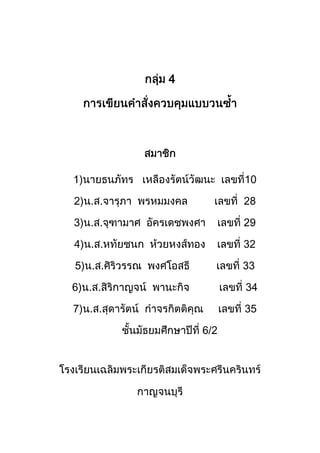
รายงานการเขียนคำสั่งควบคุมแบบวนซ้ำ กลุ่ม 4 ม. 6 ห้อง2
- 1. 4 1) 10 2) 28 3) 29 4) 32 5) 33 6) 34 7) 35 6/2
- 2. 1 2 for 3 while 4 1. 2. 3. for , while , do-while 4. for , while , do-while 5. for , while , do-while
- 3. 1. 1.1 Increment Operator 4.1 ++ increment 1
- 4. b=3 ; a=b++ 1 2 a=b; a=3 b=b+1; b=3+ 1 2. a 3 b 4 b=3 ; 1. 2 b=b+1; b=3+1 a=b; a=4 2. a 4 b 4
- 5. 1.2 decrement operator 4.2 -- decrement 1 b=3 a = b- - ; 1. 2 a=b; a=3 b=b-1; b=3-1 2. a 3 b 2 a=- -b ; 1. 2
- 6. b=b-1; b=3-1 a=b; a=2 2. a 2 b 2 1.3 (compound assignment operators) 4.3 (sym (operat bol) ors) = Assignment a=b += Addition a+=b (a=a +b) -= Subtraction a-=b (a=a- b) *= Multiplication a*=b (a=a* b) /= Division a/=b (a=a/ b) %= Remainder a%=b (a=a %b)
- 7. &= bitwise AND a&=b (a=a &b) |= bitwise Inclusive O a|=b (a=a| R b) ^= bitwise exclusive O a^=b (a=a^ R b) <<= right shift a<<2 (a=a <<2) >>= left shift a>>3 (a=a >>3) 1.4 4.1 #include <stdio .h> /* project_loop//operatorl.c */ main ( ) { int a = 2 , = 4 ; printf ( “---------------------- nn ”) ; printf ( “ * operator *n ”) ; printf ( “---------------------- nn”) ; printf ( a = -> %d n “ , a ) ; printf ( “ a = a + 1 -> %d nn ” , a ) ; printf (“ b = -> %d n “ , b ) ; b+=1 ; printf ( “ b + = 1 -> %d n ” , b ) ; printf ( “---------------------- nn ”) ; }
- 8. a=a+1; ---------------------------------------------------------------- ------ * Operator * ---------------------------------------------------------------- ------ a= --> 2 a = a+1 --> 3 b= --> 4 b + = 1 -->4.1 5 4.1 ---------------------------------------------------------------- = 1 ; a=a+1; a+ ---- Press any 4.2 to continue key #include <stdio .h> /* project_loop//operatorl.c */ main ( ) { int a = 2 , = 4 ; printf ( “---------------------- nn ”) ; printf ( “ * operator *n ”) ; printf ( “---------------------- nn”) ; printf ( a = -> %d n “ , a ) ; printf (“ b = -> %d n “ , b ) ; printf (“ n “) ; printf (“ a = b + + n “) ; printf ( “ a = %d n ” , a ) ;
- 9. a = b ++ ; b = ++a ; ---------------------------------------------------------------------- * Operator * ---------------------------------------------------------------------- a= --> 2 b= --> 4 a = b ++ a= 4 b= 5 b = a ++ a= 5 b= 5 4.2 4.2 -------------------------------------------------------------------- a = b ++ ; 2 Press any key to continue a=b; b a a=4 --------------------------------------------------------------------
- 10. a=b+1 ; 4+1 5 b b=5 b = ++ a ; a=a+1; a 4 4+1 a=5 a=b+1 ; a b a=5 1.5 implicit type conversion explicit type conversion 4.3 #include <stdio . h > / * file name job6 */ main ( ) { Int value1 = 10 , result2 ; float value 2 = 3.17 , result ; Const char line * 40 + = “______________________________” ; printf ( “ % s nn “ , line) ; printf ( “ * Implicit type conversion * n “) ; printf ( “ % s nn “ , line) ; printf ( “ 10 + 3.17 = % . 2f nn “ , result1) ;
