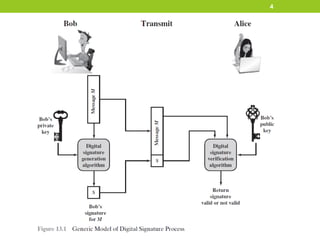
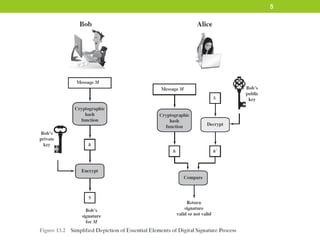
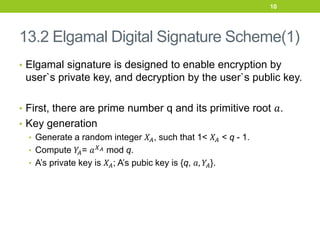
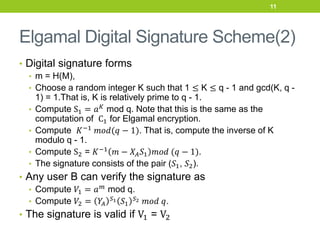
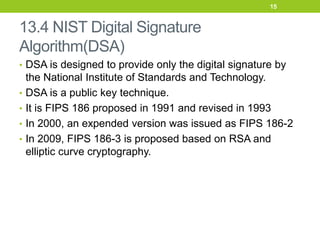
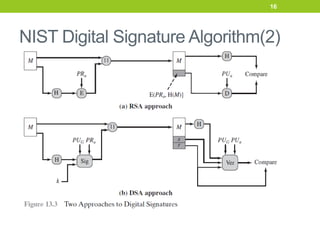
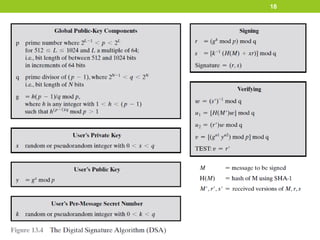
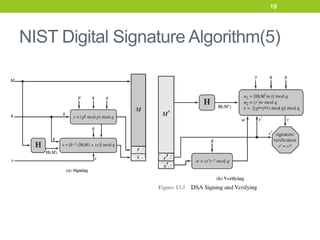
The document provides an overview of digital signatures and several digital signature schemes, including Elgamal, Schnorr, NIST DSA, and RSA-PSS. It describes the key properties and requirements of digital signatures. It then explains the technical details and signature generation/verification processes for each scheme. For Elgamal, it covers key generation, signature formation, and verification. For Schnorr, it outlines the key generation, signature generation steps, and verification step. It also discusses the design and processes of NIST DSA and RSA-PSS digital signature algorithms in multiple sections.


![RSA-PSS Digital Signature Algorithm(3)
• MGF1 is defined as follows:
• Initialize variables
T = empty string
K = [maskLen / hLen ] -1
• Calculate intermediate values
For counter = 0 to k
Represent counter as a 32-bit string C
T = T || Hash(X || C)
• Output results
Mask = the leading maskLen octets of T
22](https://image.slidesharecdn.com/chap13-digitalsignature-220823212356-5db2ce50/85/chap13-digitalsignature-pdf-22-320.jpg)
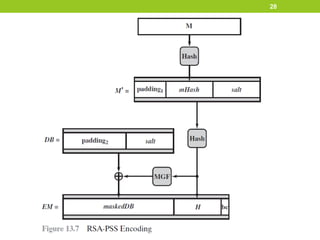
![RSA-PSS Digital Signature Algorithm(6)
Parameters
• emLen
• length of EM in octets = [emBits/8]
• Padding1
• hexadecimal string 00 * 8; that is a string of 64 zero bits.
• Padding2
• hexadecimal string of 00 octets with a length(emLen – sLen – hLen
-2) octets, followed by hexadecimal octet with value 01
• Salt
• A pseudorandom number
• bc
• The hexadecimal value BC
25](https://image.slidesharecdn.com/chap13-digitalsignature-220823212356-5db2ce50/85/chap13-digitalsignature-pdf-25-320.jpg)

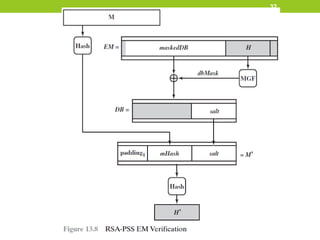
![RSA-PSS Digital Signature Algorithm(9)
Signature verification
• Decryption
• The message digest m is recovered by decrypting s
m = 𝑠𝑒
𝑚𝑜𝑑 𝑛
• Then, convert m to EM of length emLen = [modBits -
1)/8]octets, where modBits is the length in bits of the
modulus n.
29](https://image.slidesharecdn.com/chap13-digitalsignature-220823212356-5db2ce50/85/chap13-digitalsignature-pdf-29-320.jpg)