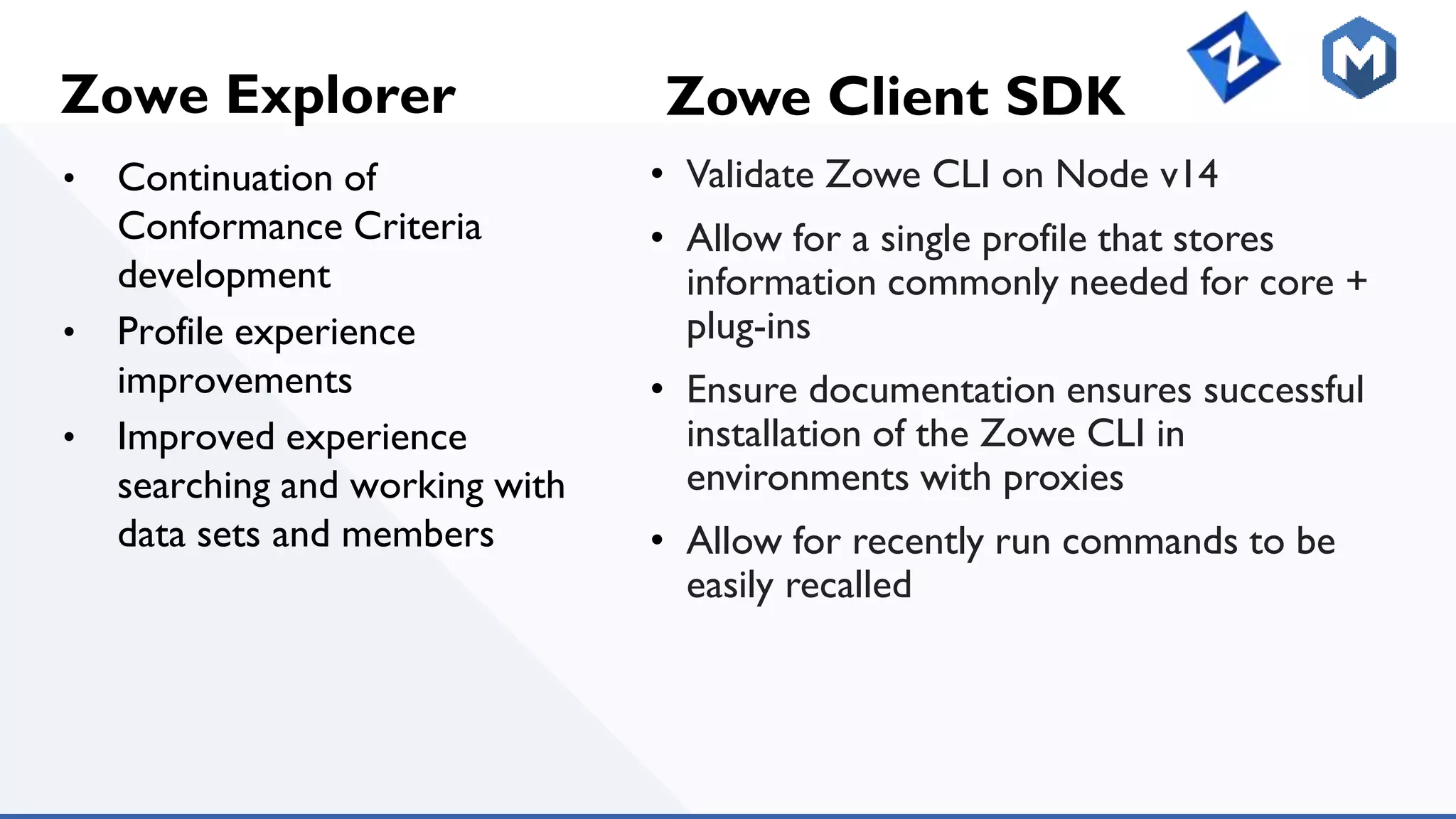
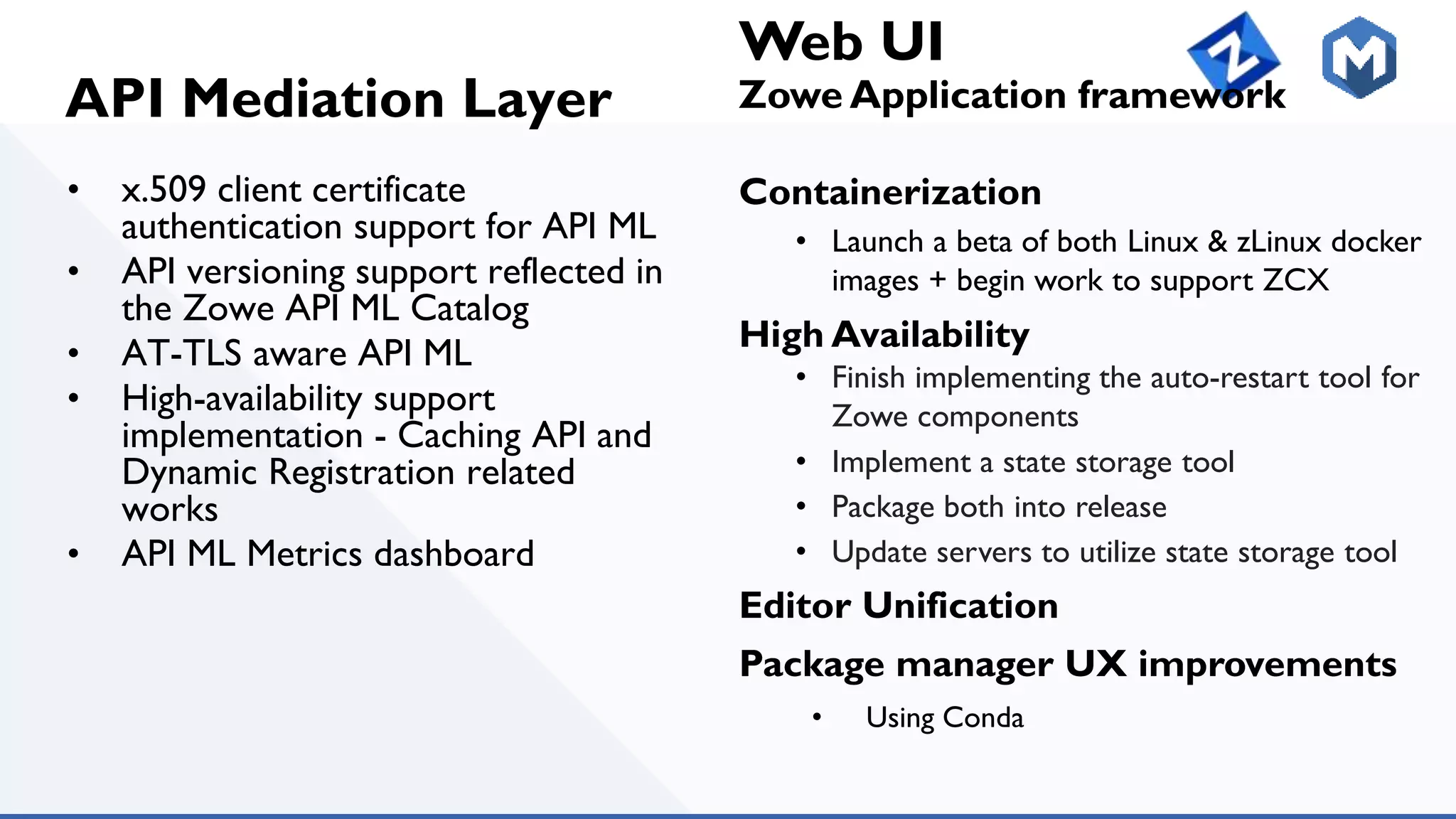
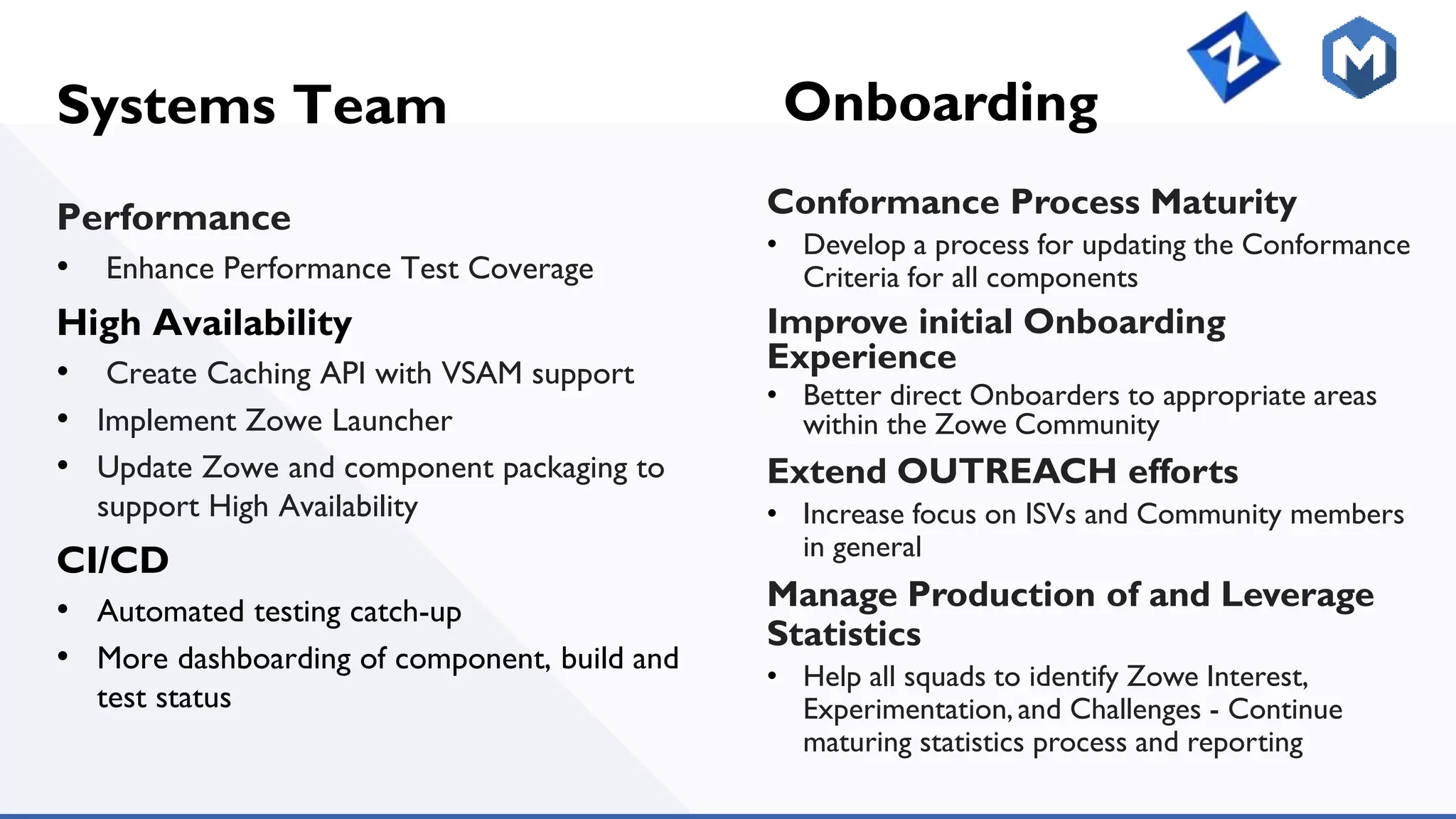
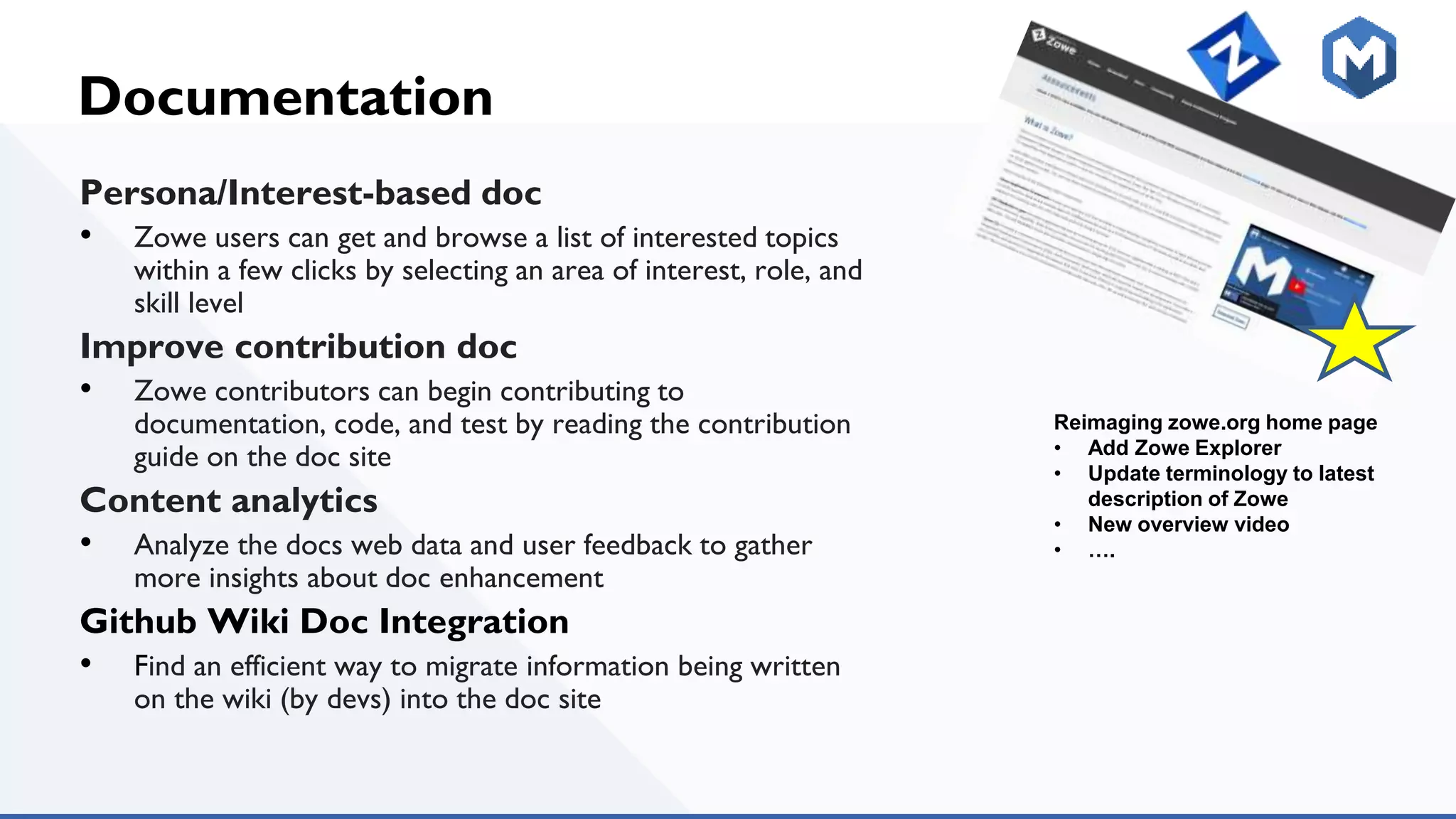
