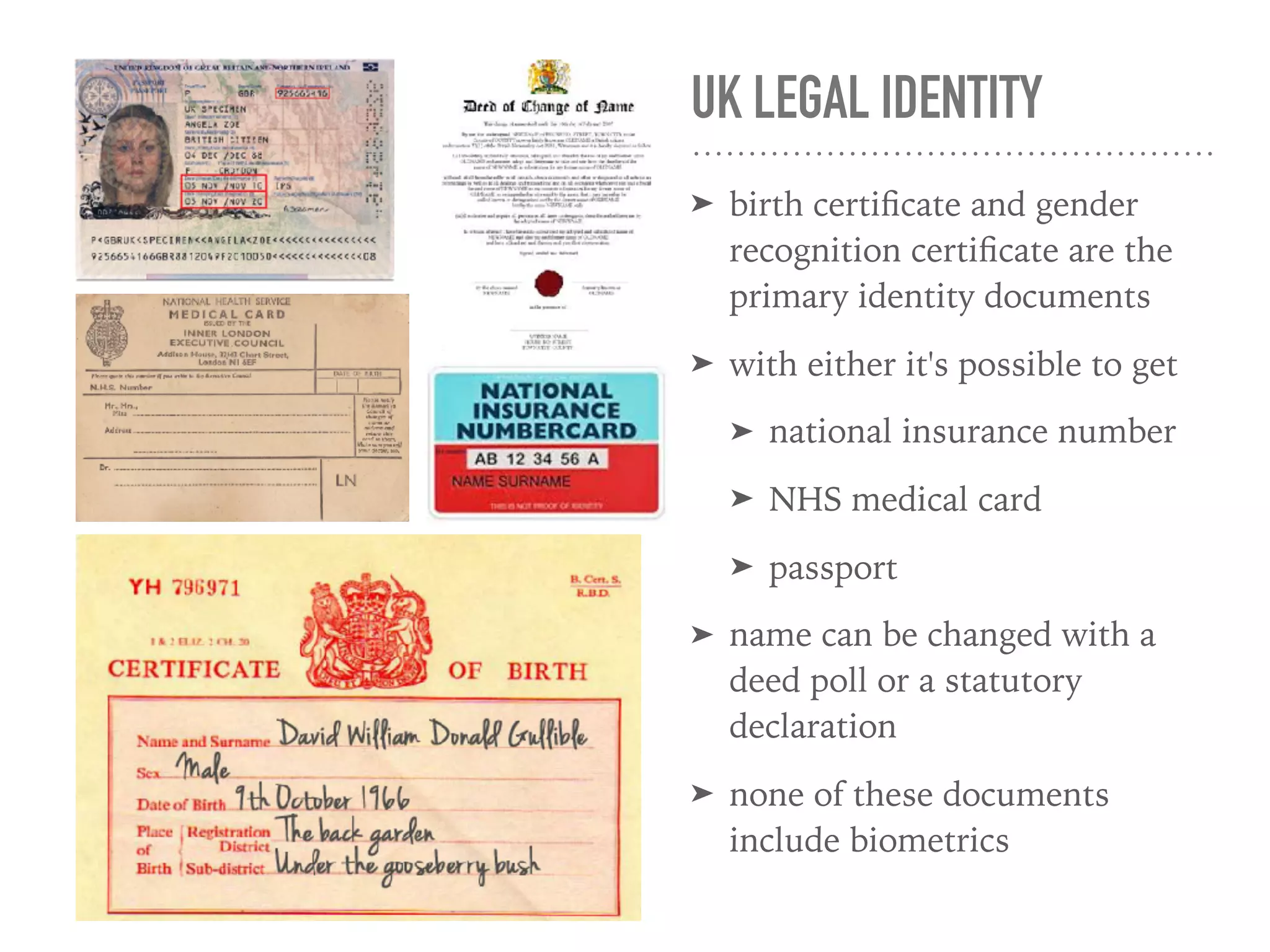
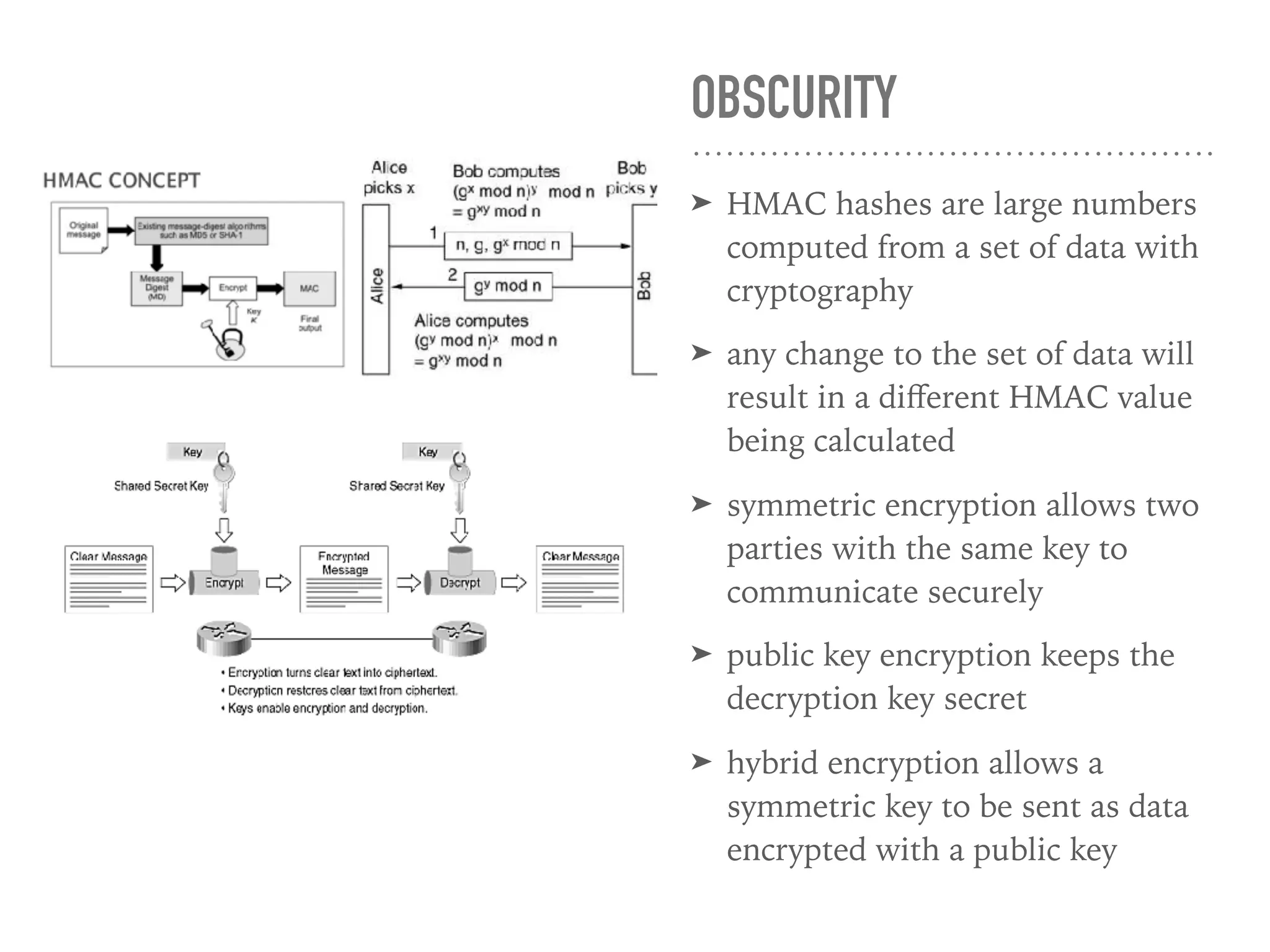
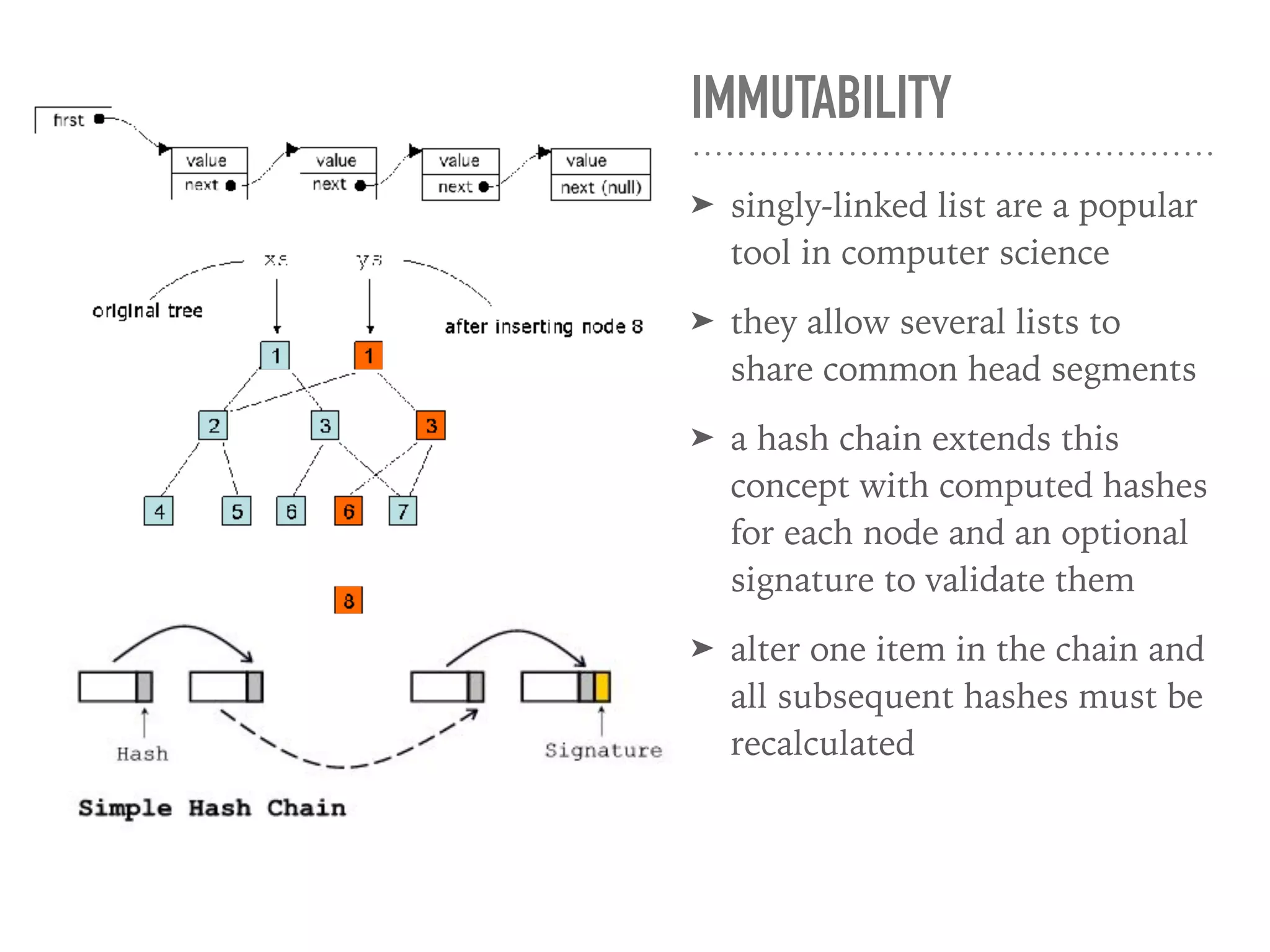
