Applications of Management Information System.pptx
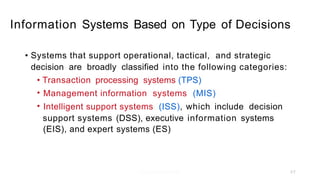
- 1. Information Systems Based on Type of Decisions • Systems that support operational, tactical, and strategic decision are broadly classified into the following categories: • • • Transaction processing systems (TPS) Management information systems (MIS) Intelligent support systems (ISS), which include decision support systems (EIS), and expert (DSS), executive systems (ES) information systems 2-7
- 2. Functional Information Systems • Information systems can also be classified according to function in these four areas: • • • • Marketing Manufacturing and service Accounting and finance Human resources 2-9
- 3. EIS OAS MIS TPS DSS ES Functional Systems Dss EIS MIS TPS ES CUSTOMER GIS EDI Figure1: Functional Information System
- 4. Marketing Information System A system that meets the marketing information needs of an organization. • • Customer-oriented and work toward achieving the strategic sales and marketing plan • Aim is to gain instantaneous access to global market information • Primary goal of retaining existing customers and attracting new ones • Can't be standardized for all companies. Every company has its own • Marketing system must be tailored to match the marketing policies, procedures and practices each company. of • A very popular marketing information system is one that automates sales and marketing functions. • Such systems capture valuable customer information and hence can improve productivity, enhance customer service and create better sales and marketing strategies. • Are influenced by and influence the strategic business plan and the strategic marketing plan.
- 5. .- . Strategic Business Plan de Strategic Sales & Marketing Plan dr Strategic Information Plan d Market information System ,r Sales Management Marketing Mix (Product, place, price, promotion) D a t a b a s e s External . - ,- ... ..-. Market Intelligence Market Analysis I .. Internal Market Research Customer Analysis Forecasting Figure2: Marketing Information System Feedback
- 6. Benefits of Marketing Information System Benefits of Marketing Information System Provides employees with information that helps companies capture niche markets in highly competitive Helps in sales forecasting. Able to provide demand forecast. Helps in achieving a company's goal. Marketing Information system have a deep and direct influence on the quality of customer service. Assists the marketing manager to maintain the better relationship with valuable customer.
- 7. Manufacturing Information System A system that supports the manufacturing functions of: • • • • • purchasing, receiving, quality control inventory management, material requirement planning, Production scheduling and plant design. Applies to both manufacturing and service industries capacity planning Manufacturing should be viewed within the broad context of delivering both goods and services since a manufacturer of automobile parts and a travel agency are likely to have manufacturing information system. Production system is a subset of manufacturing information system. Production system pertains to the production of goods and services. It specially addresses information needs relating to raw materials, equipment, manpower and other issues related to production of goods and services. • • •
- 8. Strategic Business Plan Strategic Manufacturing Plan Strategic Information Plan - - Manufacturing dr Manufacturing information System J r . Services d Purchasing Receiving Databases ~ Quality Control External - - ~ ,~ Inventory - ~ Material R equirement Planning Capacity Planning - - ~ Internal Scheduling Facilities Layout Figure3: Manufacturing Information System
- 9. Benefits Mfg. Information System • Helps supplier to store such as Home Depot Hardware. Reduces operating cost and inventory levels To achieve strategic goal of company and Ace • •
- 10. Financial and Accounting Information System(FAIS) • Provides information related to the accounting and financial activities an organization Includes a large number of subsystems that address the operational, tactical and strategic information needs of the business Includes some subsystems such as budgeting, cash and asset of • • management, capital budgeting, portfolio account receivable, inventory control and Other subsystems include record keeping, analysis, general ledger, payroll systems. account analysis, cash • management, financial analysis, leasing options, insurance underwriting, insurance claims processing and investment management. Financial instit ut ion like bank, uses specialized F AIS, such as commercial loan analyzers, credit approval system, commercial account rating system, credit applicat ion system, automated teller cont rol and securit ies trading. •