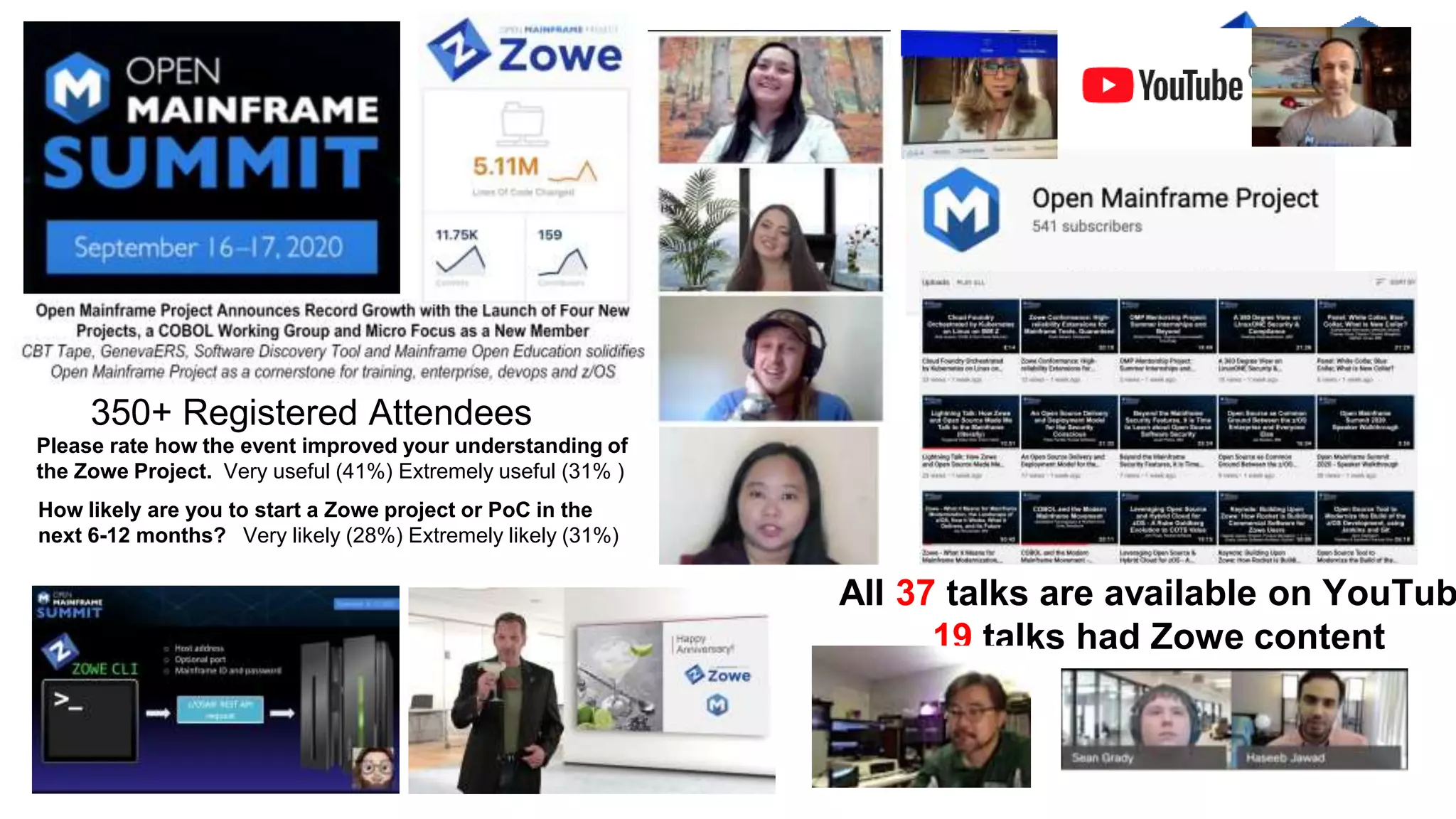
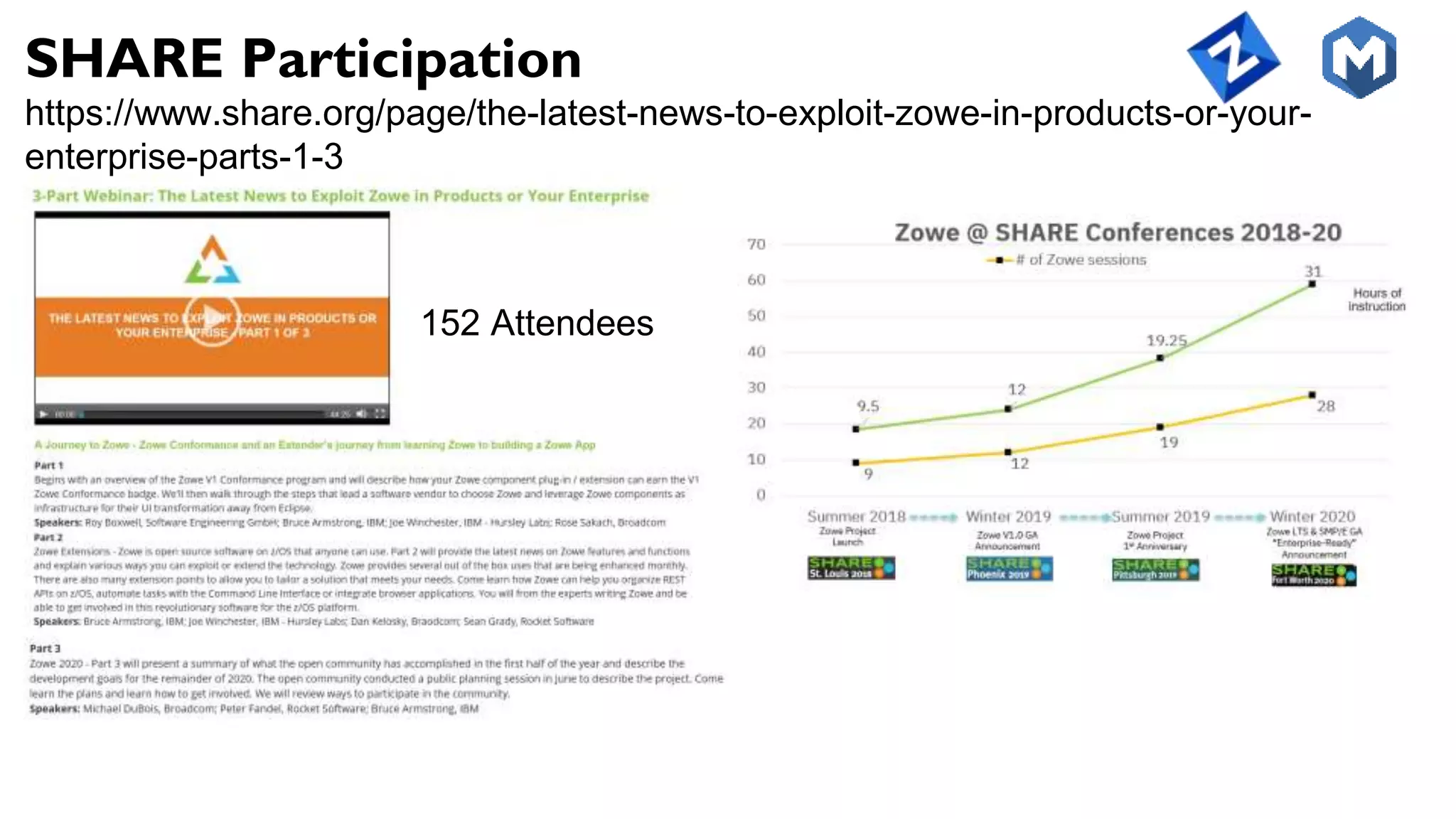
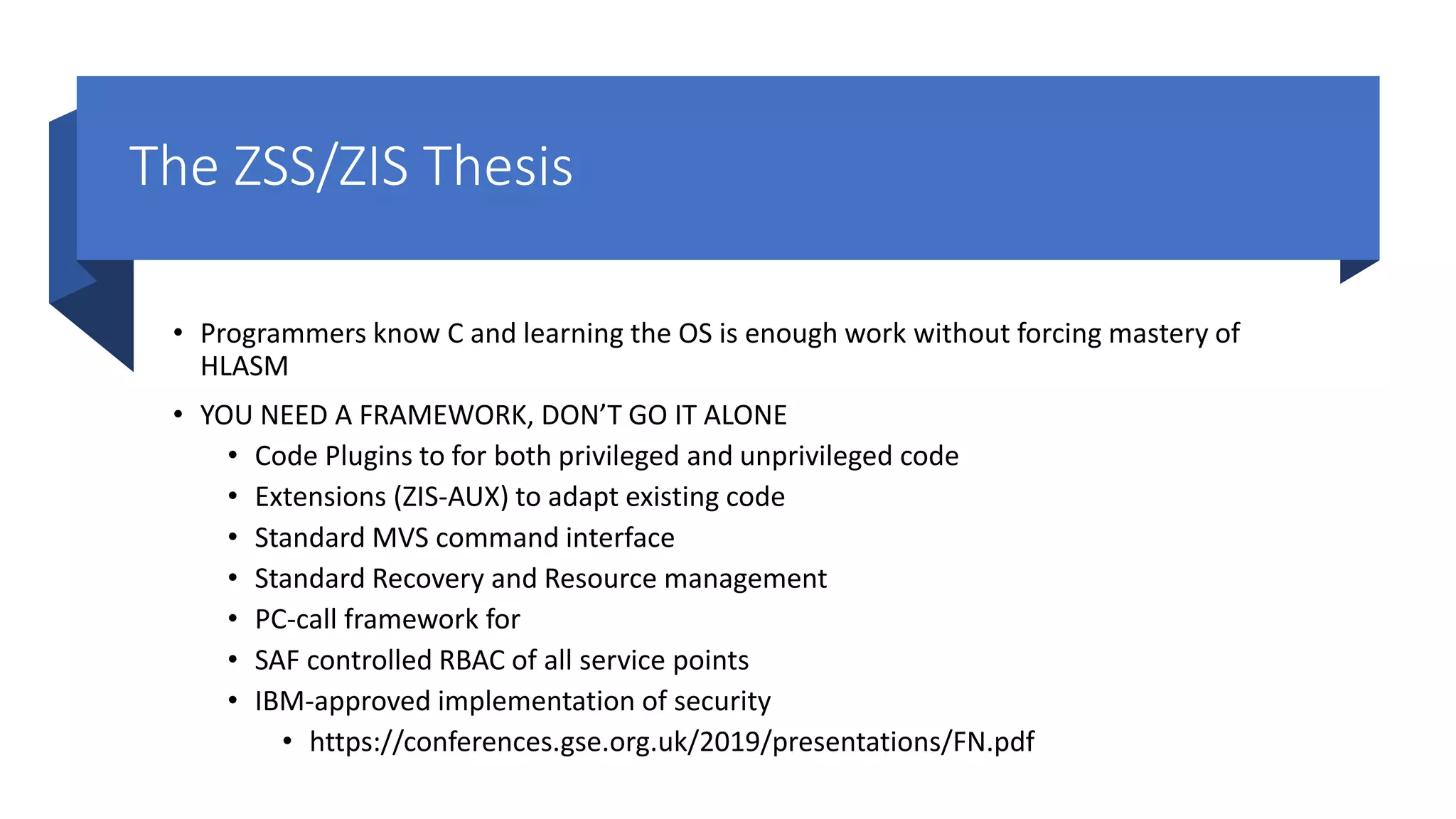
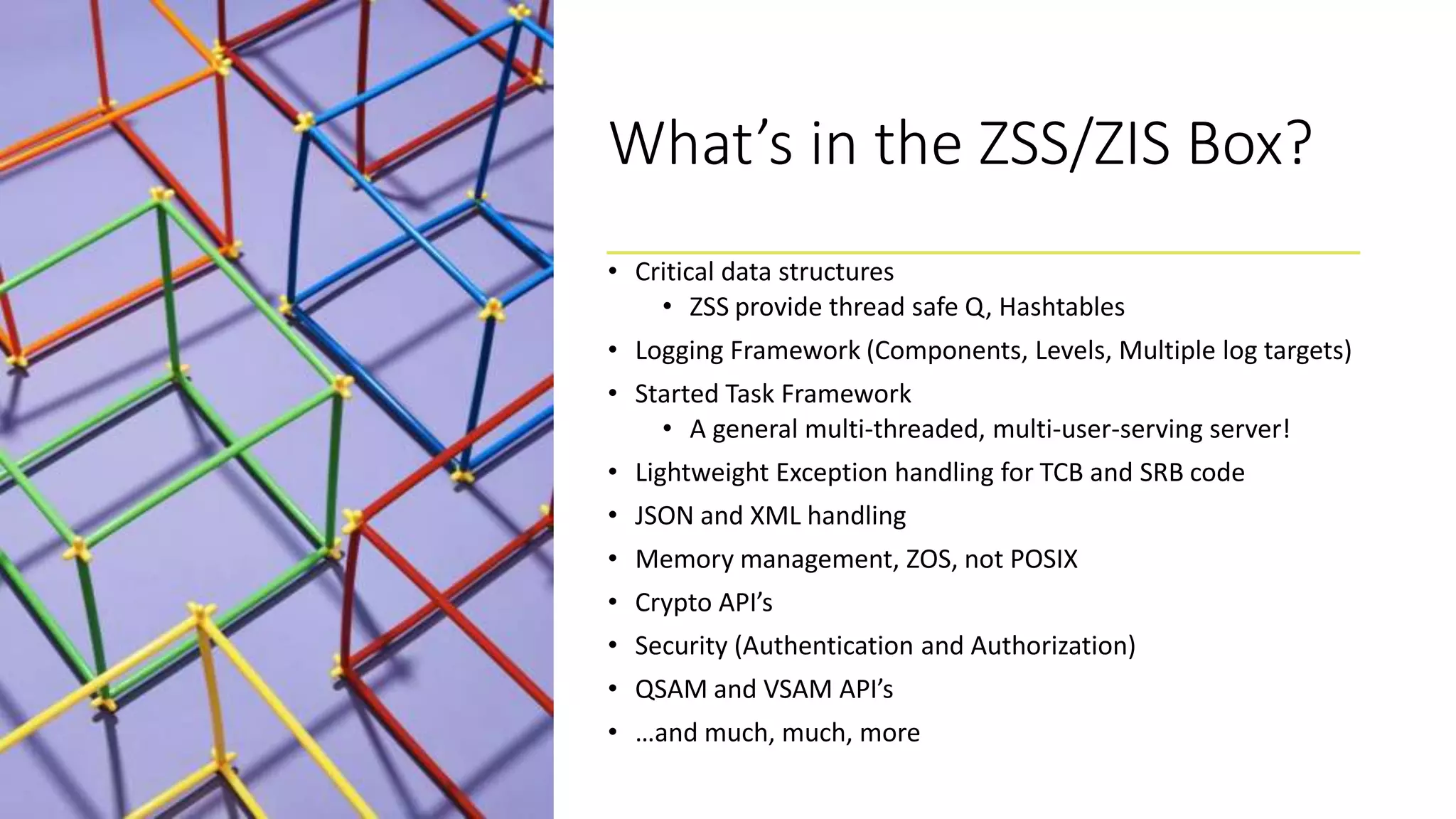
