BigID Datasheet: CCPA Data Rights Automation
•
1 like•477 views
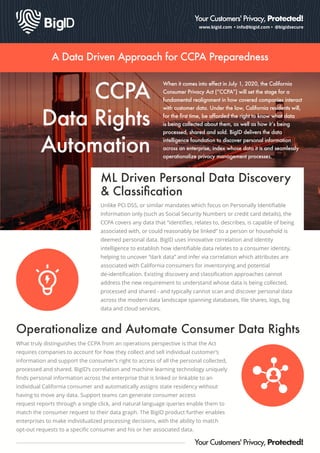
A Data Driven Approach for CCPA Preparedness By BigID. When it comes into effect in 2020, the California Consumer Privacy Act (“CCPA”) will set the stage for a fundamental realignment in how covered companies interact with customer data. Under the law, California residents will, for the first time, be afforded the right to know what data is being collected about them, as well as how it’s being processed, shared and sold. BigID delivers the data intelligence foundation to discover personal information across an enterprise, index whose data it is and seamlessly operationalize privacy management processes.
Report
Share
Report
Share
Download to read offline
Recommended
BigID DataSheet: Data Access Intelligence

Data Intelligence Meets Access
Intelligence Organizations face mounting urgency to identify sensitive data across
their data landscape to both better protect it and satisfy emerging
privacy regulations. Traditional data classification tools don’t have the
ability to find all personal information, look across all data, or sort data by both type and person. BigID provides a first of its kind identity-centric data intelligence platform that can look across unstructured, structured, Big Data, cloud and more while simultaneously classifying data by type and correlating by person - essential for meeting privacy data rights. Now BigID has added access insights so enterprises can both know what sensitive data they have where, but also whether specific data objects have open access permissions.
BigID Data Sheet HIPAA Data Security & Privacy 

Under the HIPAA mandate, covered entities and business associates are subject to the Security Rule that covers confidentiality, integrity, and availability of electronic Protected Health Information (ePHI) and the Privacy Rule that limits the uses and disclosures of PHI. These rules have long been in place, but how ePHI moves through and across
IT infrastructure and is tied to Personal Information within IT systems and applications has shifted since the rules were first written.
Also, the penalties levied by regulators for breach, unauthorized disclosure and privacy violations have escalated. BigID automatically discovers, maps and labels all instances of PHI identifiers and across data sources through novel correlation and machine learning technologies to drive both security and privacy compliance initiatives.
BigID Data Sheet: LGPD Compliance Automated

LGPD Compliance Automated:
Brazil's Data Protection Law (Lei Geral de Proteção de Dados or LGPD) establishes both a new set of obligations for companies processing personal data or using the data to provide services in Brazil, as well as a comprehensive set of individual data rights that incorporate explicit consent for specific purposes of processing. At the same time, the law also expands the definition for what data should be protected, including categories of sensitive data that require stronger protection. BigID is the first product to apply identity intelligence and smart correlation to the new privacy protection challenges, enabling companies to prepare, operationalize and automate their path to LGPD compliance
BigID Data sheet: Consent Governance & Orchestration

Under EU GDPR, capturing and recording explicit consent is a prerequisite for collecting and processing personal data. But how can covered companies manage multiple forms of consent from multiple sources to address baseline logging compliance requirements and, more fundamentally, determine whether consent is valid and consistent with which attributes are actually being collected and processed? By aggregating and correlating consent records to specific data subjects, BigID provides the foundation to address the purpose of consent. BigIDʼs unique ability to associate granular data knowledge to individuals transforms consent capture processes into a practical inspection and validation tool for how personal data is collected and processed.
BigID Data Sheet: GDPR Compliance

Data-driven General Data Protection Regulation Compliance By BigID
European Union General Data Protection Regulation (GDPR) is a landmark in data privacy protection. In formalizing individual rights including explicit consent, accountability, and processing transparency, the GDPR has teeth: regulators can impose hefty penalties of up to 4% of global revenues for violations. GDPR requires an enterprise to formalize how they manage and track personal data. BigID provides a next-generation Big Data Approach to help companies meet the regulatory requirements of GDPR.
BigID Data Sheet: Smart Data Labeling and Tagging

Effective data protection enforcement depends on understanding what data needs to be protected - especially as mandates like the EU GDPR and pending California Consumer Privacy Act add privacy protection requirements. Through smart labeling that leverages machine learning for discovery and classification and identity correlation for privacy understanding, BigID enables smarter, more accurate and automated policy enforcement actions. Customers can optimize their existing enforcement investments to take smarter policy actions and address new
BigID GDPR RoPA / Article 30 Automation Data Sheet

BigID helps organizations build and maintain GDPR Article 30 records of data processing from actual data records vs recollections. Using BigID organizations can satisfy regulator requirements and gather greater data lineage detail.
BigID Data Inventory & Data Mapping Data Sheet

See how BigID automates sensitive and PII data discovery, classification, and cataloging across structured, unstructured, Big Data and Cloud and Petabyte scale
Recommended
BigID DataSheet: Data Access Intelligence

Data Intelligence Meets Access
Intelligence Organizations face mounting urgency to identify sensitive data across
their data landscape to both better protect it and satisfy emerging
privacy regulations. Traditional data classification tools don’t have the
ability to find all personal information, look across all data, or sort data by both type and person. BigID provides a first of its kind identity-centric data intelligence platform that can look across unstructured, structured, Big Data, cloud and more while simultaneously classifying data by type and correlating by person - essential for meeting privacy data rights. Now BigID has added access insights so enterprises can both know what sensitive data they have where, but also whether specific data objects have open access permissions.
BigID Data Sheet HIPAA Data Security & Privacy 

