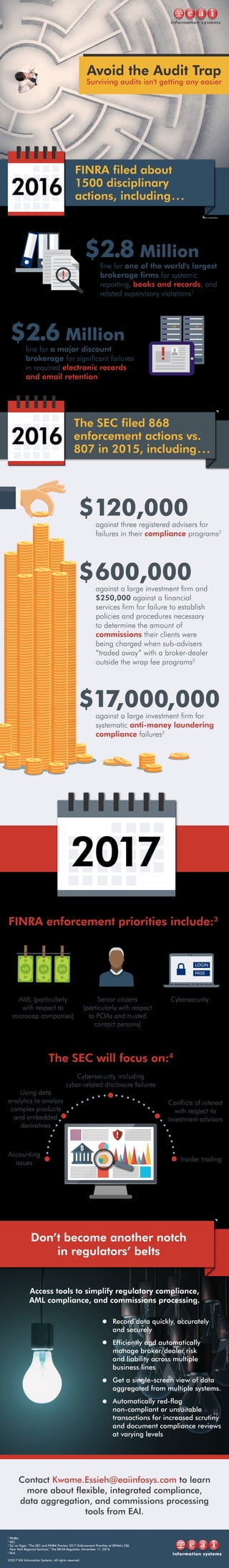
The document outlines recent fines imposed on large investment and brokerage firms for various compliance failures, including anti-money laundering and reporting violations. It highlights the enforcement priorities of regulatory bodies like SEC and FINRA, emphasizing the need for improved compliance and data management tools. The focus is on avoiding regulatory pitfalls and ensuring thorough audit preparations.