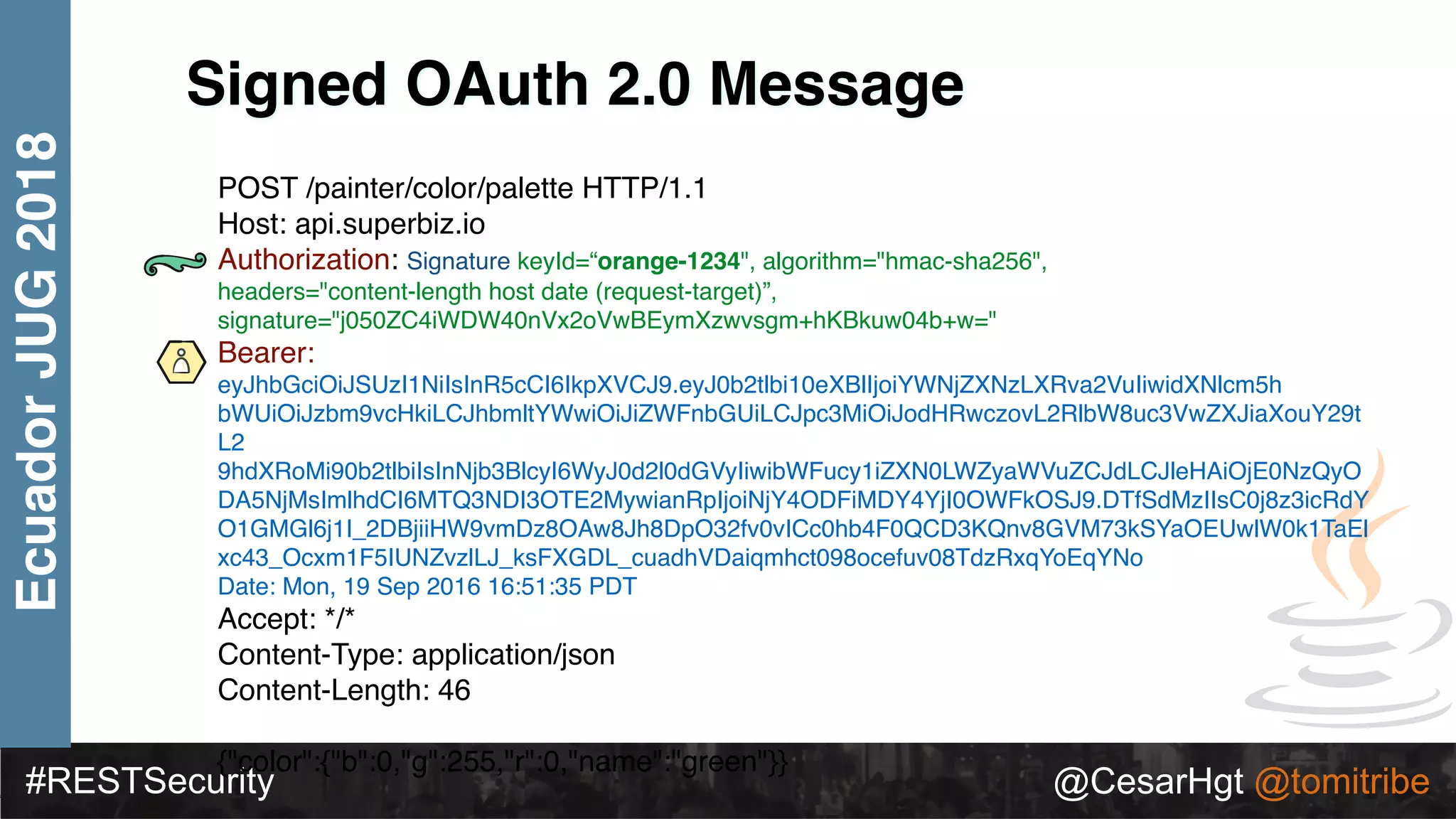
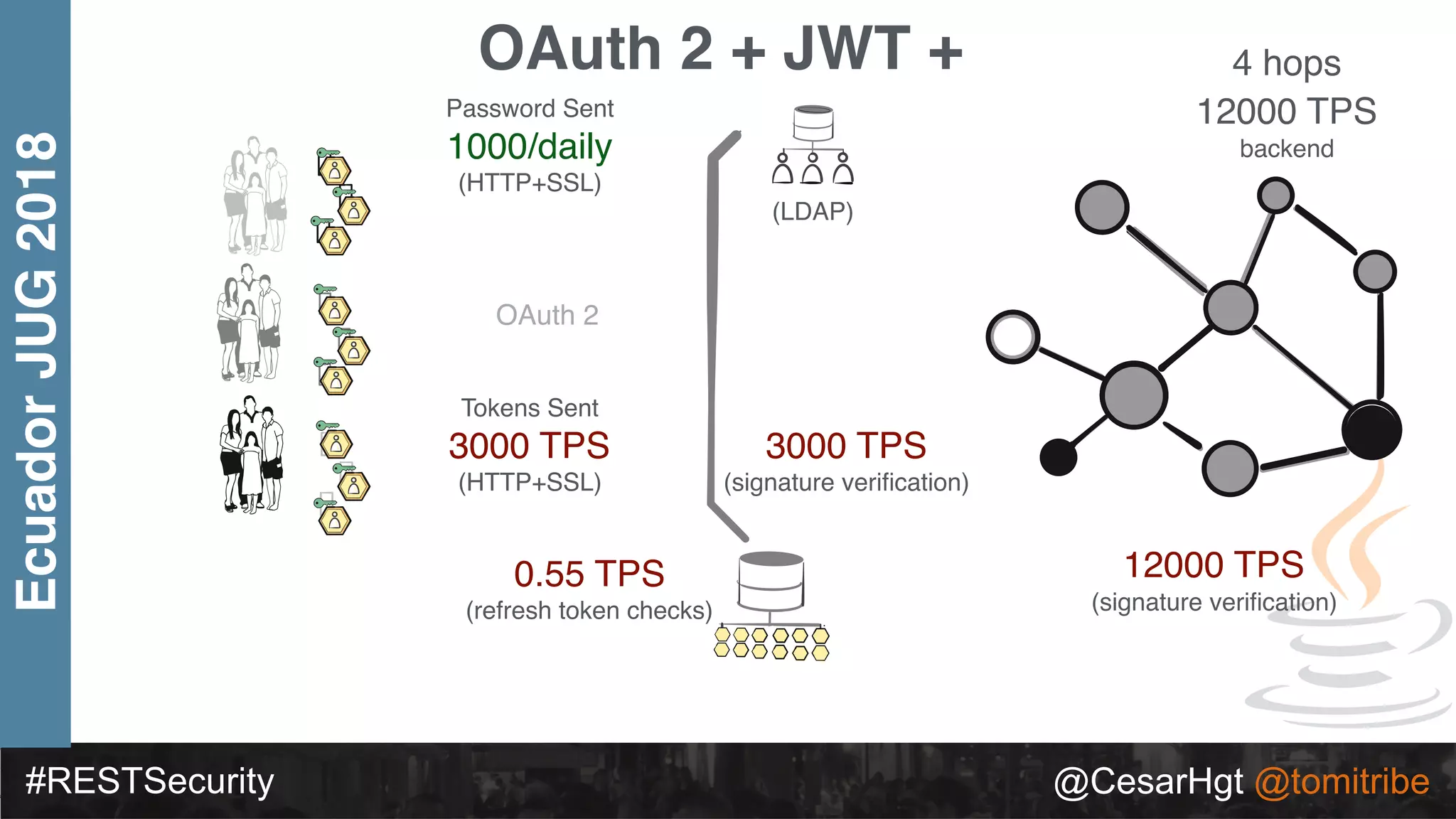
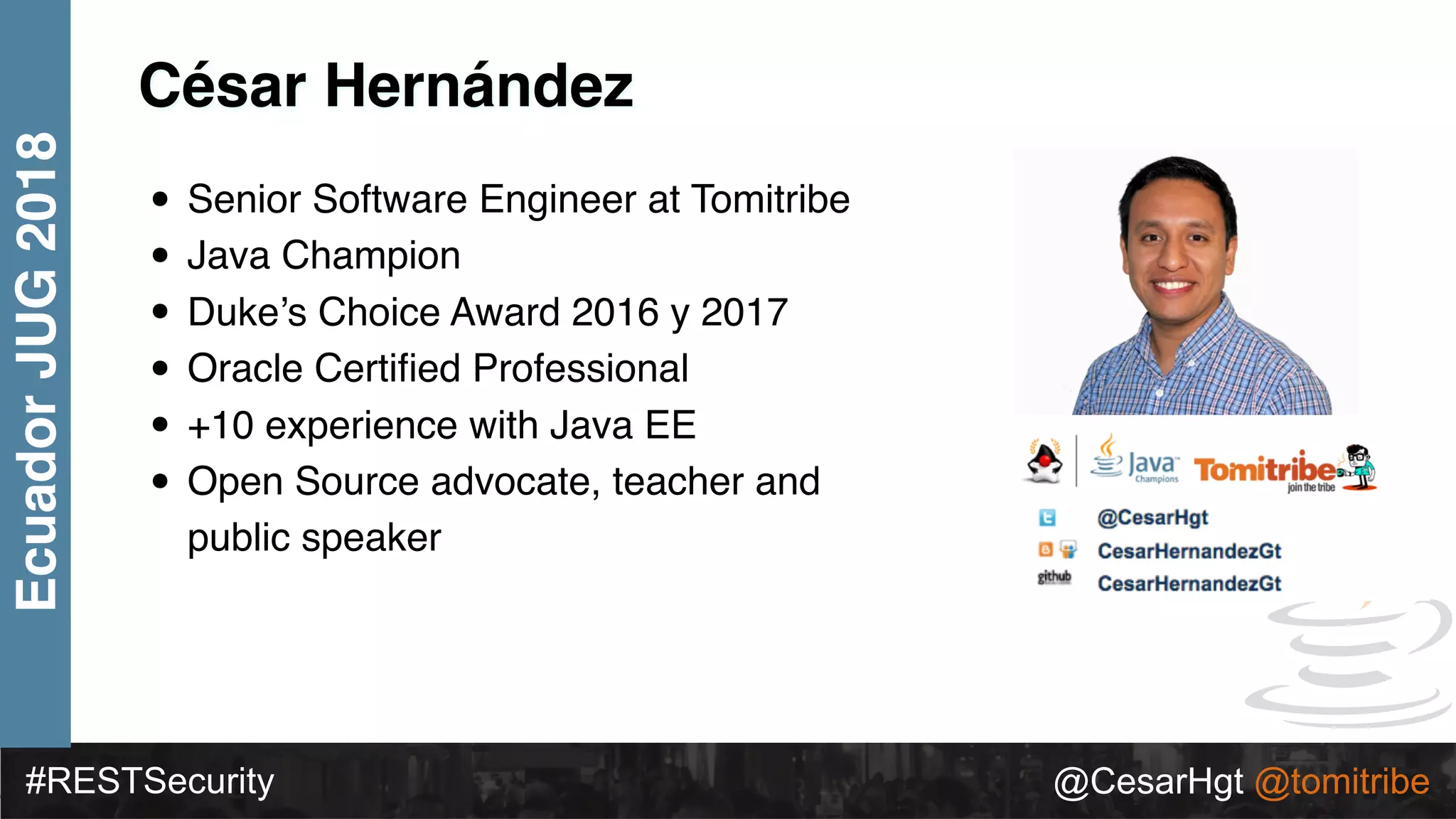
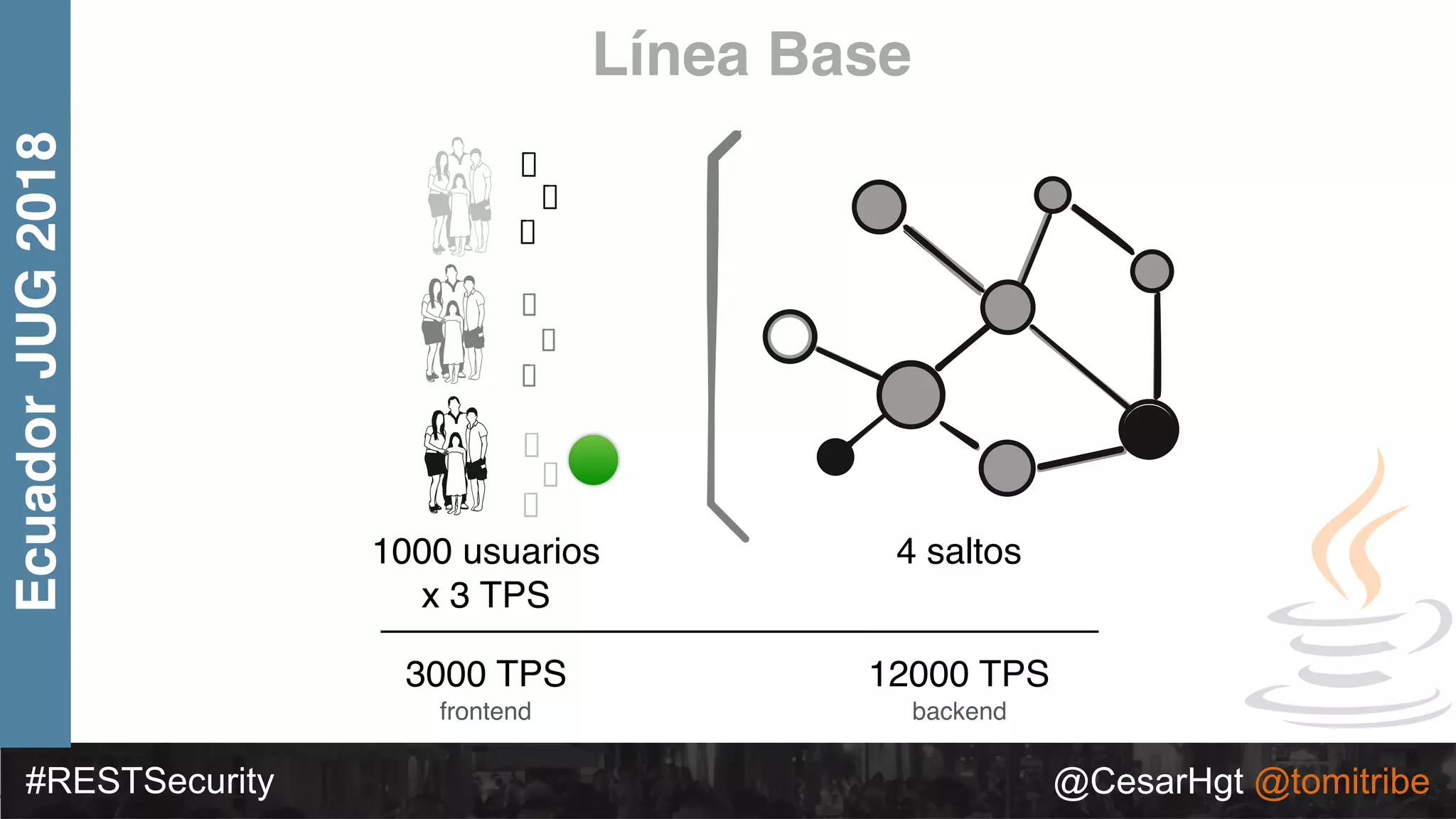
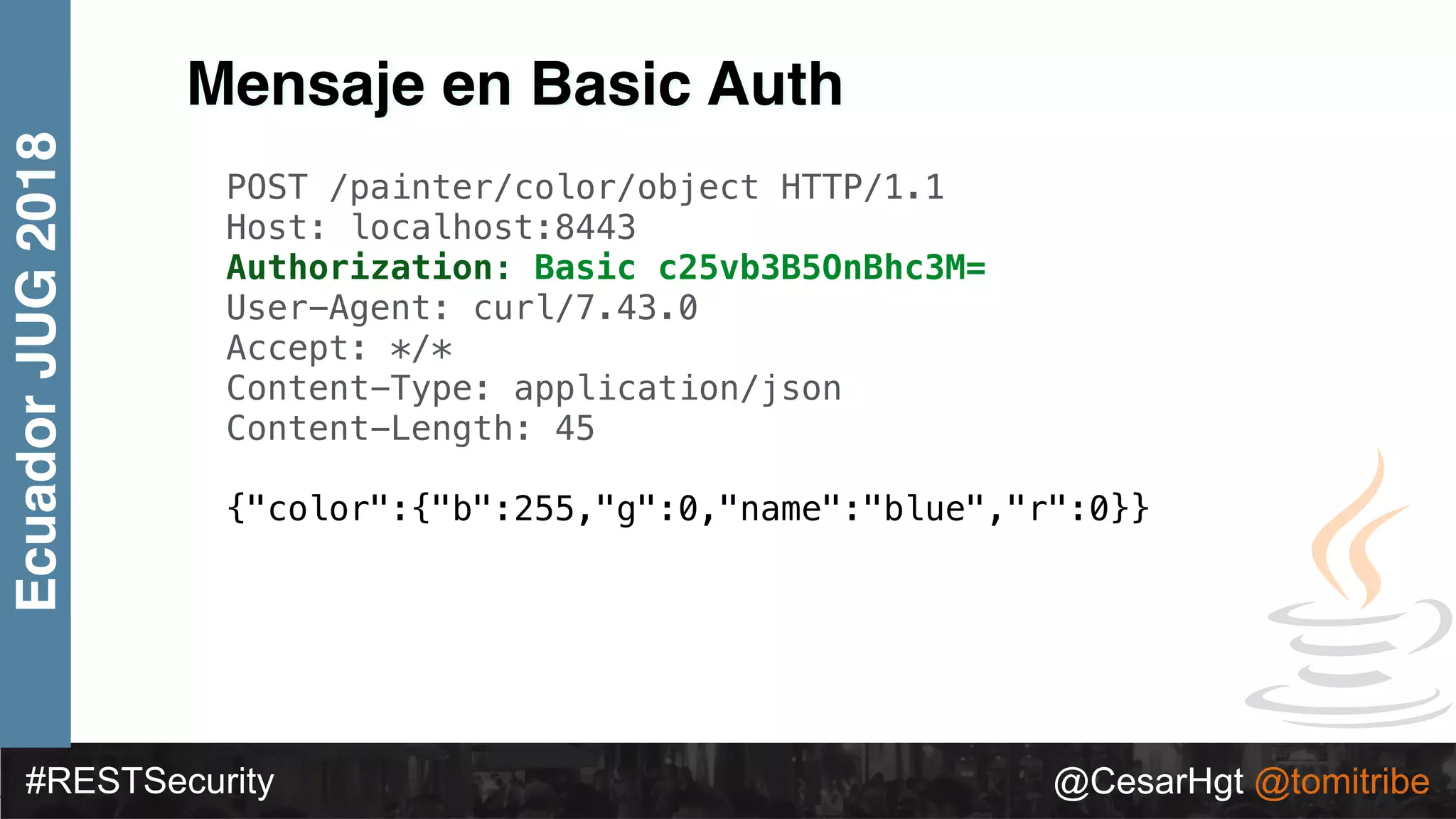
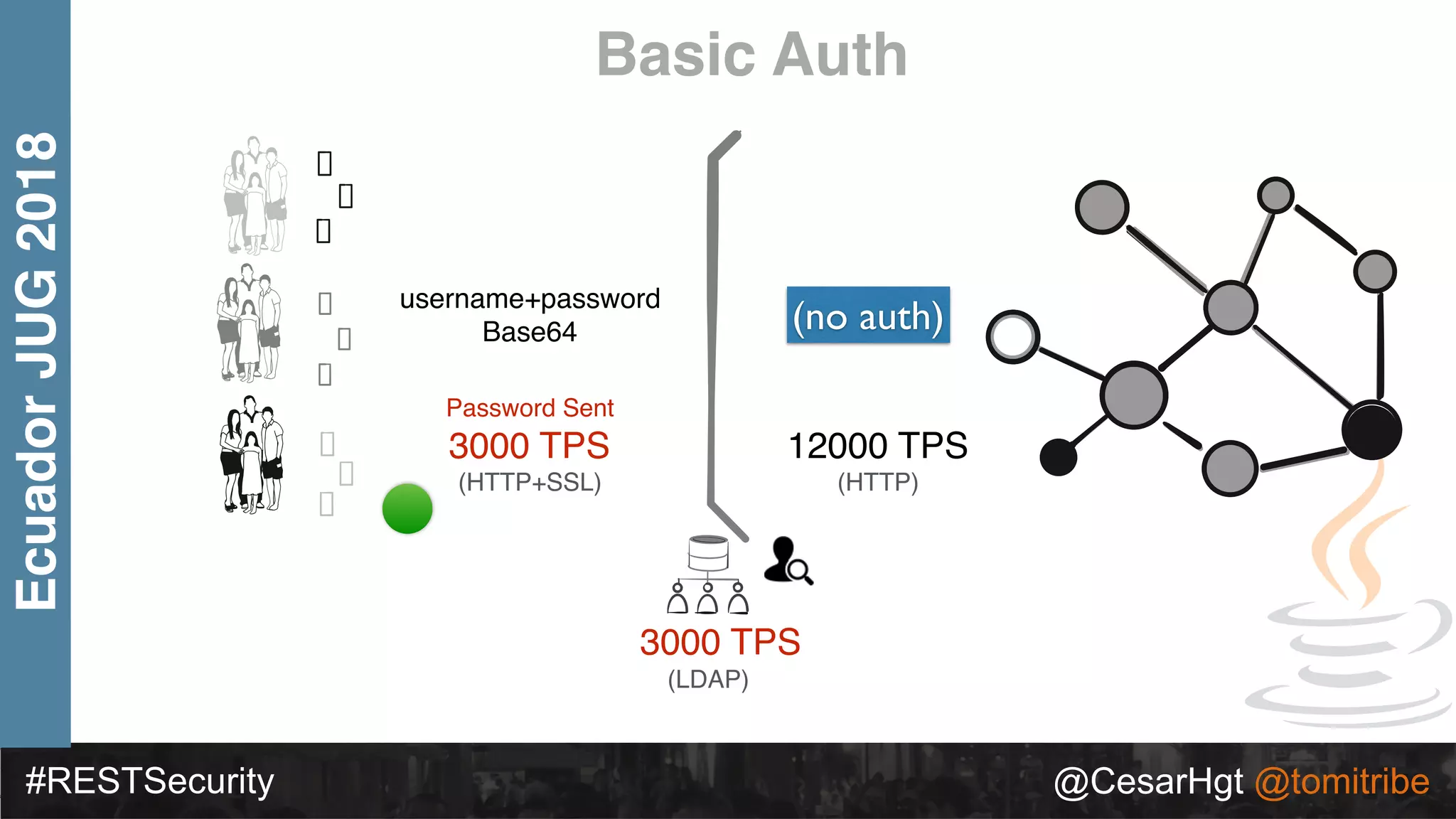