- 11. result 1 = value1 + value2 ; result 2 = (int) ( value1 + value2 ) ; ----------------------------------------------------------------------------------- * Implicit type conversion * ---------------------------------------------------------------------------------- 10 + 3.17 =13.17 10 / 3 = 3.00 ---------------------------------------------------------------------------------- * Explict type conversion * <int><10 + 3.17 > = 13 ---------------------------------------------------------------------------------- Press any key to continue 4.3 4.3 1. result 1 = value1 + value 2 ; 10 + 3.17 13.17 result 1
- 12. 2. result 1 = value / 3 ; / % .2f 3. result 2 = (int) ( value1 + value2 ) ; 10 + 3.17 13.17 int () 13 result 1 2 for : 3 : for 2.1 for for For ( = ; ; ) { statemmnt (s) ; }
- 13. : 1 {} 4.1 for 2.2 for 5 4.4 for #include <stdio . h> /* project_loop // ex_for1.cpp */ main ( ) { char name [ 30 ] ; int n ; printf (“ Report Data n “ ) ; Printf ( “ **************************************** nn “) ;
- 14. for ( n = 1 ; n < 6 ; n++ ) { printf (“ No. => %d “ , n ) ; printf ( “ Name is = > “ ) ; scanf ( “ %s “ , name ) ; } Report Data **************************************************** NO. =>1 Name is => ANAN ANAN NO. =>2 Name is => SOMJIT SOMJIT 5 NO. =>3 Name is => UILAI UILAI NO. =>4 Name is => RUNG RUNG NO. =>5 Name is => TEERA TEERA For ( n =1 ; n < 6 ; n ++) **************************************************** End program …………………………. Press any key to continue 4.4 4.4 1. 5 2. n 1 3. n 6 4. {} For ( n = 1 ; n < 6 ; n++) { Printf ( No . => %d , n ) ;
- 15. 1 for n 1 6 n = n+1 2.3 for 4.5 for #include <stdio .h > /* project_loop // ex_for2_1.cpp */ main ( ) { char name [ 30 ] ; int midterm , final ,score , n ,num ; printf ( “ key loop => “) ; scanf ( “%d” , &num) ; printf ( “ n Report Score n “ ) ; printf ( “ ***************************************** nn “ ) ; For ( n = 1 ; n <= num ; n++) { printf ( “ No. => %d “ , n) printf ( “ Name is => “ ) ; scanf ( “ %s” , name) ; } Printf( “ **************************************** n “ ) ;
- 16. Key loop => 3 3 Report Score **************************************************** NO. =>1 Name is => ANAN SOMKIT NO. =>2 Name is => SOMJIT LINDA NO. =>3 Name is => UILAI KITTI **************************************************** End program …………………………. Press any key to continue for ( n = 1 ; n <num ; n++) 4.5 4.5 1 2. 3 3 3. Printf ( “ key loop => “ ) ; scanf ( “ %d “ , num) for ( n =1 ; n <= num ; n++) { printf ( “ No. => %d “ , n) printf ( “ Name is => “ ) ; scanf ( “ %s” , name) ; }
- 17. 3. while : while {} while {} while > while while > {}
- 18. while 3.2 while while
- 19. Ctrl-Break n <= 5 n n 3. while
- 20. while while n <= 5 n = n+1 ; n>5 while n <= 5
- 21. while n
- 22. while n
- 23. n num do-while > do – while do – while
- 24. do – while do – while
- 25. do – while {}
- 26. while n <= 5 n>5 n++ : n=n +1: n n>5 {} do – while
- 27. do – while n
- 28. 5. 5.1 for For pretest loop 3 2 3 for compound statement for while for for while 20 for
