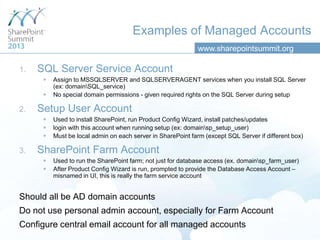
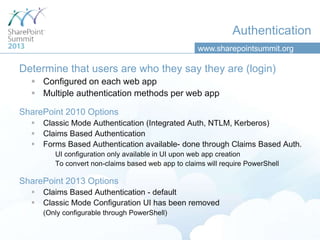
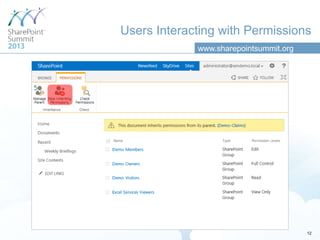
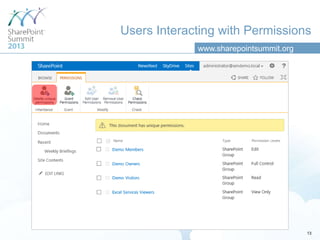
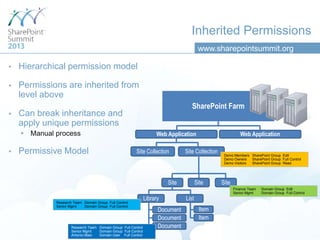
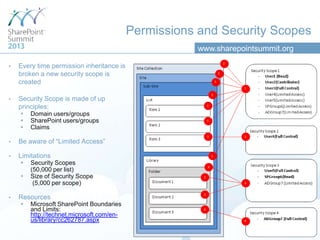
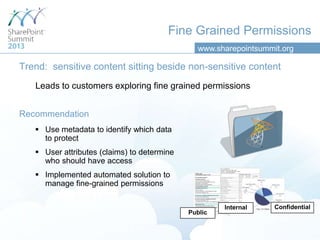
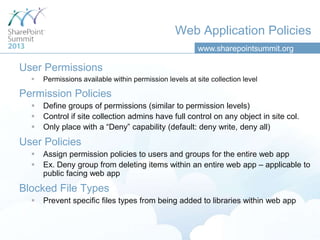
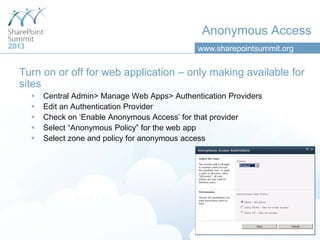
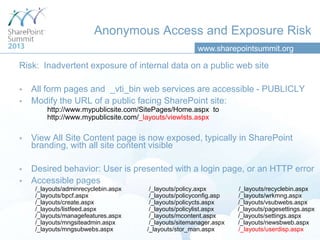
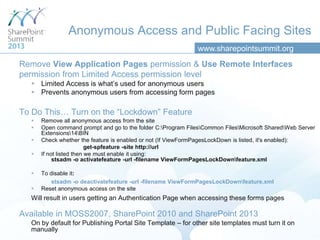
This document discusses best practices for security in Microsoft SharePoint 2013. It recommends using specific managed accounts with least privileges for SQL Server, installing and configuring SharePoint, and running the SharePoint farm. Authentication should be claims-based and permissions should be assigned through inheritance and security scopes. Web application policies allow controlling permissions and access across an entire web application. Public websites require carefully configuring anonymous access and locking down access to _layouts pages and web services. Other security features discussed include information rights management, auditing, and privileged users.