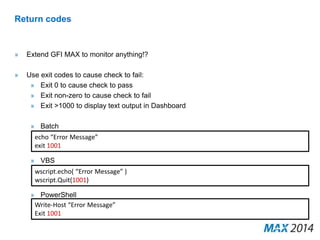
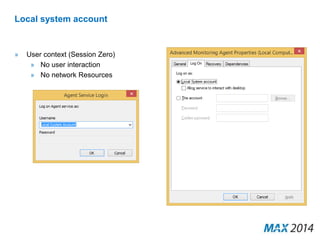
The document discusses scripting and automation capabilities in GFI MAX RemoteManagement. It provides an overview of scripting concepts, how scripts can be used for monitoring checks and automated maintenance tasks, and examples of built-in and custom scripts. The document also covers best practices for writing scripts, including using command line arguments, interacting with the file system, registry, applications, and returning results.


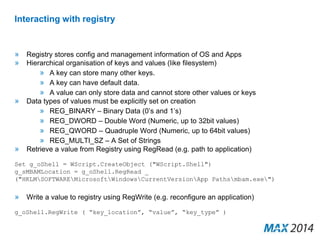
![Getting the data you need from API
» Used mainly to get data out of GFI MAX RemoteManagement
» Easy to manipulate with PowerShell:
$apikey = “YOUR API KEY"
$clientsurl = "https://www.systemmonitor.us/api/?apikey=$apikey&service=list_clients"
[xml]$xmlclients = (new-object System.Net.WebClient).DownloadString($clientsurl)
» Example Uses:
» Getting serial number data
» Getting MAC addresses for Wake-on-LAN
» See online help system for full instructions](https://image.slidesharecdn.com/scriptingautomation-140919141441-phpapp02/85/Scripting-and-Automation-within-the-MAX-Platform-Mark-Petrie-46-320.jpg)
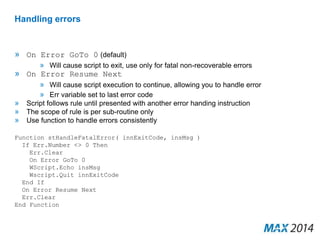
![Example: Workstations that have not been scanned in 90 days
$apikey = "YOUR API KEY"
$CurrDate = Get-Date
$clientsurl = "https://www.systemmonitor.us/api/?apikey=$apikey&service=list_clients"
$wstable = @()
[xml]$xmlclients = (new-object System.Net.WebClient).DownloadString($clientsurl)
foreach ($xmlclientslist in $xmlclients.result.items.client) {
$clientid = $xmlclientslist.clientid
$sitesurl="https://www.systemmonitor.us/api/?
apikey=$apikey&service=list_sites&clientid=$clientid"
[xml]$xmlsites = (new-object System.Net.WebClient).DownloadString($sitesurl)
foreach ($xmlsiteslist in $xmlsites.result.items.site) {
$siteid = $xmlsiteslist.siteid
$wsurl = "https://www.hound-dog.us/api/?
apikey=$apikey&service=list_workstations&siteid=$siteid"
[xml]$xmlws = (new-object System.Net.WebClient).DownloadString($wsurl)
foreach ($xmlwslist in $xmlws.result.items.workstation) {
[datetime]$wsdate = $xmlwslist.last_scan_time
if (($CurrDate).Subtract($wsdate).Days -gt 90) {
$wsObj = "" | select Client,WSName,Age
$wsObj.Client = $xmlclientslist.name."#cdata-section"
$wsObj.WSName = $xmlwslist.name."#cdata-section"
$wsObj.Age = ($CurrDate).Subtract($wsdate).Days
$wstable += $wsObj
}}}}](https://image.slidesharecdn.com/scriptingautomation-140919141441-phpapp02/85/Scripting-and-Automation-within-the-MAX-Platform-Mark-Petrie-47-320.jpg)
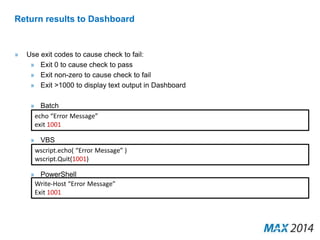
![Example: Wake devices before patching
param($siteid)
$apikey = "Put your API Key here“
$apiurl = “https://www.systemmonitor.us/api/?apikey=$apikey”
$url = "$($apiurl)&service=list_workstations&siteid=$siteid"
[xml]$xmlmac = (new-object System.Net.WebClient).DownloadString($url)
foreach ($xmlmacws in $xmlmac.result.items.workstation) {
$macString = $xmlmacws.mac1."#cdata-section"
$mac = $macString.split(':') | %{ [byte]('0x' + $_) }
$UDPclient = new-Object System.Net.Sockets.UdpClient
$UDPclient.Connect(([System.Net.IPAddress]::Broadcast),4000)
$packet = [byte[]](,0xFF * 6)
$packet += $mac * 16
[void] $UDPclient.Send($packet, $packet.Length)
write-output "Wake-On-Lan magic packet of length $($packet.Length) sent to
$macString"
}](https://image.slidesharecdn.com/scriptingautomation-140919141441-phpapp02/85/Scripting-and-Automation-within-the-MAX-Platform-Mark-Petrie-48-320.jpg)
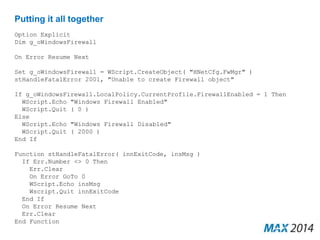
![Custom Monitoring
» Check current time vs. NTP server
$ntpcheck = w32tm /stripchart /dataonly /computer:pool.ntp.org /samples:1
[int]$ntpchecktime = $($ntpcheck.Split()[-1]).Split("s")[0].Substring("1")
Write-Output "$ntpchecktime seconds"
if ($ntpchecktime -gt 300) {
Write-Output "Check failed"
Exit 1001
}](https://image.slidesharecdn.com/scriptingautomation-140919141441-phpapp02/85/Scripting-and-Automation-within-the-MAX-Platform-Mark-Petrie-51-320.jpg)