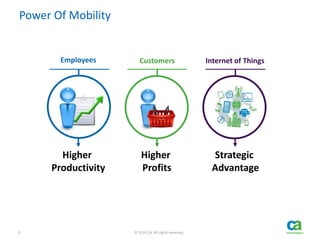
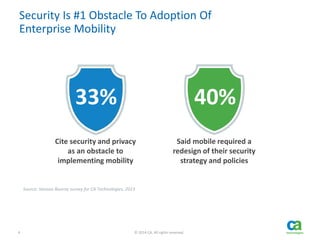
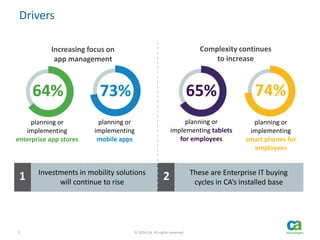
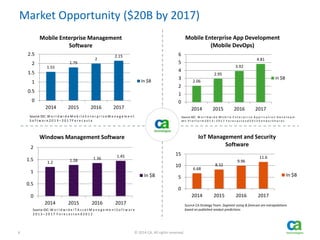
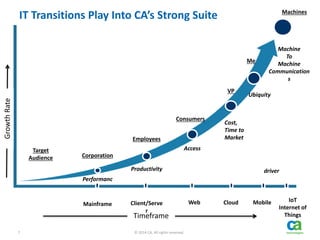
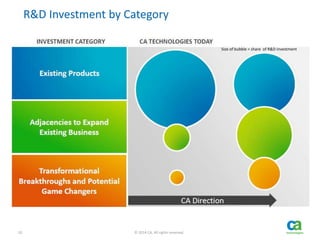
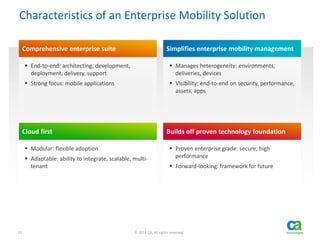
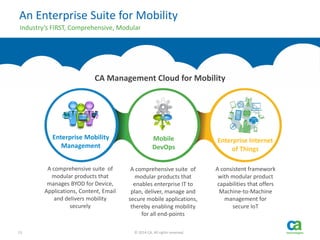
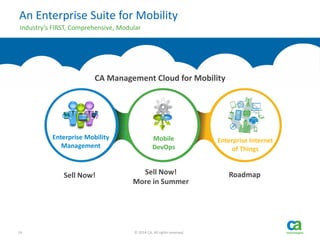
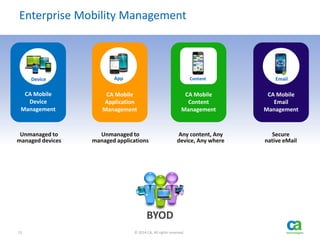
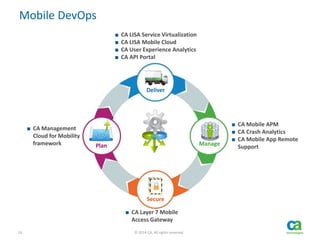
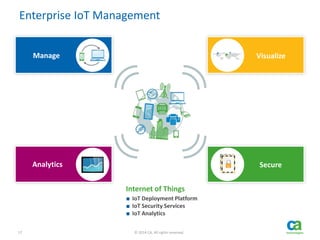
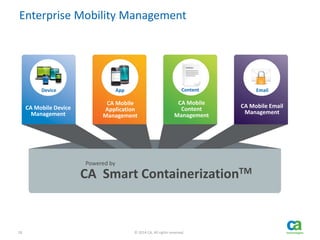
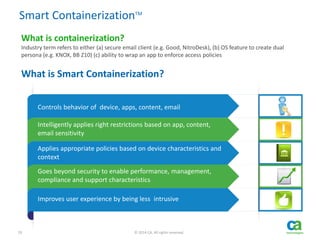
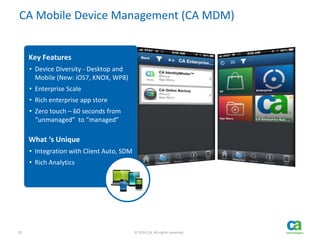
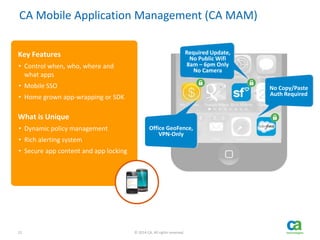
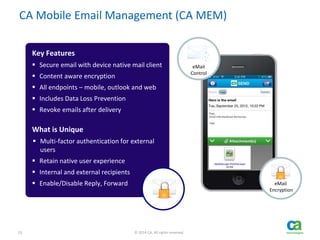
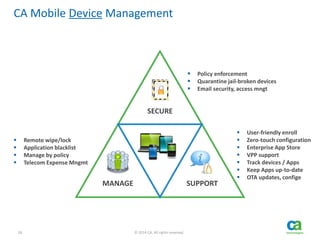
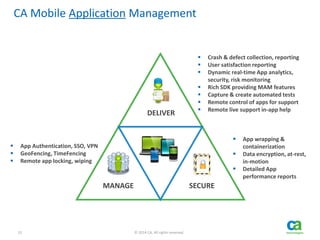
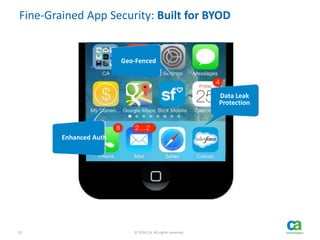
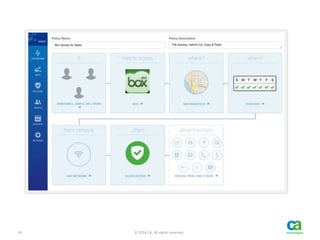
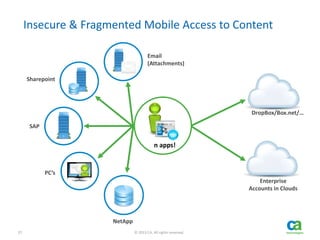
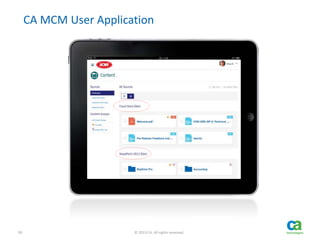
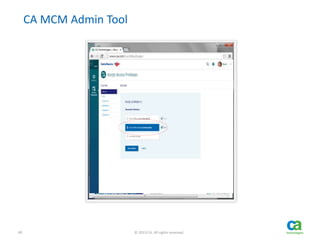
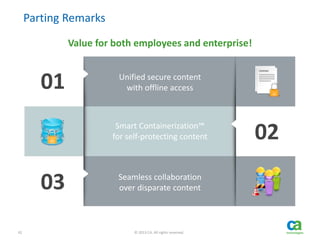
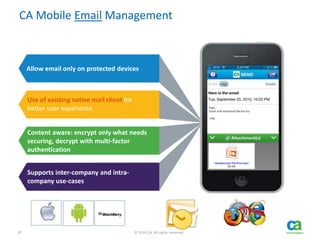
The document outlines CA Technologies' enterprise mobility management solutions, emphasizing the growing market opportunity and the need for enhanced security measures in mobile environments. It introduces the CA Management Cloud for Mobility, a comprehensive suite designed to securely manage devices, applications, and content, facilitating mobility for enterprises. Key features include modularity, adaptability, and strong focus on end-to-end solutions for diverse devices and platforms.