- 11. Strategic Business Plan Strategic Financial Plan d Strategic Information Plan • Financial & Accounting Information Systems General Ledger Databases Asset management Order entry, Accounts Receivables, Accounts payable External Inventory control, Payroll, Cash management, Capital management, Investment management Internal Long-range Forecasting Business Intelligence Figure5: Financial & Accounting Information System
- 12. Human Resource Information System (HRIS) • Supports the planning, control, coordination, administration and management of an organization's human resources. HRIS includes a large number of subsystems that address the informat ion needs of various human resource functions. They provide managers with information, policies and procedures concerning recruiting, layoffs, employee evaluation, promotion, termination,transfer, salary equity monitoring, job • • descriptions and responsibilities, training, affirmative action and employment opportunities. An HRIS also determines how hiring and training decisions made personnel department can increase sales revenues. equal • by the
- 13. Strategic Business Plan Strategic Human Resource Plan Strategic Information Plan Human Resource Information Systems Personnel D a t a b a s e s Payroll r Benefits External Equity Monitoring Internal Recruitment Compliance systems Manpower Planning Figure6: H u m a n R e s o u r c e In f o r m a t i o n S ys t em
- 14. Developing Cross-functional System Today, the emphasis is on building cross-functional systems that facilitate the flow of information among all units in an organization. Some critics to develop a Cross-functional System are: 1. Decision-making should not be compartmentalized in functional areas, but should instead be viewed in the context of the entire organization 2. A close link is made in between information system and functional system. 3. System must be designed in such a way that it can work combinely with both the systems For example, a report of the number of people who worked overtime last month or the number of machines that operated during the night shift last month (manufacturing) are often the output of an MIS.
- 16. 12-16
- 17. 12-17
- 18. 12-18 Definition of SIS Researchers have classified IS into three categories: Systems that support business functions Systems that support strategic planning such as DSS and EIS Systems that are a part of a firm’s strategy
- 19. 12-19 Definition of SIS Contd… Strategic Information System (SIS) A system that delivers information products and services that play a direct and prominent role in helping the firm achieve its strategic goals.
- 20. 12-20 Definition of SIS Contd… An SIS also supplies an organization with Business Intelligence or competitive information Business Intelligence Business Intelligence consists of internal and external data used to assess and analyze opportunities and threats in business environment
- 21. 12-21 Types of SIS SIS can be external or internal systems. External strategic systems are used primarily by external entities in the business environment, such as customers, suppliers, and distributors. Benefits to the customer: 1. Increased customer satisfaction 2. Increased customer control 3. Reduction in transaction costs (shipping and handling costs)
- 22. 12-22 Types of SIS Contd… SIS can be external or internal systems. Internal Strategic Systems are used by employees within the organization and do not have a value- added component. They focus on issues such as improving the quality of products and services and enhancing the decision-making capabilities of managers. Benefits to the Organization: 1. Increased market share 2. Reduction of processing costs 3. Ability to charge higher prices because of value-added component 4. Increase in profit margins
- 23. 12-23 Examples of SIS An example for a SIS is the Automated Teller Machine (ATM) first introduced by Citibank in 1977. This completely revolutionized the system in banking industry and forever changed the way people conducted financial transactions. ATMs were strategic systems because the only alternative to ATMs would require banks to open branch offices at a large number of convenient locations and these offices would have to remain open for 24hrs per day, 7 days per week, to provide the same level of service as ATMs.
- 24. 12-24 Strategic Information Systems Plan (SISP) Strategic Business Plan: A plan that identifies a company’s goals as a means of achieving the organizational mission; also includes what is popularly referred to as SWOT analysis. Strategic Information Systems Plan (SISP): Identifies the information systems and technologies that are vital to support a firm’s business strategy; derived from the strategic business plan. -Is like a road map that helps IS managers to identify any potential gaps between what is available and what should be available to promote good decision making.
