WebSockets allow for two-way communication between a client and server using a single connection. They provide a more efficient alternative to previous solutions like long-polling that required separate connections. While WebSockets improve performance, they also introduce some security concerns due to their ability to establish persistent connections that bypass some cross-origin protections. Attackers could potentially abuse WebSockets to conduct denial of service attacks or inject malicious content into connections. Web developers need to ensure proper security practices like using TLS to prevent issues with mixed content or connection interception.

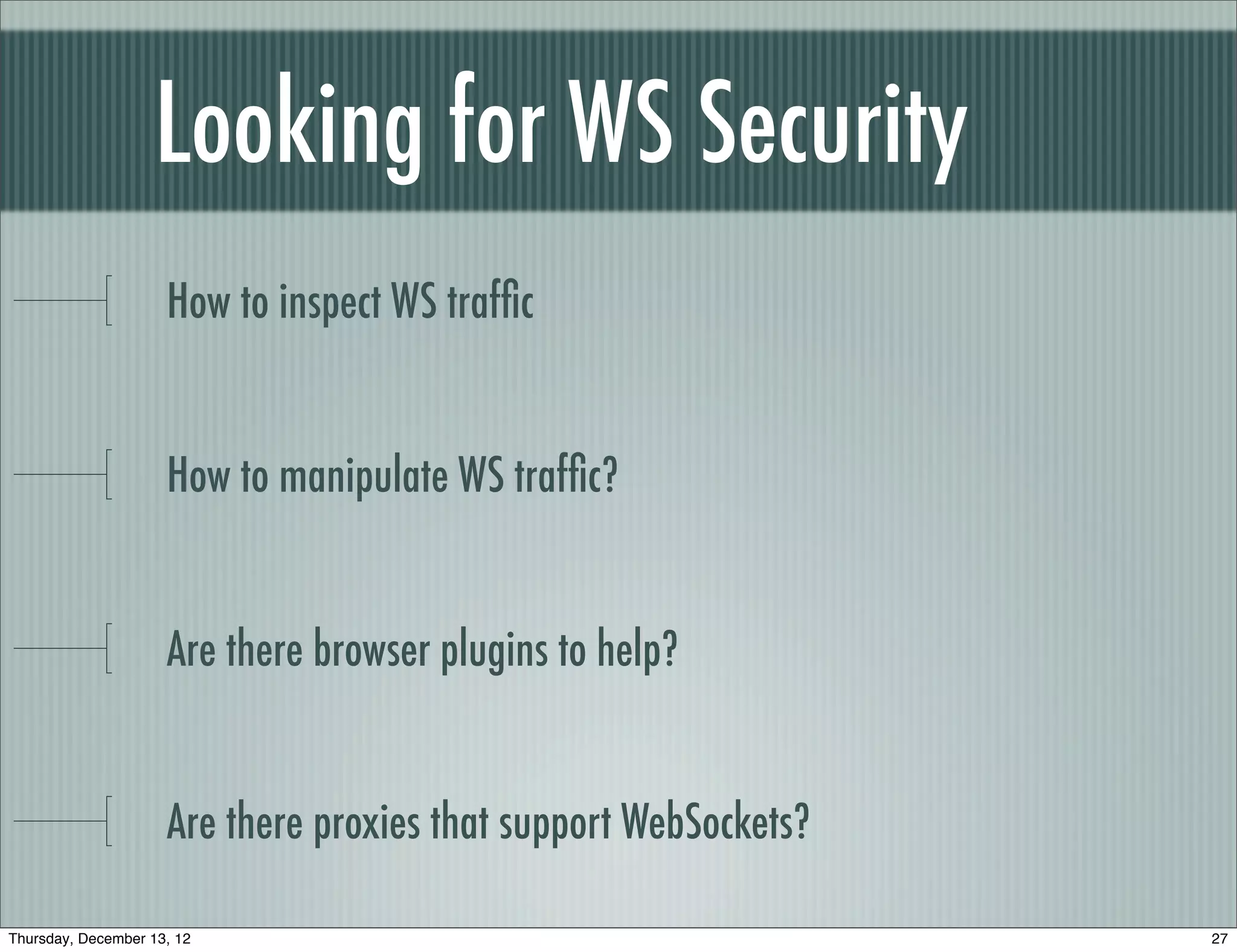
![Handshake Response
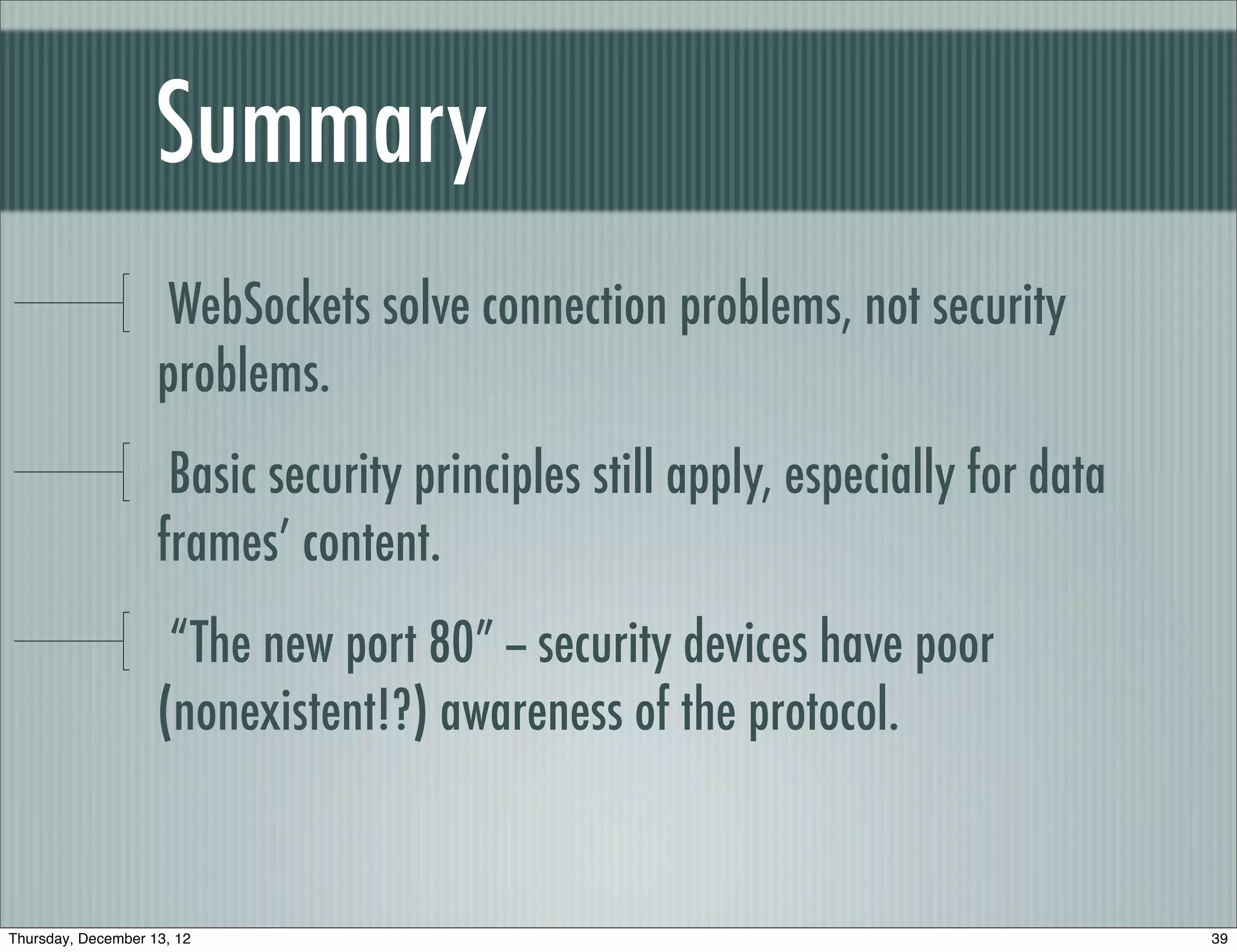
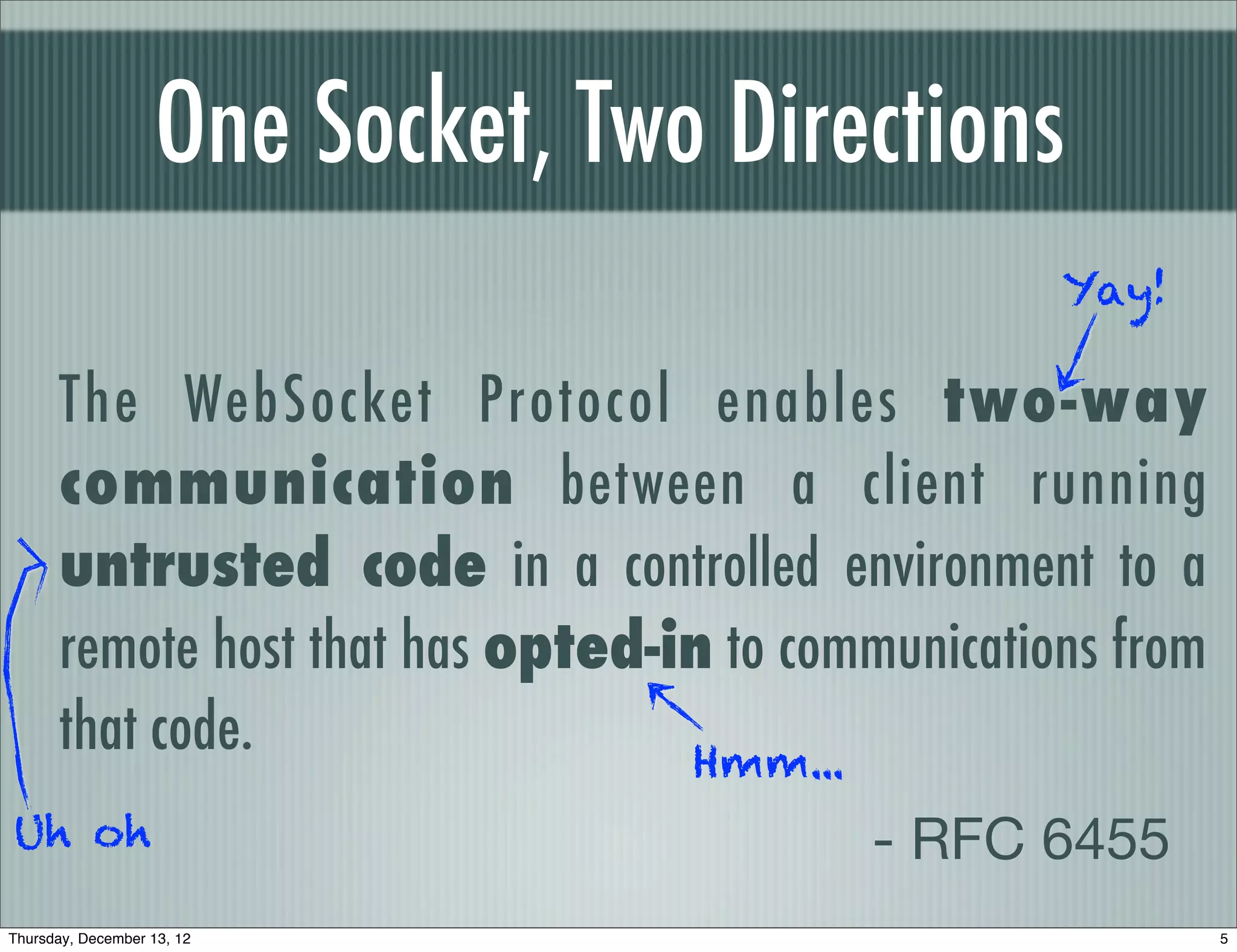
HTTP/1.1 101 Switching Protocols
Upgrade: WebSocket Proxy might
Connection: Upgrade remove this!
