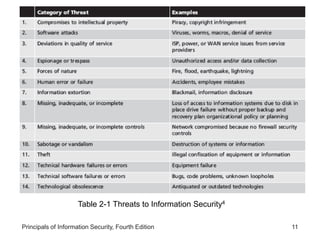
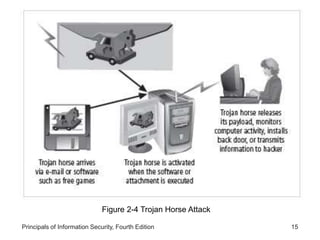
This chapter discusses the need for information security in organizations. It explains that information security has four main functions: protecting organizational functionality, enabling safe application operations, protecting collected data, and safeguarding technology assets. The chapter also identifies common threats like malware, hacking, and human error that can compromise information security. It emphasizes that effective security requires identifying threats, implementing appropriate controls, and developing secure software.