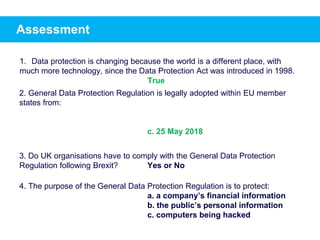
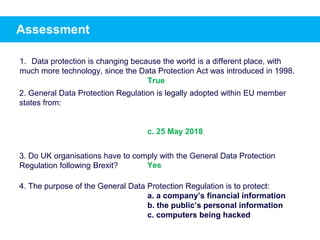
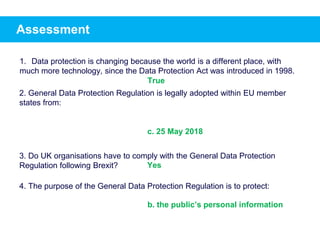
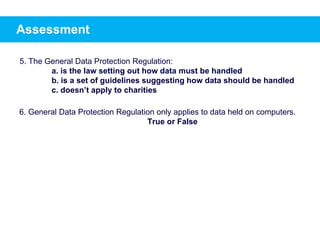
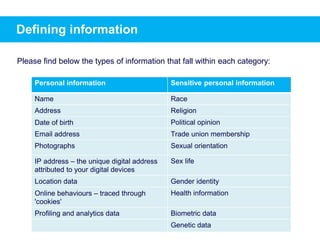
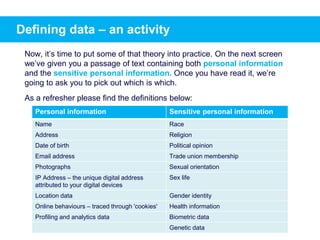
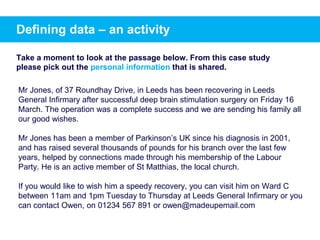
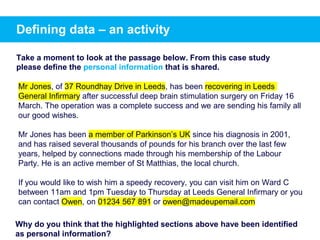
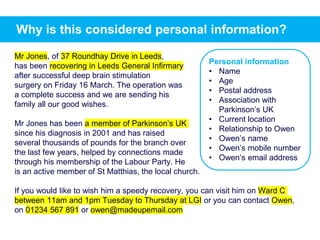
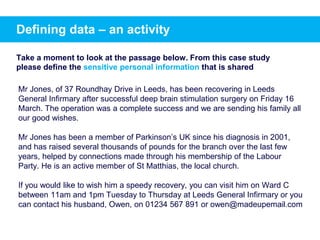
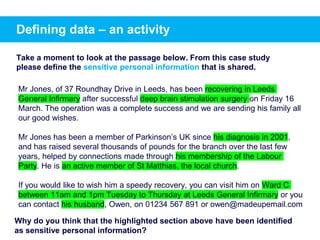
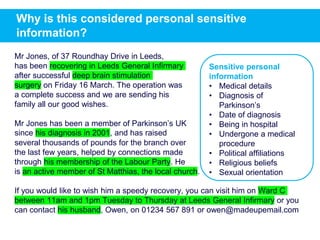
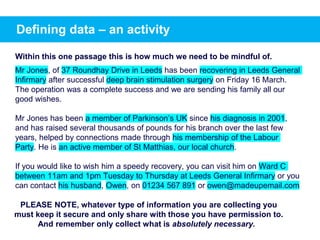
This document provides training on data protection and handling personal information. It defines personal information and sensitive personal information. It explains that the General Data Protection Regulation (GDPR) increases standards for obtaining consent and making people aware of how their data is used. It provides examples of different types of personal and sensitive information and gives guidance on properly identifying and managing this information.