Under the HIPAA mandate, covered entities and business associates are subject to the Security Rule that covers confidentiality, integrity, and availability of electronic Protected Health Information (ePHI) and the Privacy Rule that limits the uses and disclosures of PHI. These rules have long been in place, but how ePHI moves through and across
IT infrastructure and is tied to Personal Information within IT systems and applications has shifted since the rules were first written.
Also, the penalties levied by regulators for breach, unauthorized disclosure and privacy violations have escalated. BigID automatically discovers, maps and labels all instances of PHI identifiers and across data sources through novel correlation and machine learning technologies to drive both security and privacy compliance initiatives.
BigID Data Sheet: LGPD Compliance Automated

LGPD Compliance Automated:
Brazil's Data Protection Law (Lei Geral de Proteção de Dados or LGPD) establishes both a new set of obligations for companies processing personal data or using the data to provide services in Brazil, as well as a comprehensive set of individual data rights that incorporate explicit consent for specific purposes of processing. At the same time, the law also expands the definition for what data should be protected, including categories of sensitive data that require stronger protection. BigID is the first product to apply identity intelligence and smart correlation to the new privacy protection challenges, enabling companies to prepare, operationalize and automate their path to LGPD compliance
BigID Data sheet: Consent Governance & Orchestration

Under EU GDPR, capturing and recording explicit consent is a prerequisite for collecting and processing personal data. But how can covered companies manage multiple forms of consent from multiple sources to address baseline logging compliance requirements and, more fundamentally, determine whether consent is valid and consistent with which attributes are actually being collected and processed? By aggregating and correlating consent records to specific data subjects, BigID provides the foundation to address the purpose of consent. BigIDʼs unique ability to associate granular data knowledge to individuals transforms consent capture processes into a practical inspection and validation tool for how personal data is collected and processed.
BigID Data Sheet: GDPR Compliance

Data-driven General Data Protection Regulation Compliance By BigID
European Union General Data Protection Regulation (GDPR) is a landmark in data privacy protection. In formalizing individual rights including explicit consent, accountability, and processing transparency, the GDPR has teeth: regulators can impose hefty penalties of up to 4% of global revenues for violations. GDPR requires an enterprise to formalize how they manage and track personal data. BigID provides a next-generation Big Data Approach to help companies meet the regulatory requirements of GDPR.
BigID Data Sheet: Smart Data Labeling and Tagging

Effective data protection enforcement depends on understanding what data needs to be protected - especially as mandates like the EU GDPR and pending California Consumer Privacy Act add privacy protection requirements. Through smart labeling that leverages machine learning for discovery and classification and identity correlation for privacy understanding, BigID enables smarter, more accurate and automated policy enforcement actions. Customers can optimize their existing enforcement investments to take smarter policy actions and address new
BigID GDPR RoPA / Article 30 Automation Data Sheet

BigID helps organizations build and maintain GDPR Article 30 records of data processing from actual data records vs recollections. Using BigID organizations can satisfy regulator requirements and gather greater data lineage detail.
BigID Data Inventory & Data Mapping Data Sheet

See how BigID automates sensitive and PII data discovery, classification, and cataloging across structured, unstructured, Big Data and Cloud and Petabyte scale
BigID Virtual MDM Data Sheet

BigID provides the industry first virtual Master Data Management system that allows companies to easily create a centralized view across a customer's data without centralizing the data.
BigID Data Subject Rights Automation for GDPR & Privacy Data Sheet

Read how BigID helps organizations operationalized GDPR and privacy personal data rights by helping organizations fulfill data subject rights like right-to-be-forgotten, right-to-access, right-to-portability, and right-to-rectification. BigID is the first software discovery tool that can leverage advanced ML and identity intelligence to find personal data anywhere and correlate it back to a person.
BigID GDPR Privacy Automation Data Sheet

BigID gives companies to automate core privacy and GDPR functions like data inventory, right-to-be-forgotten, consent, breach notification and Article 30 record keeling at scale.
BigID & Collibra Joint Deck: Using BigID’s Privacy-centric Data Discovery to...

This presentation was shown at this year's Collibra Data Citizens Conference in New York.
BigID's Smart Data Labeling and Tagging

Modern data protection and privacy rests on accurate data classification and labeling for smarter more accurate enforcement. BigID's award-winning sensitive data discovery and tagging provides a first of its kind ability to accurately find and secure personal data.
BigID Enterprise Privacy Management Data Sheet

Read how BigID redefines privacy management from surveys and spreadsheets to data-driven compliance built on actual data. Using BigID, organizations can more easily meet global privacy requirements while also safeguarding personal data across the enterprise.
BigID PII & PI Discovery for GDPR Data Sheet

Finding PII across structured, unstructured, Big Data, Cloud and applications is hard. Finding all PI (personal information) as required by GDPR and the California Consumer Privacy Act is harder. Regular Expression is not enough. BigID's patented machine learning makes discovery of contextual PI and correlation back to a person possible for the first time.
(SACON) Nandan Nilekani - Identity Payments and Data Empowerment 

Identity Payments and Data Empowerment Addressing Different challenges, Solving the Challenges, Payment challenges, Data Sharing and Privacy Challenges.
Putting in perspective: Innovation in digital age.
Collibra Data Citizen '19 - Bridging Data Privacy with Data Governance 

This presentation was shown at the 2019 Collibra Data Citizen Event in New York City.
Presented by Nimrod Vax, Chief Product Officer & Co-Founder & Joaquin Sufuentes, Lead Architect, Metadata Managment and Personal Infomation Protection, enterprise Data Managment, Intel IT
BigID GDPR Compliance Automation Webinar Slides