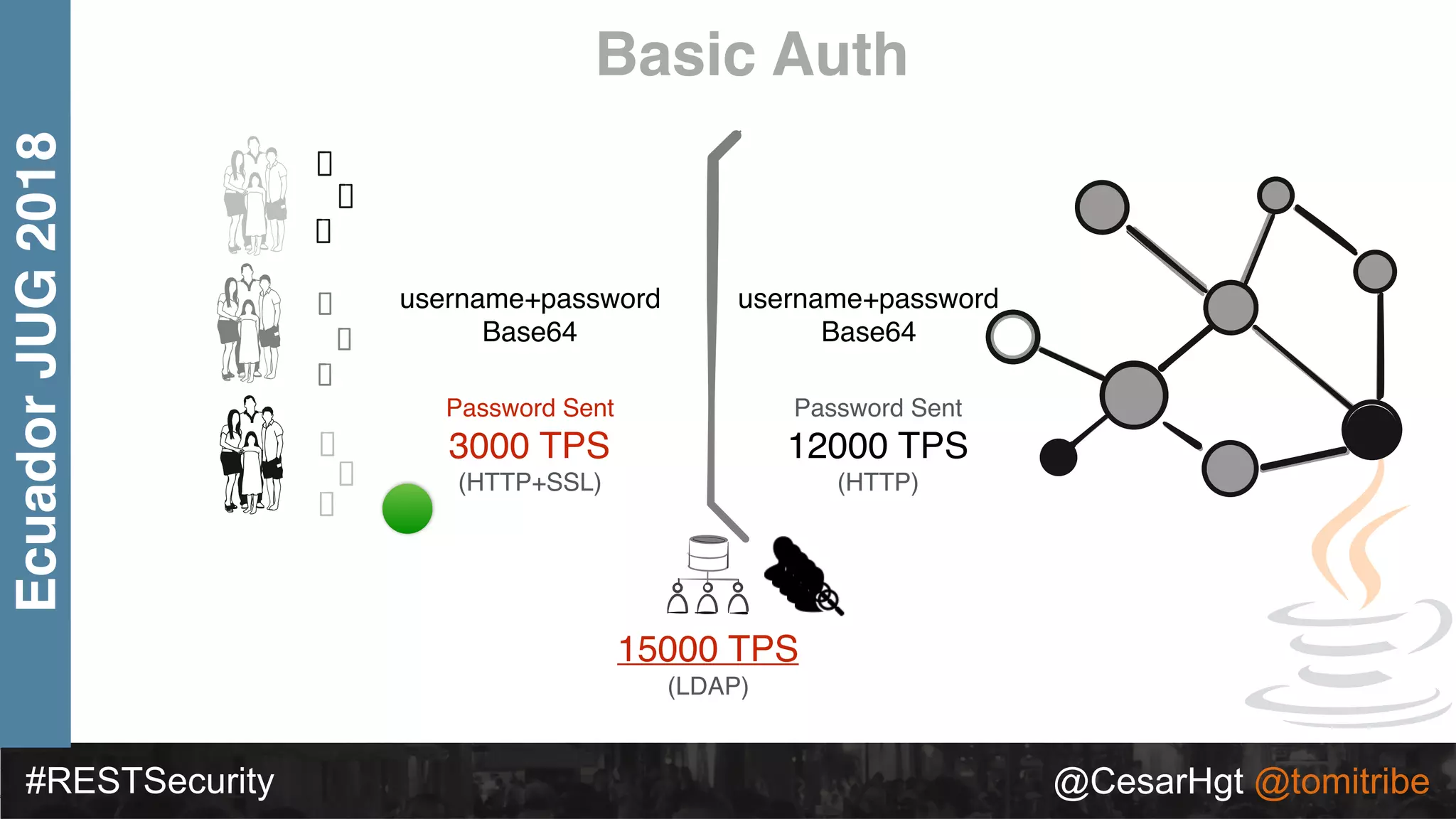
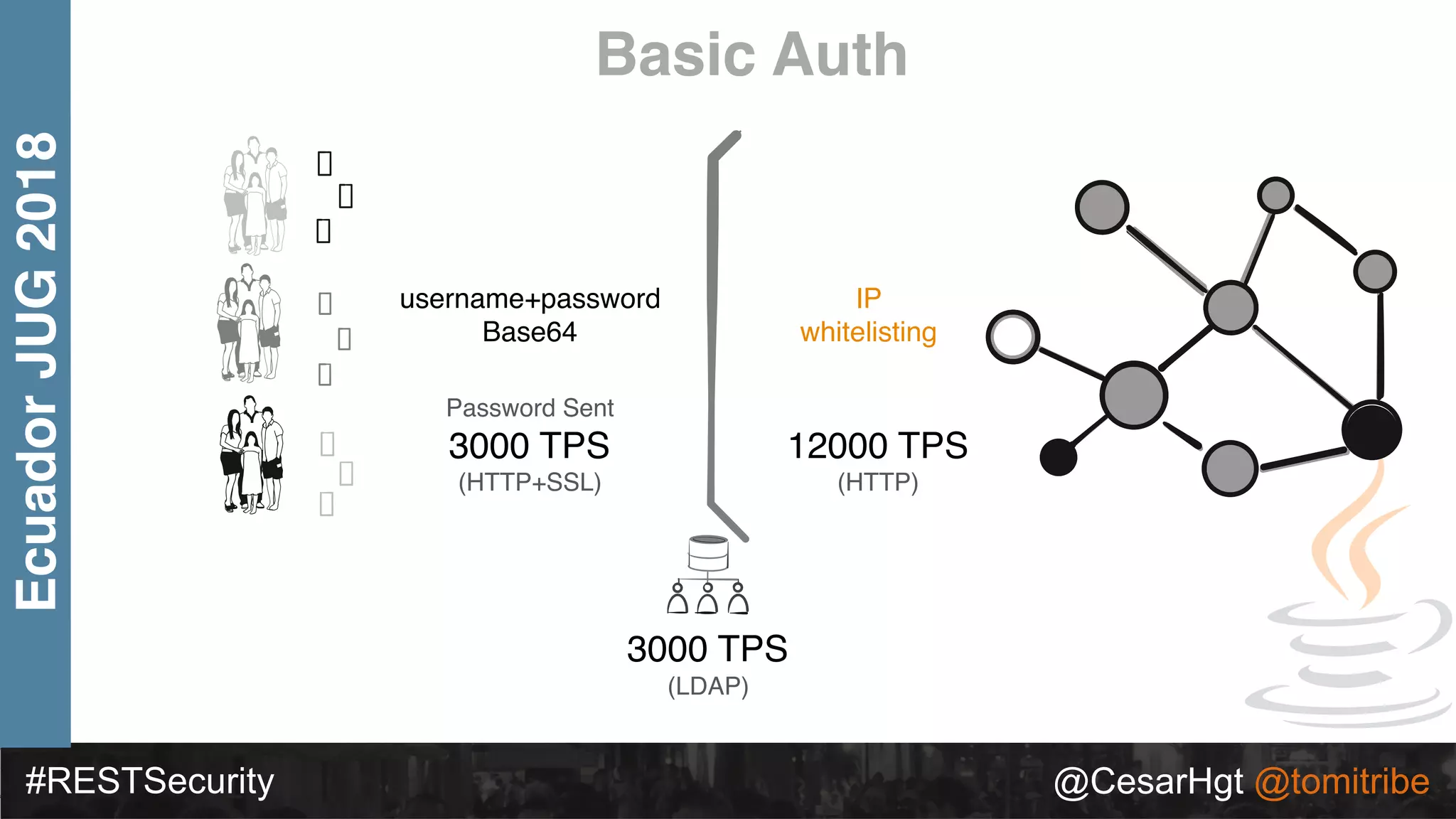
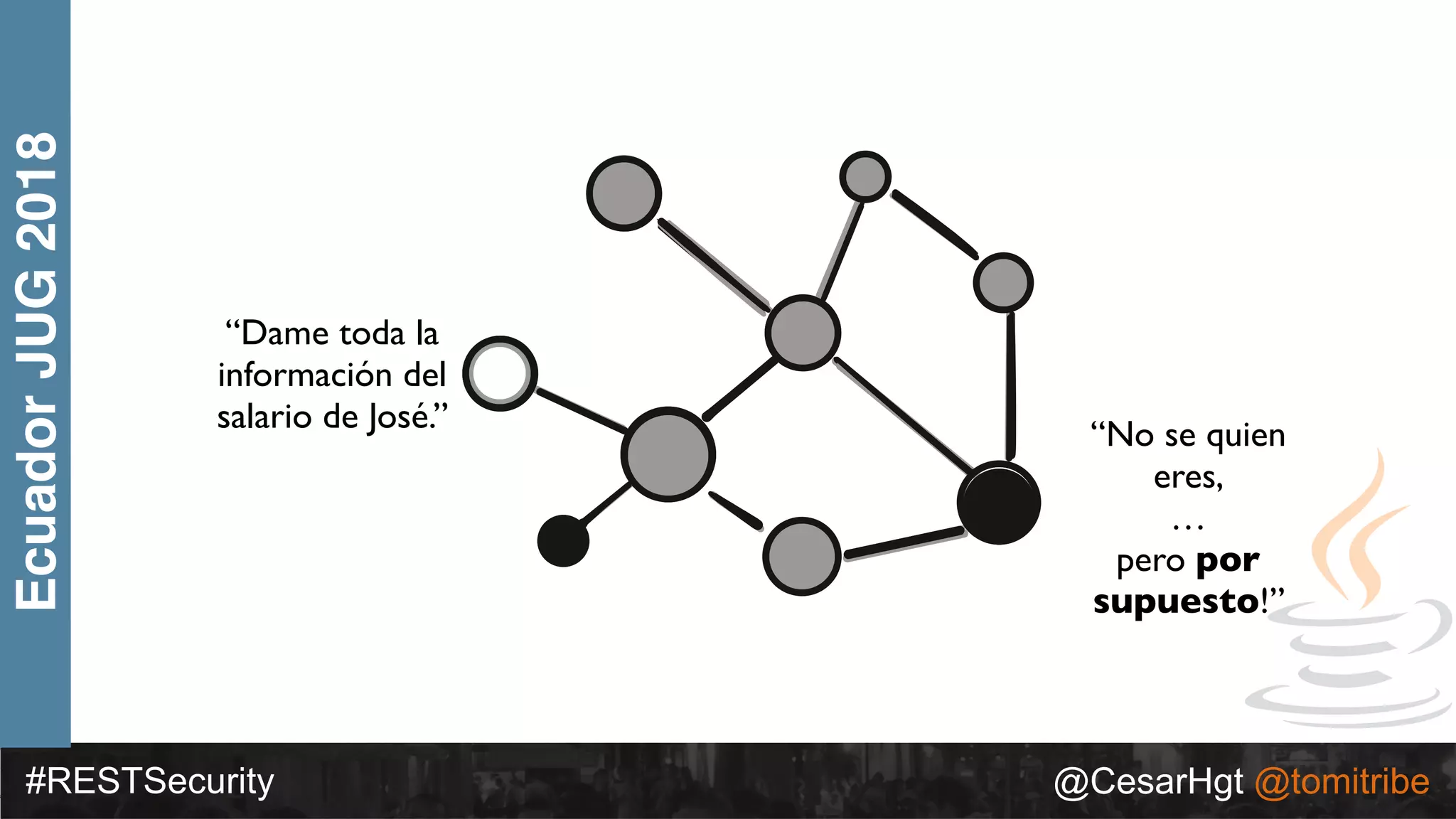
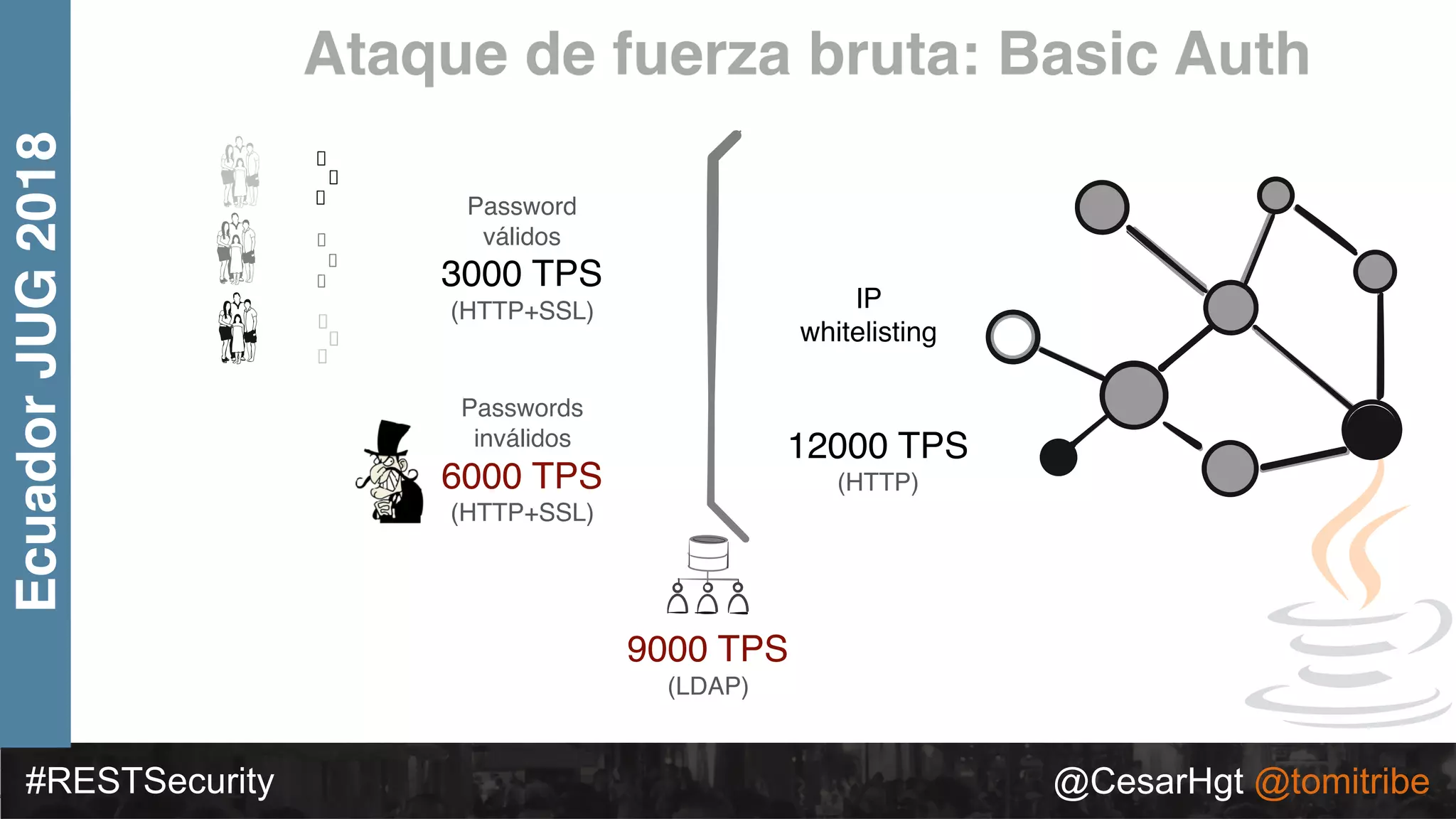
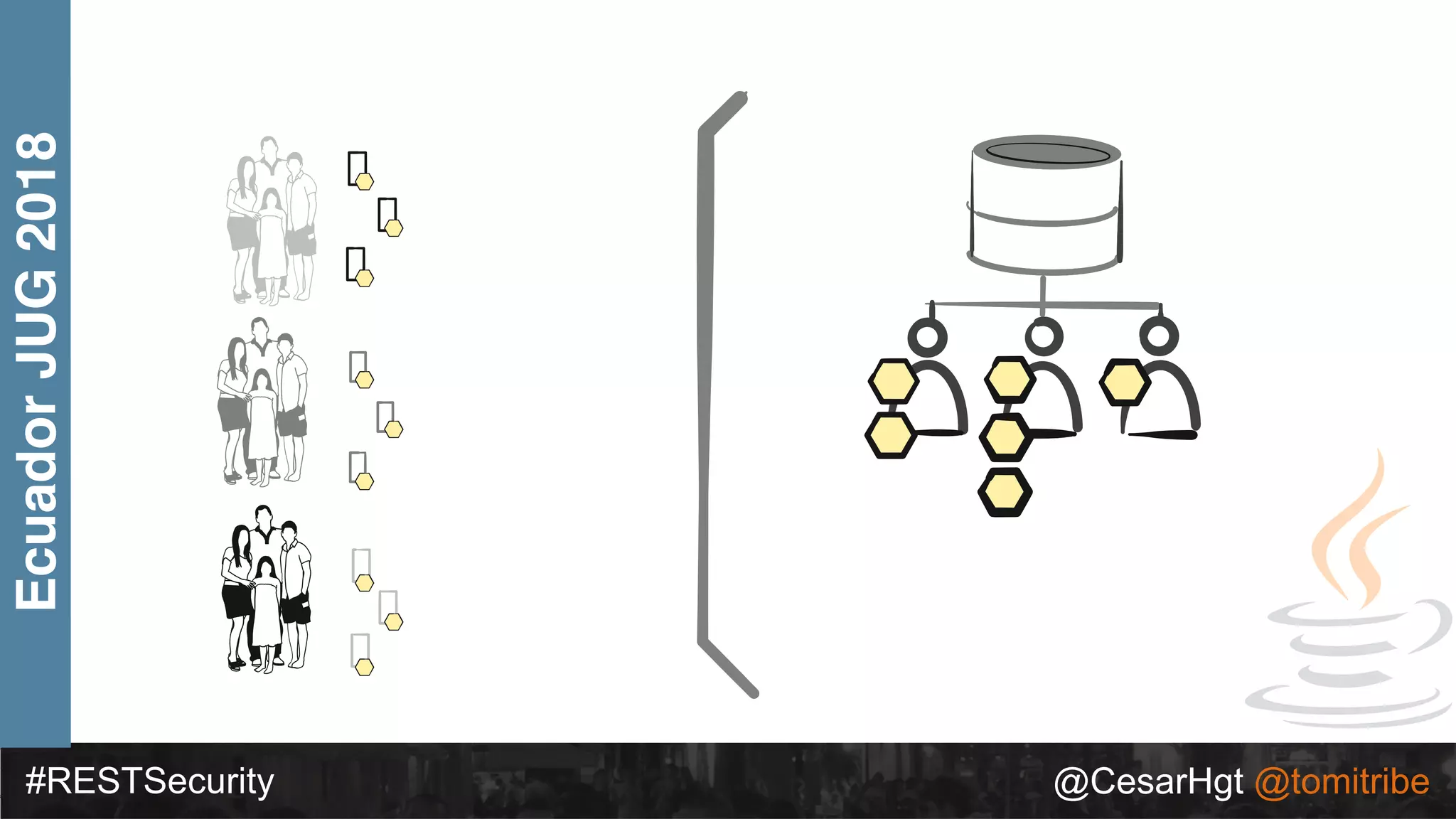