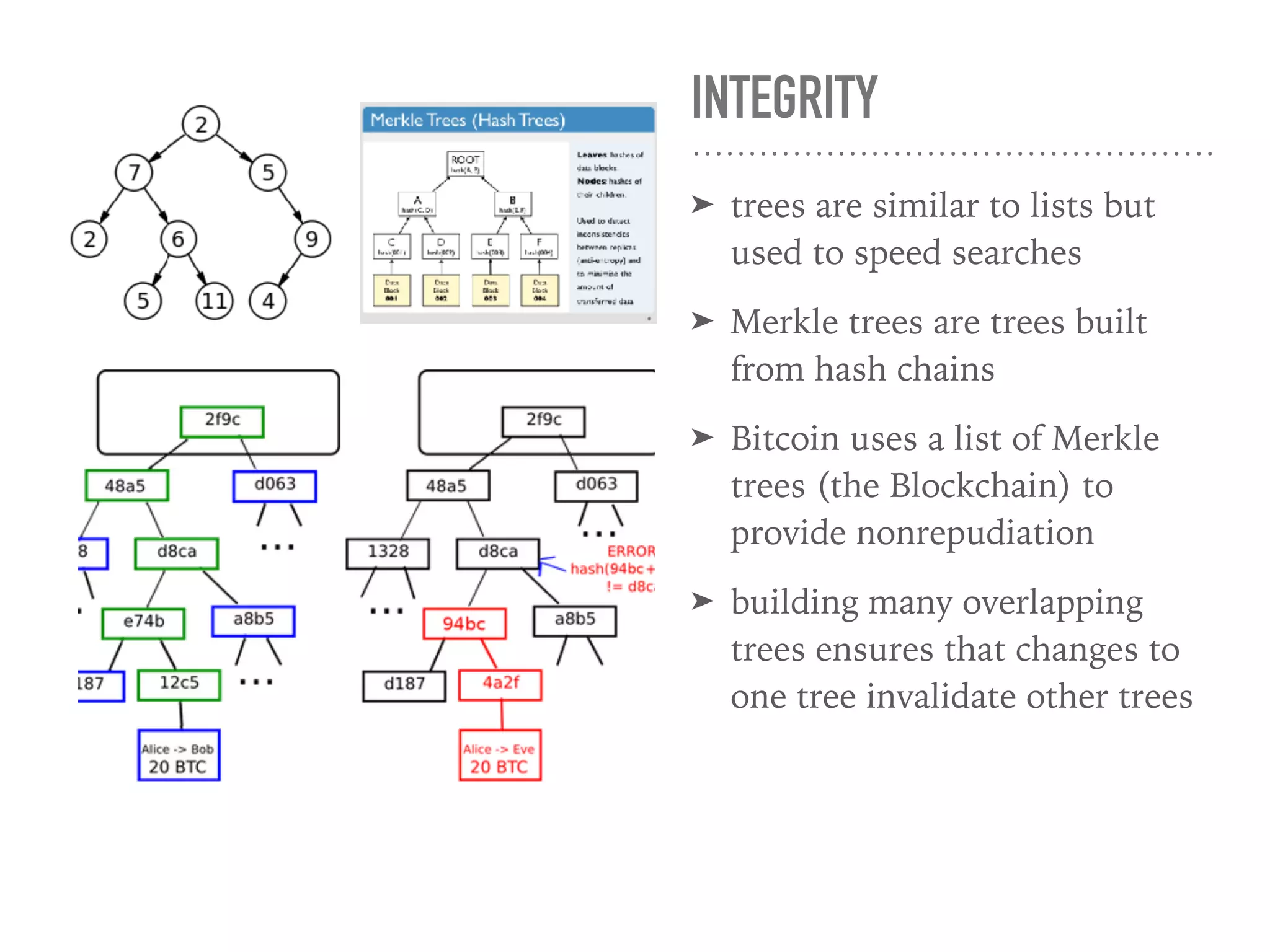
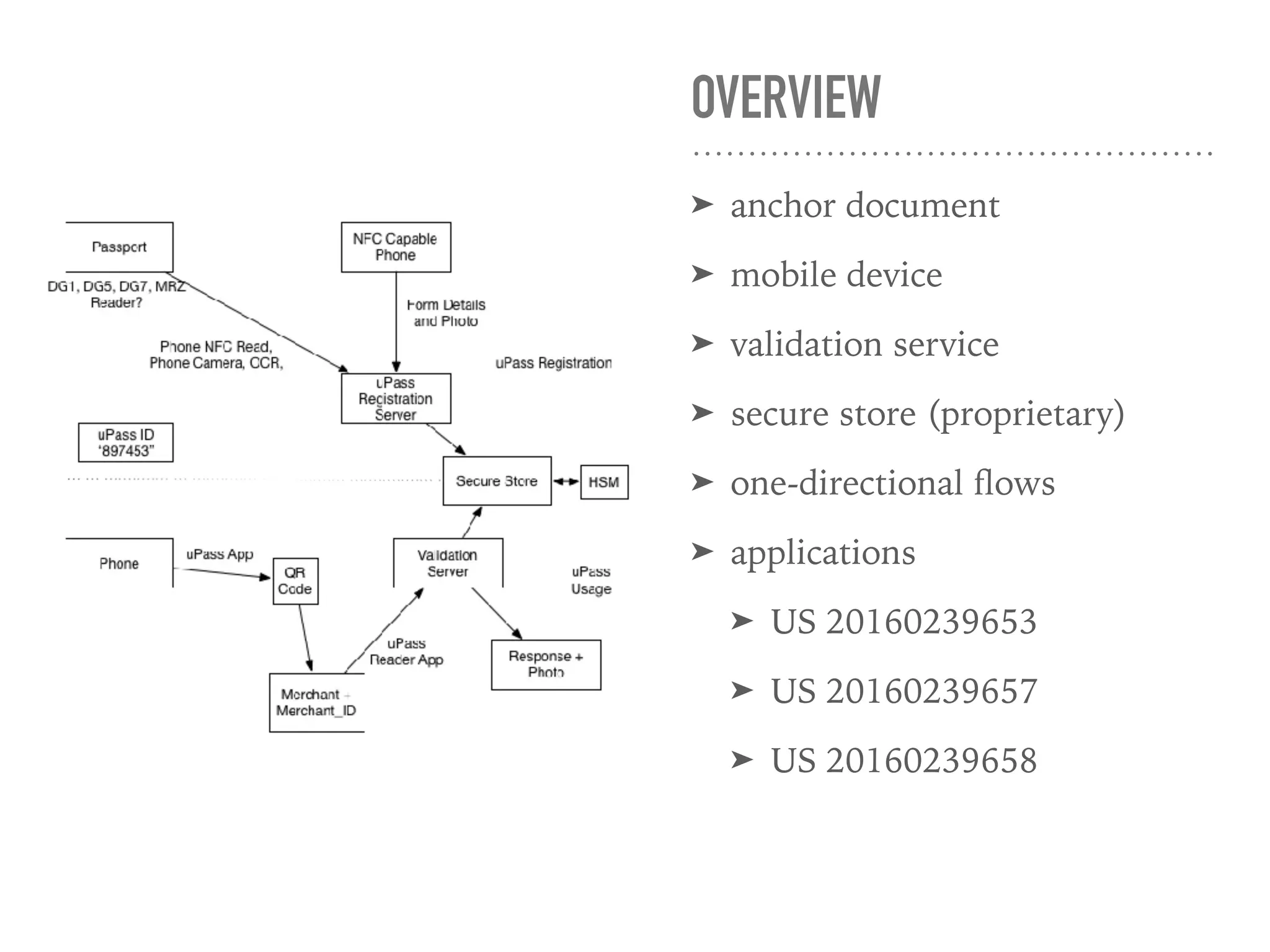
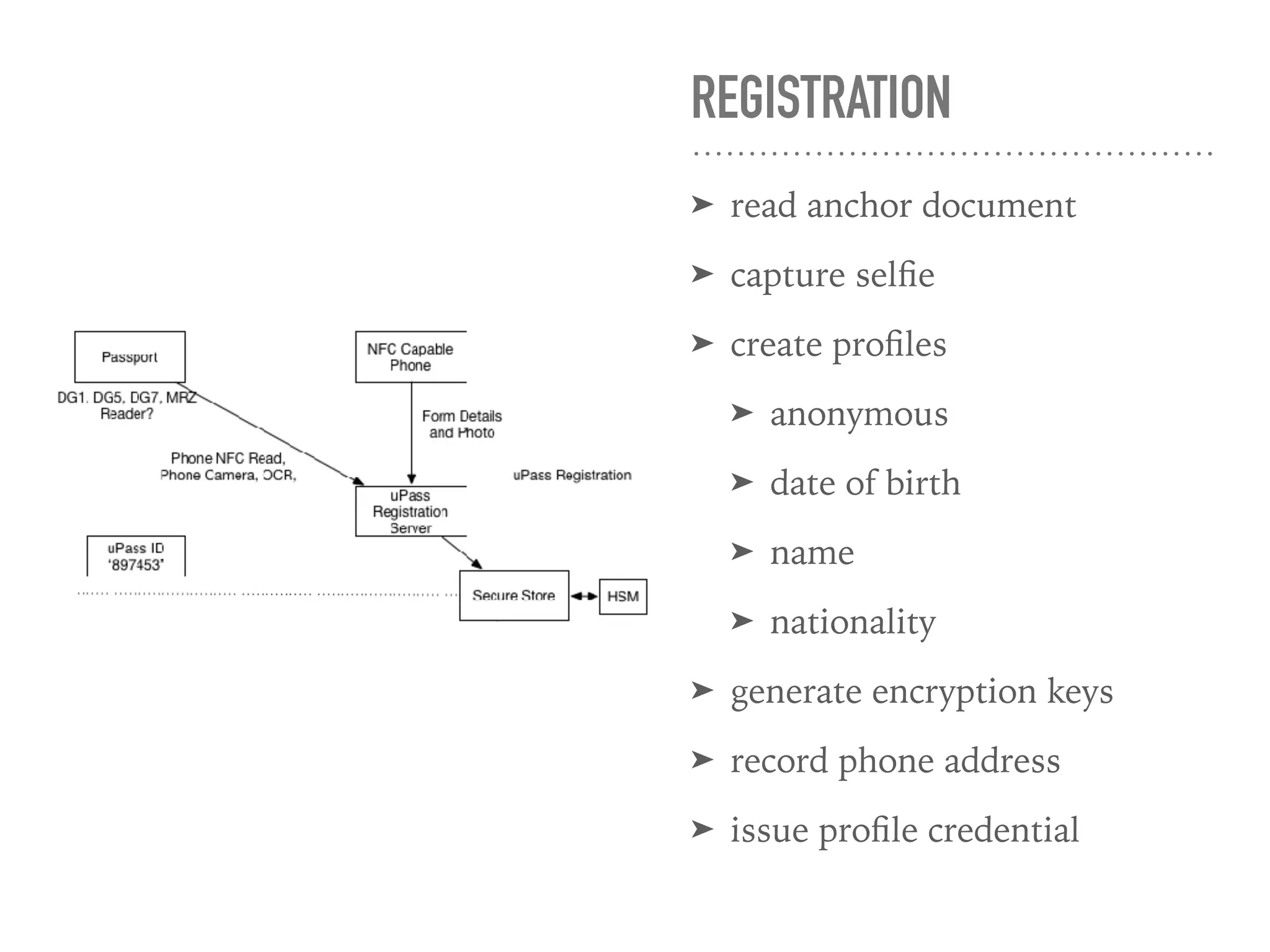