- 25. 12-25 Strategic Information Systems Plan (SISP) Contd… The SISP should specifically target the following four areas: - Aligning IS investment with business goals - Exploiting information technologies for competitive edge - Ensuring the efficient management of IS resources -Developing technology policies and practices
- 26. 12-26 Strategies for Developing an SIS Steps involved in developing an SISP: Establish the purpose of the plan and develop a broad outline describing what the plan will address. Update the strategic business plan and the goals of the business. Reassess the current business environment Identify the existing information systems including hardware, software, and networking capabilities. Determine future information needs and systems Identify the new systems, projects, and capabilities required to meet the changing environment and changing information needs. Identify the resources required to implement the plan and to win the support of top management for the plan. An organization should ask two important questions before investing in strategic systems: - Is the project financially feasible? - Is the project technically feasible?
- 27. 12-27 Steps to Ensure Success of Strategic Systems Re-engineering: Re-evaluating and radically redesigning the way in which a company does business; driven by the question, “Why do we do what we do?” Technology decisions should be grounded in a clear understanding of the processes that drive the technology. Strategic systems should be driven by strategic alliances between trading partners Continuous improvement and investment in strategic systems are essential for their long-term success The organizational culture should encourage some risk taking Users must be fully trained if the full potential of the strategic system is to be achieved
- 28. 12-28 Potential Barriers for Developing an SIS Development (Definition) Barriers: - Generating Workable ideas requires leadership and teamwork - Many innovative ideas are technically feasible - Many innovative ideas are prohibitively expensive -Many ideas die because they lack a sufficient market. Implementation Barriers: - Telecommunications increases the complexity of implementing SIS - Multiple systems are difficult to integrate - SIS systems often require inter-organizational cooperation - State-of-the-art technologies are difficult to implement Maintenance Barriers: - Competitors can copy SIS - Unanticipated demand can overwhelm the usefulness of an SIS - Applications can be expensive to maintain or enhance - High exit barriers can cause devastating losses.
- 30. 12-30 Computer Security The process of protecting and safeguarding hardware, software, networks, physical facilities, data, and personnel from accidental, intentional, or natural disasters.
- 31. 12-31 Common Types of Security Violations Company data theft by employees Gaining access to information stored on computer networks by cracking passwords Industrial espionage by criminals eavesdropping on wireless communications or on LANs and Internet connections Deliberate, unauthorized modification of software Theft of employees’ identities to make outrageous or illegal statements on the Internet Starting or fueling rumors on the Internet that are designed to harm the company Denial of service attacks in which people call a toll-free number or send an e-mail but the number stays perpetually busy or they are denied access
- 32. 12-32 Awareness of Security Violations 0 60 50 10 40 30 20 70 Yes No Unknown 53% 69% 9% 14% 38% 17% 1996 1998 Has your organization been the target of information espionage? Source: Warroom Research, Inc., Annapolis, Md.
- 33. 12-33 Why Information Systems Are Vulnerable Increased Access to the System Key sources of security breaches are employees, authorized external users such as suppliers, and crackers outside the business Increased System Complexity Information systems today are much more complex than systems even a few years ago – the software has many more functions and features and the hardware has integrated components, all of which must work together to provide overall system security – each operating system has its own security features, so switching to a new operating system can throw previous security measures into disarray
- 34. 12-34 Why Information Systems Are Vulnerable (cont.) Cyber Terrorism on the Internet The Internet is a haven for those engaging in security misdeeds The Internet connects two million host computers and provides access to a rich and extensive set of data and information to millions of users, with the numbers increasing by 15 percent every month Networks Are the Weakest Link in the Chain “Networks are essentially sieves to anyone with minor technical skills, and the desire to retrieve other peoples’ information”
- 35. 12-35 Why Information Systems Are Vulnerable (cont.) Complacent Management Top managers are often reluctant to invest in security because it is difficult to see the effect it has on the ‘bottom line”
- 36. 12-36 The Three Categories of Security Breaches Types of Security Breaches Description Accidental or unintentional errors Accidents relating to hardware and software. Employees can also cause unintentional security breaches. Most common type of security violation, in which individuals intentionally decode passwords. Breaking into computer hardware such as modems, faxes, and cellular phones. Infected software that behaves in unexpected and undesirable ways. Tornadoes, earthquakes, and other disasters that cause computer systems to fail. Intentional errors Cracking passwords Breaking into computer hardware Software virus Natural disasters
- 37. 12-37 Techniques for Reducing Accidental Security Breaches WAYS TO REDUCE ACCIDENTAL SECURITY BREACHES Introduce Hardware Tracking Methods Establish and Enforce Clear Security Policies and Procedures Training and Educating Users
- 38. 12-38 Eight Symptoms of a Software Virus Inexplicable loss of free memory Unusually long program loading or execution times Changes in program or file size Malfunctioning print routines Computer freezing Unusual messages or beeps Computer rebooting in the midst of a process Corrupt files
- 39. 12-39 Computer Security Controls Policies, procedures, tools, techniques, and methods designed to reduce security breaches, system destruction, and system errors from accidental, intentional, and natural disasters.