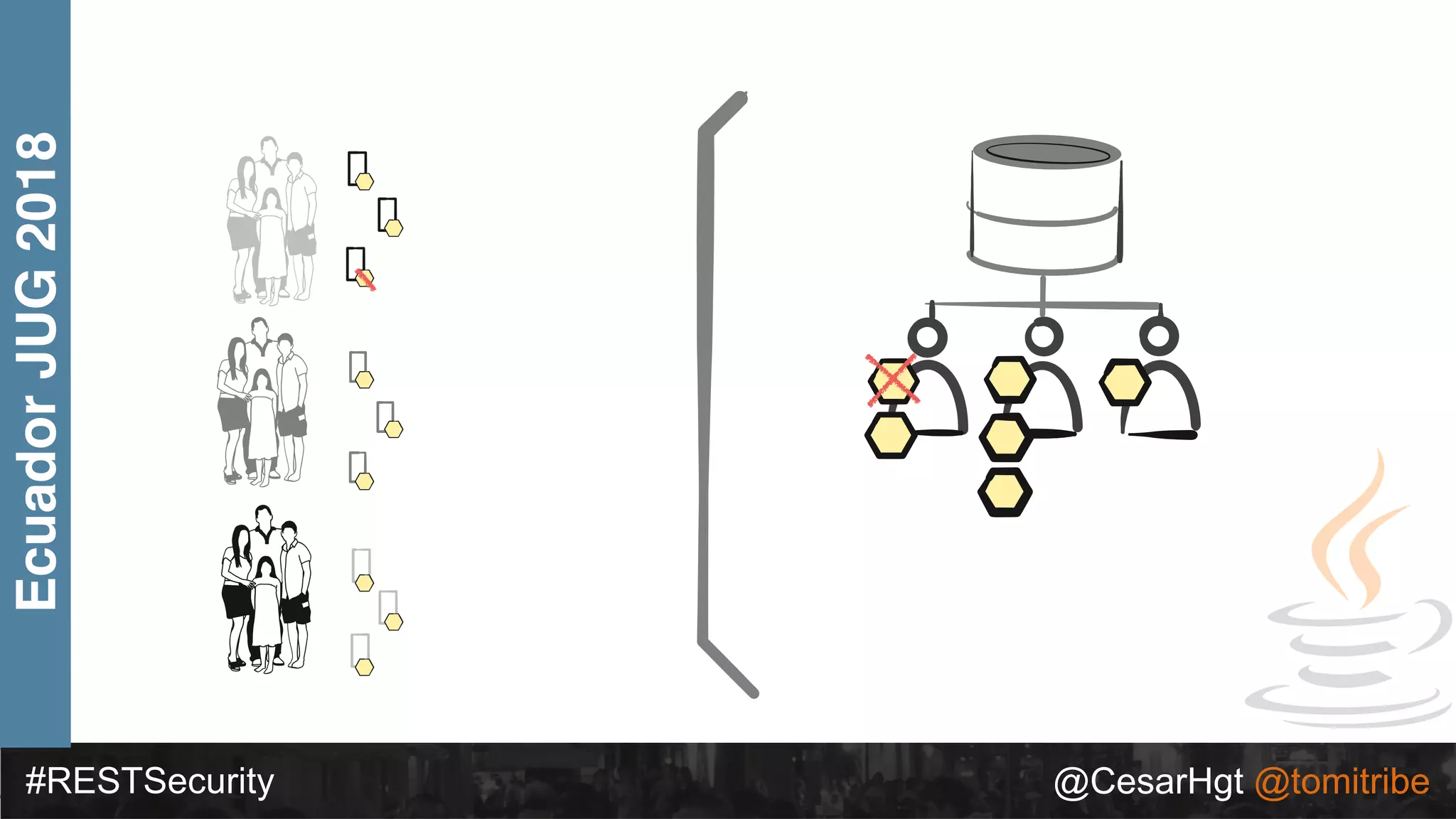
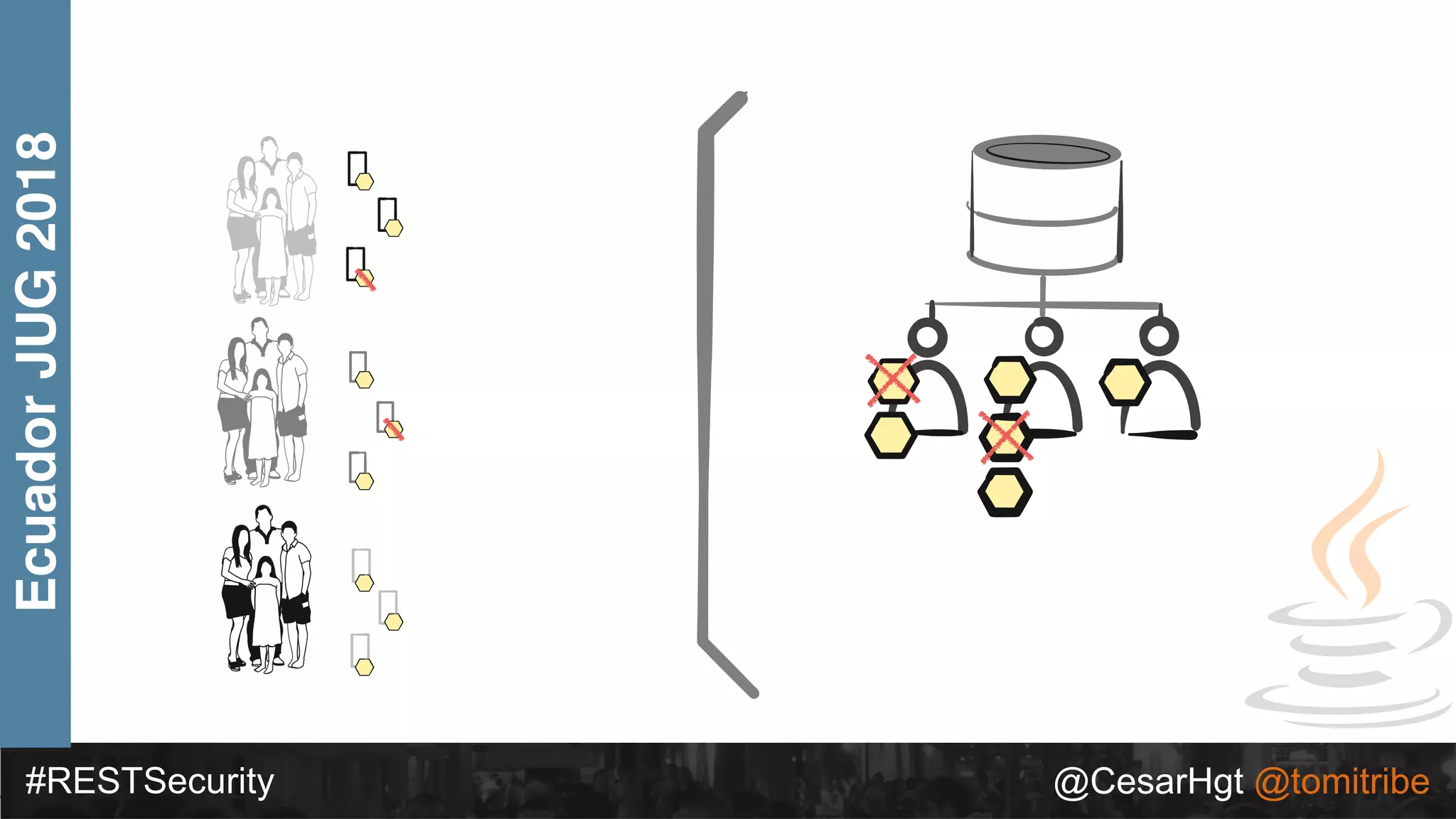
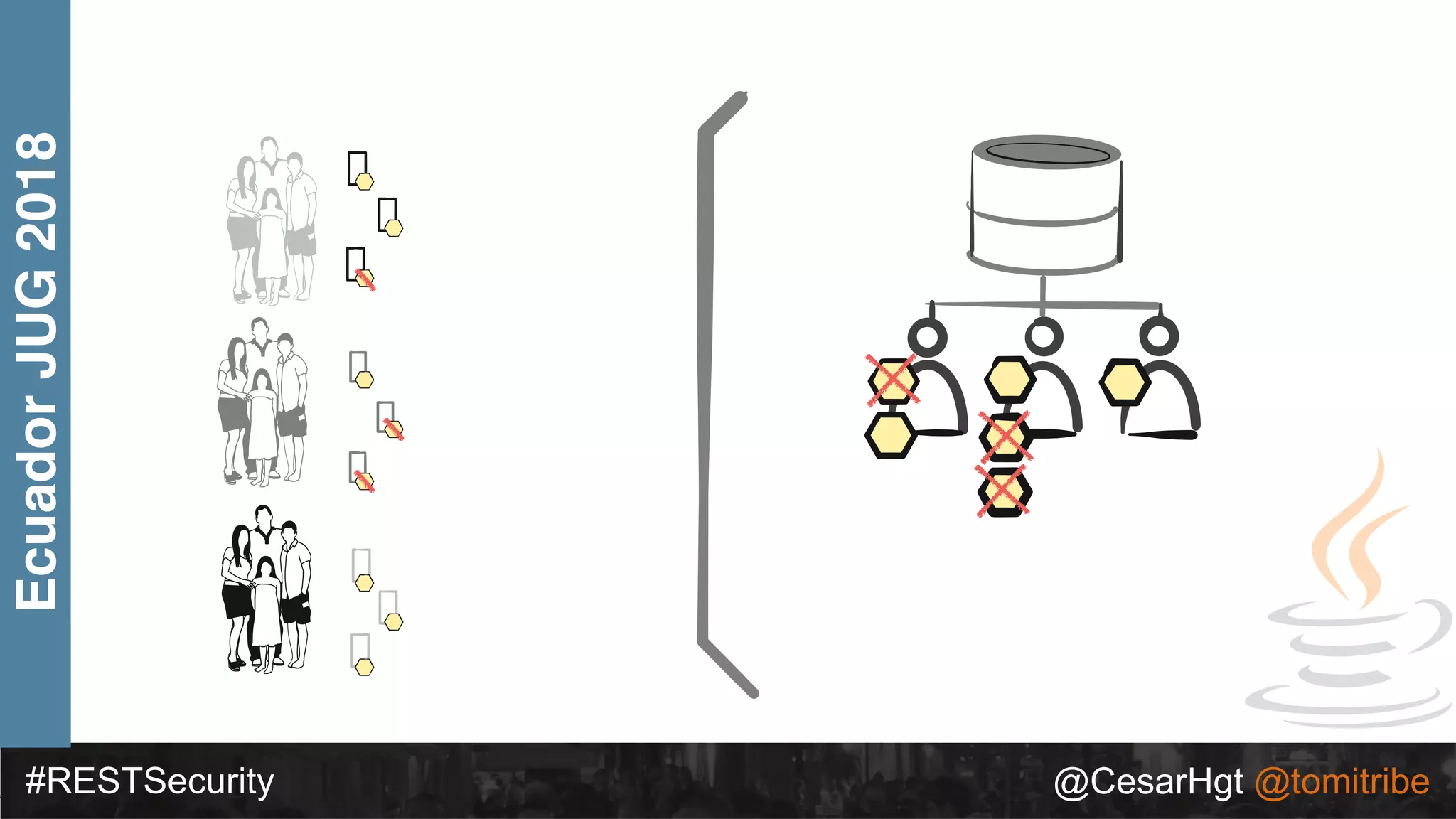
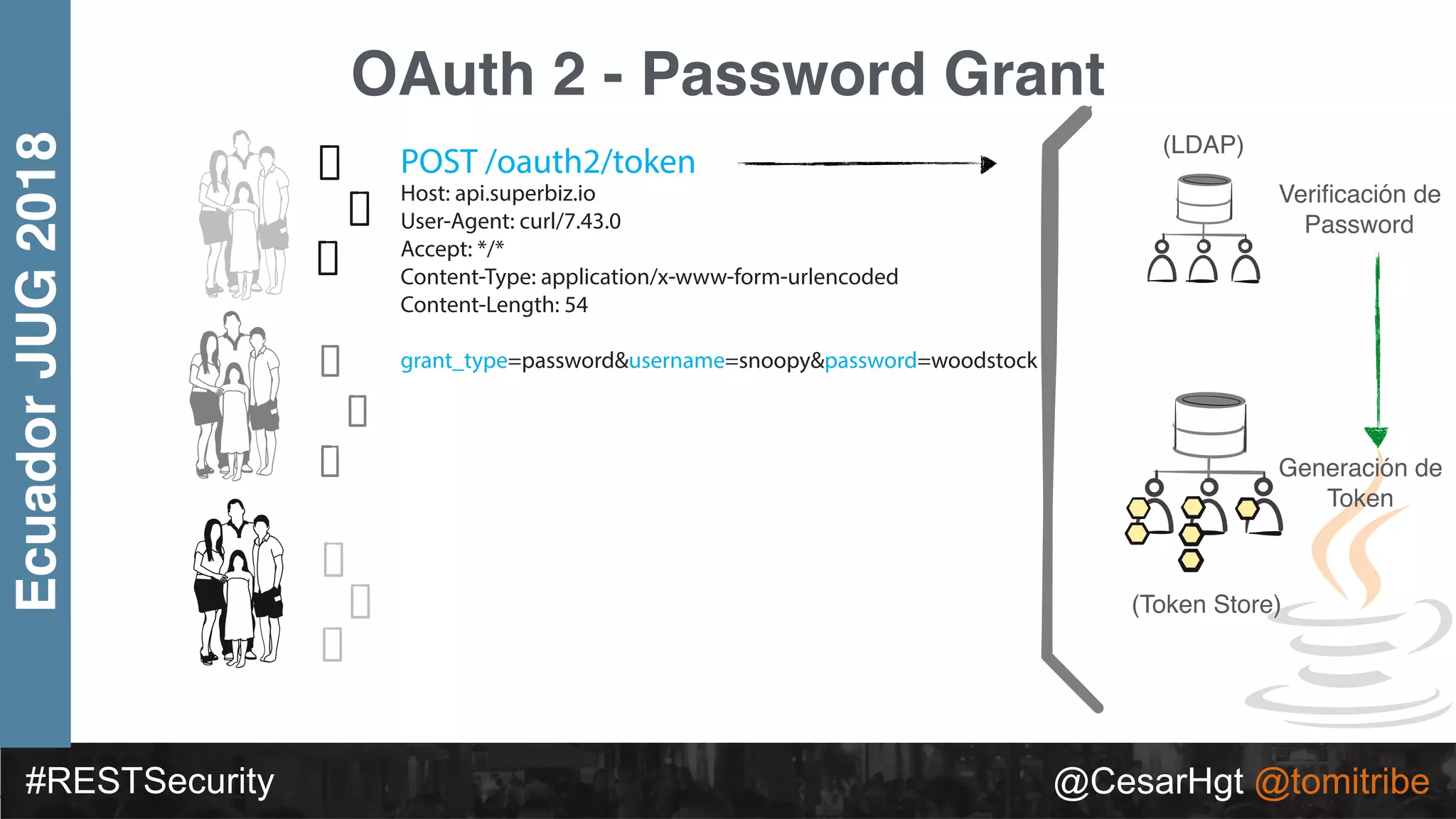
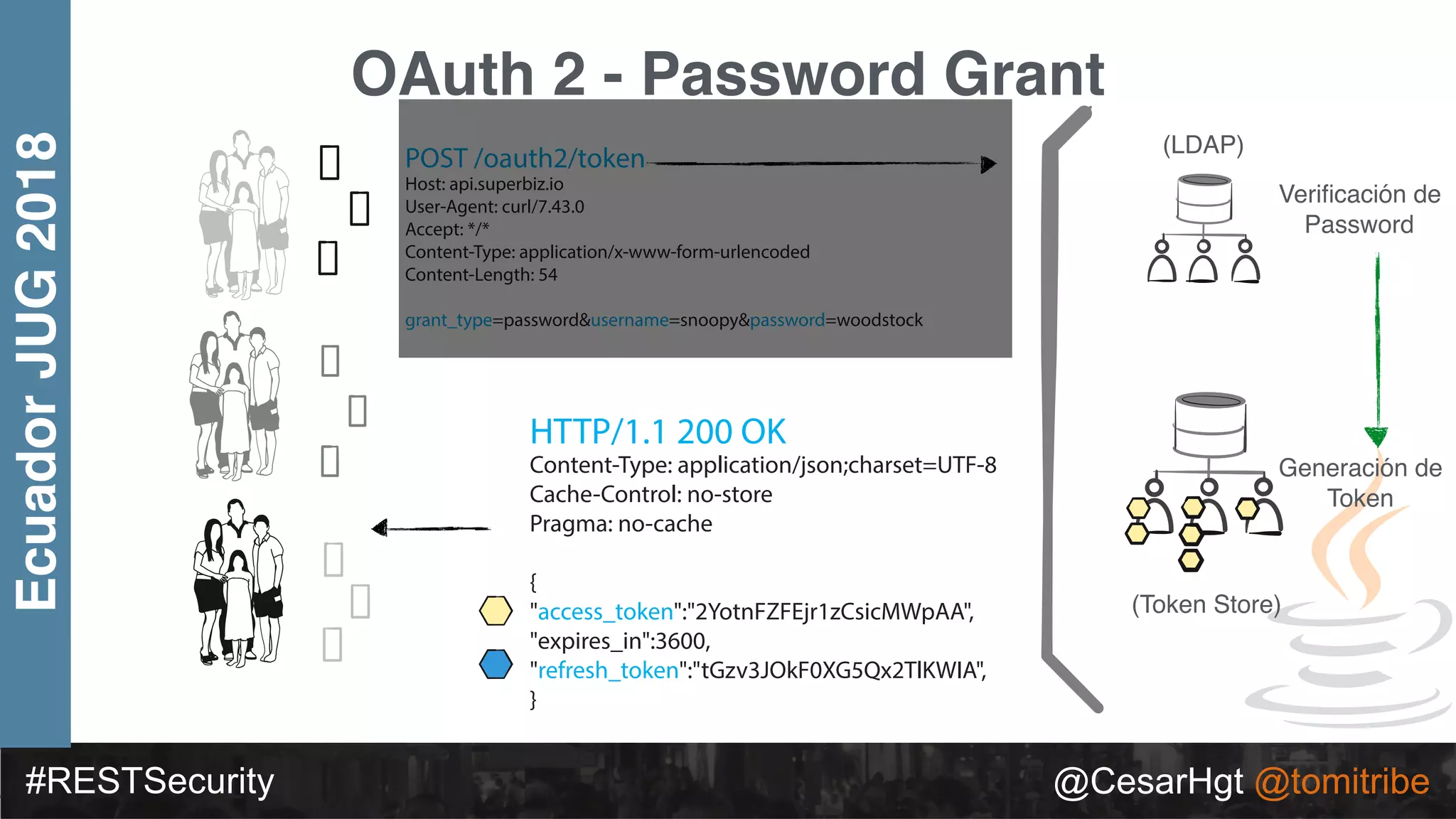
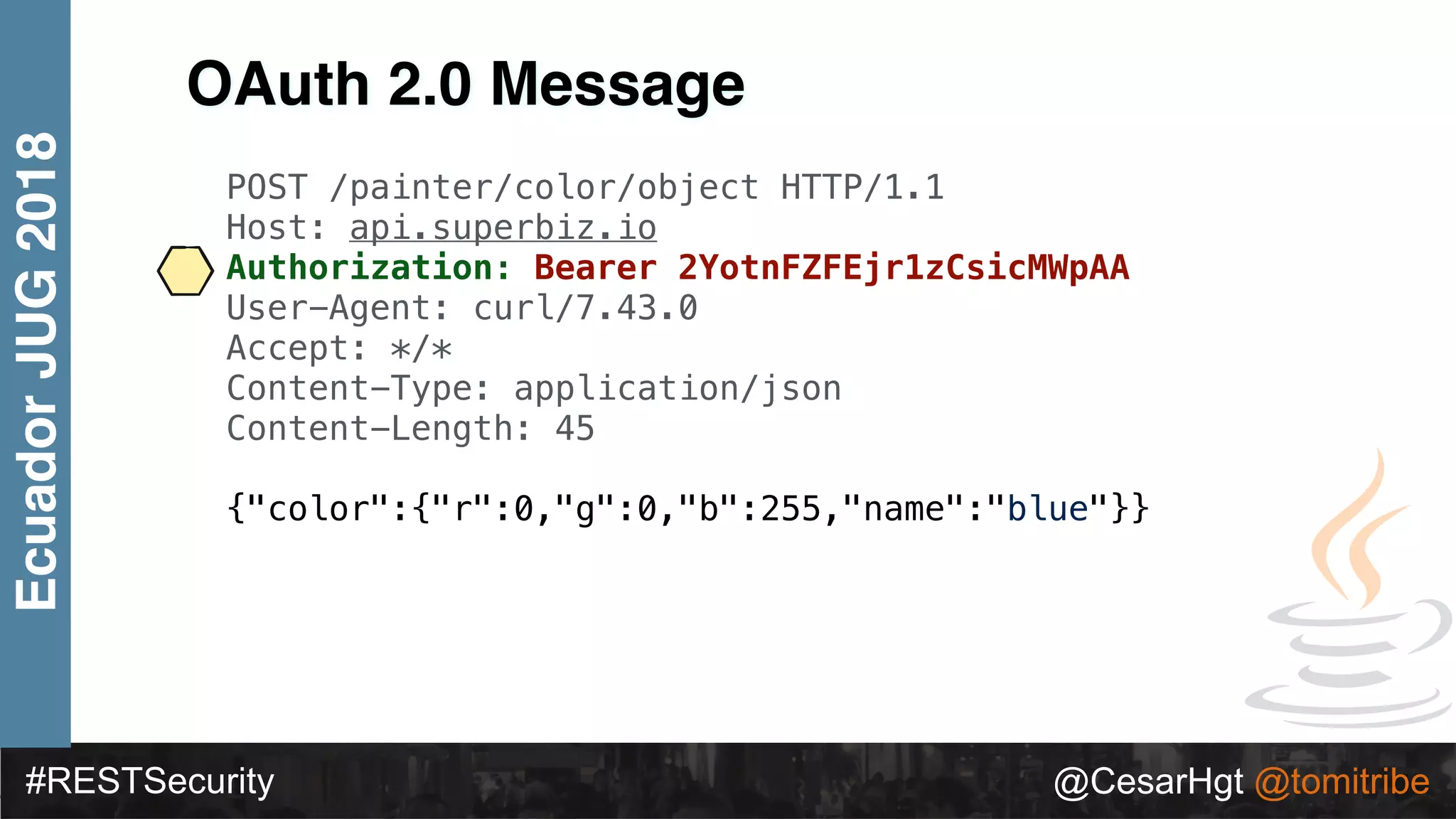