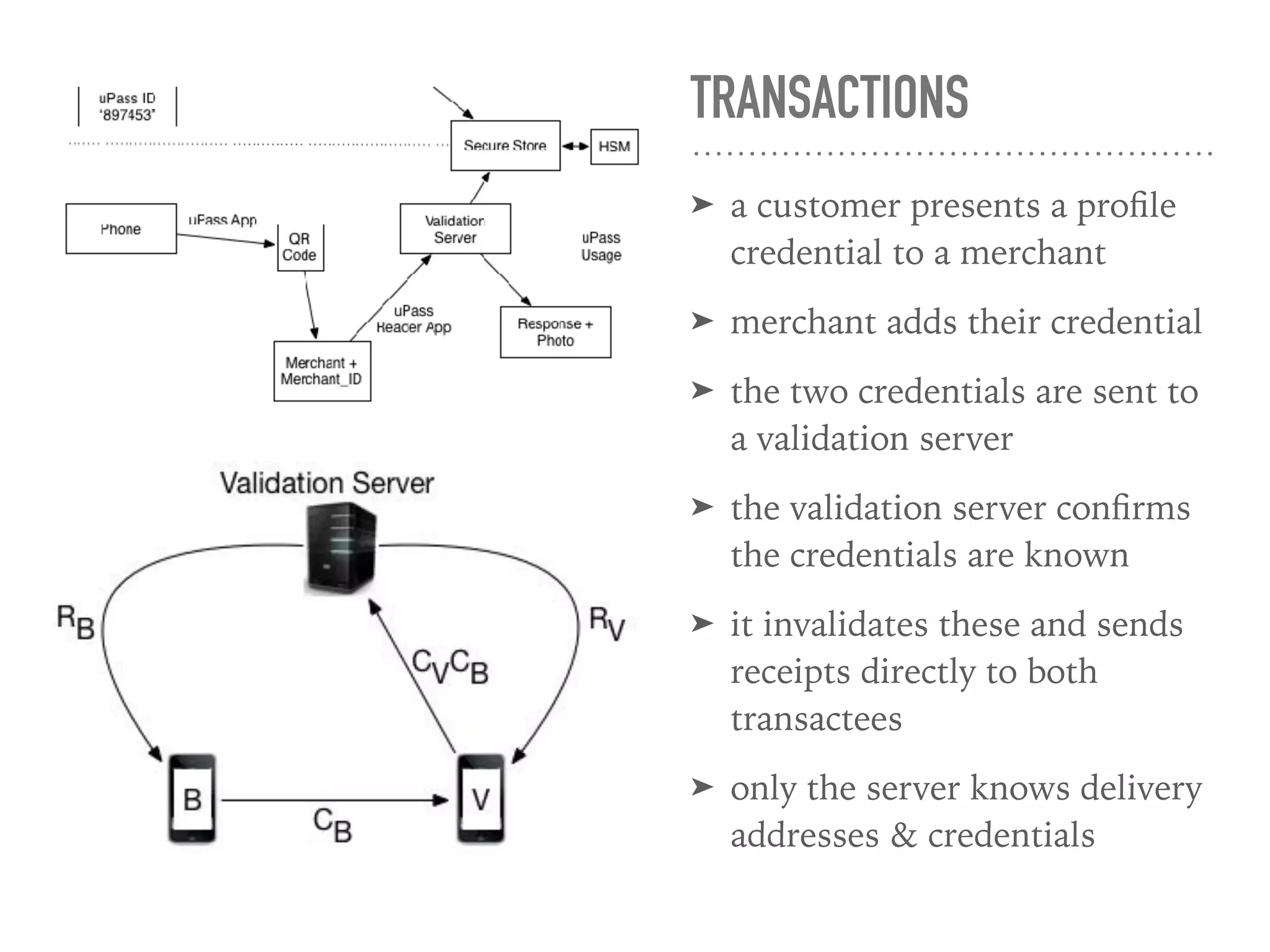
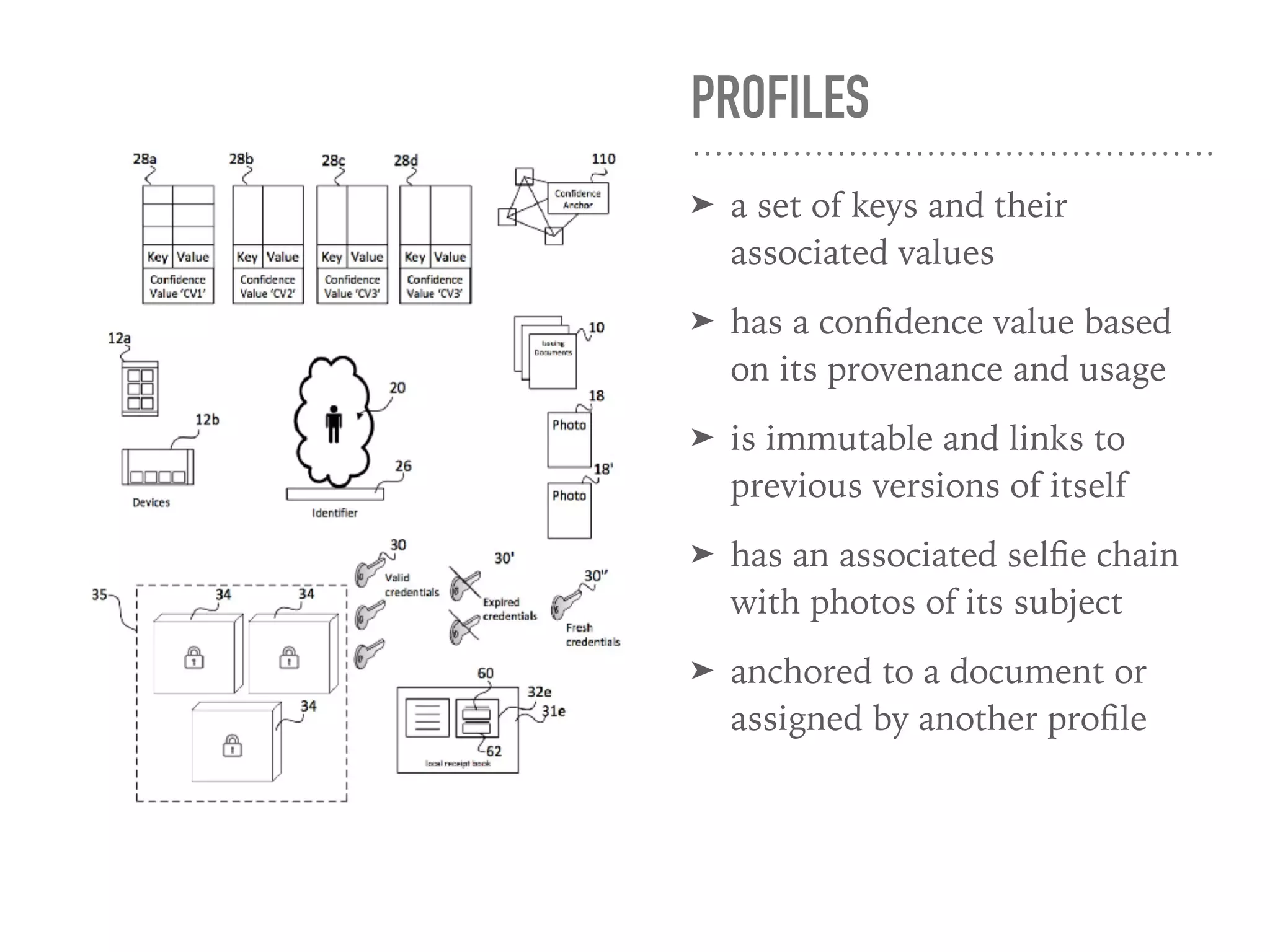
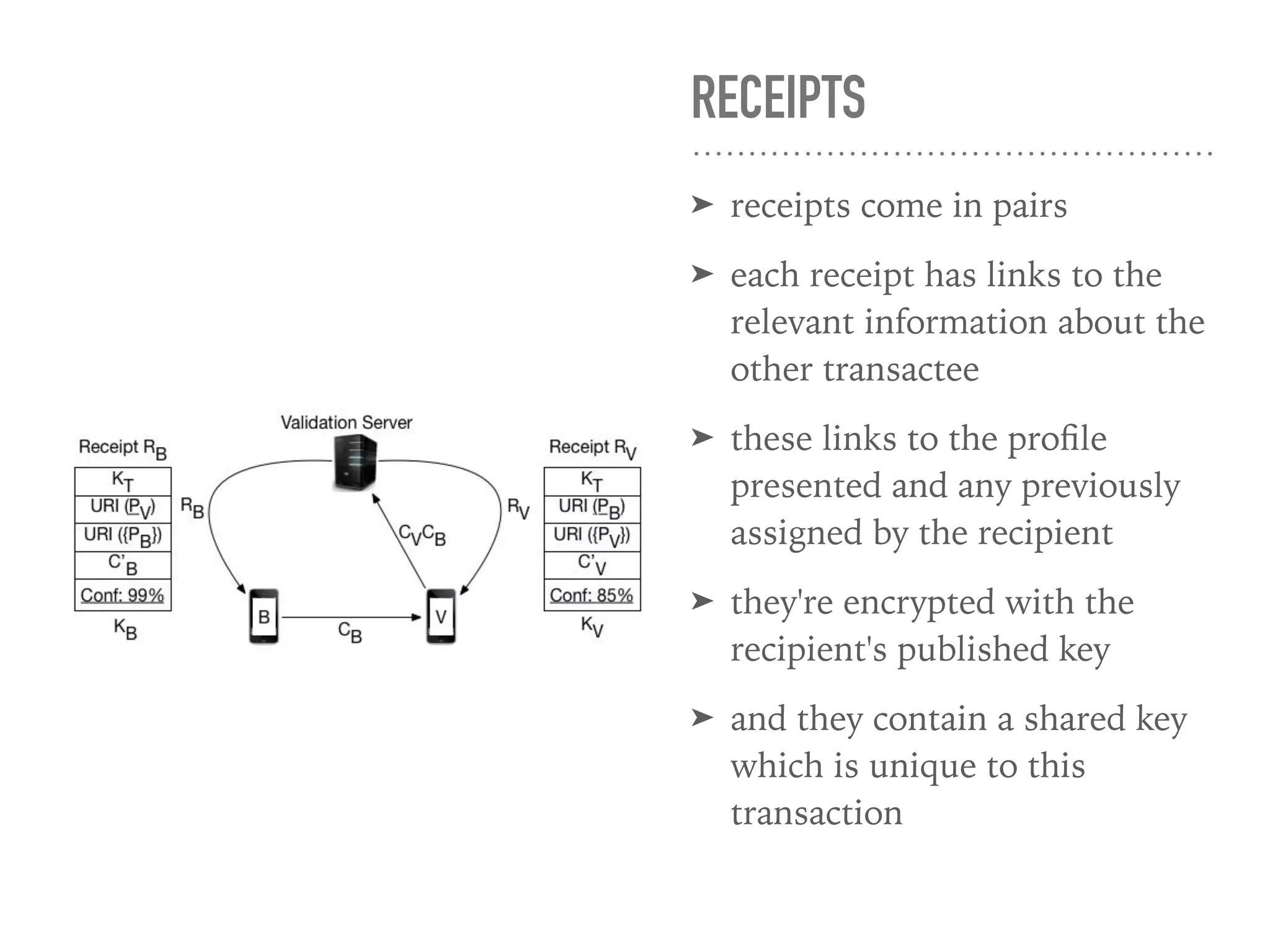
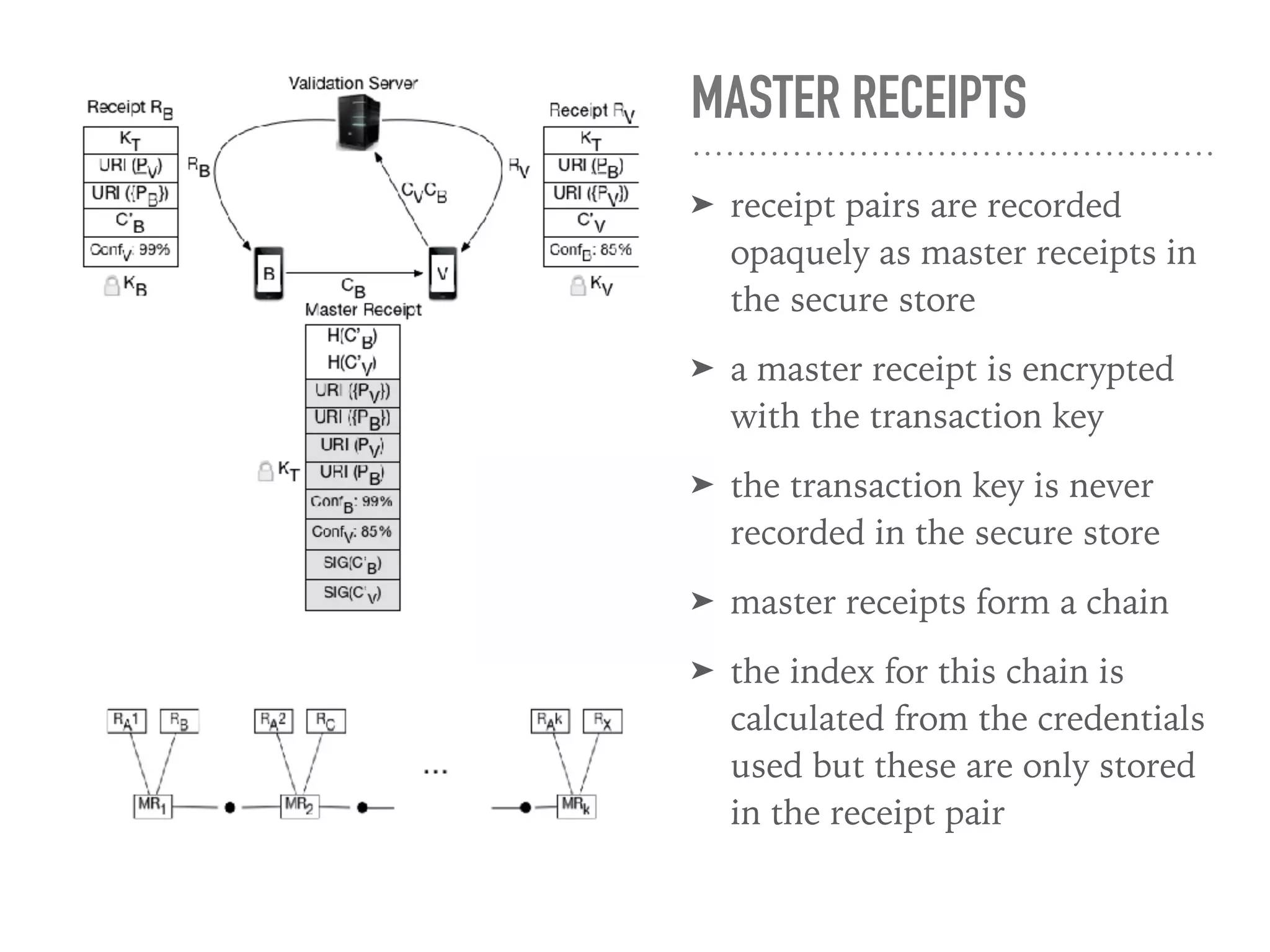