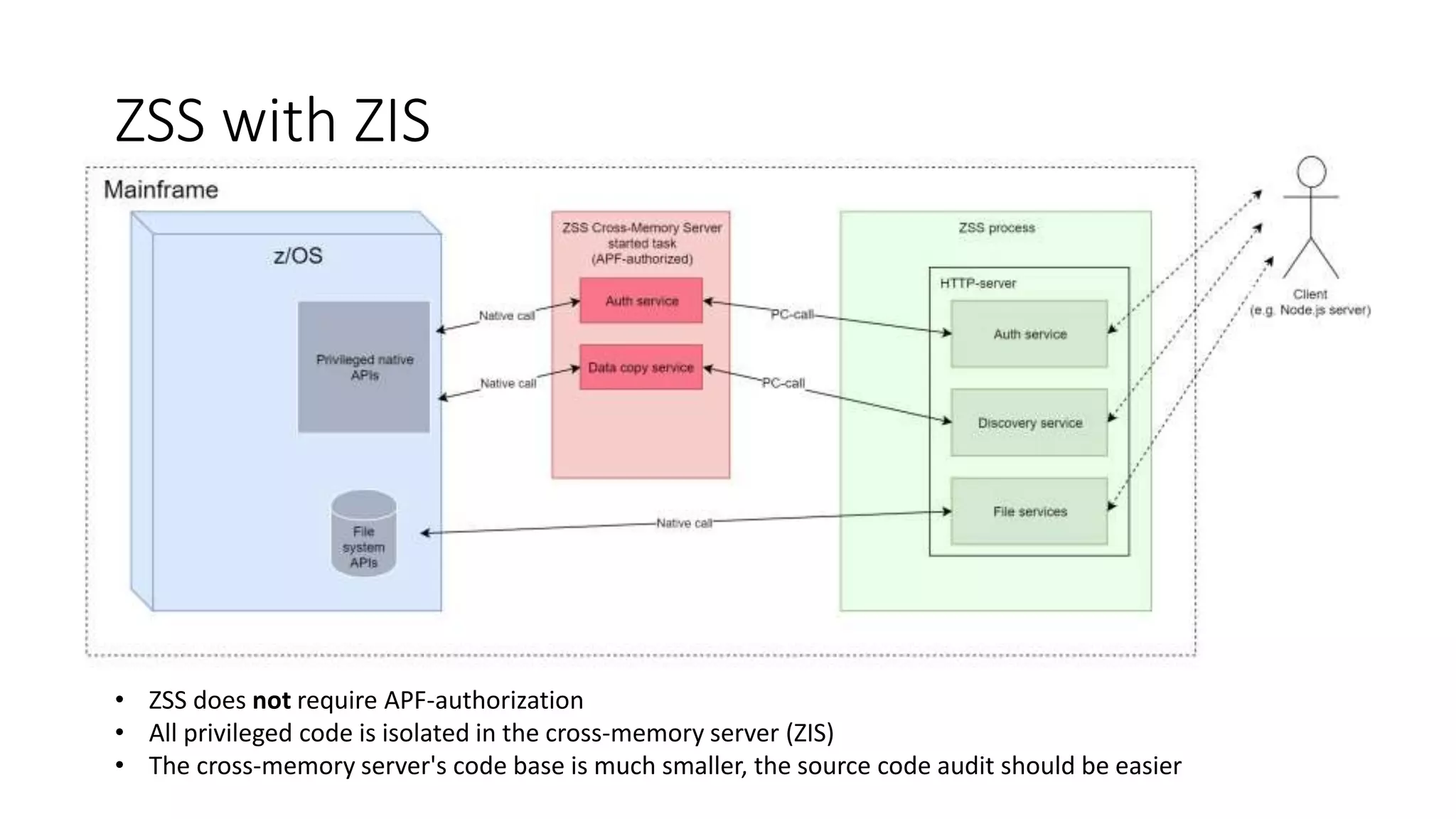
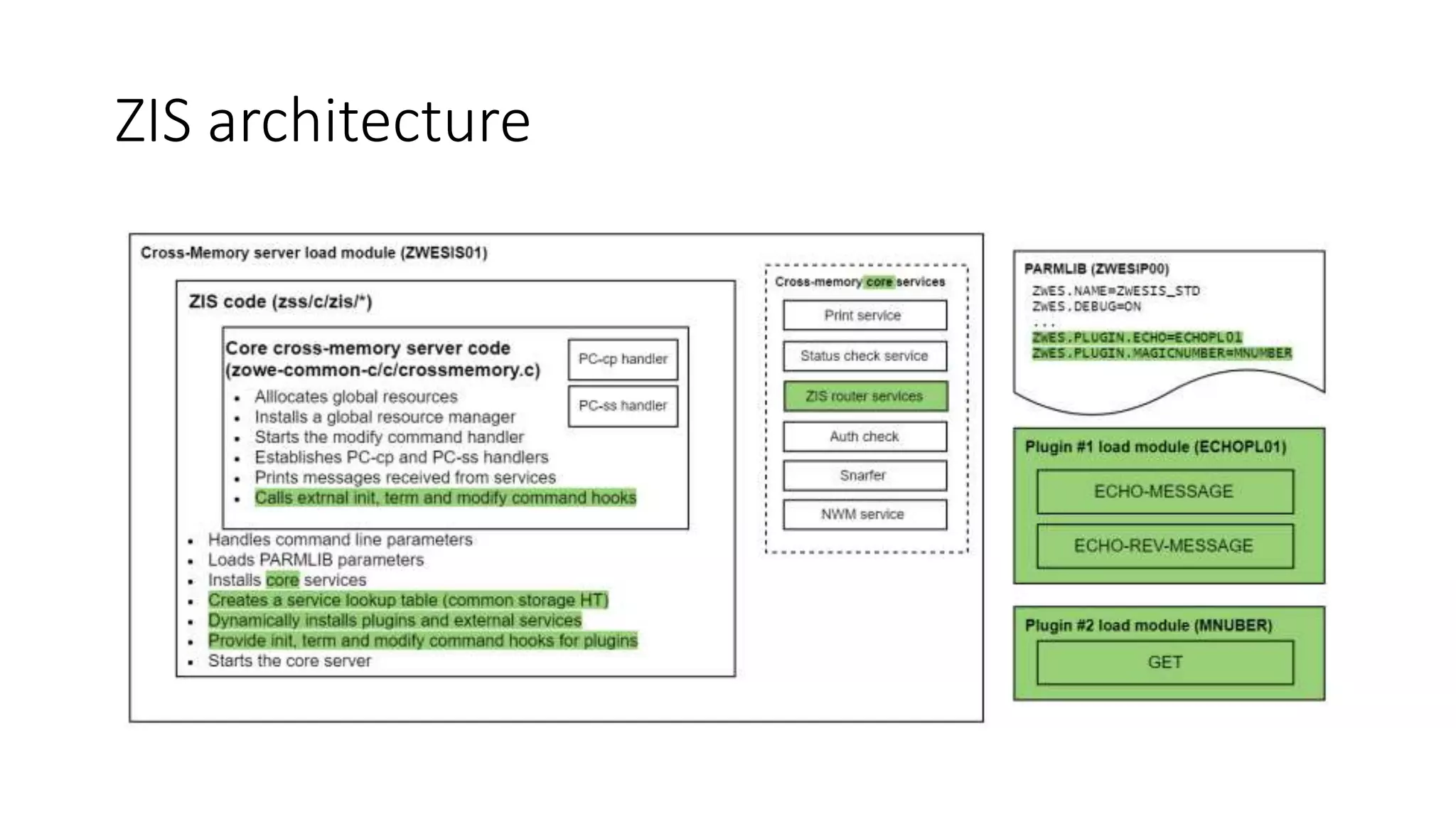
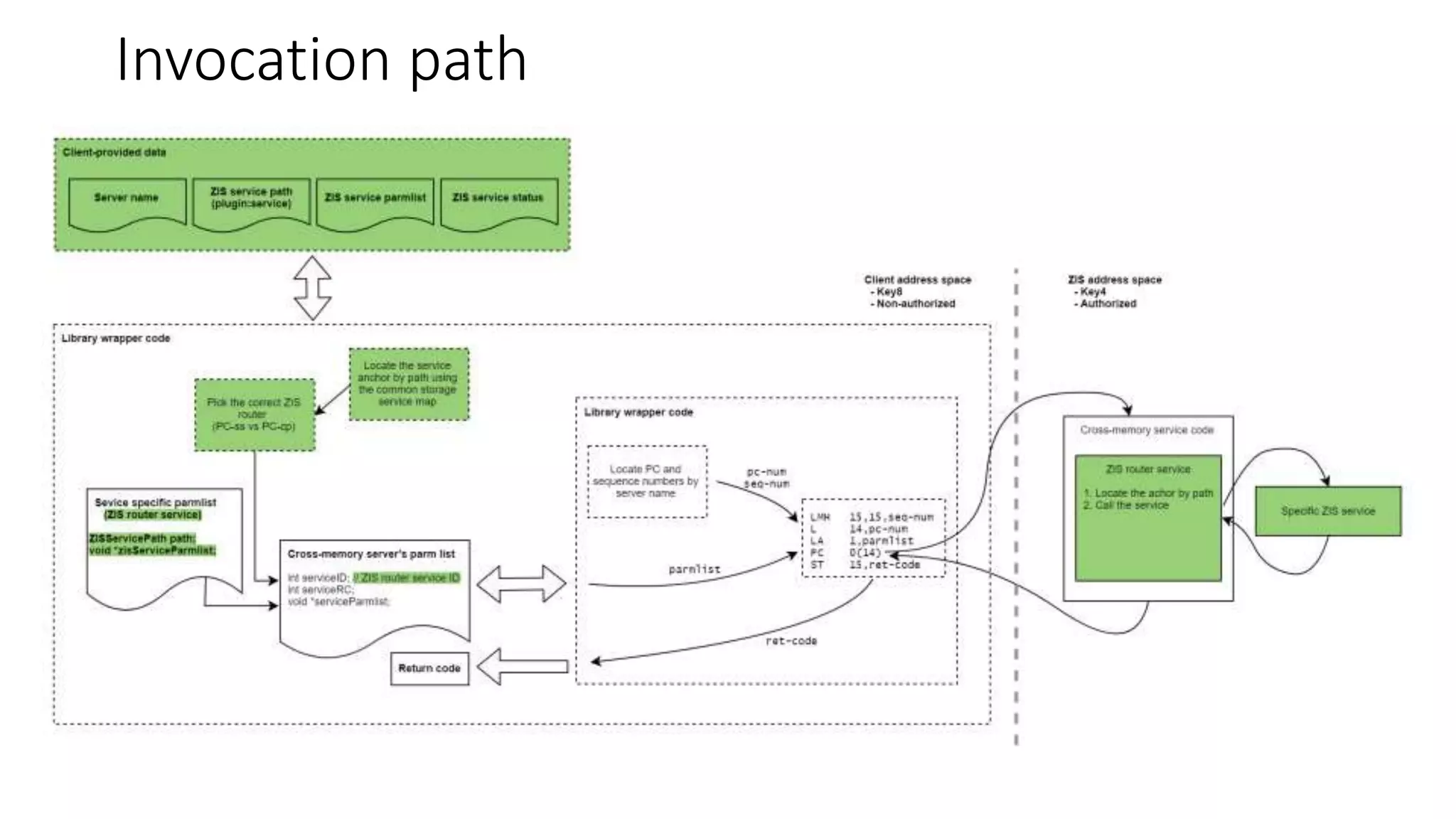