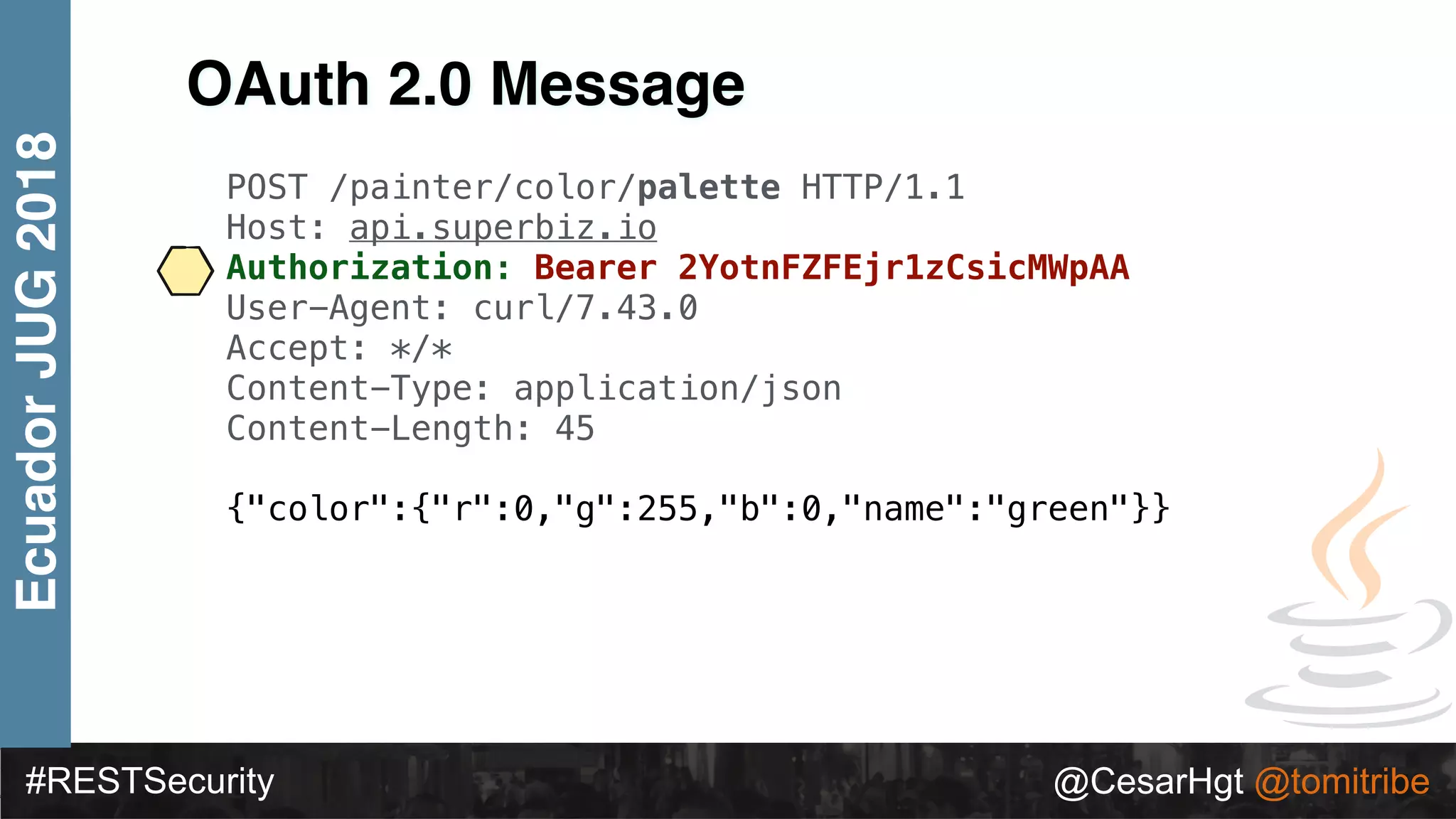
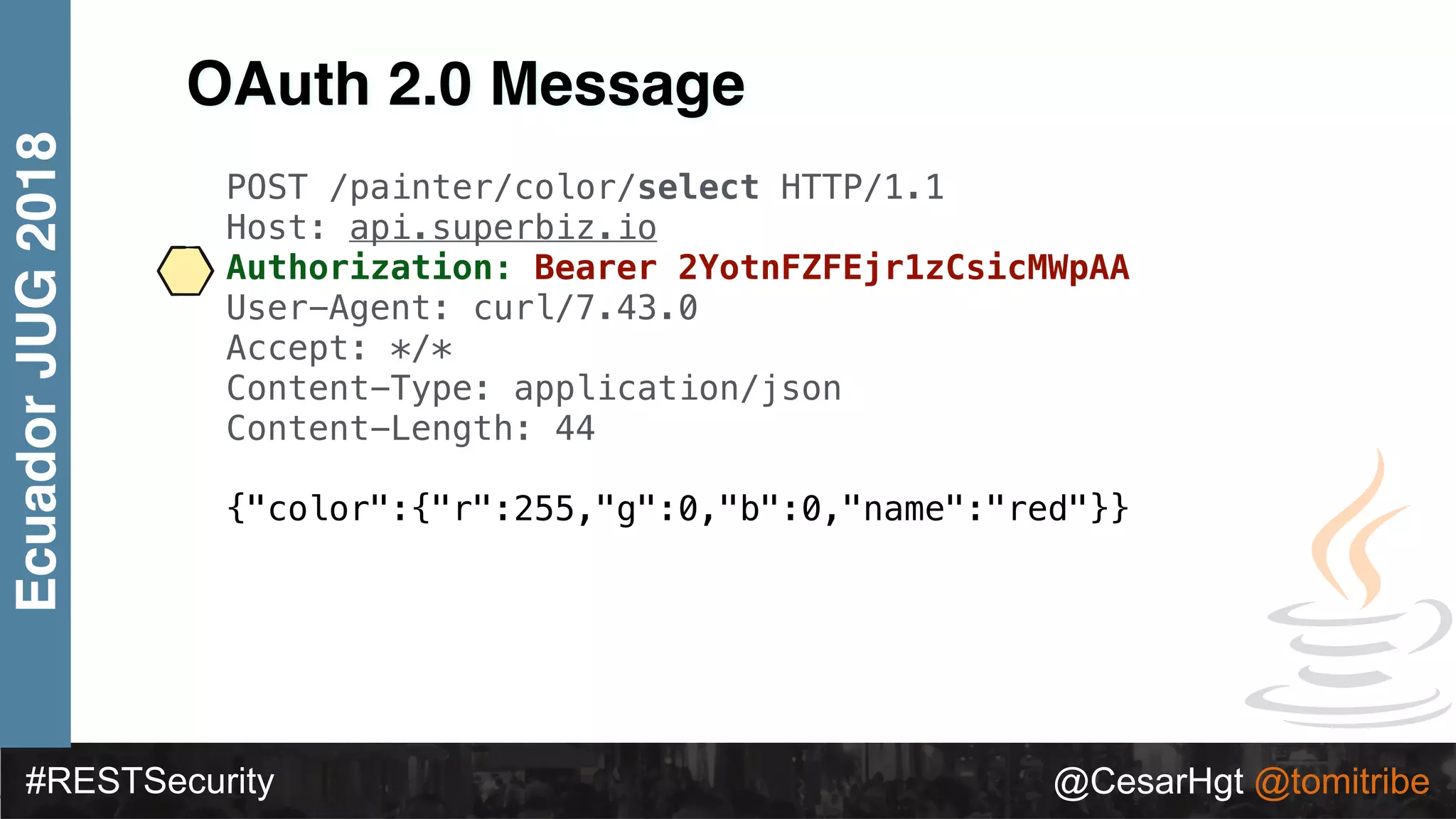
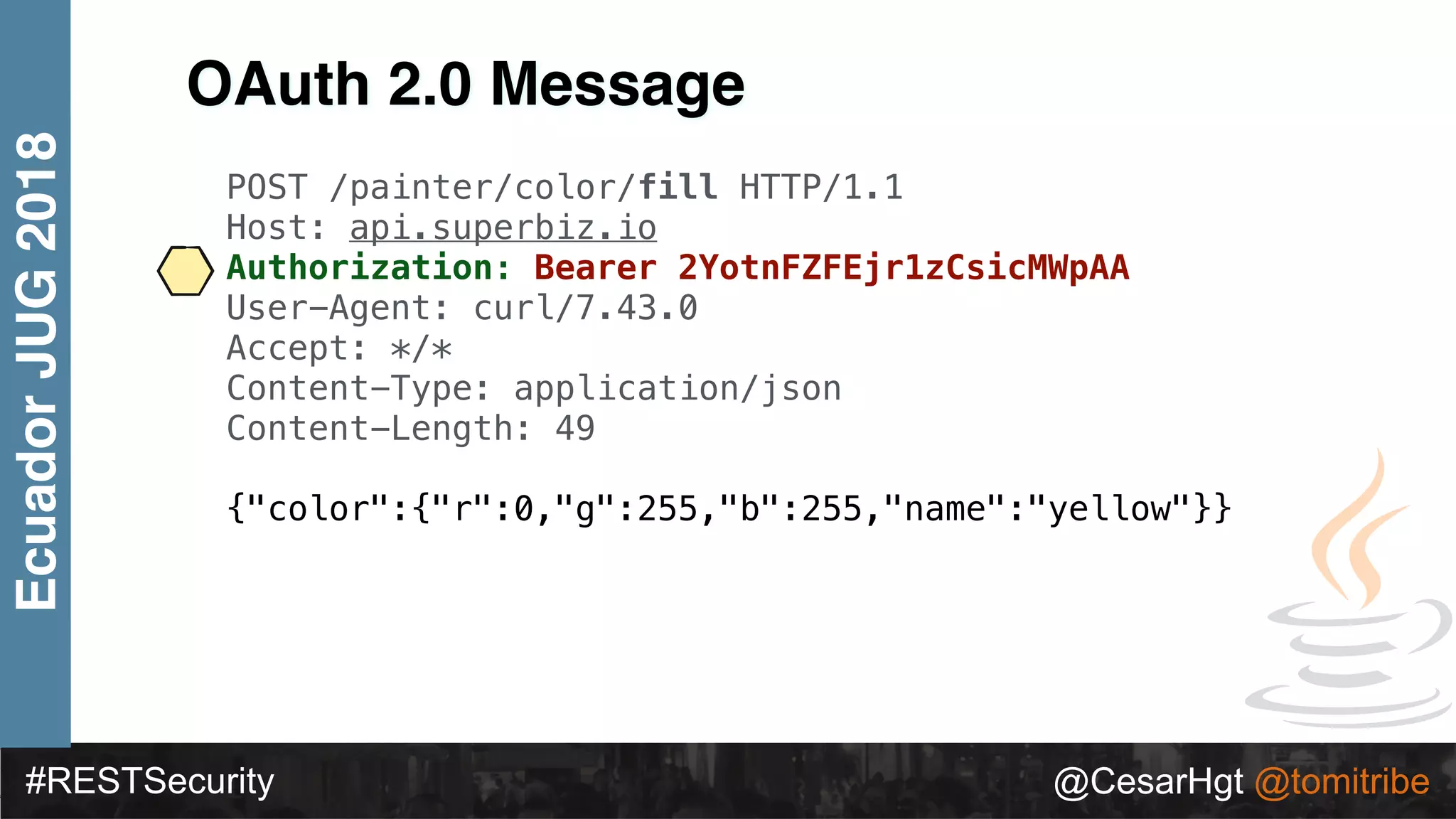
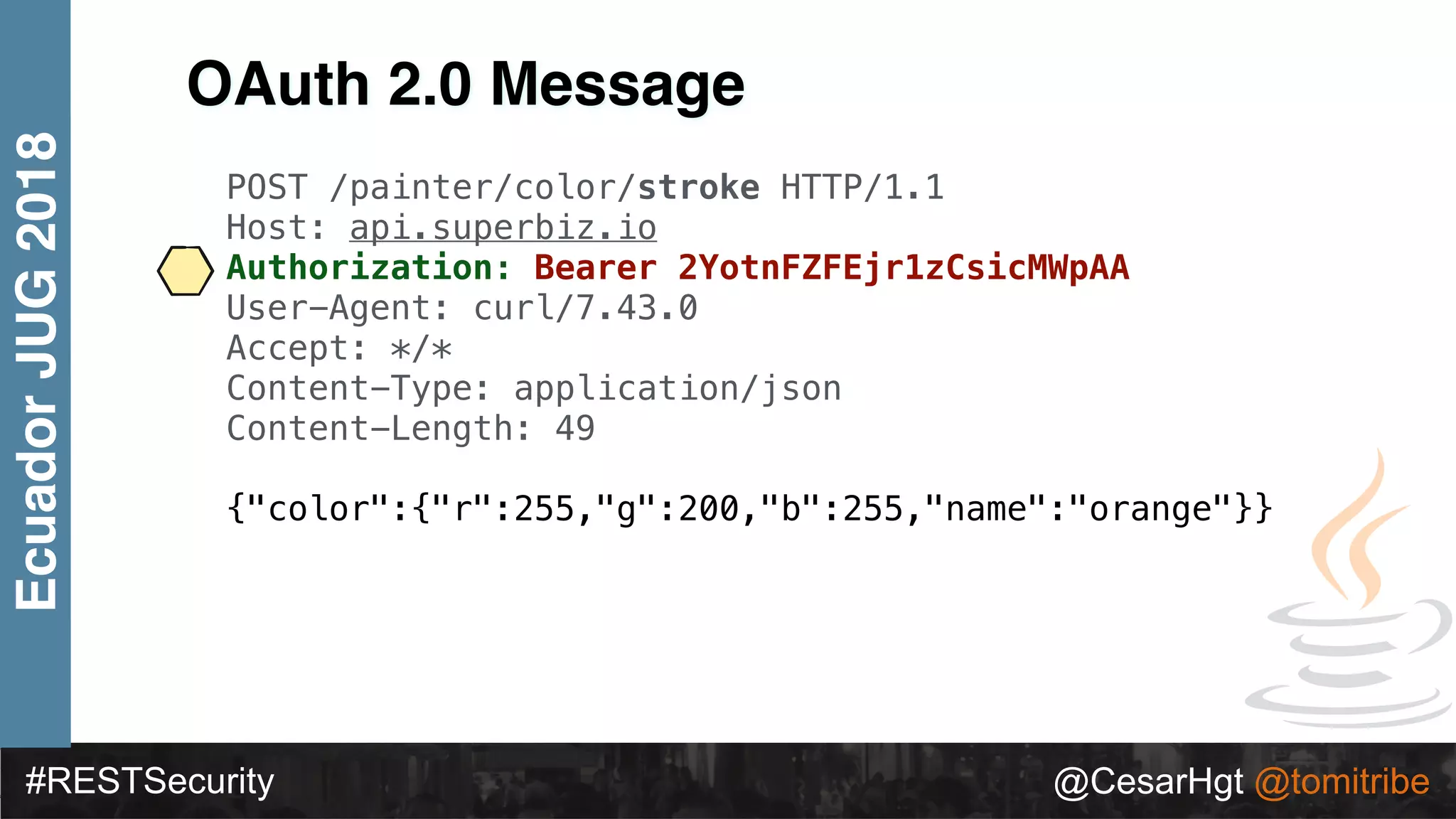
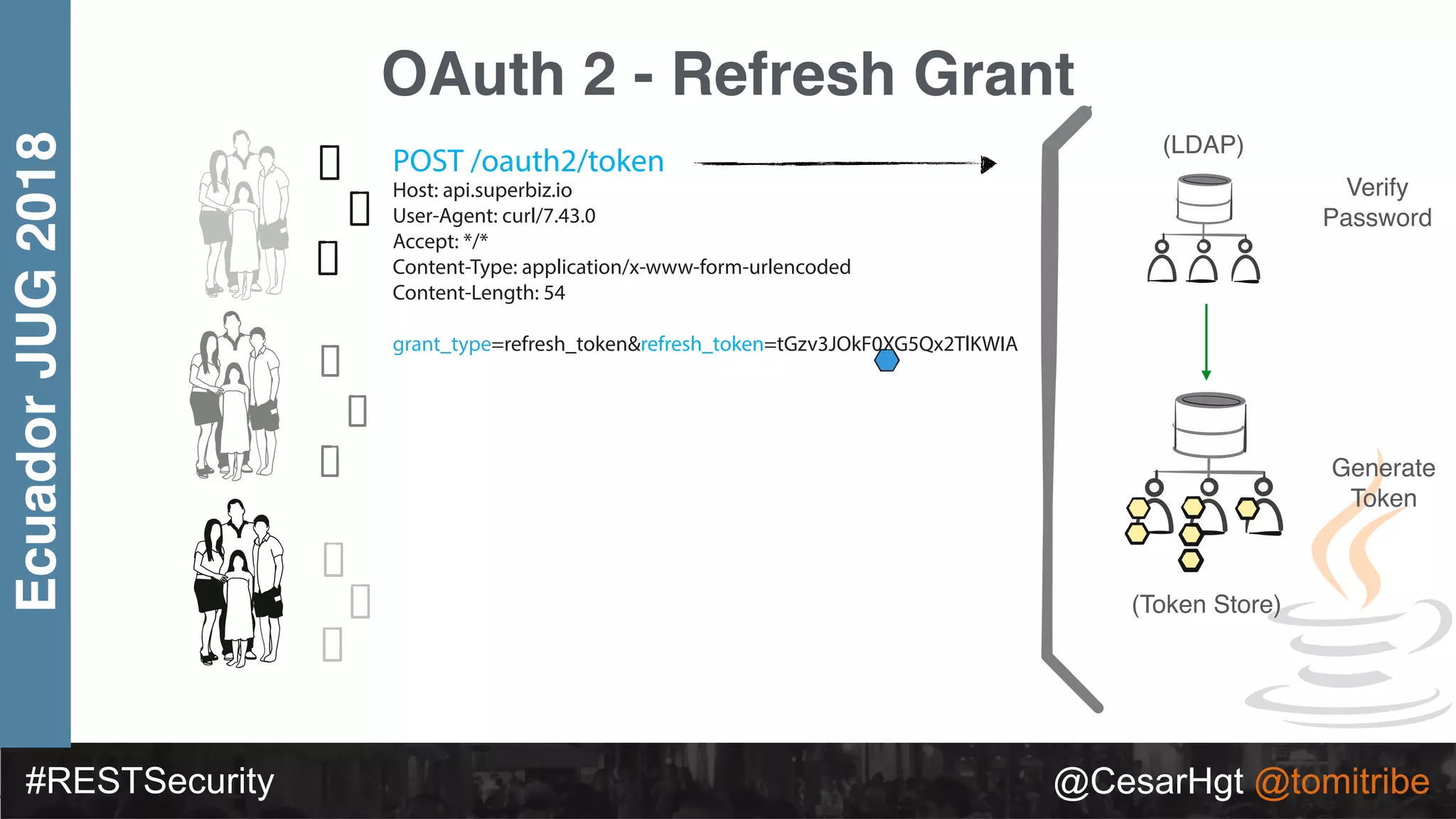