This Webinar featuring guests from the EU Commission, the French data regulator CNIL, DLA Piper and IBM provided an overview of the new EU data protection and privacy perspective from the perspective of the regulation author, regulator, legal advisor and technology providers.
India'a Proposed Privacy & Personal Data Protection Law 

India'a Proposed Privacy & Personal Data Protection Law by Aaron Kamath
(SACON) Shivangi Nadkarni & Sandeep Rao - An introduction to Data Privacy

Data Privacy & Personal Data Protection has become a key driver today in dialogues involving data. India is at the cusp of getting its own law in place - one of the last few countries in the world to do so. However, the reality on the ground is that few people really understand what Data Privacy is all about. It is often confused with Data Security. This session seeks to de-mystify Data Privacy, giving an overview of the domain and how it is different from Data Security.
Gigya's China Data Center - Data Sheet

New China Data Center Helps Gigya’s Clients Manage Compliance with New Chinese Cybersecurity Law.
As businesses expand into new markets to grow their customer bases through digital initiatives, compliance with widely variable data protection and privacy regulations is now one of the key competitive differentiators between industry leaders
and losers.
Checklist for SMEs for GDPR compliance

If you are in the UK and need to check that you will comply with the General Data Protection Regulations when they come into force in May 2018, this checklist might help. Developed for use in my own business it is shared without liability. Please use it wisely to start the process of complying.
For more information on making your processes and your legal documents simple, especially if you are in the UK construction industry, go to http://500words.co.uk/
Beyond GDPR Compliance - Role of Internal Audit

More than the requirement to comply with the regulation, GDPR encourages good practices for data privacy and data protection beyond May 2018. This slide deck shares examples of areas where Internal Audit can play a significant role in ensuring that the right controls are built-in at the front-end of the compliance journey. This is in-line with the increasing expectation from stakeholders for IA to add value to more strategic areas of risk to the business.
Finding Data at Risk for CCPA Compliance

Do you have customers residing in California? If so, you need to prepare yourself for the California Consumer Privacy Act (CCPA) going into effect in January 2020. CCPA mandates data privacy protection for California consumers much like GDPR. Personal information for consumers, households, and devices is covered and it is broadly applied. It’s not just names and addresses or personal identifiers like driver’s license and social security number but includes: geolocation data; records of personal property; products or services purchased, obtained, or even considered for purchase; browsing history; education information; professional information; and more. And you need to know where all that information is.
In order to ensure compliance, it’s time to put data profiling to work! You need rapid insight into your data sources whether on traditional platforms or in your data lake, and you need to find the outliers, not just cursory review of data samples, that help you ensure you’ve identified all the places this information has spread to as the information has been copied, reported, and delivered from central data stores.
View this webinar on-demand where we talk through some of the salient points of CCPA and show you how to leverage Trillium Discovery to profile, assess, and evaluate the data sources to find this data at risk.
BigID Data Sheet: Enterprise Privacy Management

Privacy management in the digital age hinges on direct knowledge of whose data organizations collect and process. Designed to address the foundational - and most challenging - aspects of enterprise privacy management, BigID puts the person front and center in how organizations inventory personal information and data, manage data rights, maintain accurate record keeping and mitigate privacy risk. Even as organizations deal with a deluge of data, BigID enables Customer to center discovery,
inventorying and indexing by person in order to respond
to compliance requirements, threats to personal data, and customer expectations of privacy.
BigID Consent Governance 

How to centrally manage consent distributed across de-centralized different systems
BigID Data Sheet: Data subject rights

The EU General Data Protection Regulation is the first compliance mandate to explicitly require that data subjects have access to all the personal data that a covered entity stores about them, and the ability to modify and delete the data. Traditional discovery tools can determine where personally identifiable information (PII) is stored by type of data source, but now whose data is being processed, or even what constitutes personal information (PI) under the GDPR’s definition. BigID’s correlation and machine learning uniquely provide a comprehensive map by data subject of all personal and private data across platforms with indexing of the locations of data values in order to operationalize GDPR Data Subject Access rights.
BigID Data Sheet: Master Your Customer Data Without MDM

Centralize Your Customer View Without Centralizing Your Data:
Traditional methods for building a master data view of customers is complex and costly. It requires an enterprise-wide effort to merge and normalize dispersed data sets to create a single master view of customers and clients. More process than product, today’s MDM efforts can take years and require constant resourcing to maintain in an evolving business and IT environment. Worse, the centralization introduces new security hazards that risk business reputation and untold liability in the event of a breach. BigID provides an alternative. The BigID solution provides a virtual data hub for identity data. A customer’s or client’s data can be mapped at petabyte scale across structured, unstructured, Big Data, cloud and apps without centralization
Internal vs. external identity access management

Strategies to develop an end-to-end customer data management framework.
More Related Content
What's hot
BigID Virtual MDM Data Sheet

BigID provides the industry first virtual Master Data Management system that allows companies to easily create a centralized view across a customer's data without centralizing the data.
BigID Data Subject Rights Automation for GDPR & Privacy Data Sheet

Read how BigID helps organizations operationalized GDPR and privacy personal data rights by helping organizations fulfill data subject rights like right-to-be-forgotten, right-to-access, right-to-portability, and right-to-rectification. BigID is the first software discovery tool that can leverage advanced ML and identity intelligence to find personal data anywhere and correlate it back to a person.
BigID GDPR Privacy Automation Data Sheet

BigID gives companies to automate core privacy and GDPR functions like data inventory, right-to-be-forgotten, consent, breach notification and Article 30 record keeling at scale.
BigID & Collibra Joint Deck: Using BigID’s Privacy-centric Data Discovery to...