- 40. 12-40 Classifications of Security Controls SECURITY CONTROLS Examples: •Documentation •Encryption •Firewalls Examples: •Passwords •Smart cards •Biometric identification •Backups Development Controls Examples: •Fire alarms •Security personnel •Restricted access to a facility •Devices that monitor temperature Physical Facility Controls Application Controls
- 41. 12-41 Application Controls Passwords Many companies require employees to change their passwords frequently Employees should use hard-to-guess or randomly generated passwords Smart cards A plastic card with an embedded chip that provides users with a new password each time they log on
- 42. 12-42 Application Controls (cont.) Biometric identification techniques Rely on body parts to validate that the user can access the system – finger prints – retinal scans – voice recognition Backup Treat information like gold Establish a backup routine Keep your backups in a safe place
- 43. 12-43 Development Controls Documentation Written set of documents that explain in detail the reasoning behind processes, procedures, and other details – The more detailed the documentation, the better off the company will be in the future Encryption Converts data into a secret code before they are transmitted over the network
- 44. 12-44 Physical Facility Controls Physical Facility Controls are the policies and procedures that control the physical environment in which systems reside Posting security personnel Installing fire alarms Security alarms Hidden cameras Requiring users to wear badges or use smart cards to gain access to a building
- 45. 12-45 Disaster Recovery Plan (DRP) There are seven steps in developing a DRP Identify specific situations that are classified as a disaster Name the individuals who have the right and the responsibility to declare a disaster Identify specific steps for declaring a disaster Inventory all crucial corporate assets, functions, and resources that are essential to operate the business Specify the general course of action the business will take when disaster strikes Develop a specific course of action that each employee must take to make the company operational when disaster strikes Identify resources required to recover from the disaster, including money, time, personnel, and facilities
- 46. 12-46 Business Guidelines for Security Success Recognize the Symptoms of Security Breaches Unknown accounts added to the system and file server An unusual number of log-on failures and dial-in attempts Unexpected system or network crashes Unauthorized changes to system software and system files High system activity when no users are logged on, especially during off-peak hours
- 47. 12-47 Business Guidelines for Security Success (cont.) Be Watchful of Disgruntled Employees Disgruntled employees, or those who have been fired, are often likely to cause security breaches Establish clear policies and legal agreements with fired employees Involve Law Enforcement When You Suspect a Security Breach Call police immediately Train employees not to erase or destroy files that the suspected employee used or created Cooperate with law enforcement Quantify damages to assist with prosecution
- 48. 12-48 Business Guidelines for Security Success (cont.) Build Security Partnerships Security depends on partnerships with suppliers and customers, and sometimes the government Convince Top Management That Security Is Not an Option 41% of survey participants reported that their company doesn’t have formal security policies More than half said they lack disaster recovery plans More than a third said they don’t monitor their networks for suspicious activity Fewer than one in five use encryption technology to safeguard sensitive information