This document summarizes the key aspects of database normalization including:
1) It discusses the first, second, third, and Boyce-Codd normal forms and the objectives of normalization to reduce data redundancy and dependencies.
2) It provides examples of applying normalization to tables to remove anomalies like modifying a passenger's phone number would require changing it in multiple places.
3) It includes examples of SQL queries on the normalized tables including finding driver salaries between a range, displaying bus seat availability, and retrieving passenger details based on user ID.
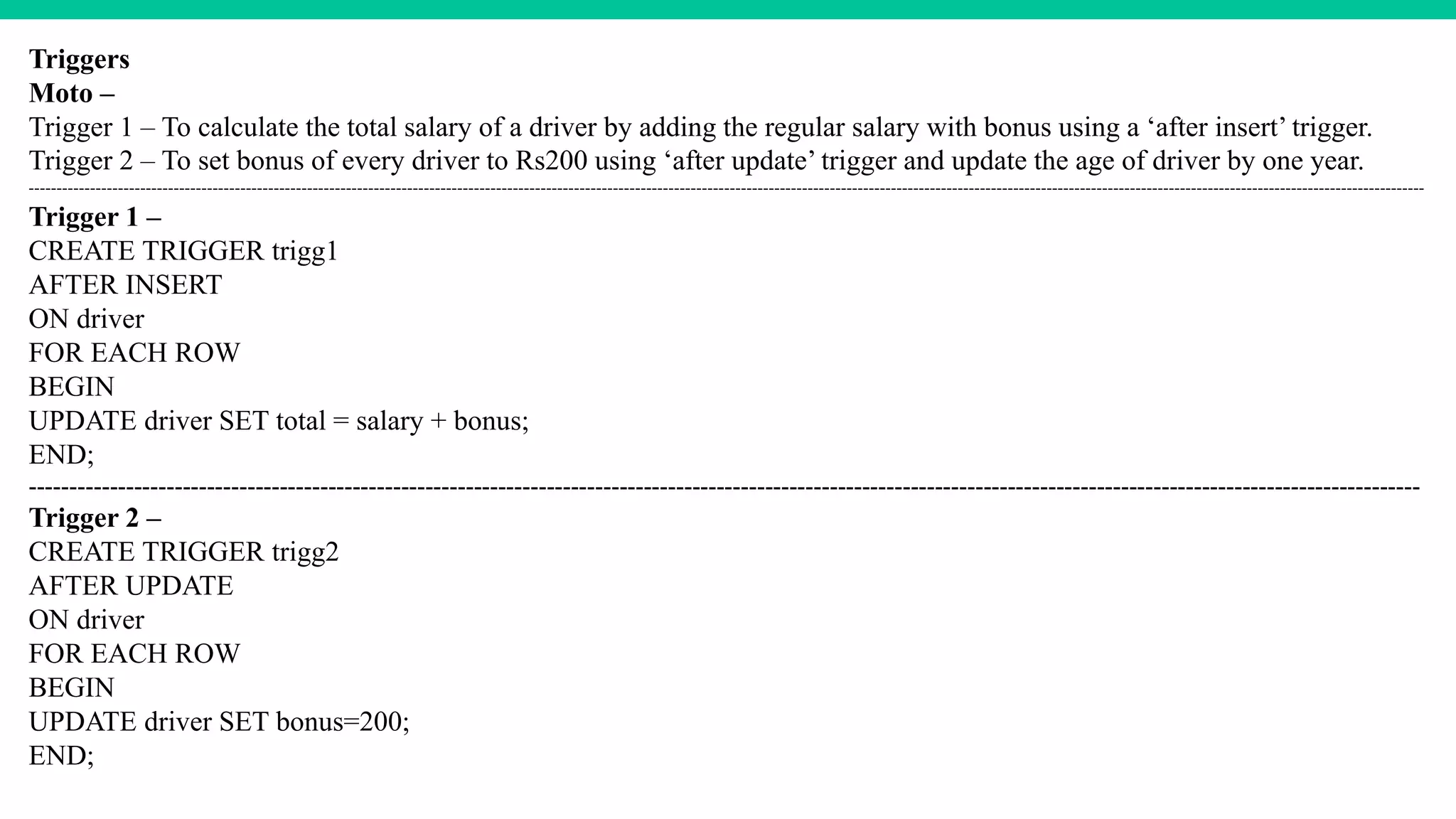
4) Triggers are defined to calculate total salary on insert and update bonus amounts and driver age on update. Views are defined with advantages being logical representation of data and