This presentation was shown at this year's Collibra Data Citizens Conference in New York.
BigID's Smart Data Labeling and Tagging

Modern data protection and privacy rests on accurate data classification and labeling for smarter more accurate enforcement. BigID's award-winning sensitive data discovery and tagging provides a first of its kind ability to accurately find and secure personal data.
BigID Enterprise Privacy Management Data Sheet

Read how BigID redefines privacy management from surveys and spreadsheets to data-driven compliance built on actual data. Using BigID, organizations can more easily meet global privacy requirements while also safeguarding personal data across the enterprise.
BigID PII & PI Discovery for GDPR Data Sheet

Finding PII across structured, unstructured, Big Data, Cloud and applications is hard. Finding all PI (personal information) as required by GDPR and the California Consumer Privacy Act is harder. Regular Expression is not enough. BigID's patented machine learning makes discovery of contextual PI and correlation back to a person possible for the first time.
(SACON) Nandan Nilekani - Identity Payments and Data Empowerment 

Identity Payments and Data Empowerment Addressing Different challenges, Solving the Challenges, Payment challenges, Data Sharing and Privacy Challenges.
Putting in perspective: Innovation in digital age.
Collibra Data Citizen '19 - Bridging Data Privacy with Data Governance 

This presentation was shown at the 2019 Collibra Data Citizen Event in New York City.
Presented by Nimrod Vax, Chief Product Officer & Co-Founder & Joaquin Sufuentes, Lead Architect, Metadata Managment and Personal Infomation Protection, enterprise Data Managment, Intel IT
BigID GDPR Compliance Automation Webinar Slides

This Webinar featuring guests from the EU Commission, the French data regulator CNIL, DLA Piper and IBM provided an overview of the new EU data protection and privacy perspective from the perspective of the regulation author, regulator, legal advisor and technology providers.
India'a Proposed Privacy & Personal Data Protection Law 

India'a Proposed Privacy & Personal Data Protection Law by Aaron Kamath
(SACON) Shivangi Nadkarni & Sandeep Rao - An introduction to Data Privacy

Data Privacy & Personal Data Protection has become a key driver today in dialogues involving data. India is at the cusp of getting its own law in place - one of the last few countries in the world to do so. However, the reality on the ground is that few people really understand what Data Privacy is all about. It is often confused with Data Security. This session seeks to de-mystify Data Privacy, giving an overview of the domain and how it is different from Data Security.
Gigya's China Data Center - Data Sheet

New China Data Center Helps Gigya’s Clients Manage Compliance with New Chinese Cybersecurity Law.
As businesses expand into new markets to grow their customer bases through digital initiatives, compliance with widely variable data protection and privacy regulations is now one of the key competitive differentiators between industry leaders
and losers.
Checklist for SMEs for GDPR compliance

If you are in the UK and need to check that you will comply with the General Data Protection Regulations when they come into force in May 2018, this checklist might help. Developed for use in my own business it is shared without liability. Please use it wisely to start the process of complying.
For more information on making your processes and your legal documents simple, especially if you are in the UK construction industry, go to http://500words.co.uk/
Beyond GDPR Compliance - Role of Internal Audit

More than the requirement to comply with the regulation, GDPR encourages good practices for data privacy and data protection beyond May 2018. This slide deck shares examples of areas where Internal Audit can play a significant role in ensuring that the right controls are built-in at the front-end of the compliance journey. This is in-line with the increasing expectation from stakeholders for IA to add value to more strategic areas of risk to the business.
Finding Data at Risk for CCPA Compliance

Do you have customers residing in California? If so, you need to prepare yourself for the California Consumer Privacy Act (CCPA) going into effect in January 2020. CCPA mandates data privacy protection for California consumers much like GDPR. Personal information for consumers, households, and devices is covered and it is broadly applied. It’s not just names and addresses or personal identifiers like driver’s license and social security number but includes: geolocation data; records of personal property; products or services purchased, obtained, or even considered for purchase; browsing history; education information; professional information; and more. And you need to know where all that information is.
In order to ensure compliance, it’s time to put data profiling to work! You need rapid insight into your data sources whether on traditional platforms or in your data lake, and you need to find the outliers, not just cursory review of data samples, that help you ensure you’ve identified all the places this information has spread to as the information has been copied, reported, and delivered from central data stores.
View this webinar on-demand where we talk through some of the salient points of CCPA and show you how to leverage Trillium Discovery to profile, assess, and evaluate the data sources to find this data at risk.
What's hot (17)
BigID Data Subject Rights Automation for GDPR & Privacy Data Sheet

BigID Data Subject Rights Automation for GDPR & Privacy Data Sheet
BigID & Collibra Joint Deck: Using BigID’s Privacy-centric Data Discovery to...