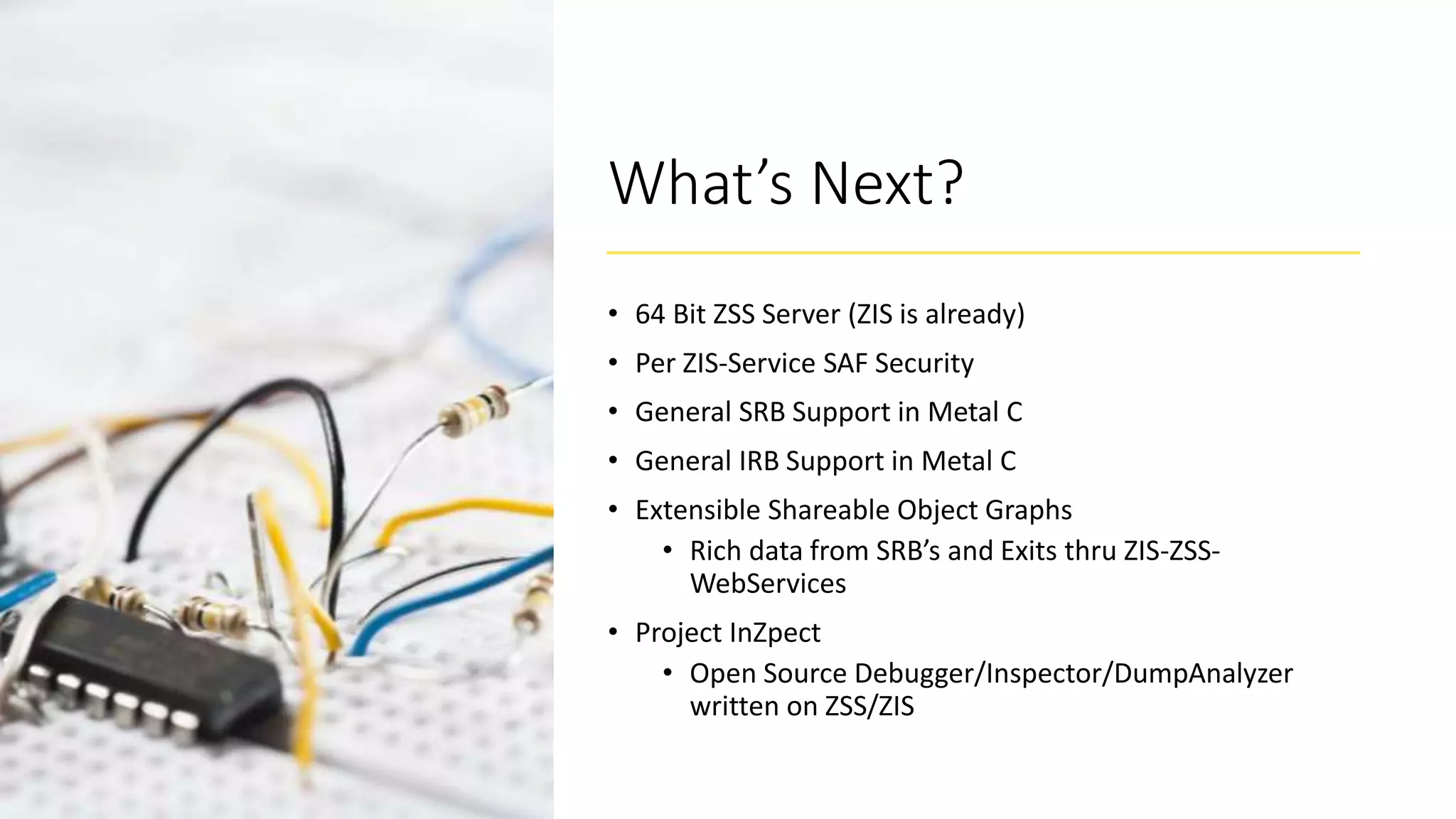
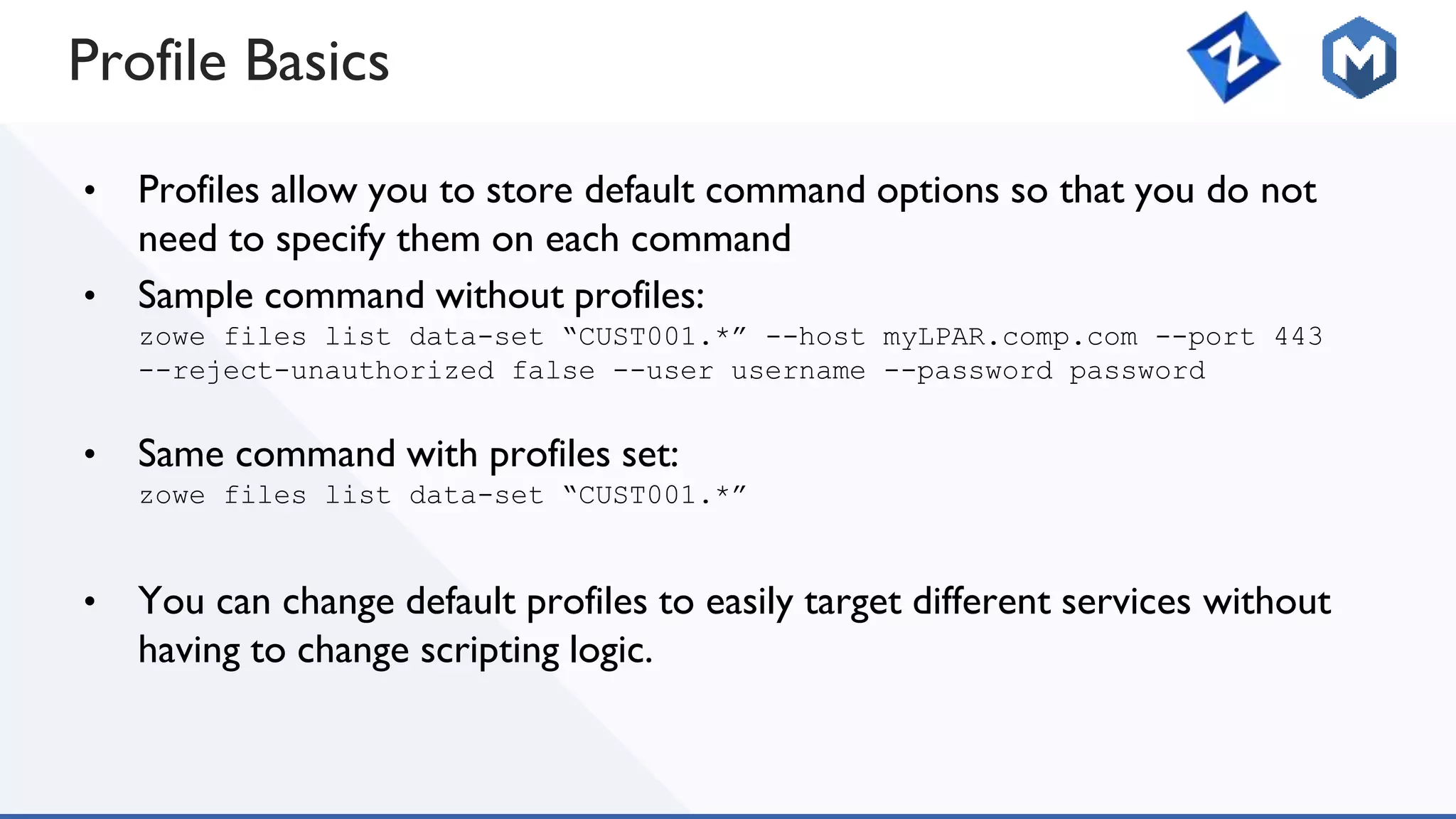
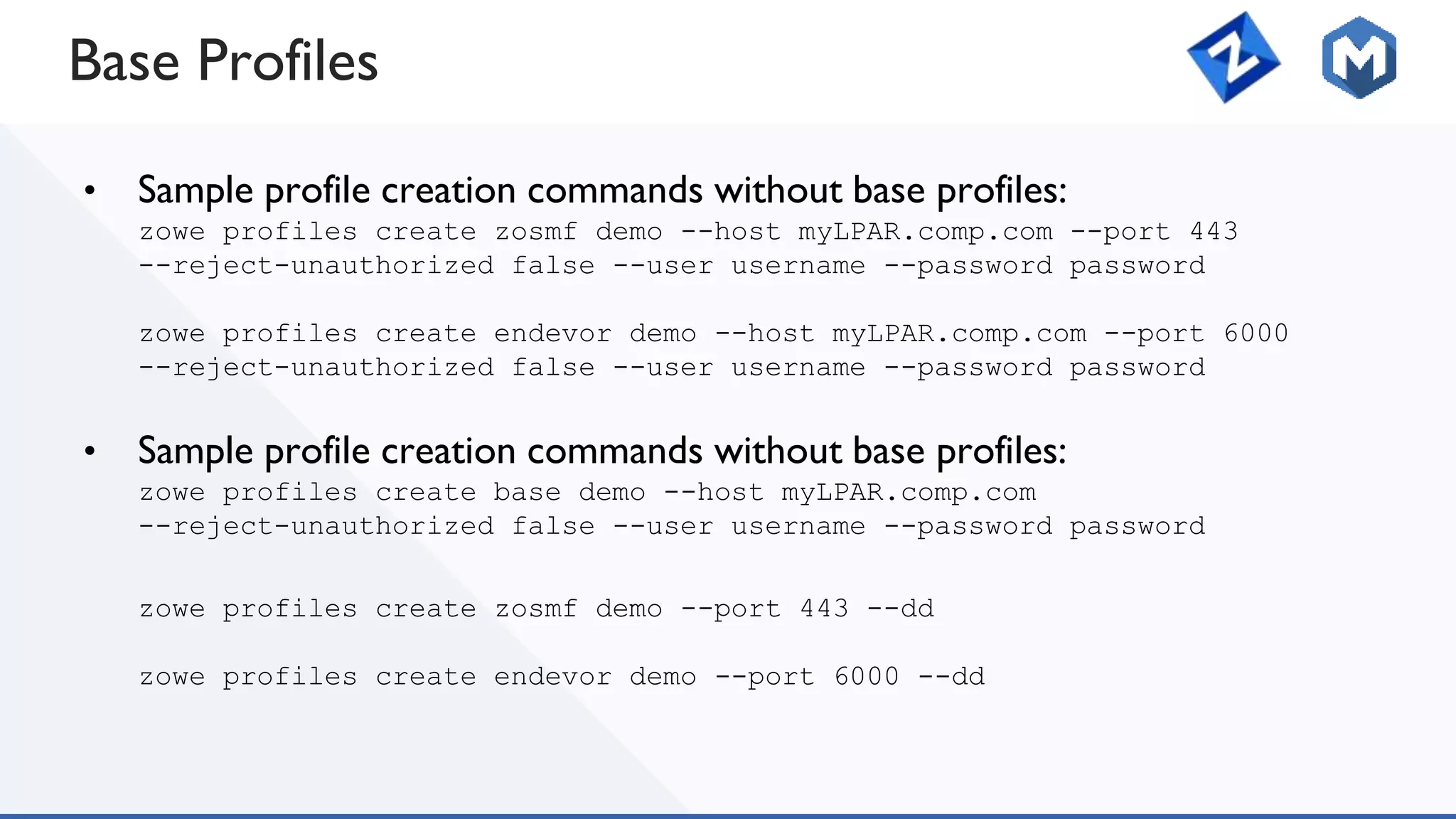
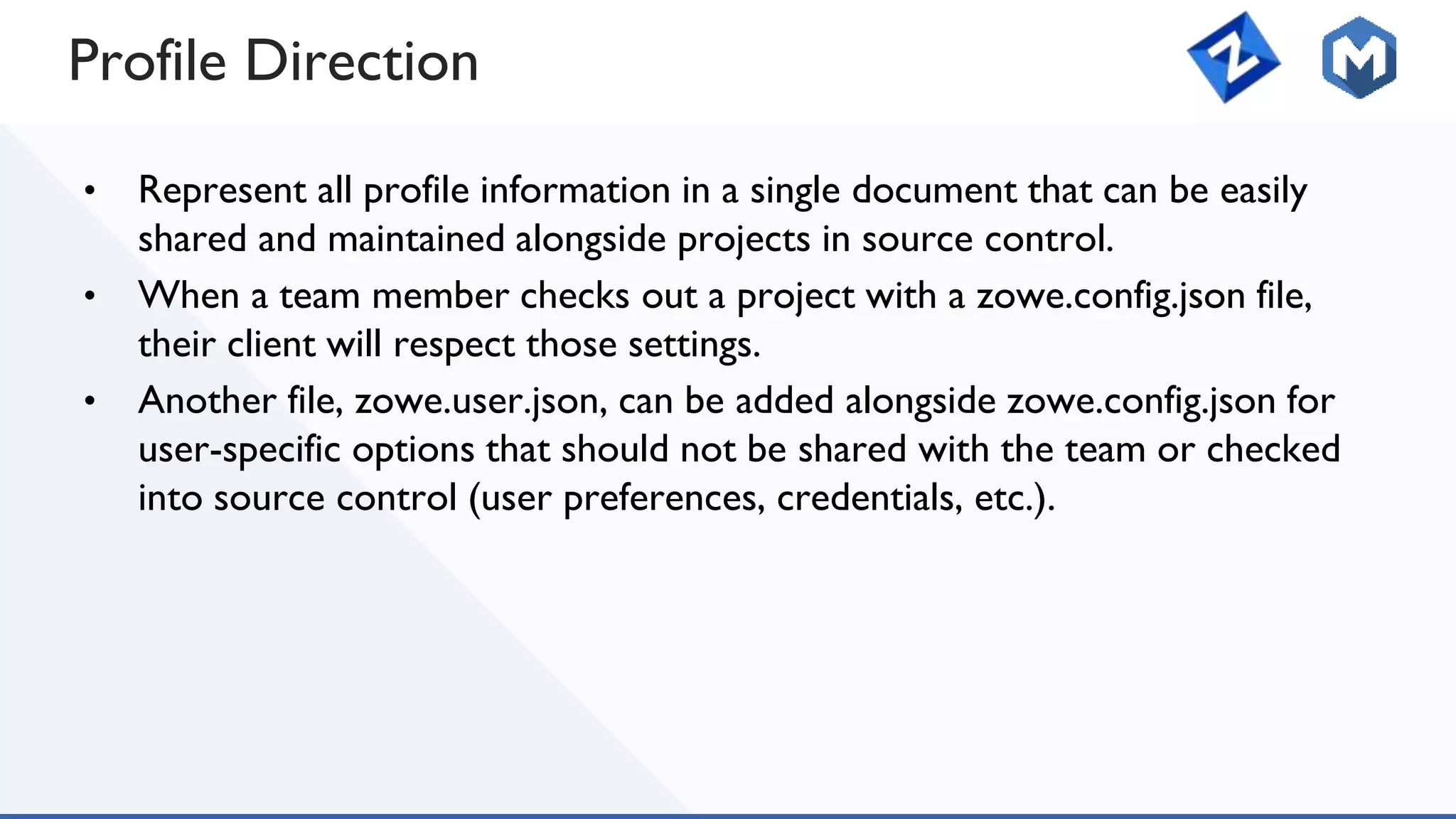