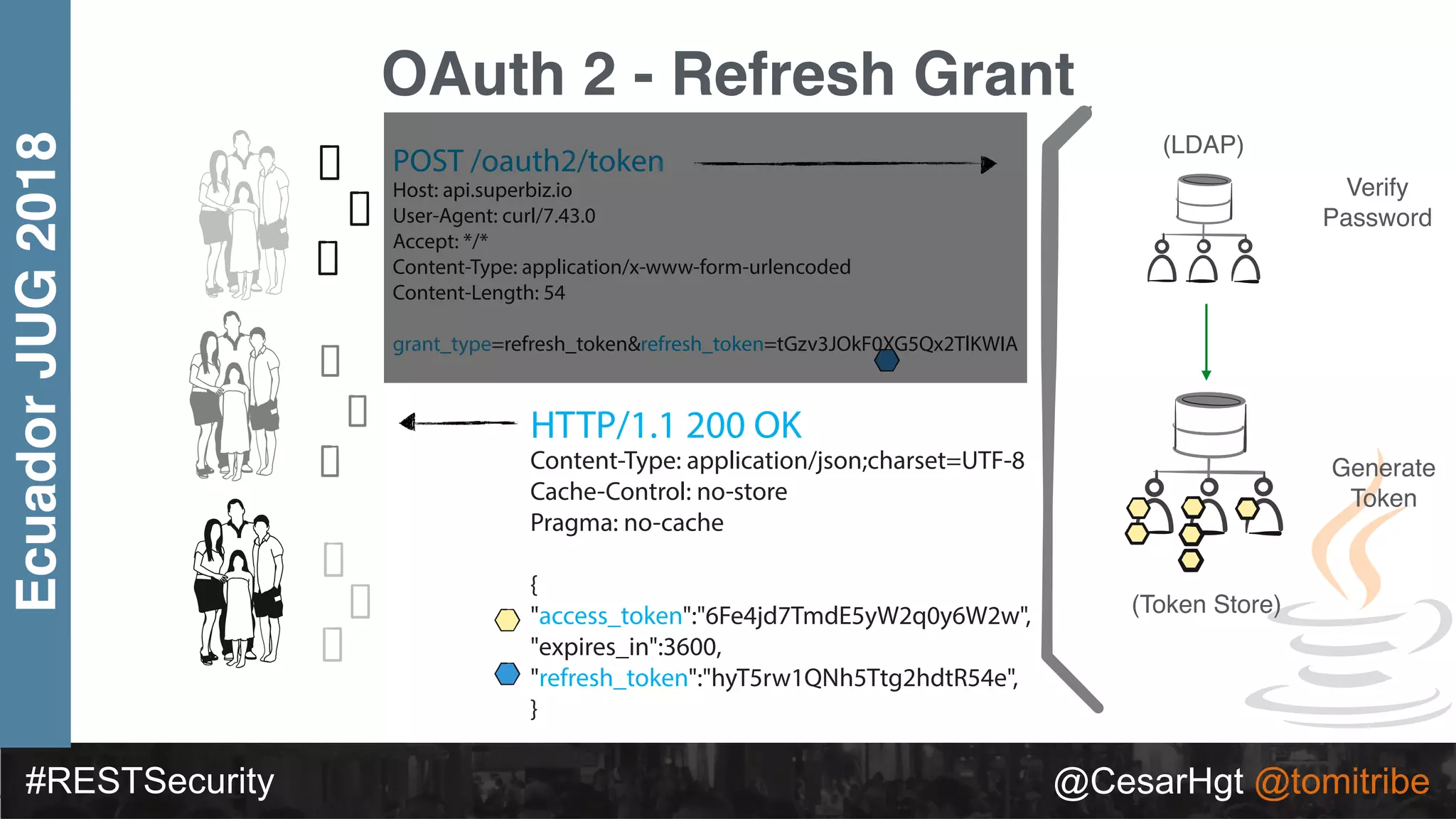
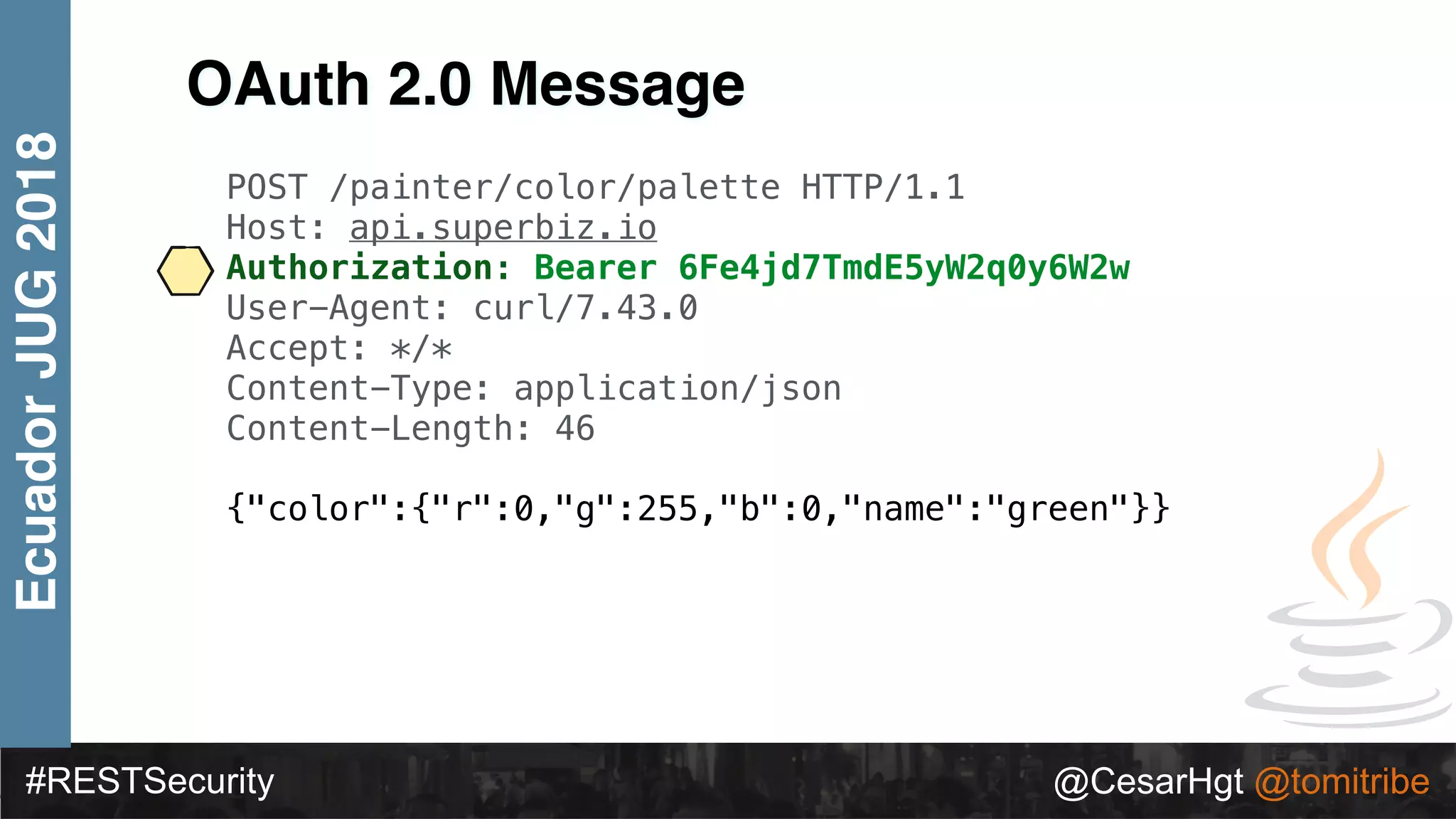
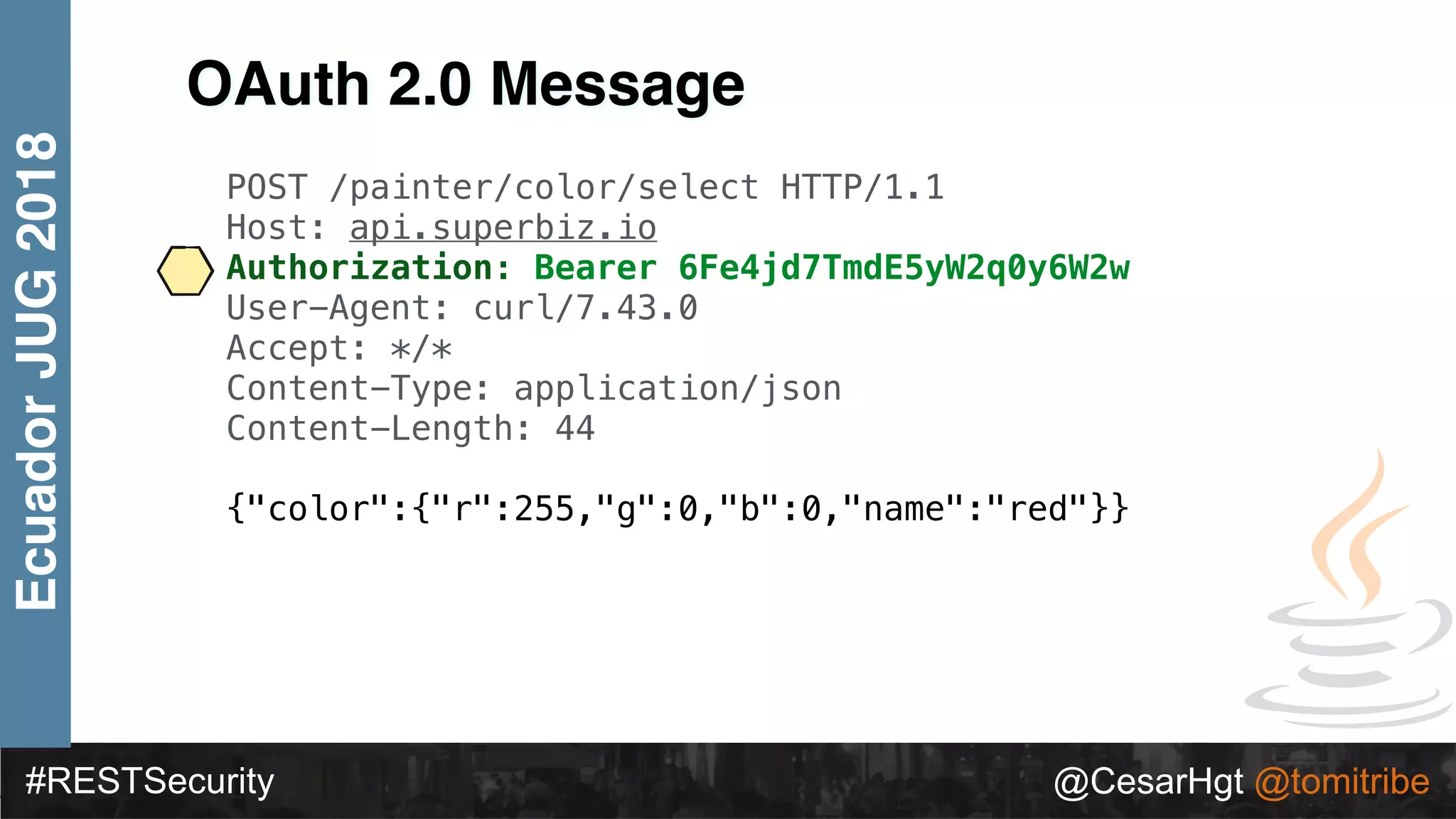
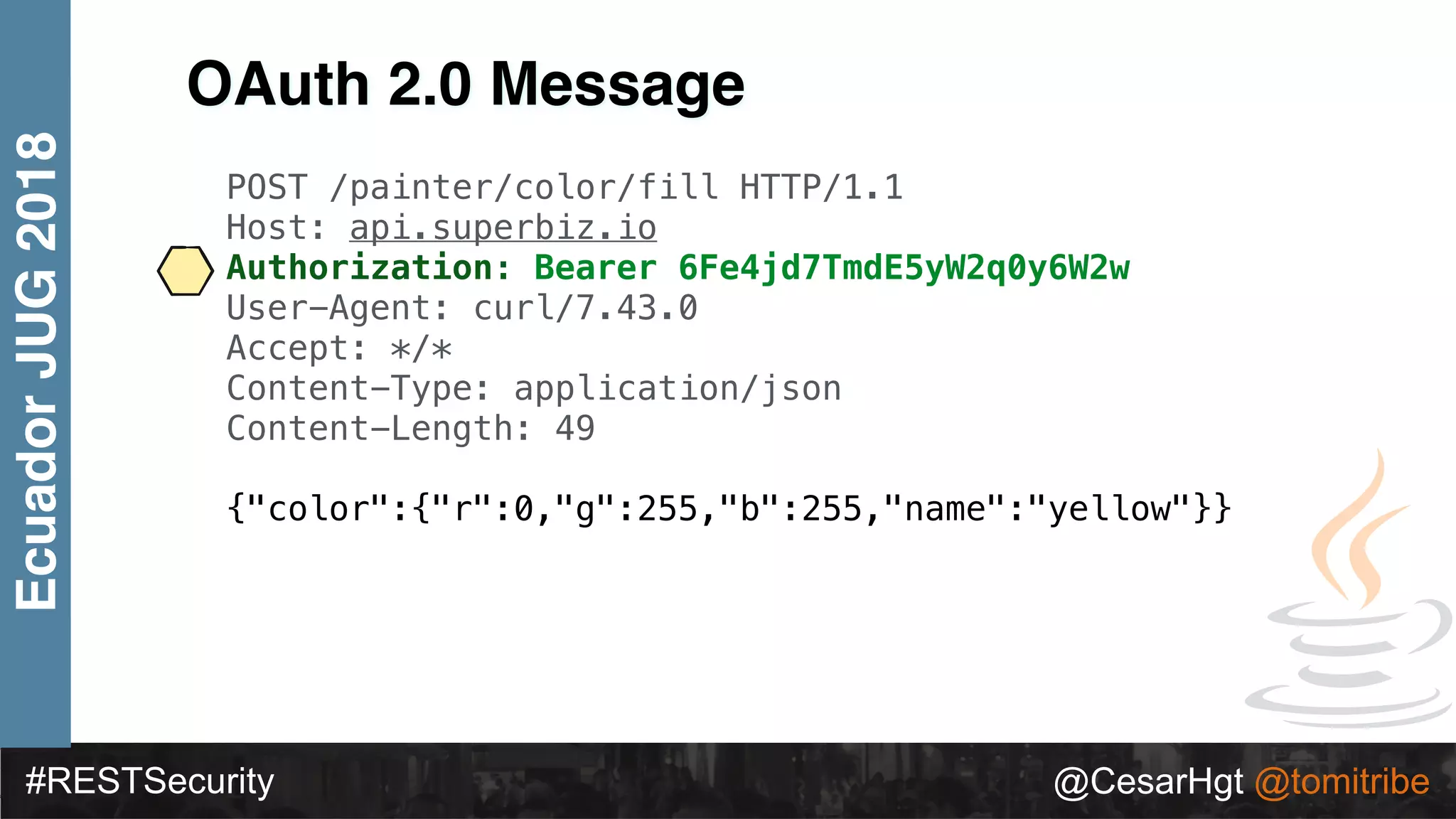
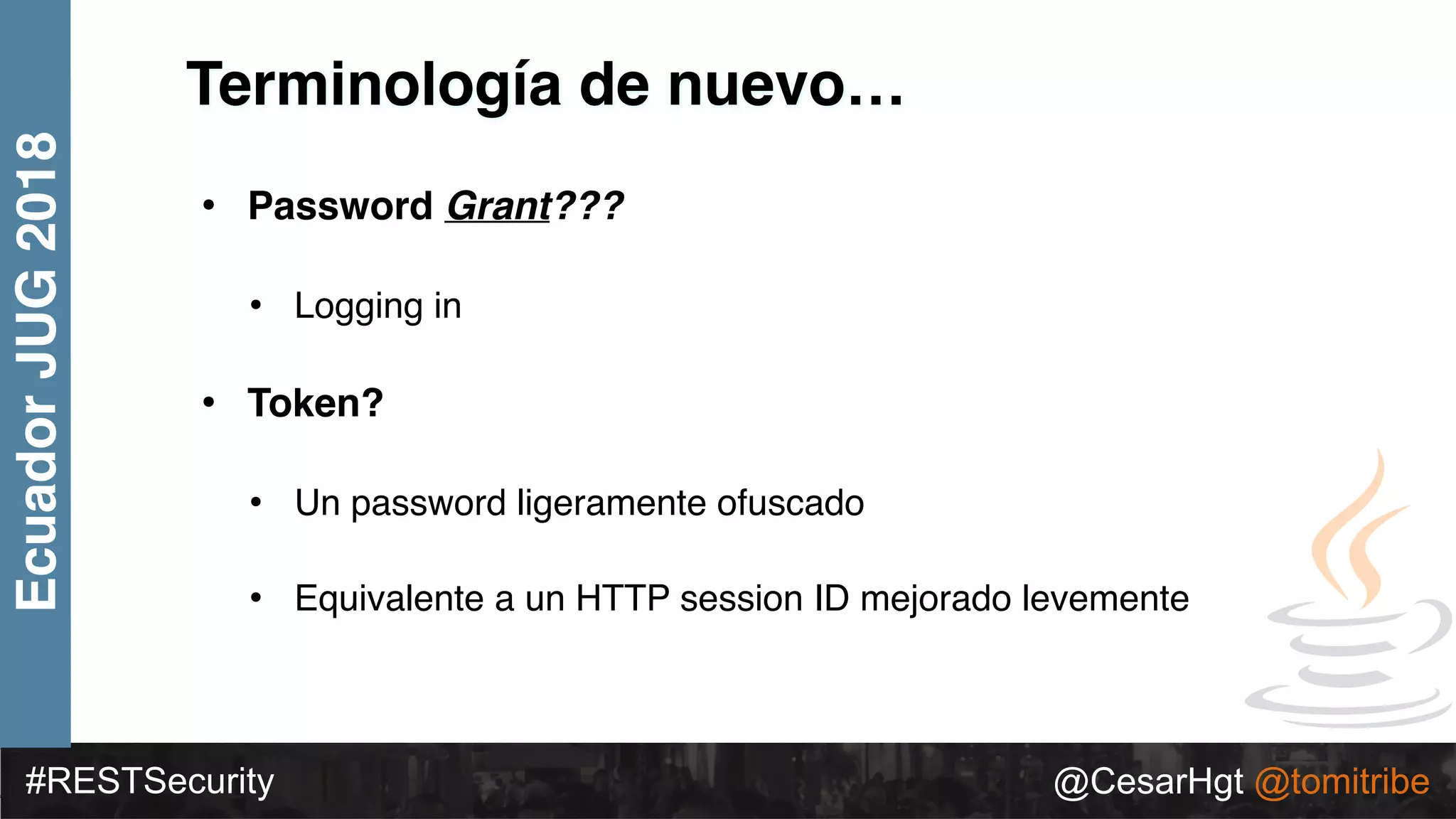
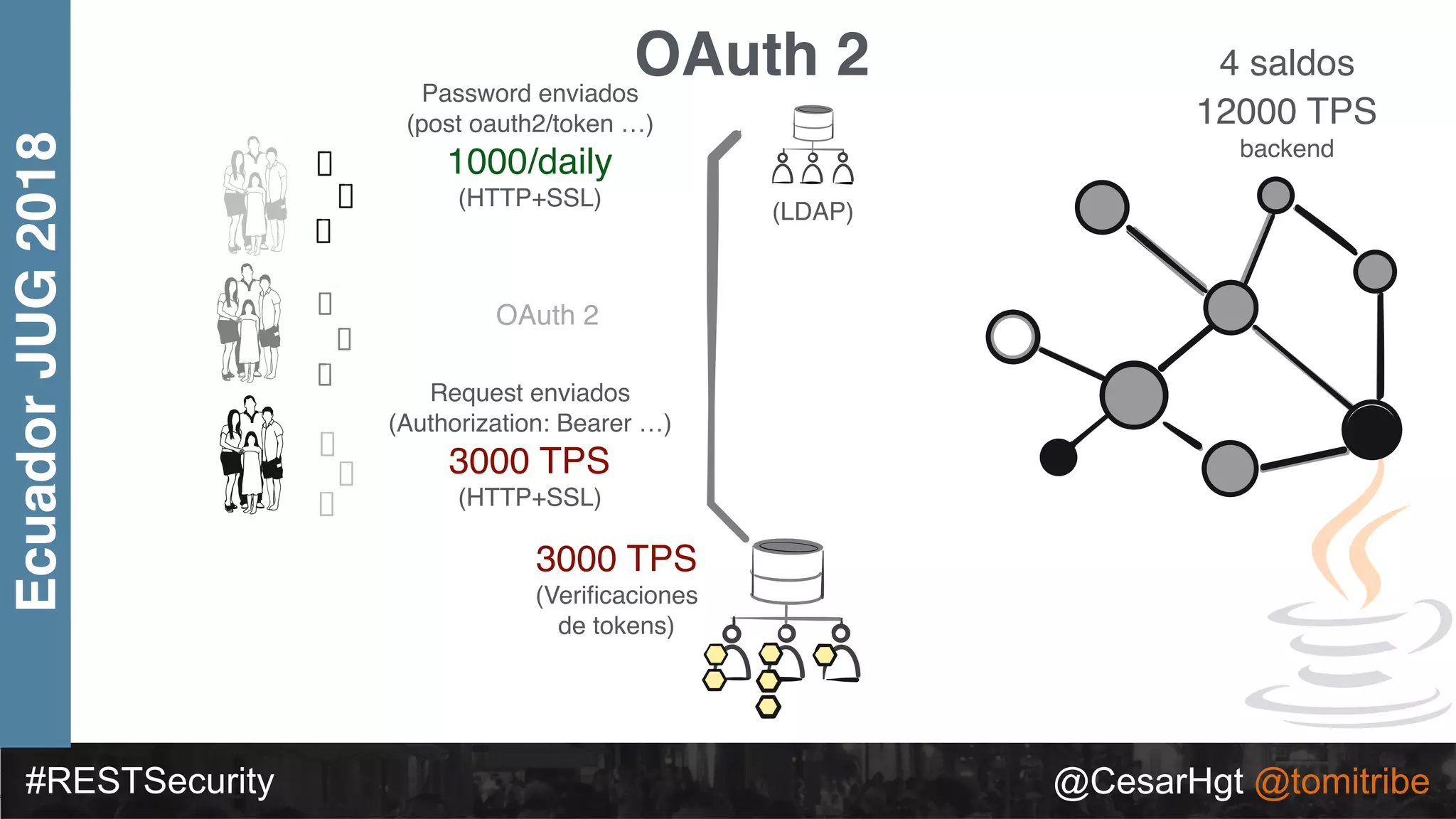