BigID & Collibra Joint Deck: Using BigID’s Privacy-centric Data Discovery to...
(SACON) Nandan Nilekani - Identity Payments and Data Empowerment 

(SACON) Nandan Nilekani - Identity Payments and Data Empowerment
Collibra Data Citizen '19 - Bridging Data Privacy with Data Governance 

Collibra Data Citizen '19 - Bridging Data Privacy with Data Governance
India'a Proposed Privacy & Personal Data Protection Law 

India'a Proposed Privacy & Personal Data Protection Law
(SACON) Shivangi Nadkarni & Sandeep Rao - An introduction to Data Privacy

(SACON) Shivangi Nadkarni & Sandeep Rao - An introduction to Data Privacy
Similar to BigID Datasheet: CCPA Data Rights Automation
BigID Data Sheet: Enterprise Privacy Management

Privacy management in the digital age hinges on direct knowledge of whose data organizations collect and process. Designed to address the foundational - and most challenging - aspects of enterprise privacy management, BigID puts the person front and center in how organizations inventory personal information and data, manage data rights, maintain accurate record keeping and mitigate privacy risk. Even as organizations deal with a deluge of data, BigID enables Customer to center discovery,
inventorying and indexing by person in order to respond
to compliance requirements, threats to personal data, and customer expectations of privacy.
BigID Consent Governance 

How to centrally manage consent distributed across de-centralized different systems
BigID Data Sheet: Data subject rights

The EU General Data Protection Regulation is the first compliance mandate to explicitly require that data subjects have access to all the personal data that a covered entity stores about them, and the ability to modify and delete the data. Traditional discovery tools can determine where personally identifiable information (PII) is stored by type of data source, but now whose data is being processed, or even what constitutes personal information (PI) under the GDPR’s definition. BigID’s correlation and machine learning uniquely provide a comprehensive map by data subject of all personal and private data across platforms with indexing of the locations of data values in order to operationalize GDPR Data Subject Access rights.
BigID Data Sheet: Master Your Customer Data Without MDM

Centralize Your Customer View Without Centralizing Your Data:
Traditional methods for building a master data view of customers is complex and costly. It requires an enterprise-wide effort to merge and normalize dispersed data sets to create a single master view of customers and clients. More process than product, today’s MDM efforts can take years and require constant resourcing to maintain in an evolving business and IT environment. Worse, the centralization introduces new security hazards that risk business reputation and untold liability in the event of a breach. BigID provides an alternative. The BigID solution provides a virtual data hub for identity data. A customer’s or client’s data can be mapped at petabyte scale across structured, unstructured, Big Data, cloud and apps without centralization
Internal vs. external identity access management

Strategies to develop an end-to-end customer data management framework.
White Paper: Internal vs. External Identity Access Management 

Customer identity and access management (CIAM)
BigId GDPRcompliance

Automate the security and management of structured and unstructured PII across data centers and cloud.
BigID PII Protection GDPR 

How to automate the security and management of structured and unstructured PII across data centers and cloud.
data-dilemma-navigating-the-legal-and-ethical-maze-of-big-data-2023-5-25-7-18...

data-dilemma-navigating-the-legal-and-ethical-maze-of-big-data-2023-5-25-7-18...Data & Analytics Magazin
As we dive deeper into the world of big data, the legal and ethical obstacles we face become increasingly complex. It's like trying to navigate a maze made of legal documents and moral dilemmas...in the dark...while blindfolded. Okay, maybe it's not that bad, but you get the picture. From privacy concerns to potential biases, there's a lot to consider. It's like a choose-your-own-adventure book, except the choices could land you in court. So, buckle up and get ready for the ride, because the data dilemma maze is not for the faint of heart.The GDPR - A data revolution

Here's a short presentation on the GDPR, first presented at the Morning Advertiser MA500 event in Edinburgh on 14th September. This is an overview regulations.
Rethinking Trust in Data 

The explosive growth of data and the value it creates calls on data professionals to level up their programs to build, demonstrate, and maintain trust. The days of fine print, pre-ticked boxes, and data hoarding are gone and strong collaboration from data, privacy, marketing and ethics teams is necessary to design trustworthy data-driven practices.
Join for a discussion on the latest trends in trusted data and how you can take critical steps to build trust in data practices by:
- Embedding privacy by design into data operations
- Respecting individual choice and optimizing the ongoing relationship with consumers
- Preparing for future data challenges including responsible AI and sustainability
Three big questions about AI in financial services

To ride the rising wave of AI, financial services companies will have to navigate evolving standards, regulations and risk dynamics—particularly regarding data rights, algorithmic accountability and cybersecurity.
White Paper: The Evolution of Consumer Identity - Five Predictions for 2016

2016 promises to be a year of enhanced development in the customer identity and access management (CIAM) space, with customer experience, data privacy and personalization proving to be increasingly critical components of business success. This white paper reveals five identity-related trends we foresee taking hold in the new year, including:
- The death of traditional usernames and passwords
- The decline of data broker revenues
- The convergence of security and customer experience
GDPR: the IBM journey to compliance

As one of the largest processors and controllers of global information, IBM has embarked on a global program towards GDPR compliance readiness. Using the same methodology, services, and solutions as it does with clients, this session will demonstrate how this process can serve as a model for GDPR for any large enterprise. How this model can then be a basis to help comply with all other regulatory needs and be a framework for future business transformation and opportunity. Specifics will include:
• A summary to the needs and opportunities of the GDPR regulation
• With the time left, where are you, what can still be done
• A prescriptive phased methodology of execution
• Core solution technical measures and capabilities
• Key GDPR actionable outcomes by stakeholder
The focus is on discovering, mapping, and managing personal data for GDPR, along with data protection and compliance, on Hadoop in a sustainable way.
Speaker
Richard Hogg, Global GDPR Evangelist, IBM
For digital media companies, effective cybersecurity programs a must

In digital media trust is everything, without it your business model doesn’t work. Cybersecurity can be a key component, ensuring the integrity of your services. Check out this brief guide to securing your data.
General Data Protection Regulation & Customer IAM

The “General Data Protection & Customer IAM” white paper outlines the legal premise of the GDPR, and then delves into the specific parts where Customer Identity and Access Management solutions can help your organisation.
FIDO Authentication and GDPR