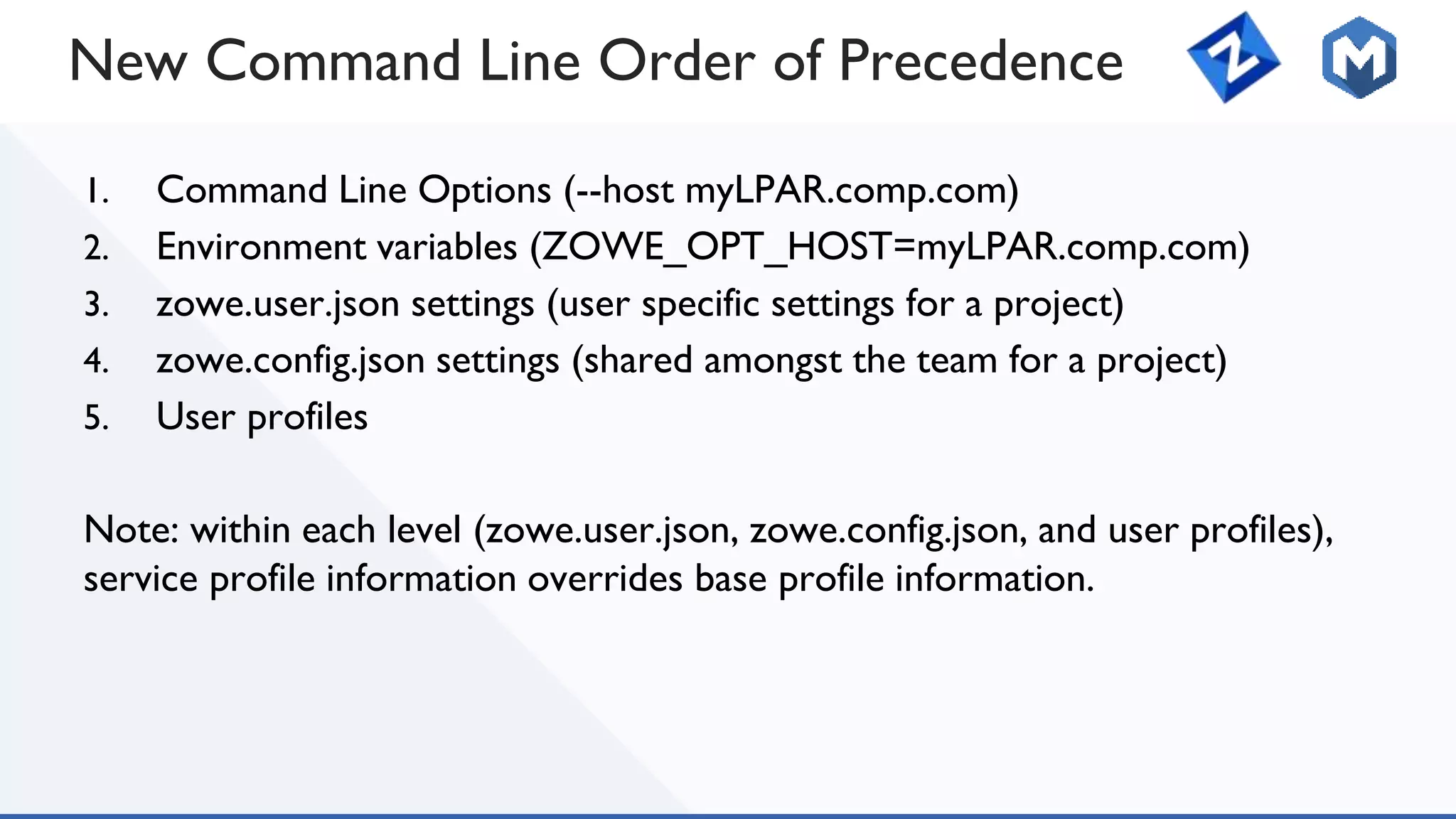
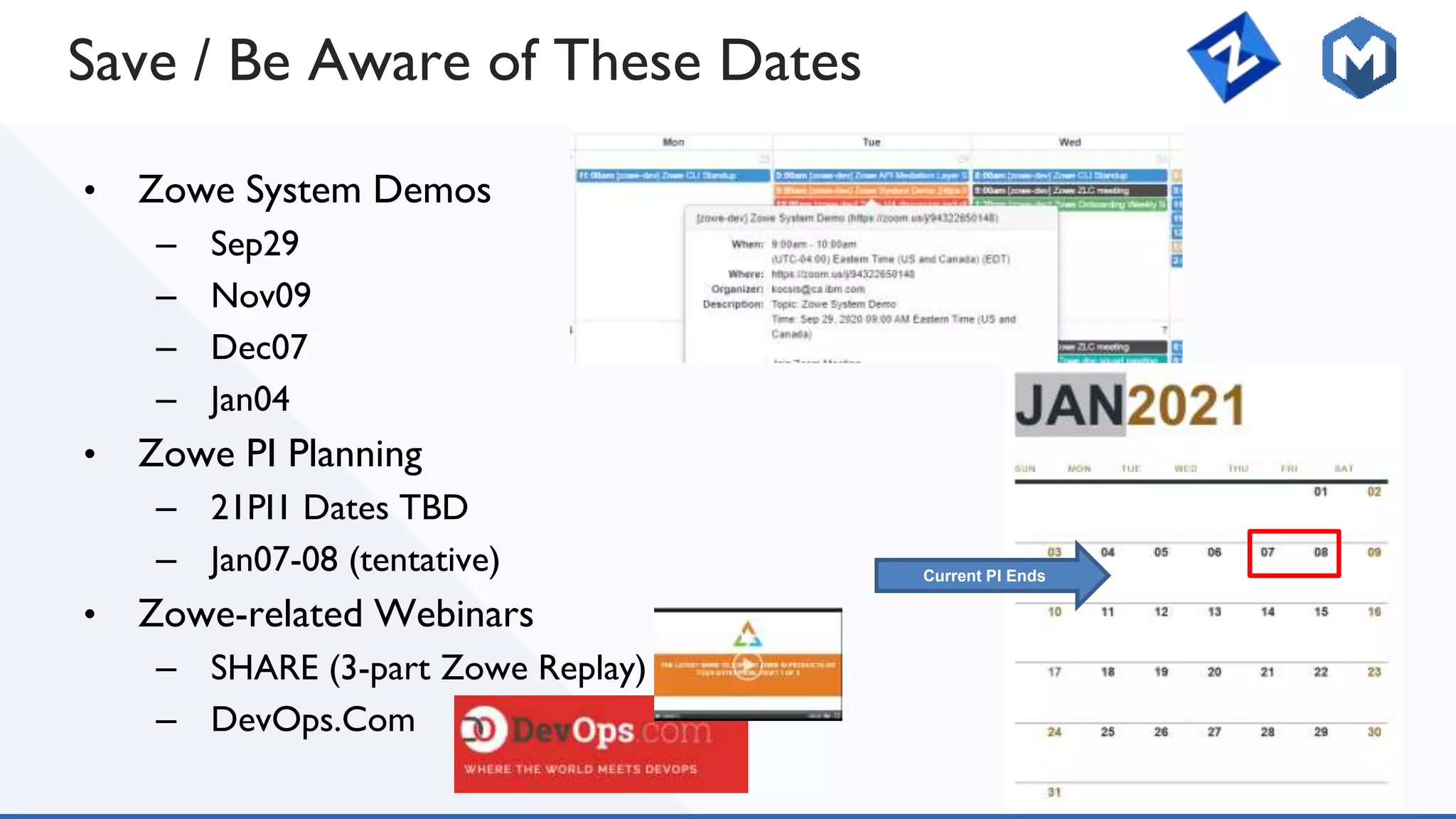
The October 2020 Zowe quarterly update highlights the ongoing development efforts within the Zowe community, focusing on various squads and their specific projects such as Zowe Explorer, Zowe CLI, and API mediation layer enhancements. Key topics include improvements in onboarding processes, performance testing, document management, and the introduction of privileged programming capabilities for z/OS applications. The webinar attracted over 350 participants, showcasing the community's engagement and interest in expanding their use of the Zowe framework.