- 29. n key loop =>…………… Report Score **************************** No. => …………… name is => ………….. midterm is => ………….. Final is => …………… * Score = …………… ***************************** *Average Score is = …………. ***************************** 1. 1.1 1.2
- 30. = 1 = = = 1.3 1.4 1.5 num n name midterm final score sum average 1.6 action)
- 31. 1 (num) 2) for (n =1; n<=num ; n++) 2.1-2.6 3 2.1) (n) 2.2) (name) (midterm) (final) 2.3) (score) = midterm + final 2.4) score 2.5) (sum) = sum + score 2.6) 2 3) (average) = sum / num 4) average 5)
- 32. 2. start num For (n = 1 ; n <= num ; n++) n >num n <= num n Averge = sum / num name,midterm,final average Score = midterm + final end score sum = sum + score
- 33. 3. #include <stdio.h> /* file name ex_for3.cpp*/ main () { char name [30] ; int midterm = 0 , final = 0 , score = 0 ,n , num ; float sum = 0 , average = 0 ; printf (“ key loop => “) ; scanf (“%d “,&num) ; Printf (“n Report Score n”) ; printf(“*************************n n”) ; for(n = 1;n <= num ; n++) { printf (,“No. => %d n” , n) ; printf (“Name is => “) ; scanf (“%s”,name) ; printf (“midterm is => “) ; scanf (“%d”&midterm) ; printf (“final is => “) ; scanf (“%d”&final) ; score = midterm =+ final; printf ( “* score = %dn”,score) ; sum = sum + score ; printf (“*****************n”) ; } average = sum / num ; printf (“* Averge score is = %.2f n” , averge) ; printf (“***********************n) ; }
- 34. 3 1. 2. 3. for 2 3 for
- 35. 5.2 while while repetition control structure) loop) for while endless loop) while - w hile
- 36. while while statement ; while { ; ; ; } while 0 n
- 37. 0 Report Score =========================== Student Id => …………… 0 No. => ……………. name is => ………….. midterm is => ………….. Final is => …………… * Score = …………… =========================== *Average Score is = …………. =========================== 1. 1.1 1.2 = 1 = =
- 38. –1) = 1.3 1.4 1.5 id n name midterm final score sum average 1.6 action) 1) (n) 1 2 (id) 3) while (id ! = 0) 3.1-3.8
- 39. 4 3.1) (n) 3.2) (name) (midterm) (final) 3.3) (score) = midterm + final 3.4) score 3.5) (sum) = sum + score 3.6) n 3.7) id) 3.8) 4) (average) = sum / (num-1) 5) average 6)
- 40. 2. start n =1 id no While (id !=0) yes n Averge = sum / num (n-1) name,midterm,final average Score = midterm + final end score sum = sum + score
- 41. n = n+1 id 3. #include <stdio.h> /* file name ex_while4.c*/ main () { char name [30] ; int midterm = 0 , final = 0 , score = 0 ,n=1 , id ; float sum = 0 , average = 0 ; printf (“n Report Score n“) ; printf(“==========================n n”) ; Printf (“student id . => ”) ; scanf (“%d”,& id) ; while (id ! =0) { printf (,“No. => %d n” , n) ; printf (“Name is => “) ; scanf (“%s”,name) ; printf (“midterm is => “) ; scanf (“%d”&midterm) ; printf (“final is => “) ; scanf (“%d”&final) ; score = midterm =+ final; printf ( “* score = %dn”,score) ; sum = sum + score ; printf (“============================n”) ; printf (“student id . => ”) ; scanf (“%d”,& id) ; } average = sum / (n-1) ; printf end job….. n” ,) ; printf (“======================n) ; printf (“* Averge score is = %.2f n” , averge) ; printf (“======================n) ; }