The General Data Protection Regulation (GDPR) come into effect earlier this year, ushering in the most significant change to European data protection laws in twenty years. The regulation impacts not only impact firms resident in the European Union (EU), but around the world, as any organization doing business with EU citizens must comply with the regulation.
FIDO Alliance standards were created from the outset with a “privacy by design” approach and are a strong fit for GDPR compliance. Crucially, FIDO delivers authentication with no third-party involvement or tracking between accounts and services. And when it comes to biometrics, FIDO standards prevent this information from being stored and matched in servers – it never leaves the user’s device – and FIDO(R) Certified devices do not allow for any biometric data to be captured.
This presentation includes:
- Key GDPR considerations when deploying strong authentication
- Where FIDO Authentication relates to GDPR articles on data protection, consent of data subject and data subject rights
- How FIDO can help your organization meet GDPR requirements
Similar to BigID Datasheet: CCPA Data Rights Automation (20)
BigID Data Sheet: Master Your Customer Data Without MDM

BigID Data Sheet: Master Your Customer Data Without MDM
White Paper: Internal vs. External Identity Access Management 

White Paper: Internal vs. External Identity Access Management
data-dilemma-navigating-the-legal-and-ethical-maze-of-big-data-2023-5-25-7-18...

data-dilemma-navigating-the-legal-and-ethical-maze-of-big-data-2023-5-25-7-18...
Three big questions about AI in financial services

Three big questions about AI in financial services
White Paper: The Evolution of Consumer Identity - Five Predictions for 2016

White Paper: The Evolution of Consumer Identity - Five Predictions for 2016
For digital media companies, effective cybersecurity programs a must

For digital media companies, effective cybersecurity programs a must
Recently uploaded
Lecture 1 Introduction to games development

Software engineering
Game Development
unity Game Development
GlobusWorld 2024 Opening Keynote session

Listen to the keynote address and hear about the latest developments from Rachana Ananthakrishnan and Ian Foster who review the updates to the Globus Platform and Service, and the relevance of Globus to the scientific community as an automation platform to accelerate scientific discovery.
BoxLang: Review our Visionary Licenses of 2024

Unleash Unlimited Potential with One-Time Purchase
BoxLang is more than just a language; it's a community. By choosing a Visionary License, you're not just investing in your success, you're actively contributing to the ongoing development and support of BoxLang.
Multiple Your Crypto Portfolio with the Innovative Features of Advanced Crypt...

Multiple Your Crypto Portfolio with the Innovative Features of Advanced Crypt...Hivelance Technology
Cryptocurrency trading bots are computer programs designed to automate buying, selling, and managing cryptocurrency transactions. These bots utilize advanced algorithms and machine learning techniques to analyze market data, identify trading opportunities, and execute trades on behalf of their users. By automating the decision-making process, crypto trading bots can react to market changes faster than human traders
Hivelance, a leading provider of cryptocurrency trading bot development services, stands out as the premier choice for crypto traders and developers. Hivelance boasts a team of seasoned cryptocurrency experts and software engineers who deeply understand the crypto market and the latest trends in automated trading, Hivelance leverages the latest technologies and tools in the industry, including advanced AI and machine learning algorithms, to create highly efficient and adaptable crypto trading botsVitthal Shirke Microservices Resume Montevideo

Software Engineering, Software Consulting, Tech Lead.
Spring Boot, Spring Cloud, Spring Core, Spring JDBC, Spring Security,
Spring Transaction, Spring MVC,
Log4j, REST/SOAP WEB-SERVICES.
Visitor Management System in India- Vizman.app

Your Digital Assistant.
Making complex approach simple. Straightforward process saves time. No more waiting to connect with people that matter to you. Safety first is not a cliché - Securely protect information in cloud storage to prevent any third party from accessing data.
Would you rather make your visitors feel burdened by making them wait? Or choose VizMan for a stress-free experience? VizMan is an automated visitor management system that works for any industries not limited to factories, societies, government institutes, and warehouses. A new age contactless way of logging information of visitors, employees, packages, and vehicles. VizMan is a digital logbook so it deters unnecessary use of paper or space since there is no requirement of bundles of registers that is left to collect dust in a corner of a room. Visitor’s essential details, helps in scheduling meetings for visitors and employees, and assists in supervising the attendance of the employees. With VizMan, visitors don’t need to wait for hours in long queues. VizMan handles visitors with the value they deserve because we know time is important to you.
Feasible Features
One Subscription, Four Modules – Admin, Employee, Receptionist, and Gatekeeper ensures confidentiality and prevents data from being manipulated
User Friendly – can be easily used on Android, iOS, and Web Interface
Multiple Accessibility – Log in through any device from any place at any time
One app for all industries – a Visitor Management System that works for any organisation.
Stress-free Sign-up
Visitor is registered and checked-in by the Receptionist
Host gets a notification, where they opt to Approve the meeting
Host notifies the Receptionist of the end of the meeting
Visitor is checked-out by the Receptionist
Host enters notes and remarks of the meeting
Customizable Components
Scheduling Meetings – Host can invite visitors for meetings and also approve, reject and reschedule meetings
Single/Bulk invites – Invitations can be sent individually to a visitor or collectively to many visitors
VIP Visitors – Additional security of data for VIP visitors to avoid misuse of information
Courier Management – Keeps a check on deliveries like commodities being delivered in and out of establishments
Alerts & Notifications – Get notified on SMS, email, and application
Parking Management – Manage availability of parking space
Individual log-in – Every user has their own log-in id
Visitor/Meeting Analytics – Evaluate notes and remarks of the meeting stored in the system
Visitor Management System is a secure and user friendly database manager that records, filters, tracks the visitors to your organization.
"Secure Your Premises with VizMan (VMS) – Get It Now"
In 2015, I used to write extensions for Joomla, WordPress, phpBB3, etc and I ...