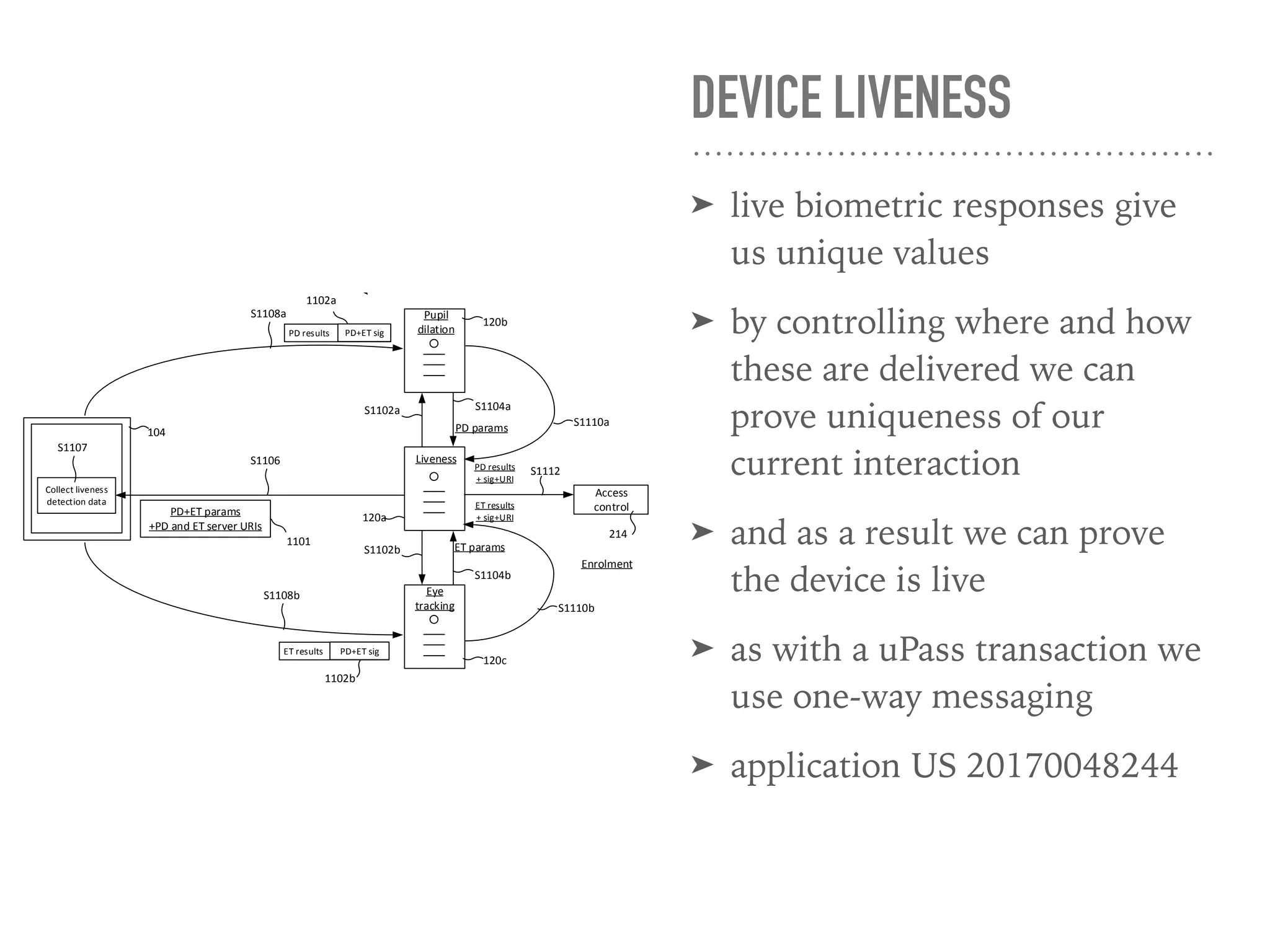
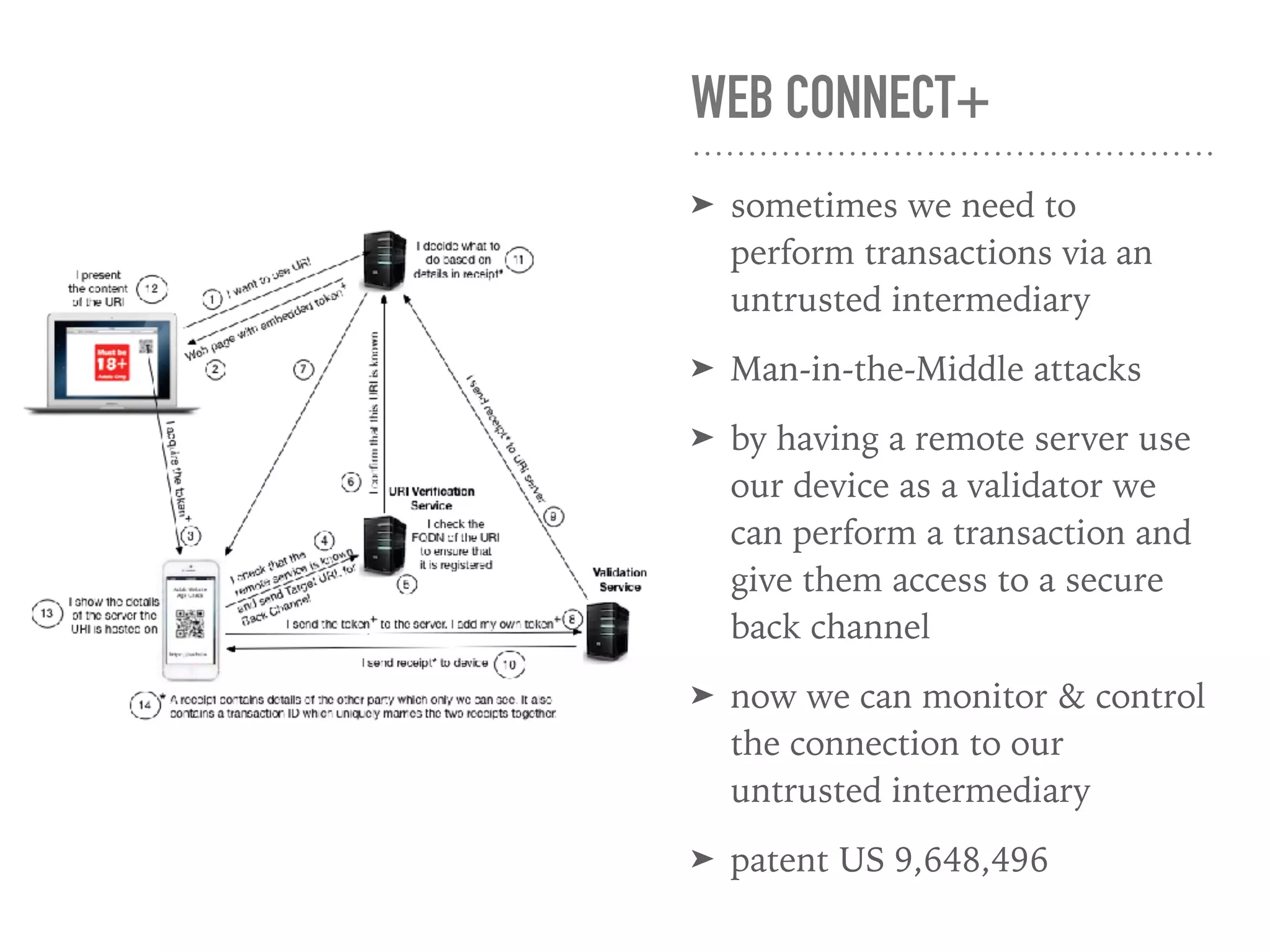
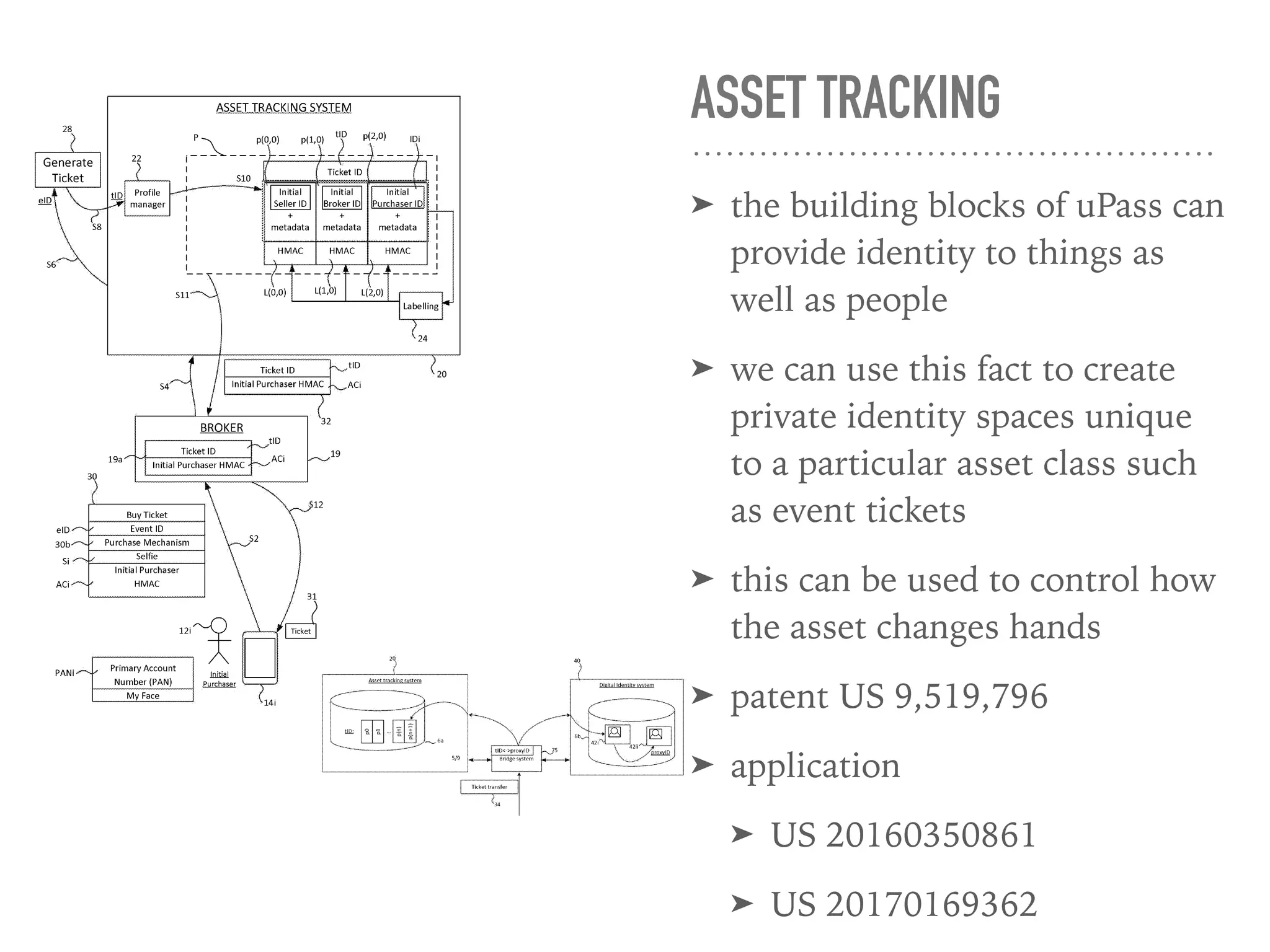
The document provides an overview of the Upass identity system developed by Romek Szczesniak and Eleanor McHugh, encompassing various aspects of digital identity and privacy. It discusses identity verification methods, including biometrics and cryptographic techniques, while highlighting the importance of trust and proof in identity exchanges. Additionally, it outlines features of the Upass system, such as anonymity, secure transactions, and the integration of identity for both individuals and assets.