Sec-WebSocket-Accept: c4RVZSknSoEHizZu6BKl3v
+xUuI=
base64(SHA1(challenge + GUID)
[ then the data frames begin ]
Thursday, December 13, 12 8](https://image.slidesharecdn.com/baythreat2012websockets-121214005725-phpapp02/75/Hacking-with-WebSockets-8-2048.jpg)
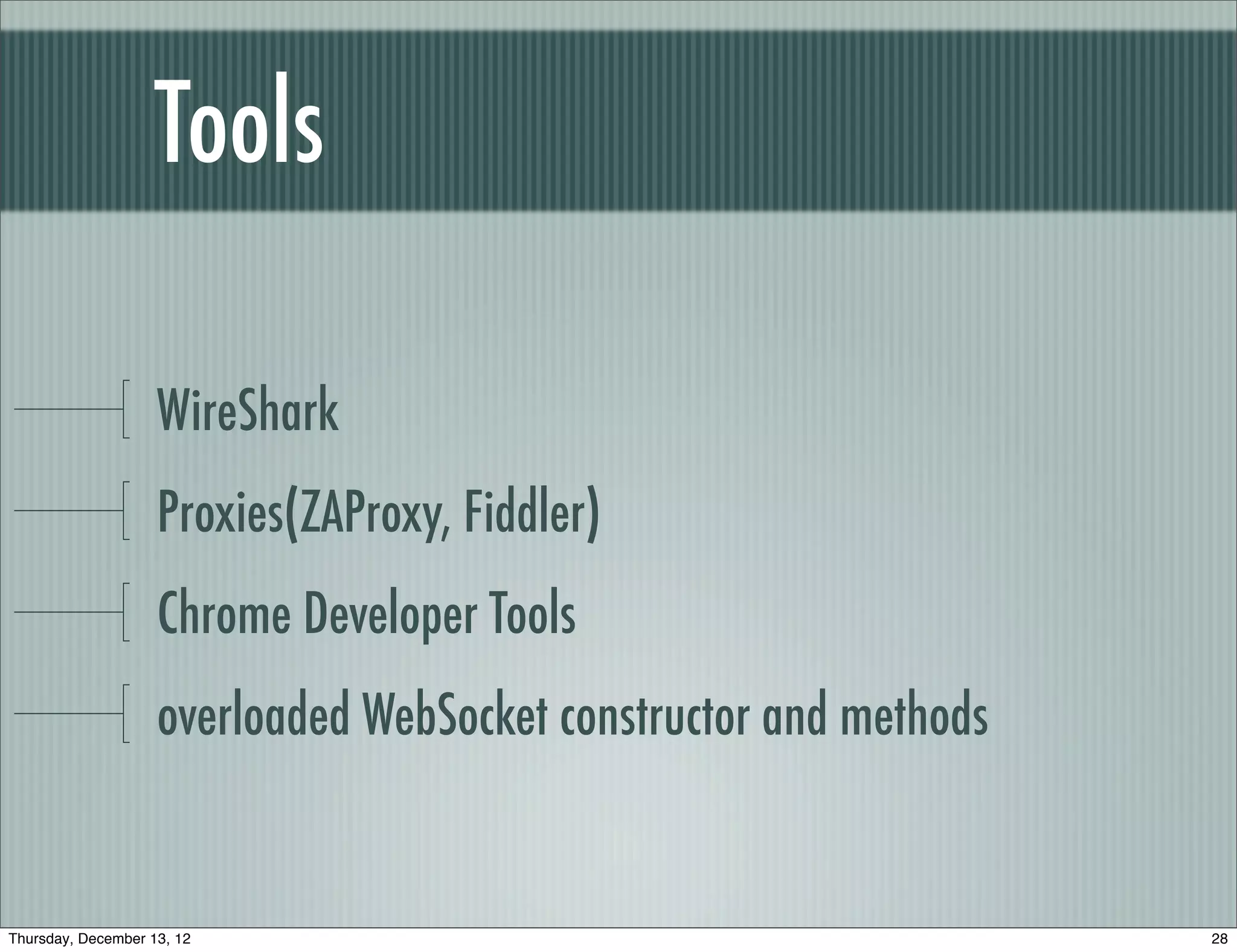