In 2015, I used to write extensions for Joomla, WordPress, phpBB3, etc and I didn't get rich from it but it did have 63K downloads (powered possible tens of thousands of websites).
Quarkus Hidden and Forbidden Extensions

Quarkus has a vast extension ecosystem and is known for its subsonic and subatomic feature set. Some of these features are not as well known, and some extensions are less talked about, but that does not make them less interesting - quite the opposite.
Come join this talk to see some tips and tricks for using Quarkus and some of the lesser known features, extensions and development techniques.
top nidhi software solution freedownload

This presentation emphasizes the importance of data security and legal compliance for Nidhi companies in India. It highlights how online Nidhi software solutions, like Vector Nidhi Software, offer advanced features tailored to these needs. Key aspects include encryption, access controls, and audit trails to ensure data security. The software complies with regulatory guidelines from the MCA and RBI and adheres to Nidhi Rules, 2014. With customizable, user-friendly interfaces and real-time features, these Nidhi software solutions enhance efficiency, support growth, and provide exceptional member services. The presentation concludes with contact information for further inquiries.
Strategies for Successful Data Migration Tools.pptx

Data migration is a complex but essential task for organizations aiming to modernize their IT infrastructure and leverage new technologies. By understanding common challenges and implementing these strategies, businesses can achieve a successful migration with minimal disruption. Data Migration Tool like Ask On Data play a pivotal role in this journey, offering features that streamline the process, ensure data integrity, and maintain security. With the right approach and tools, organizations can turn the challenge of data migration into an opportunity for growth and innovation.
De mooiste recreatieve routes ontdekken met RouteYou en FME

FME Innovation Day - presented by Nordend.
"De mooiste recreatieve routes ontdekken met RouteYou en FME." door Kevin Baker
2024 RoOUG Security model for the cloud.pptx

How we've evolved the MySQL server security model from a single DBA to the cloud.
Innovating Inference - Remote Triggering of Large Language Models on HPC Clus...

Large Language Models (LLMs) are currently the center of attention in the tech world, particularly for their potential to advance research. In this presentation, we'll explore a straightforward and effective method for quickly initiating inference runs on supercomputers using the vLLM tool with Globus Compute, specifically on the Polaris system at ALCF. We'll begin by briefly discussing the popularity and applications of LLMs in various fields. Following this, we will introduce the vLLM tool, and explain how it integrates with Globus Compute to efficiently manage LLM operations on Polaris. Attendees will learn the practical aspects of setting up and remotely triggering LLMs from local machines, focusing on ease of use and efficiency. This talk is ideal for researchers and practitioners looking to leverage the power of LLMs in their work, offering a clear guide to harnessing supercomputing resources for quick and effective LLM inference.
Dominate Social Media with TubeTrivia AI’s Addictive Quiz Videos.pdf

Dominate Social Media with TubeTrivia AI’s Addictive Quiz Videos
https://www.amb-review.com/tubetrivia-ai
Exclusive Features:
AI-Powered Questions,
Wide Range of Categories,
Adaptive Difficulty,
User-Friendly Interface,
Multiplayer Mode,
Regular Updates.
#TubeTriviaAI
#QuizVideoMagic
#ViralQuizVideos
#AIQuizGenerator
#EngageExciteExplode
#MarketingRevolution
#BoostYourTraffic
#SocialMediaSuccess
#AIContentCreation
#UnlimitedTraffic
Globus Connect Server Deep Dive - GlobusWorld 2024

We explore the Globus Connect Server (GCS) architecture and experiment with advanced configuration options and use cases. This content is targeted at system administrators who are familiar with GCS and currently operate—or are planning to operate—broader deployments at their institution.
WSO2Con2024 - WSO2's IAM Vision: Identity-Led Digital Transformation

WSO2Con2024 - WSO2's IAM Vision: Identity-Led Digital Transformation
Developing Distributed High-performance Computing Capabilities of an Open Sci...

COVID-19 had an unprecedented impact on scientific collaboration. The pandemic and its broad response from the scientific community has forged new relationships among public health practitioners, mathematical modelers, and scientific computing specialists, while revealing critical gaps in exploiting advanced computing systems to support urgent decision making. Informed by our team’s work in applying high-performance computing in support of public health decision makers during the COVID-19 pandemic, we present how Globus technologies are enabling the development of an open science platform for robust epidemic analysis, with the goal of collaborative, secure, distributed, on-demand, and fast time-to-solution analyses to support public health.
Beyond Event Sourcing - Embracing CRUD for Wix Platform - Java.IL

In software engineering, the right architecture is essential for robust, scalable platforms. Wix has undergone a pivotal shift from event sourcing to a CRUD-based model for its microservices. This talk will chart the course of this pivotal journey.
Event sourcing, which records state changes as immutable events, provided robust auditing and "time travel" debugging for Wix Stores' microservices. Despite its benefits, the complexity it introduced in state management slowed development. Wix responded by adopting a simpler, unified CRUD model. This talk will explore the challenges of event sourcing and the advantages of Wix's new "CRUD on steroids" approach, which streamlines API integration and domain event management while preserving data integrity and system resilience.
Participants will gain valuable insights into Wix's strategies for ensuring atomicity in database updates and event production, as well as caching, materialization, and performance optimization techniques within a distributed system.
Join us to discover how Wix has mastered the art of balancing simplicity and extensibility, and learn how the re-adoption of the modest CRUD has turbocharged their development velocity, resilience, and scalability in a high-growth environment.
Accelerate Enterprise Software Engineering with Platformless

Key takeaways:
Challenges of building platforms and the benefits of platformless.
Key principles of platformless, including API-first, cloud-native middleware, platform engineering, and developer experience.
How Choreo enables the platformless experience.
How key concepts like application architecture, domain-driven design, zero trust, and cell-based architecture are inherently a part of Choreo.
Demo of an end-to-end app built and deployed on Choreo.
Recently uploaded (20)
Multiple Your Crypto Portfolio with the Innovative Features of Advanced Crypt...