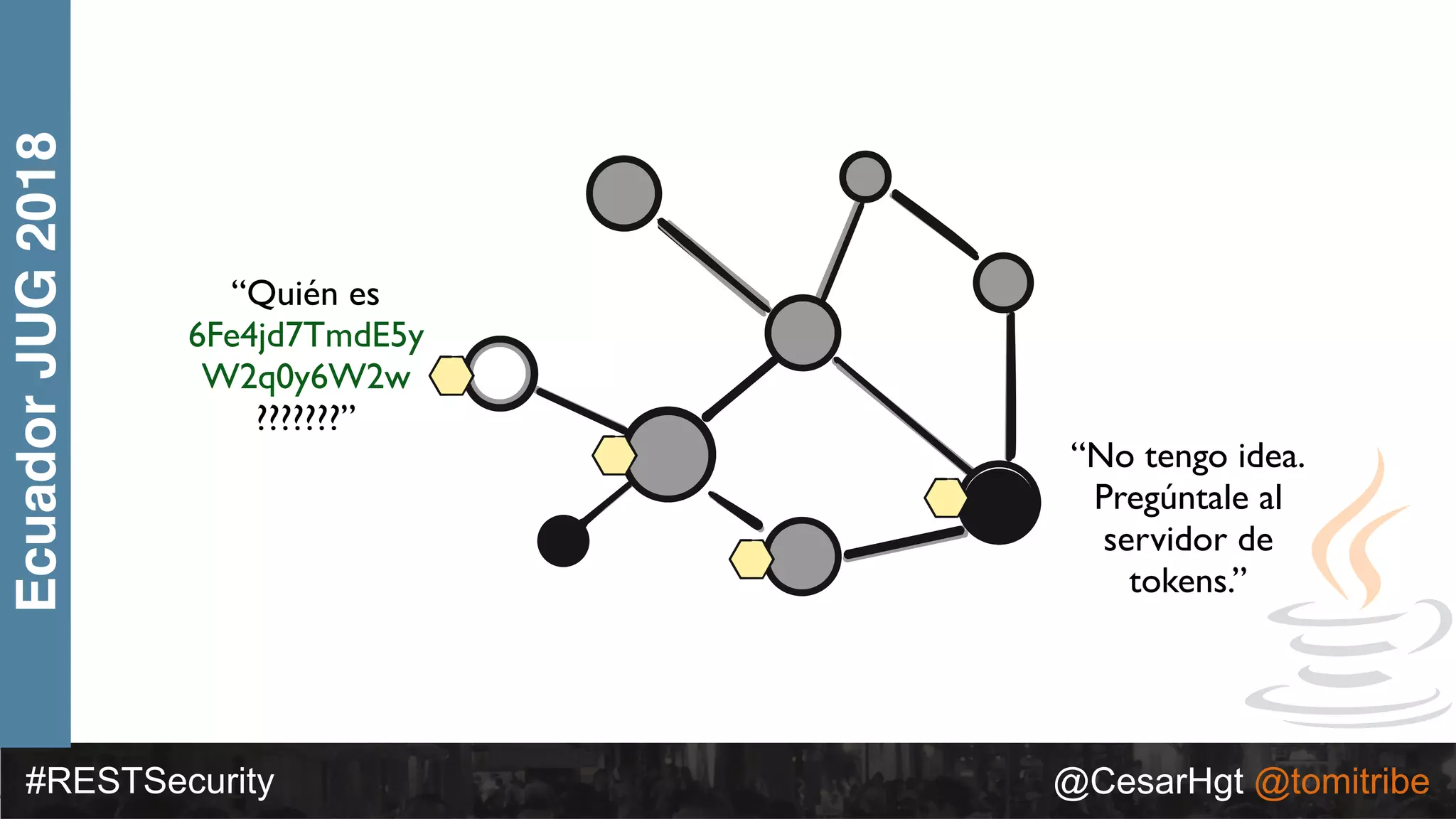
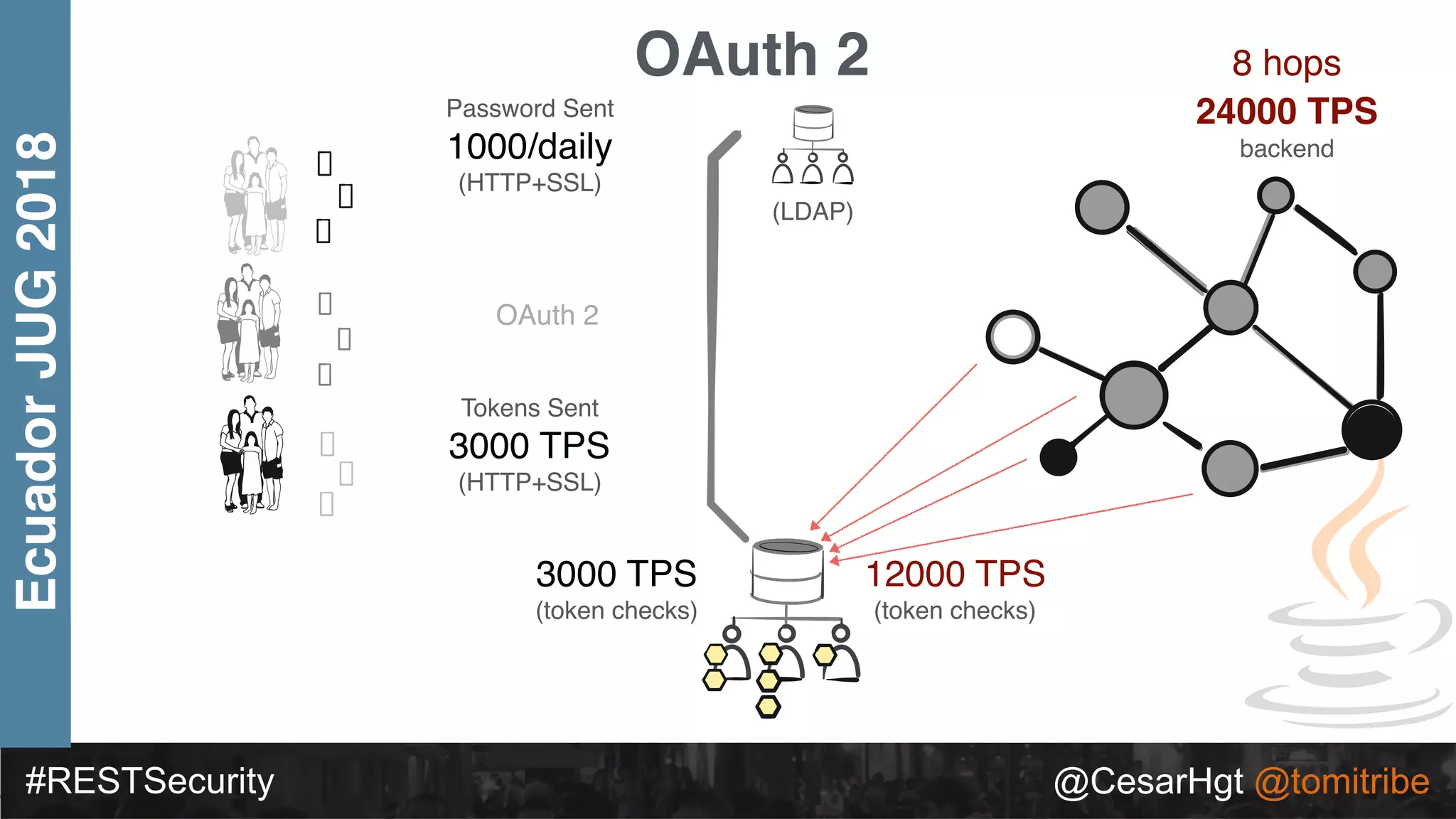
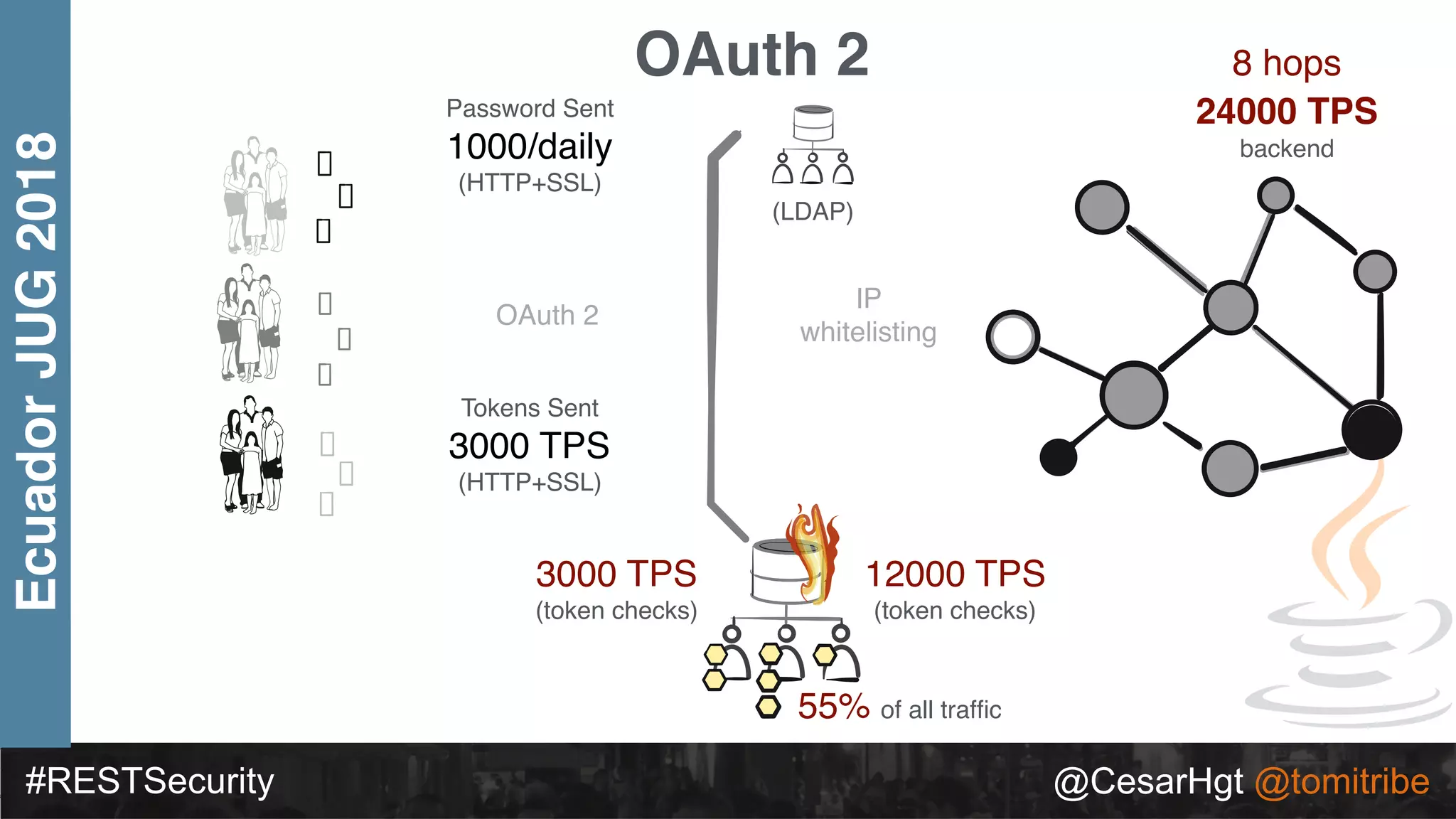
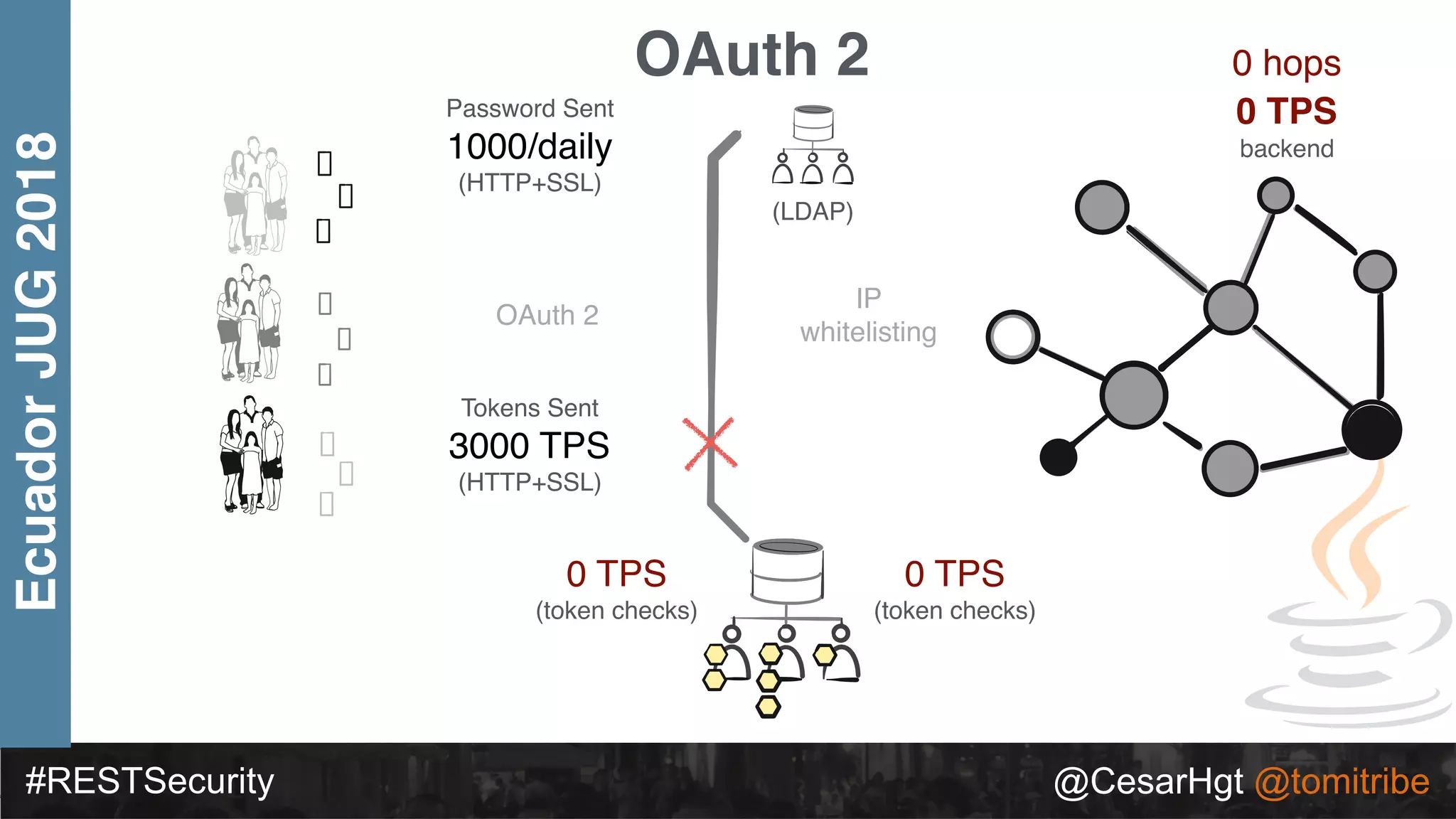
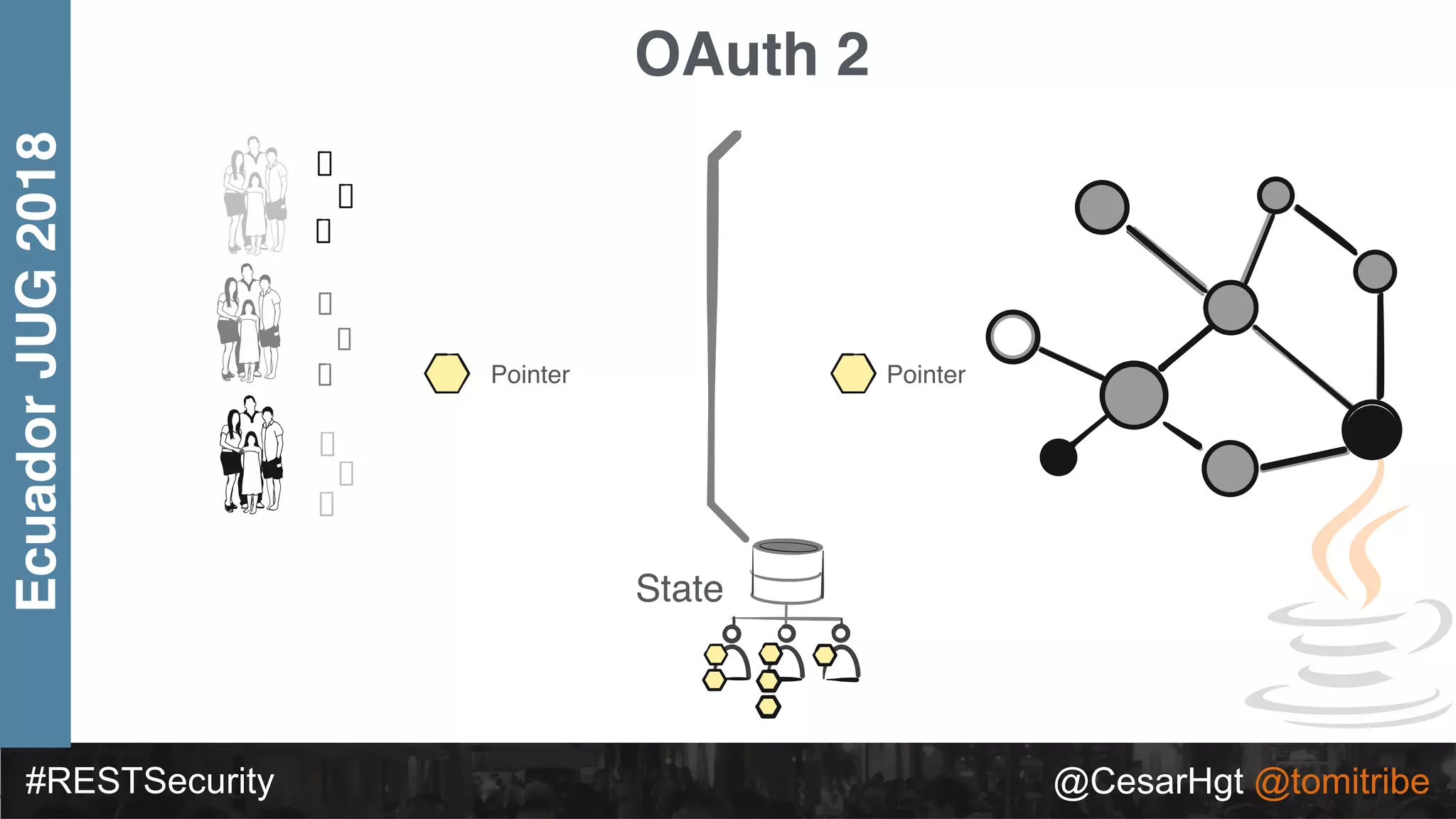
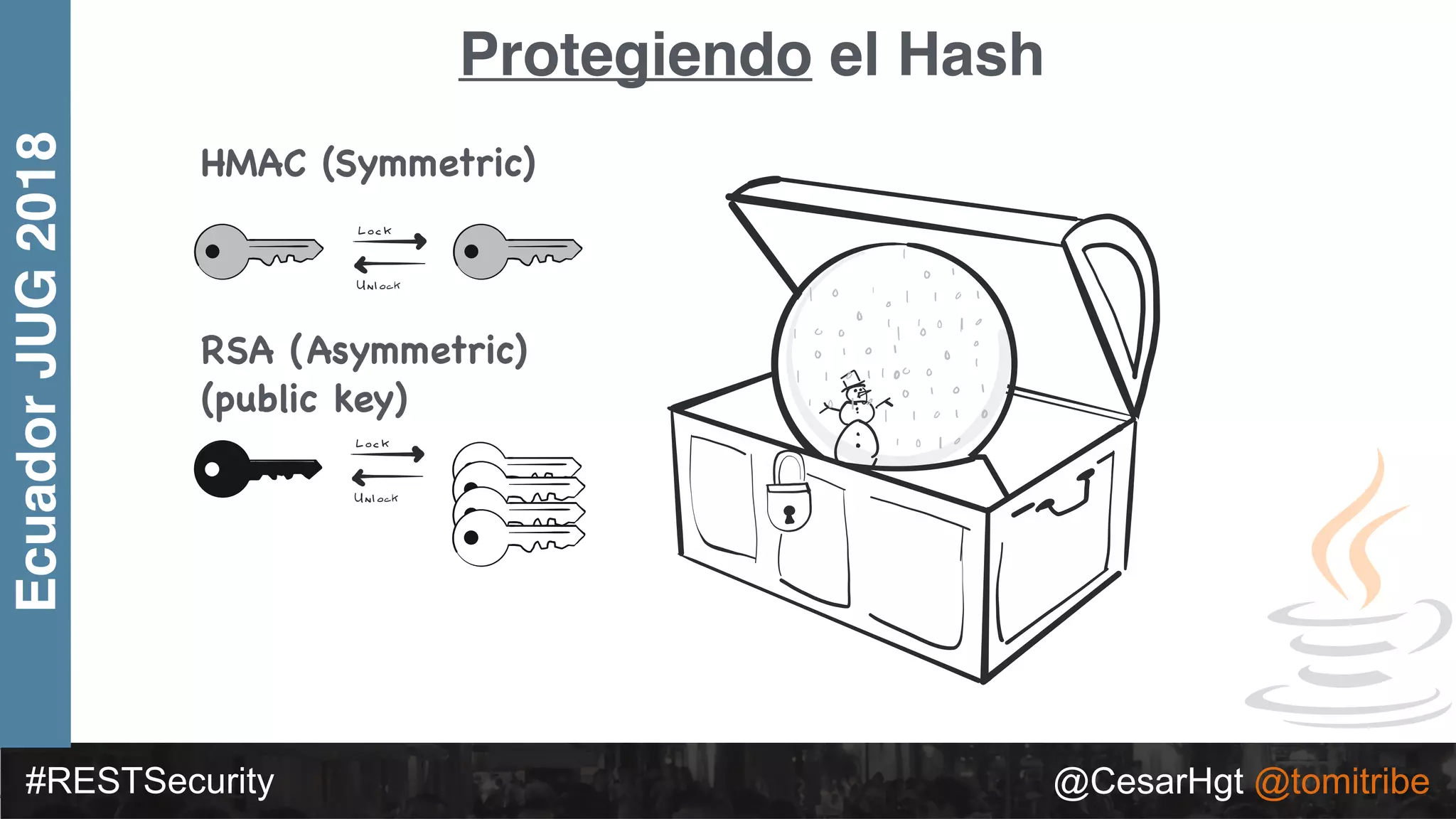