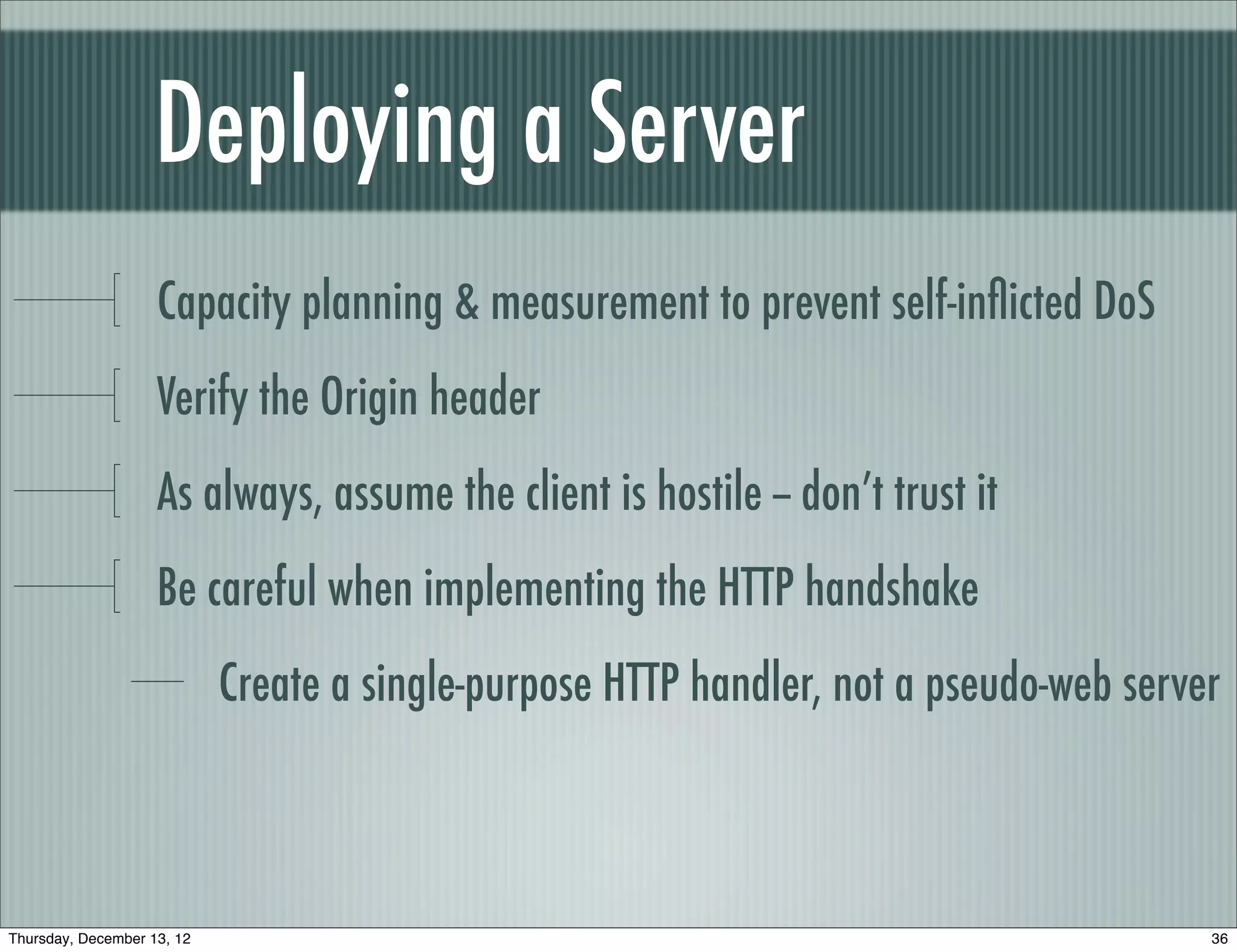
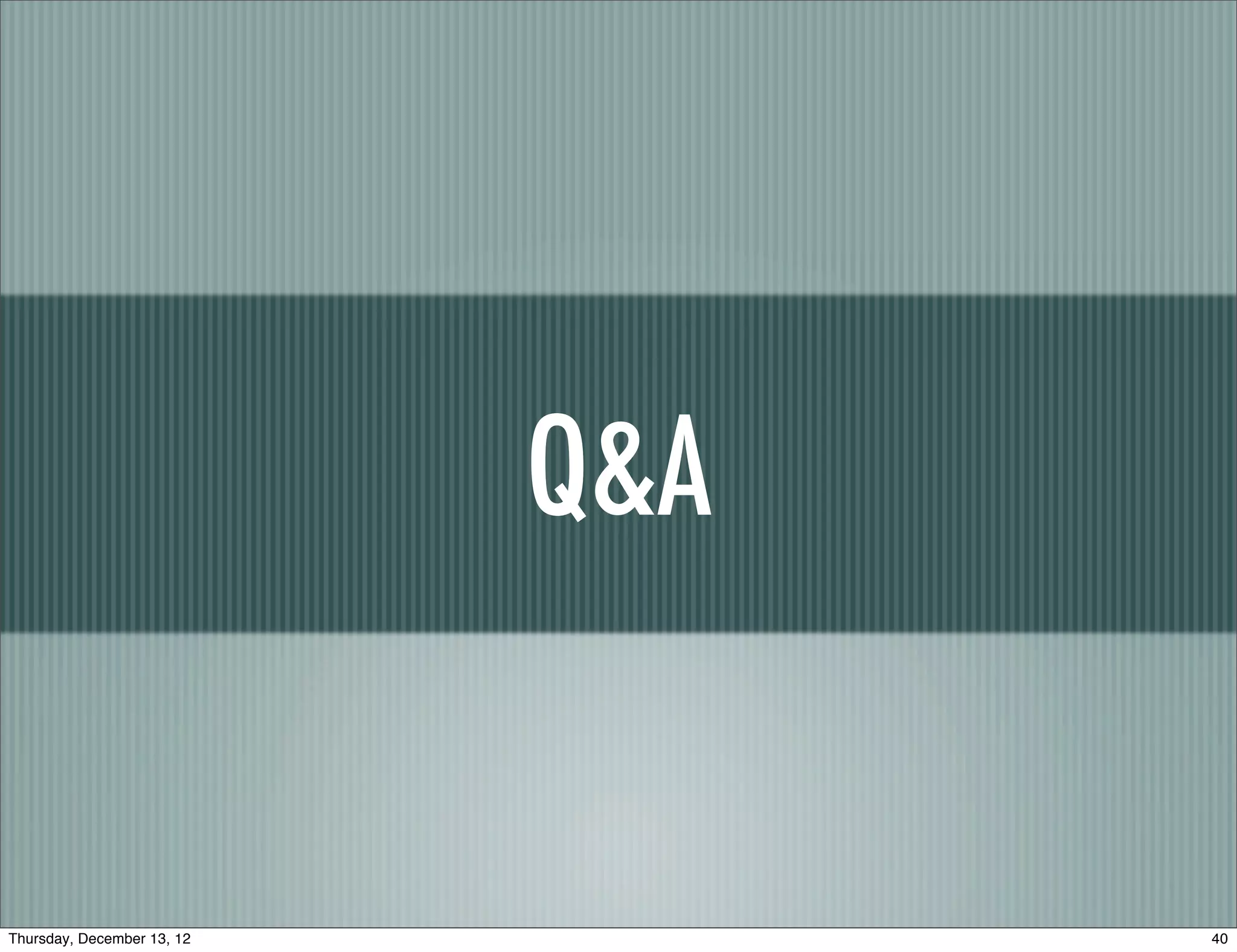
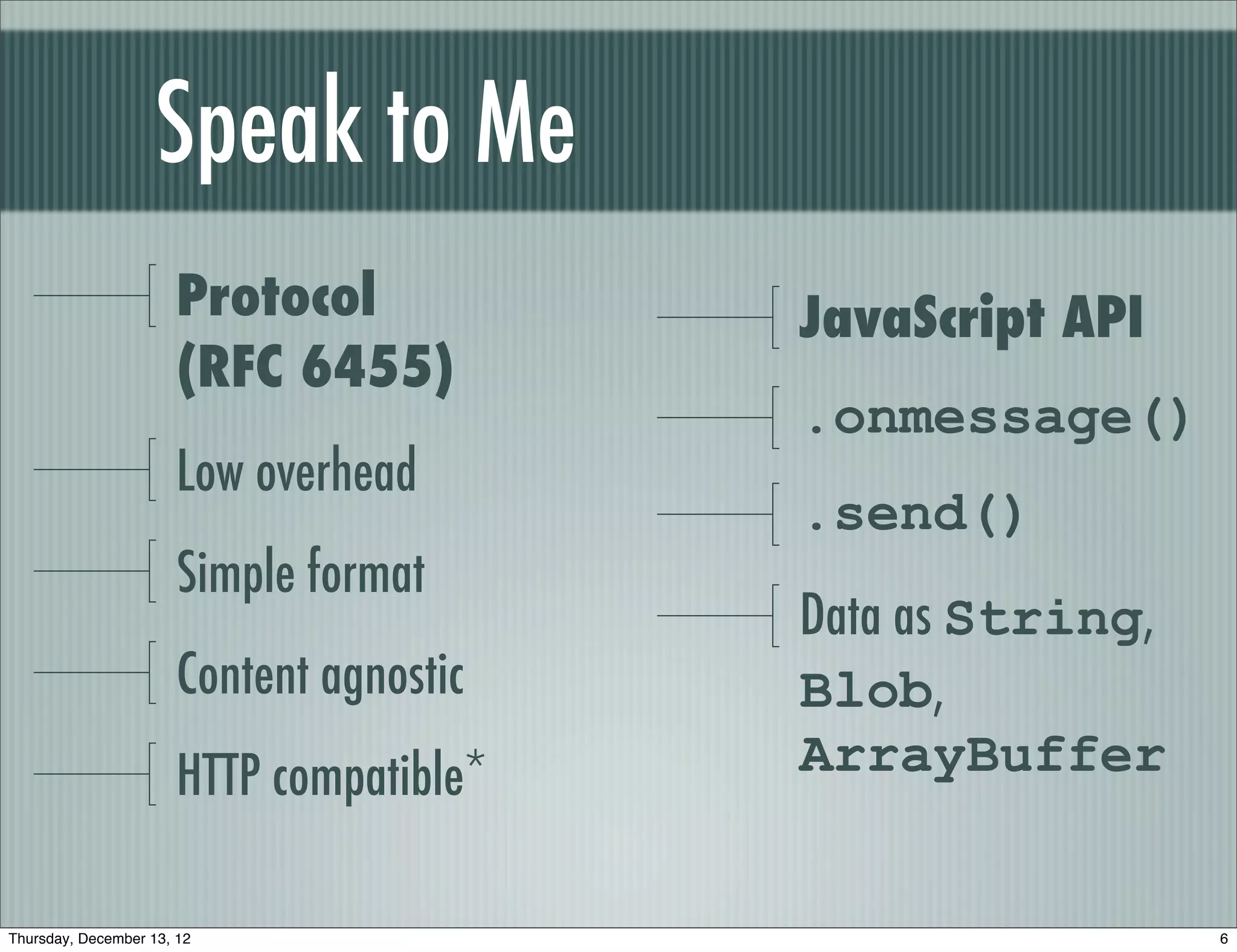
![src 10.171.90.44
dst 174.129.224.73
options []
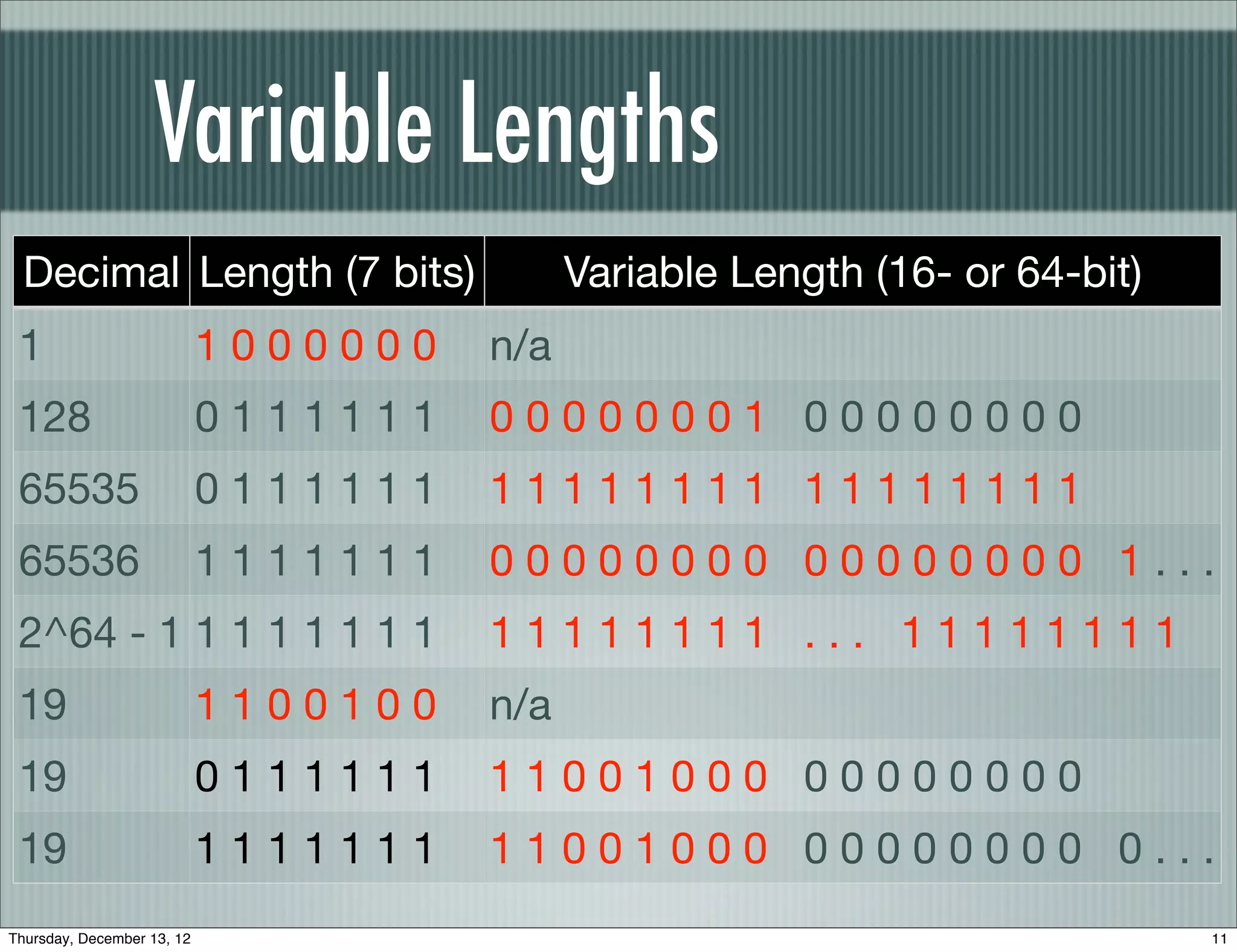
Masking Data
TCP
sport 63784
dport http
f9 28 00 50 fb 51 8d 7f ea d5 21 21 80 18
seq 4216425855
82 18 fa c2 00 00 01 01 08 0a c5 4f 2d e2 61 52
ack 3939836193
72 98
dataofs 8L
reserved 0L
flags 32-bit pseudo-random value, XOR byte by byte
PA
window 33304
chksum 0xfac2
urgptr Prevent the browser from being leveraged for cross-protocol attacks, cache poisoning
0
options [(’NOP’, None), (’[...]