Multiple Your Crypto Portfolio with the Innovative Features of Advanced Crypt...
In 2015, I used to write extensions for Joomla, WordPress, phpBB3, etc and I ...

In 2015, I used to write extensions for Joomla, WordPress, phpBB3, etc and I ...
Strategies for Successful Data Migration Tools.pptx

Strategies for Successful Data Migration Tools.pptx
De mooiste recreatieve routes ontdekken met RouteYou en FME

De mooiste recreatieve routes ontdekken met RouteYou en FME
Innovating Inference - Remote Triggering of Large Language Models on HPC Clus...

Innovating Inference - Remote Triggering of Large Language Models on HPC Clus...
Dominate Social Media with TubeTrivia AI’s Addictive Quiz Videos.pdf

Dominate Social Media with TubeTrivia AI’s Addictive Quiz Videos.pdf
Globus Connect Server Deep Dive - GlobusWorld 2024

Globus Connect Server Deep Dive - GlobusWorld 2024
WSO2Con2024 - WSO2's IAM Vision: Identity-Led Digital Transformation

WSO2Con2024 - WSO2's IAM Vision: Identity-Led Digital Transformation
Developing Distributed High-performance Computing Capabilities of an Open Sci...

Developing Distributed High-performance Computing Capabilities of an Open Sci...
Beyond Event Sourcing - Embracing CRUD for Wix Platform - Java.IL

Beyond Event Sourcing - Embracing CRUD for Wix Platform - Java.IL
Accelerate Enterprise Software Engineering with Platformless

Accelerate Enterprise Software Engineering with Platformless
BigID Datasheet: CCPA Data Rights Automation
- 1. www.bigid.com • info@bigid.com • @bigidsecure Your Customers' Privacy, Protected! A Data Driven Approach for CCPA Preparedness CCPA Data Rights Automation When it comes into effect in July 1, 2020, the California Consumer Privacy Act (“CCPA”) will set the stage for a fundamental realignment in how covered companies interact with customer data. Under the law, California residents will, for the first time, be afforded the right to know what data is being collected about them, as well as how it’s being processed, shared and sold. BigID delivers the data intelligence foundation to discover personal information across an enterprise, index whose data it is and seamlessly operationalize privacy management processes. ML Driven Personal Data Discovery & Classification Unlike PCI DSS, or similar mandates which focus on Personally Identifiable Information only (such as Social Security Numbers or credit card details), the CCPA covers any data that “identifies, relates to, describes, is capable of being associated with, or could reasonably be linked” to a person or household is deemed personal data. BigID uses innovative correlation and identity intelligence to establish how identifiable data relates to a consumer identity, helping to uncover “dark data” and infer via correlation which attributes are associated with California consumers for inventorying and potential de-identification. Existing discovery and classification approaches cannot address the new requirement to understand whose data is being collected, processed and shared - and typically cannot scan and discover personal data across the modern data landscape spanning databases, file shares, logs, big data and cloud services. Your Customers' Privacy, Protected! What truly distinguishes the CCPA from an operations perspective is that the Act requires companies to account for how they collect and sell individual customer’s information and support the consumer’s right to access of all the personal collected, processed and shared. BigID’s correlation and machine learning technology uniquely finds personal information across the enterprise that is linked or linkable to an individual California consumer and automatically assigns state residency without having to move any data. Support teams can generate consumer access request reports through a single click, and natural language queries enable them to match the consumer request to their data graph. The BigID product further enables enterprises to make individualized processing decisions, with the ability to match opt-out requests to a specific consumer and his or her associated data. Operationalize and Automate Consumer Data Rights
- 2. www.bigid.com • info@bigid.com • @bigidsecure Your Customers' Privacy, Protected! Inventory Processing and Data Flow Maps As a direct consequence of the of consumer data rights that the CCPA introduces - including the Right to Know, the Right to Access and the Right to Delete - covered companies will be required to maintain an inventory of processing activities. For enterprises with complex data collection and processing, it will be important to get a picture of what personal information is collected and how it is used in a verifiable, data-driven way. The BigID product compiles an index of all personal information and confidential data that points to where specific data values are stored, and it facilitates the automated and collaborative building of an inventory of processing activities. BigID is redefining personal data protection and privacy in the enterprise. Organizations are facing record breaches of personal information and proliferating global privacy regulations, with fines reaching 4% of annual revenue. BigID gives enterprises software to automate the security and management of structured and unstructured PI across datacenters and cloud. Using BigID, enterprises can better steward their most vital assets: their customer, employee and client data. For more information, email info@bigid.com or schedule a demo at bigid.com/demo How BigID Can Help Your Customers' Privacy, Protected! Along with potential penalties and fines levied by the California Attorney General for violations, the CCPA introduces a “right to private action”, and in particular to sue if a breach is the result of the company not taking “reasonable security procedures and practices.” Based on BigID’s mapping of personal data, security teams can better understand their data breach risk and orchestrate security controls through APIs such as encryption or de-identification. In the event of an incident or data breach, Security and IT can quickly scope the impact and understand which consumer identities and attributes have been impacted by a breach based on BigID’s inventory of personal data and consumer identity by data source. Risk Analysis and Breach Assessment A Data Driven Approach for CCPA Preparedness