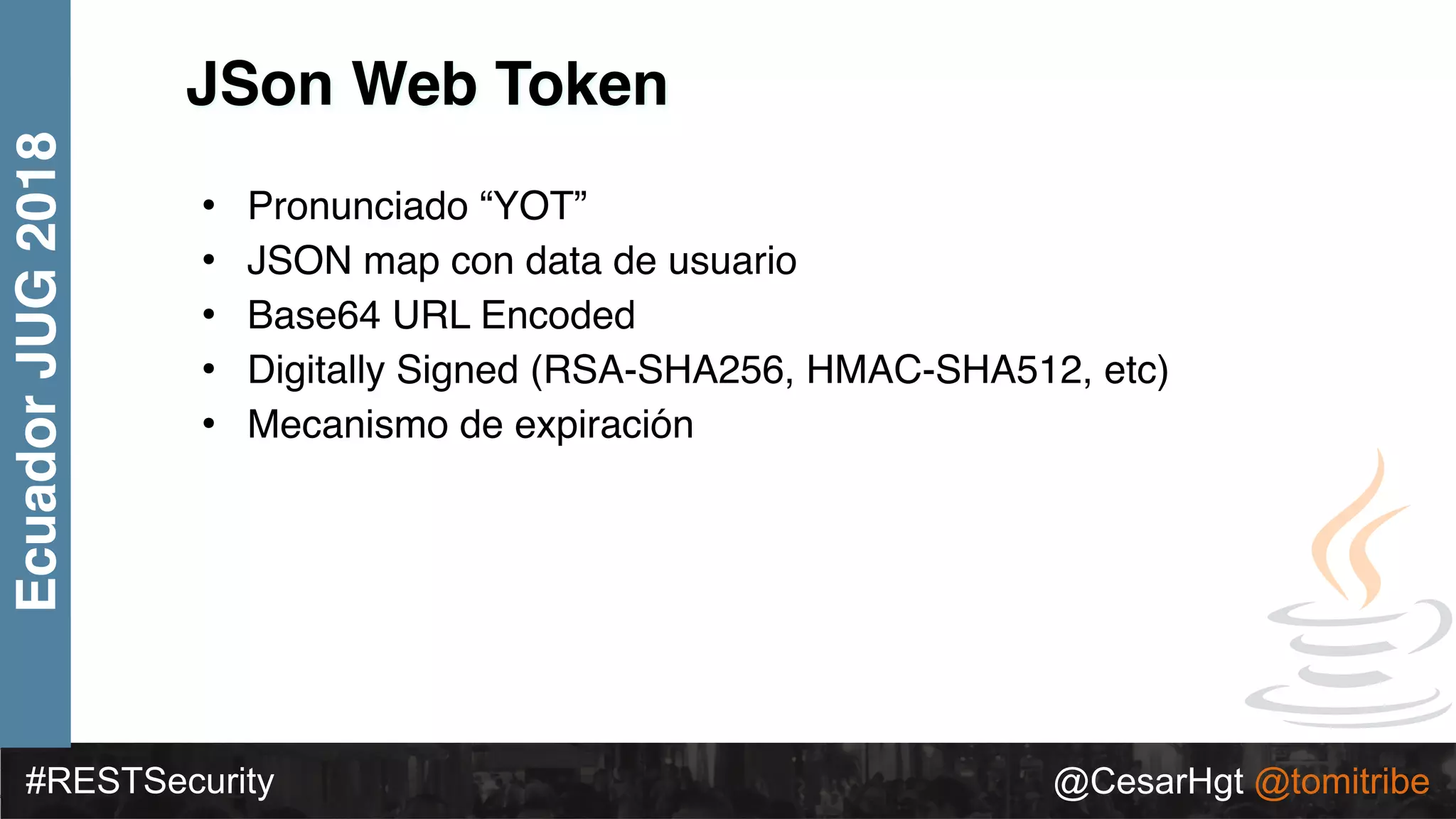
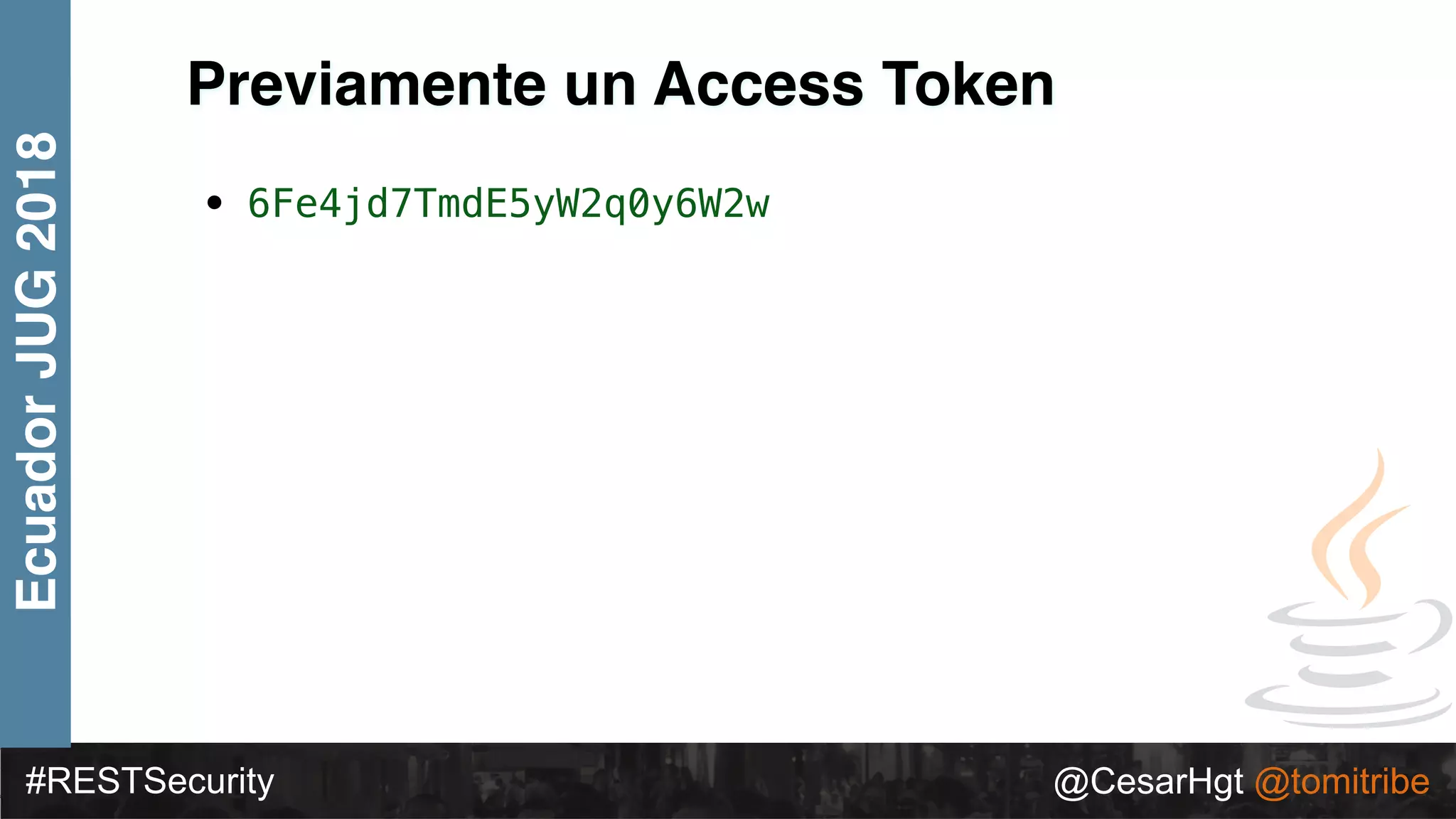
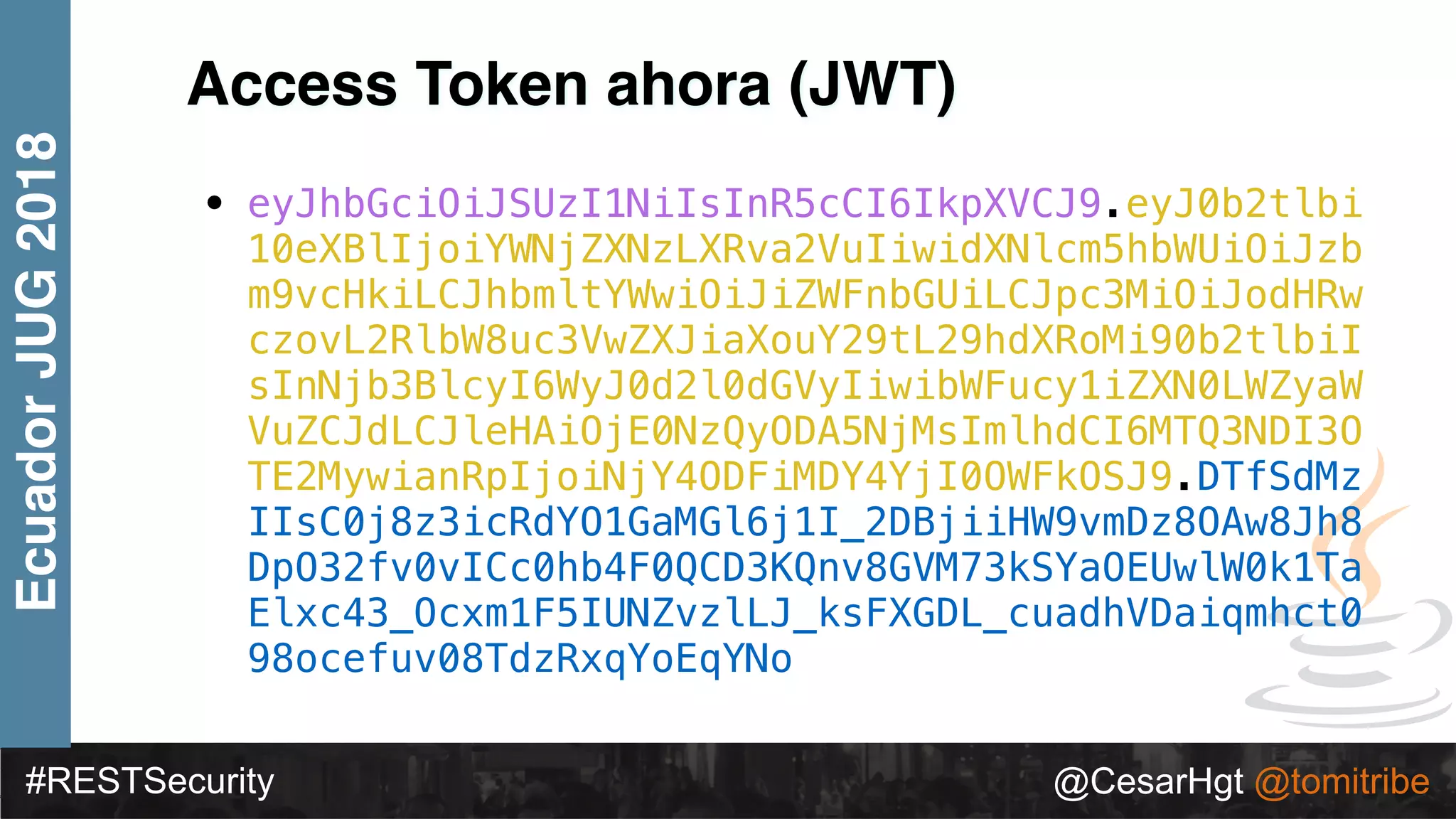
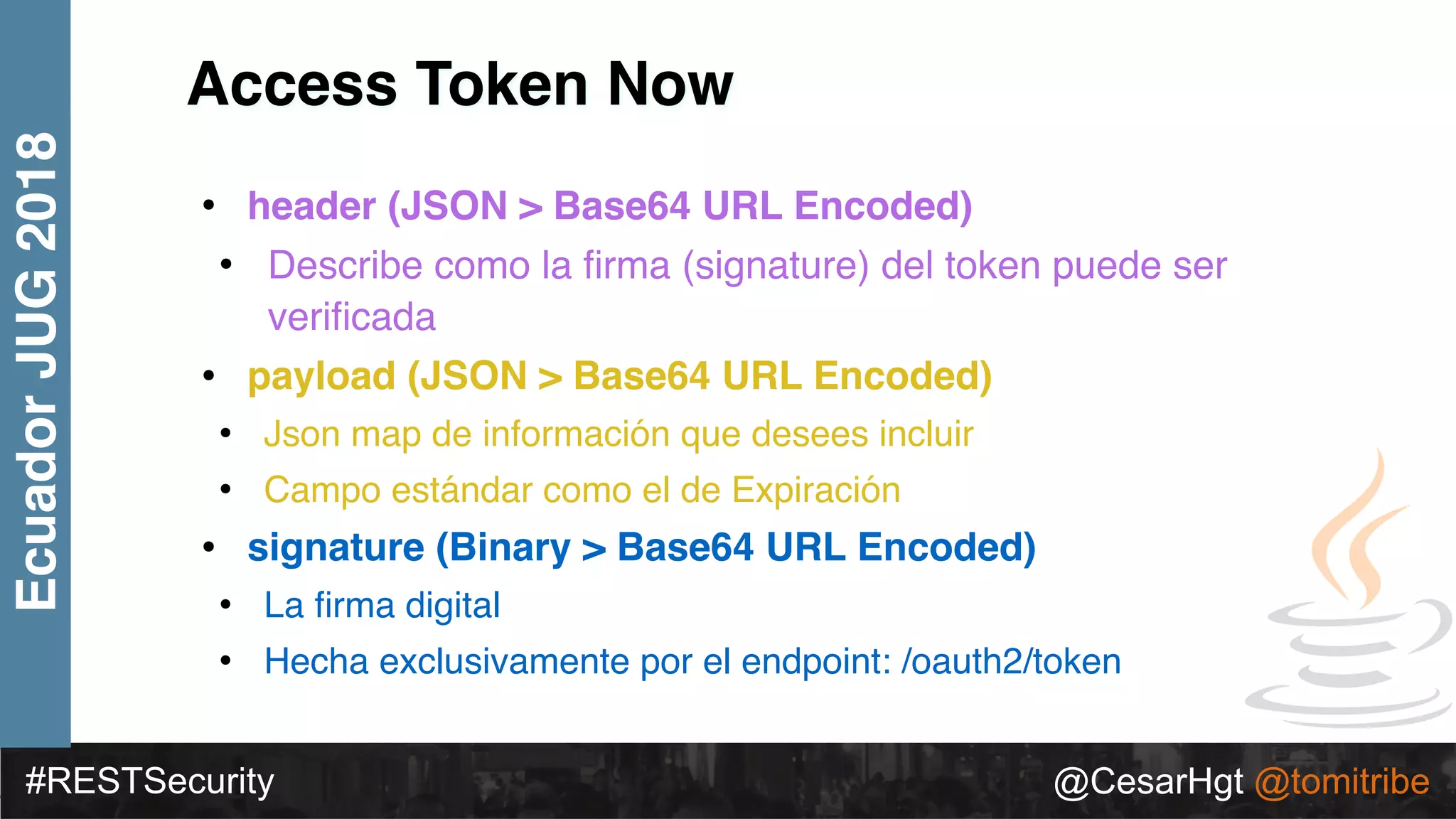
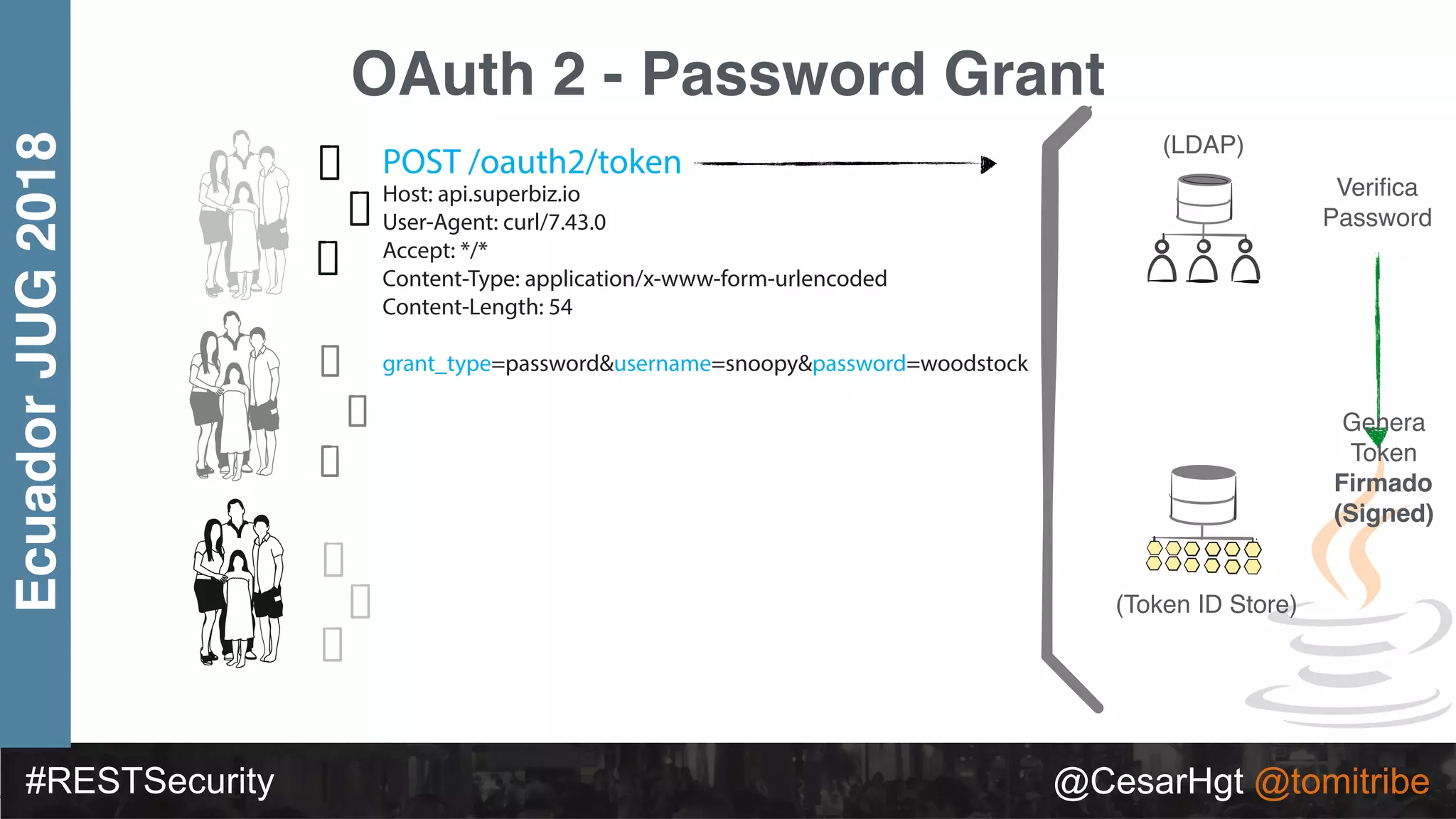