- 42. 1. (averge) = (sum) (n)-1) ; n n 3 1 0 2 1 = / 2. scanf (“%d”,& id) ; 2
- 43. Printf (“student id . => ”) ; scanf (“%d”,& id) ; while (id ! =0) { printf (,“No. => %d n” , n) ; ………. printf (“student id . => ”) ; scanf (“%d”,& id) ; } 2 while (id ! =0) #include <stdio.h> int counter , num; char word[20] = "Bodindecha";
- 44. num counter while counter <= 11 printf("ntcounter = %2d my school is %s print round %d. ",counter,word,++num); counter = counter + 2 counter
- 45. counter counter <= 11 5.3 do-while do while loop) while do while endless loop) do while -
- 46. do while Do { ; ; ; }while ; do while #include <stdio.h> intcounter ,num ; char word[20] = "Bodindecha";
- 47. counter do while printf("ntcounter = %2d my school is %s print round %d. ",counter,word,++num); counter = counter + 2; counter < 11
- 48. counter /* example4_17.c */ while Report Score =========================== No. => ……………. name is => ………….. midterm is => ………….. Final is => …………… * Score = …………… =========================== calculate again y/n => …………. =========================== *Average Score is = …………. y/n ===========================
- 49. 1. 1.1 1.2 = 1 = = –1) = + = 1.3 – 1.4 1.5 ans n name midterm
- 50. final score sum average 1.6 action) 1) (n) 1 2) do 2.1) (n) 2.2) (name) (midterm) (final) 2.3) (score) = midterm + final 2.4) score 2.5) (sum) = sum + score 2.6) n = n+1 2.7) (ans) 2.8) while (ans!=’n’) 2 3
- 51. 3) (average) = sum / (n-1) 4) average 5)
- 52. start 2. n =1 do n name,midterm,final Score = midterm + final score sum = sum + score n = n+1 ans yes While (ans!=’n’)
- 53. Averge = sum / num (n-1) average 3. end #include <stdio.h> /* file name ex_do5.c*/ main () { char ans ; char name [30] ; int midterm = 0 , final = 0 , score = 0 ,n=1 , id ; float sum = 0 , average = 0 ; printf (“n Report Score n“) ; printf(“==========================n n”) ; do { printf (“n”) printf (,“No. => %d n” , n) ; printf (“Name is => “) ; scanf (“%s”,name) ; printf (“midterm is => “) ; scanf (“%d”&midterm) ; printf (“final is => “) ; scanf (“%d”&final) ; score = midterm =+ final; printf ( “* score = %dn”,score) ; sum = sum + score ; n = n+ 1 printf (“============================n”) ; printf (“n calculate again y/n = > “ ) ; ans = getche ( ) ; } while (ans ! = “n”) ; average = sum / (n-1) ; printf (“n”,) ; printf (“======================n) ; printf (“* Averge score is = %.2f n” , averge) ; printf (“======================n) ; printf end job….. n” ,) ; }
- 54. 1. do { …………………… ans = getche ( ) ; } while (ans ! = “n”) ; 2. ans = getche ( ) ; ans 3. ans } while (ans ! = “n”) ; n
- 55. 3 for while do-while
- 56. for while {} {} do – while {} 1 while
- 57. 4 “ ++ ” 2. 3. for while
- 58. loop) loop) loop) loop) loop) loop) loop) while for for 6. “--” 2
- 59. a = 3 , b= 2 7-8 7. a /=b ; a (a=a/b) a 1 (a=a * b) a 1 (a=a-b) a 1 (a=a+ b) a 5 8. a - =b ; a (a=a/b) a 1 (a=a * b) a 1 (a=a-b) a 1 (a=a+ b) a 5 9. for 5 4 2 3 10. for
