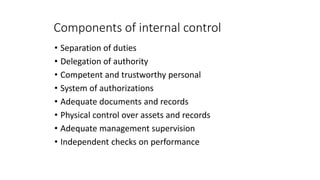
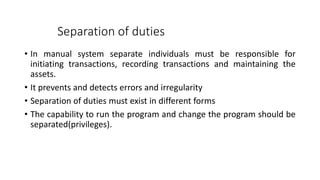
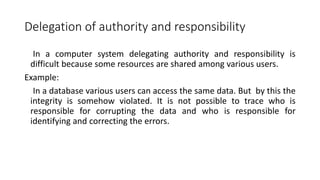
This document provides an overview of information systems auditing. It discusses the need for auditing computers due to risks like data loss, incorrect decisions, and abuse. An information systems audit aims to safeguard assets, maintain data integrity, and ensure system effectiveness and efficiency. The document also examines how computers affect internal controls and the audit process. It notes computers concentrate organizational assets, making oversight important. Finally, the document outlines how computers can help audits by enabling testing of large data volumes quickly and accurately.