WebSocket
flags FIN
opcode text frame 81 a5 bd cc ef e0 e9 a4 8a 99 9a be 8a c0
mask flag 1L de a3 82 89 d3 ab cf 94 d2 ec 88 85 c9 ec 96 8f
length 37L c8 e0 cf a2 dc be 8d 81 cf ad c1 ce 93
mask 0xbdccefe0
frame data ’xe9xa4x8ax99[...]
bd cc ef e0 bd cc ef e0 bd ...
e9 a4 8a 99 9a be 8a c0 de ...
T h e y ‘ r e c
Thursday, December 13, 12 12](https://image.slidesharecdn.com/baythreat2012websockets-121214005725-phpapp02/75/Hacking-with-WebSockets-12-2048.jpg)
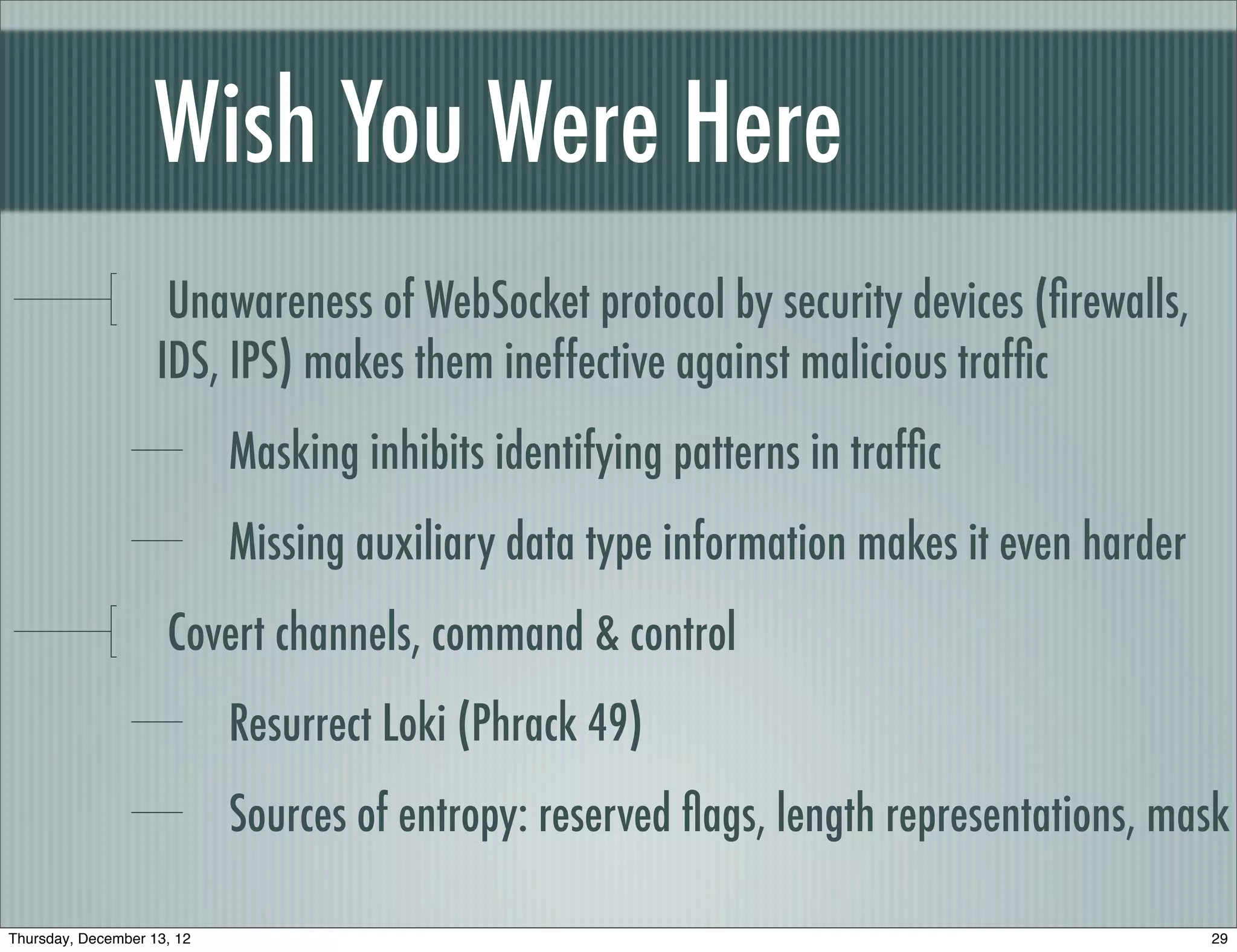
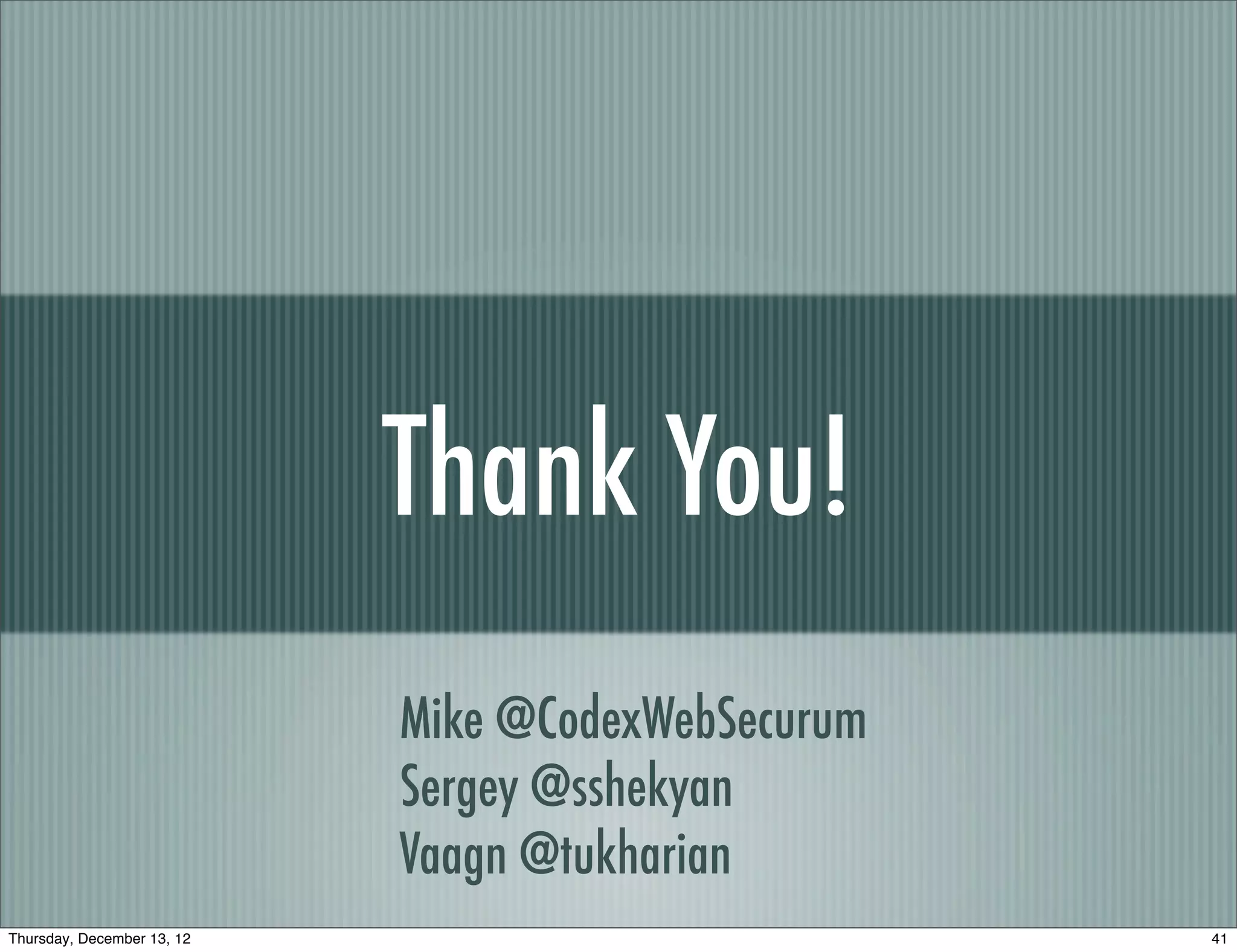
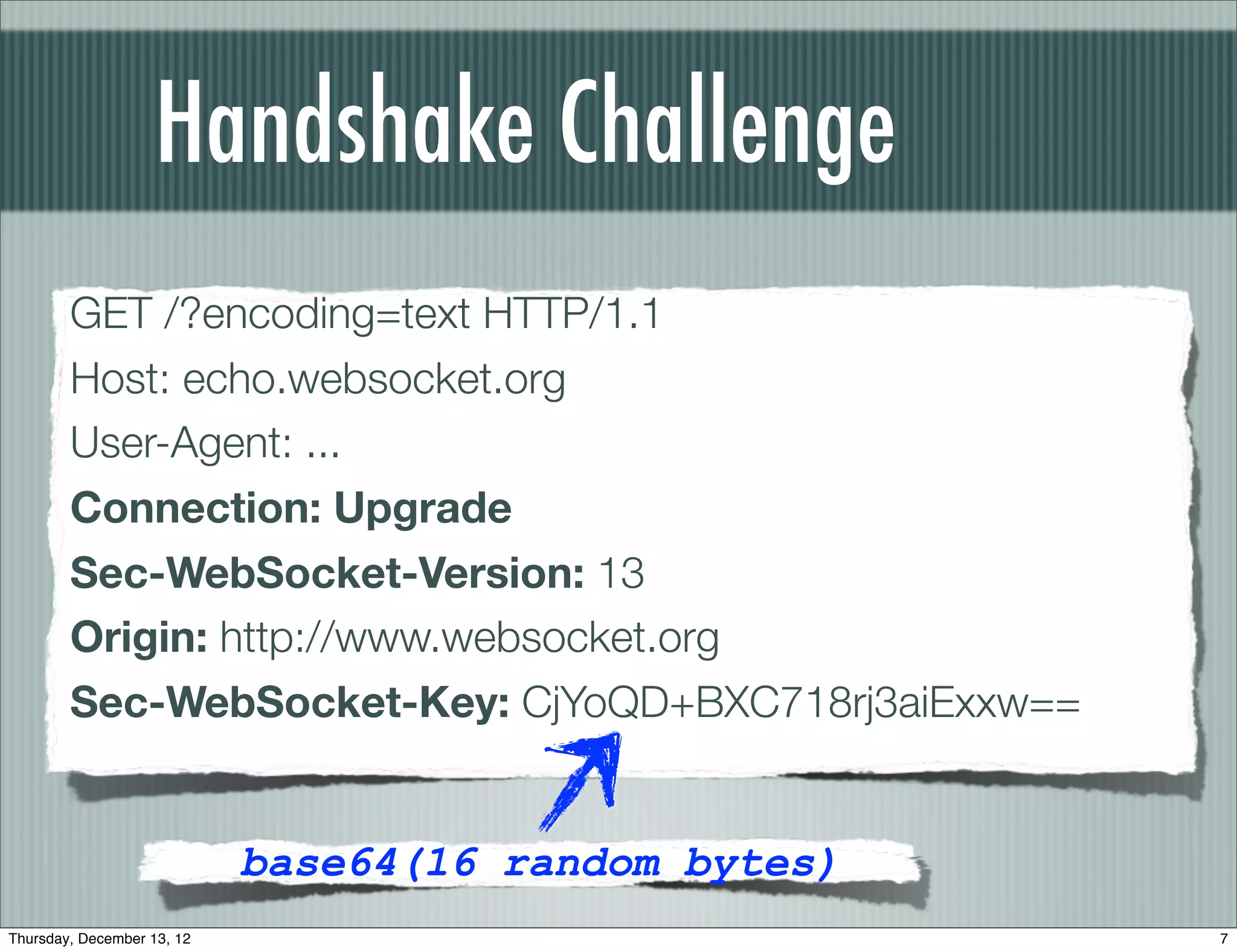
![Data Frame Security
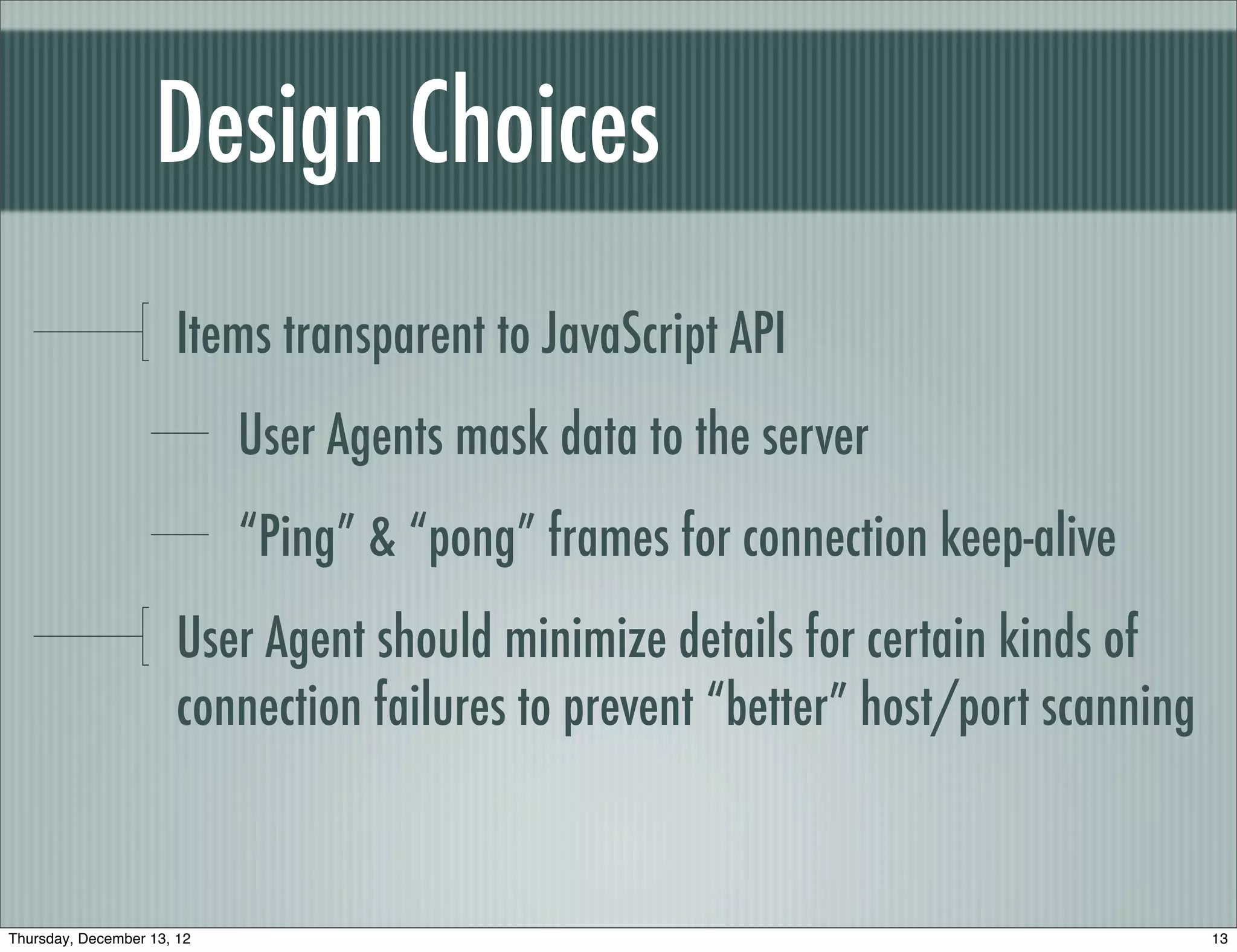
The handshake provides the headers to create a security context
Cookies, CORS, Origin, etc.
Decoupling this information is dangerous
0 1 2 3
0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1
+---------------------------------------------------------------+
| [ insert your protocol here ] |
+---------------------------------------------------------------+
| It is pitch dark. |
+ - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - +
| You are likely to be eaten by a grue. |
+---------------------------------------------------------------+
Thursday, December 13, 12 14](https://image.slidesharecdn.com/baythreat2012websockets-121214005725-phpapp02/75/Hacking-with-WebSockets-14-2048.jpg)