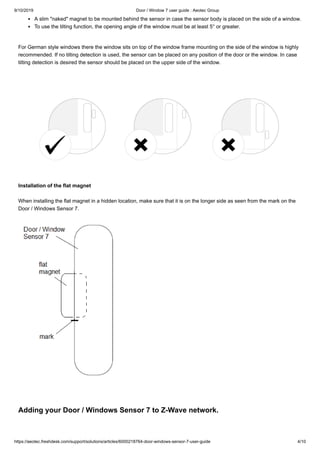
The document provides instructions for setting up and using the Aeotec Door/Window Sensor 7. It includes details on package contents, installation steps like mounting the sensor and magnet, adding it to a Z-Wave network, and configuring functions like open/close detection, tilt detection, and using it as a dry contact sensor or scene controller. Advanced functions and troubleshooting steps are also covered.