The document discusses several problems with traditional client-server architectures for mobile applications and presents an adopted solution.
The main problems discussed are:
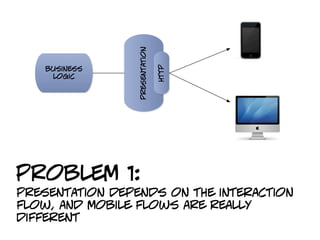
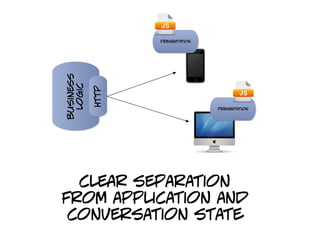
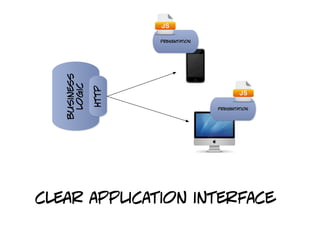
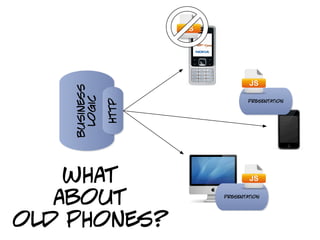
1. Presentation logic depends on interaction flows which differ between mobile and web.
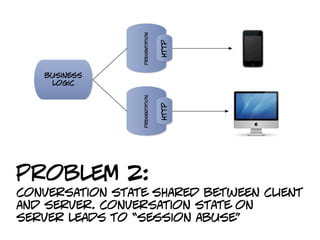
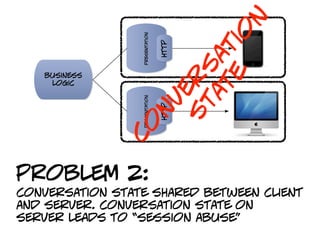
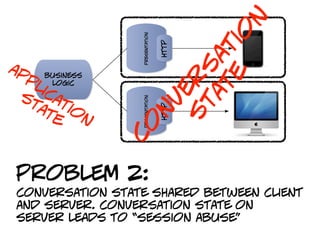
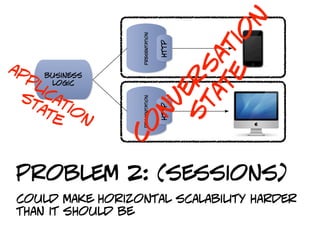
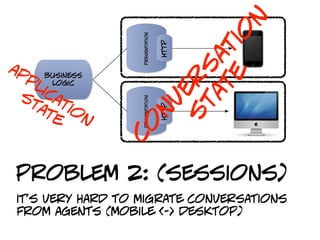
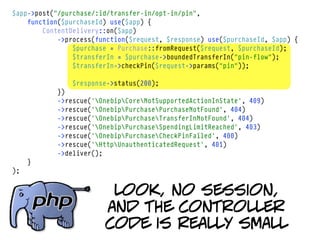
2. Conversation state shared between client and server can lead to "session abuse".
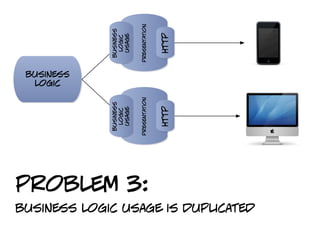
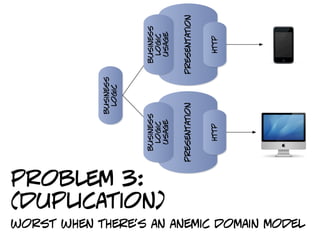
3. Business logic usage is duplicated across clients.
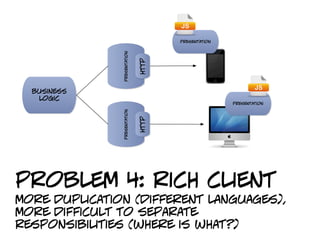
4. Rich clients result in more duplication across languages and responsibilities.
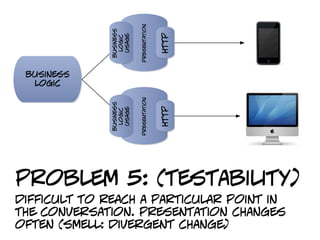
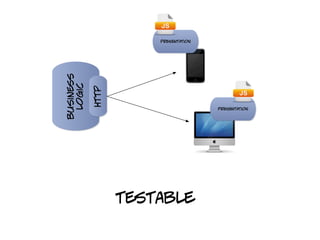
5. Presentation changes often make conversations hard to test.
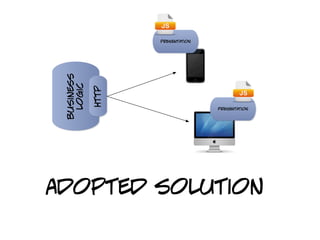
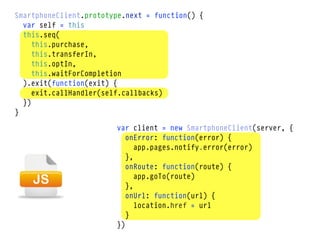
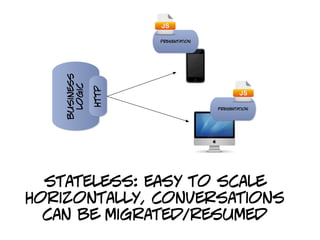
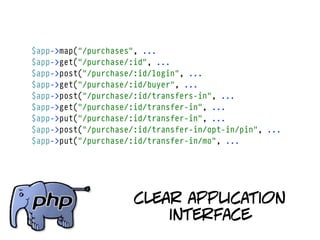
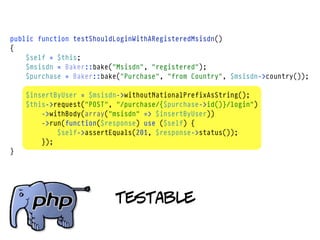
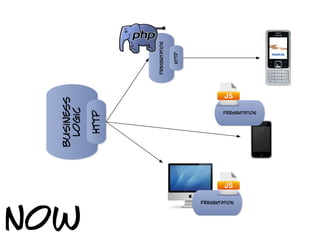
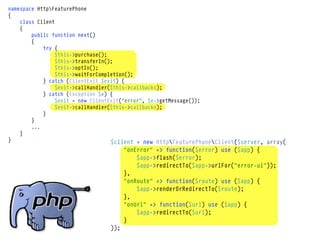
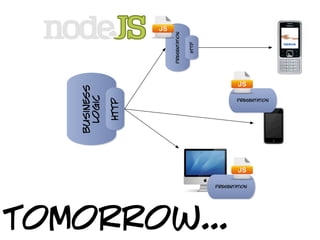
The adopted solution separates presentation from business logic and uses a stateless, conversational approach with clear application interfaces to address these issues. It allows for horizontal scalability, easy migration of conversations, and improved