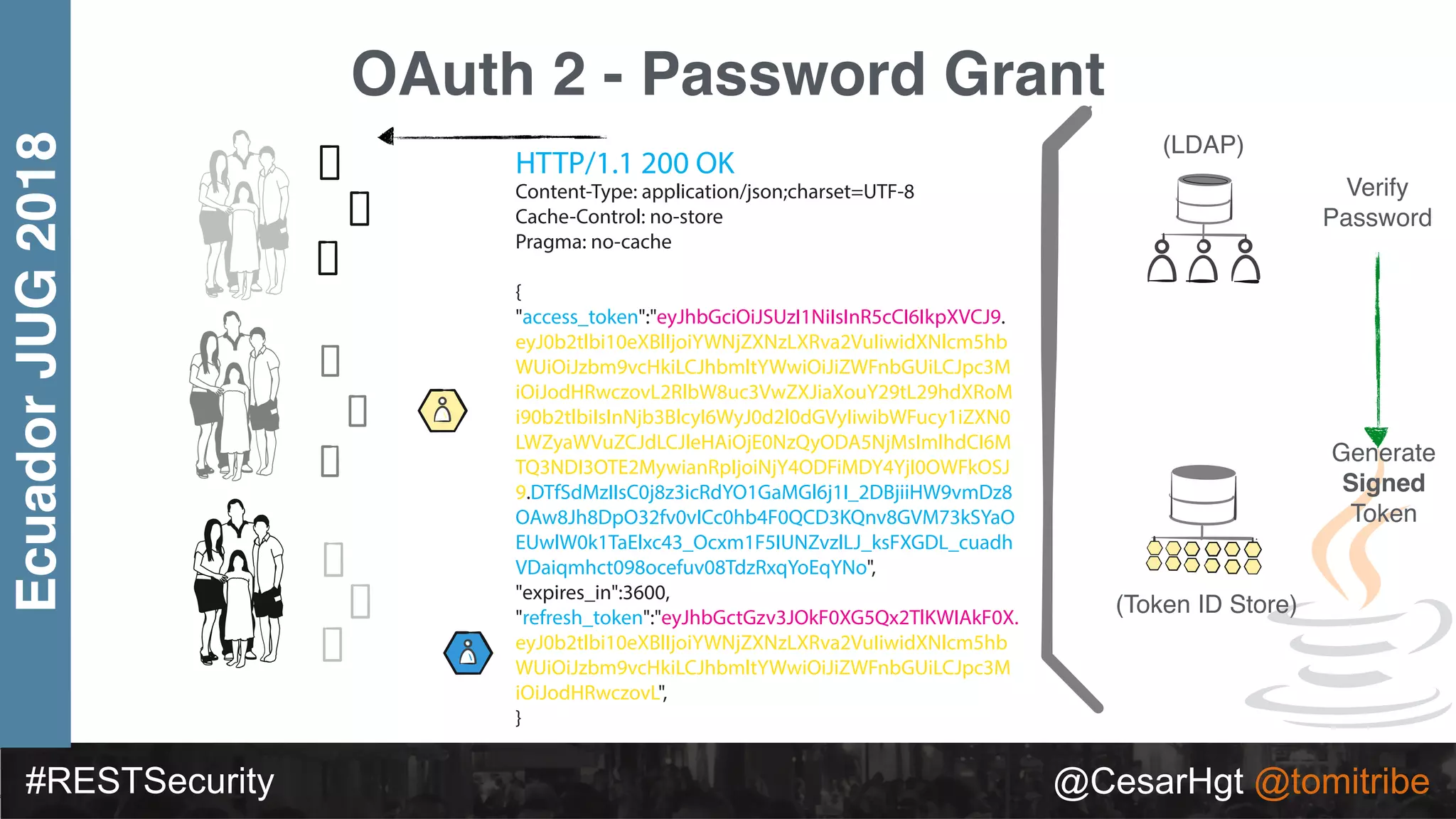
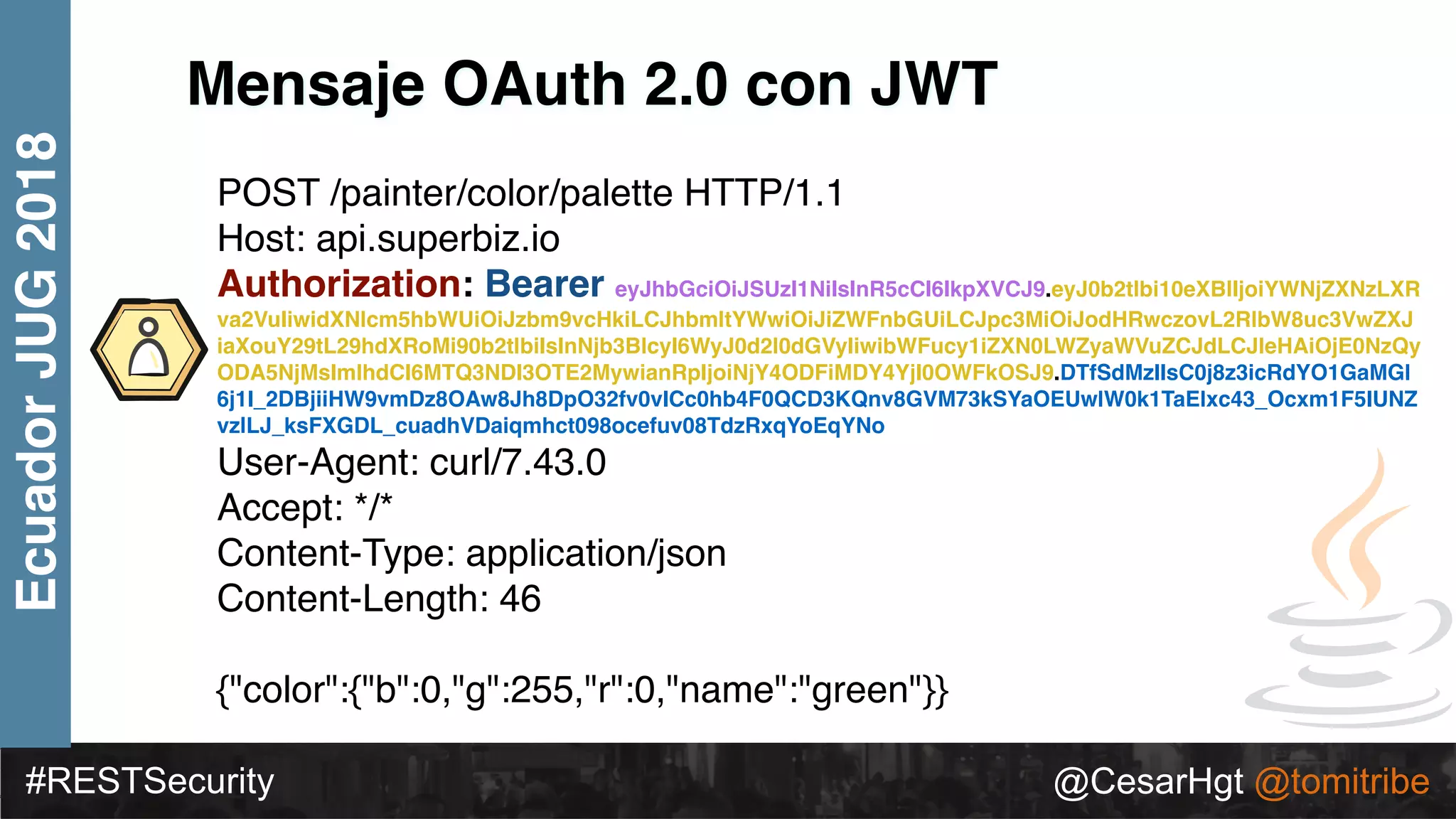
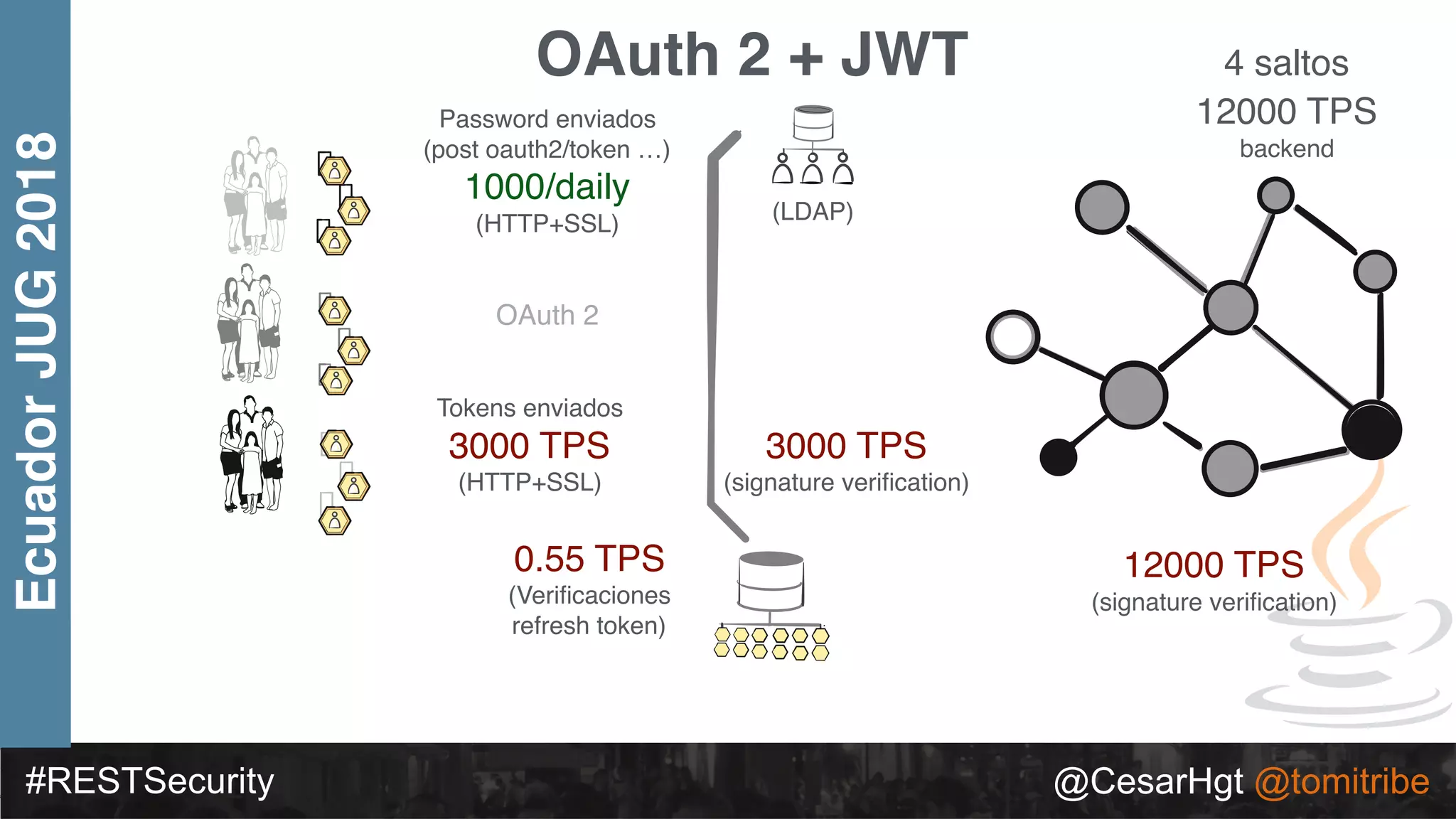
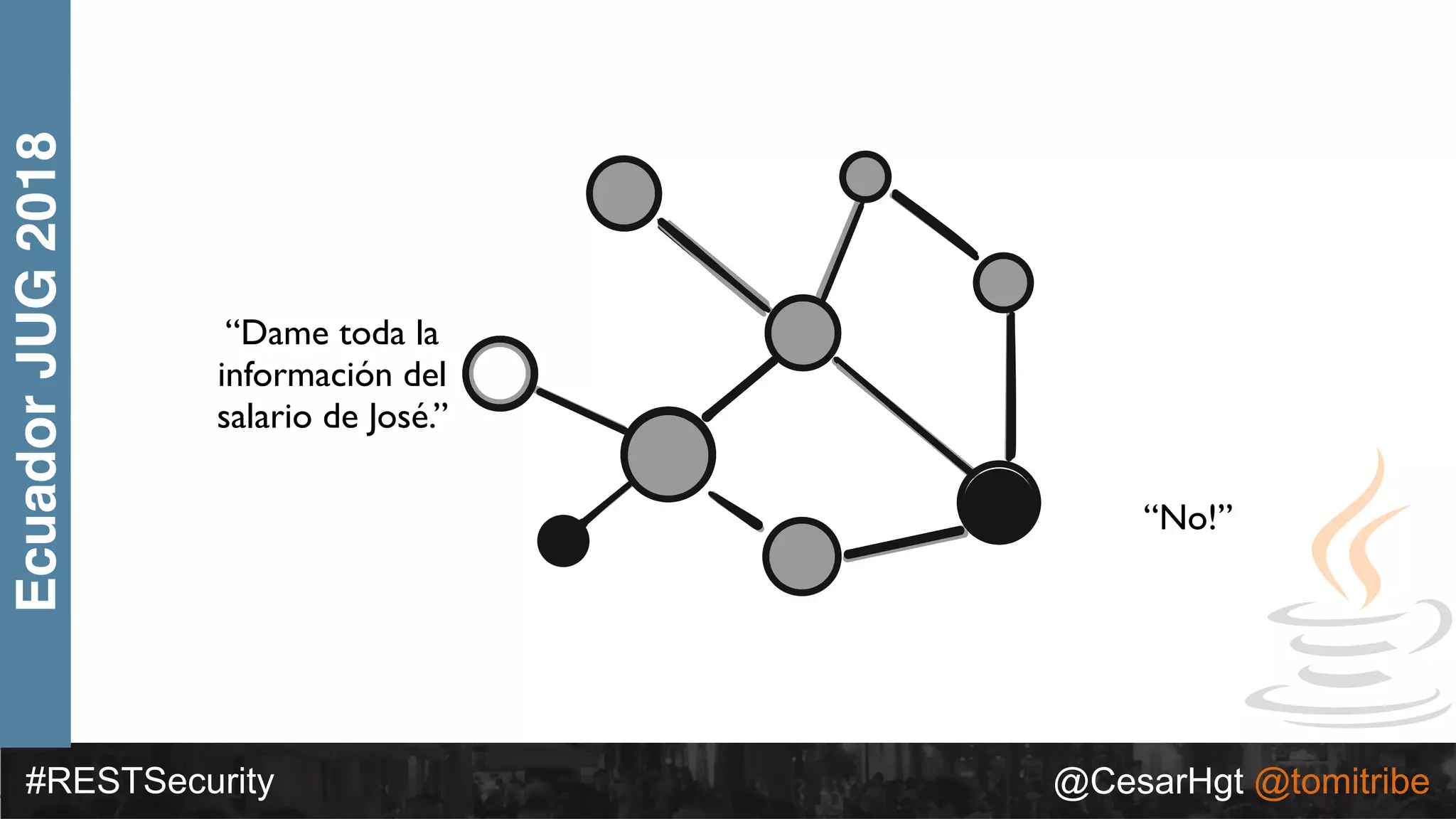
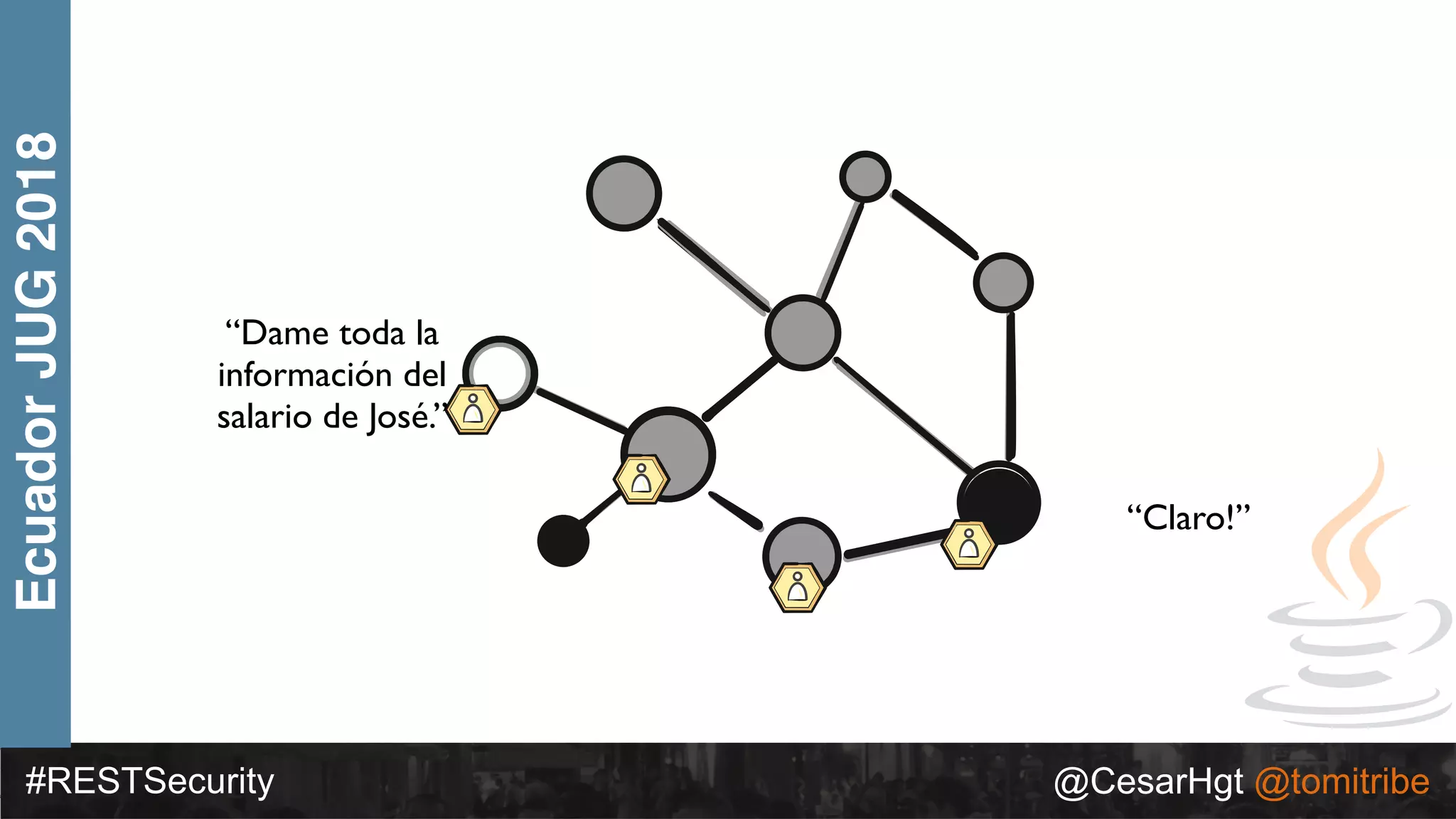
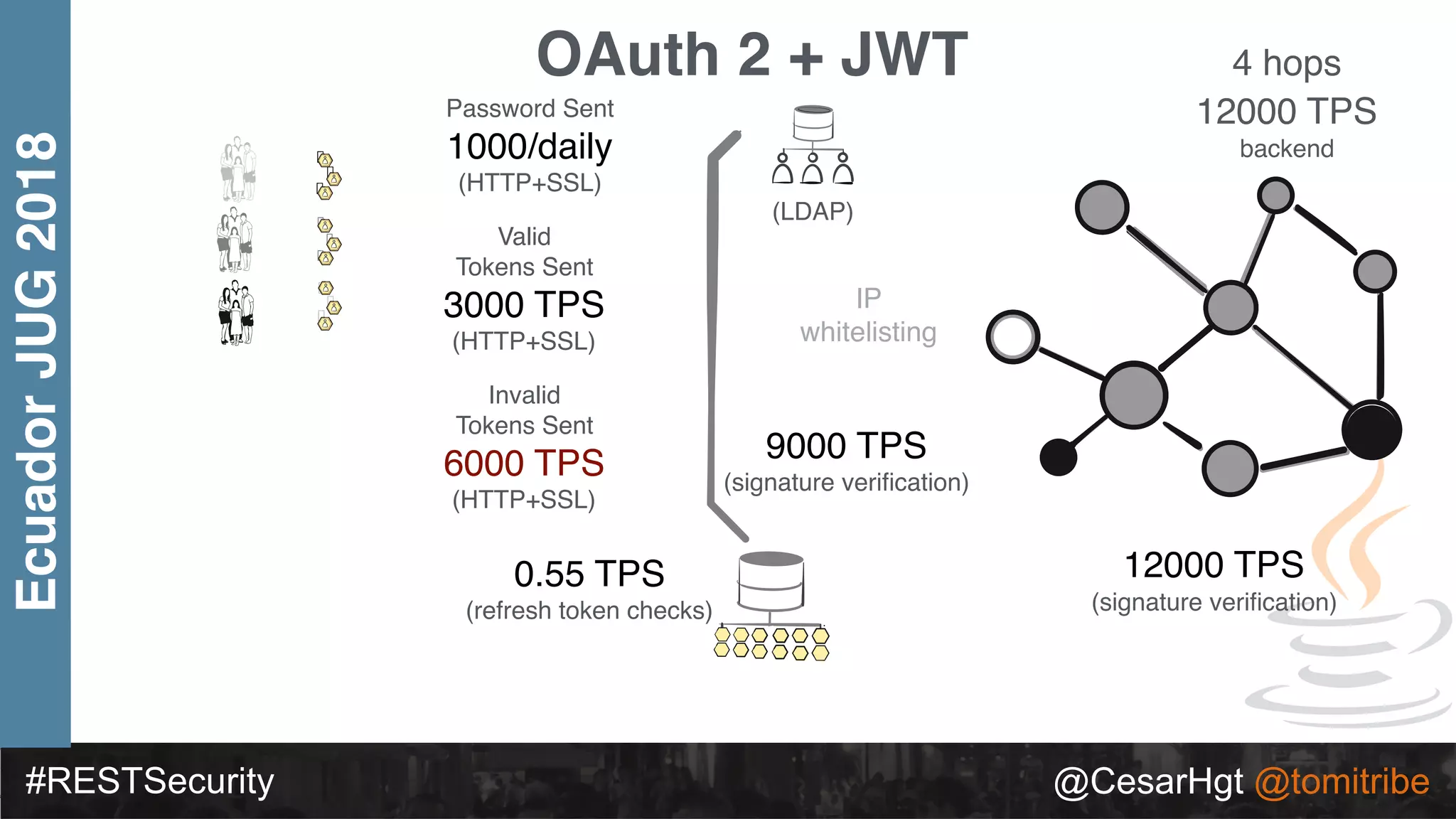
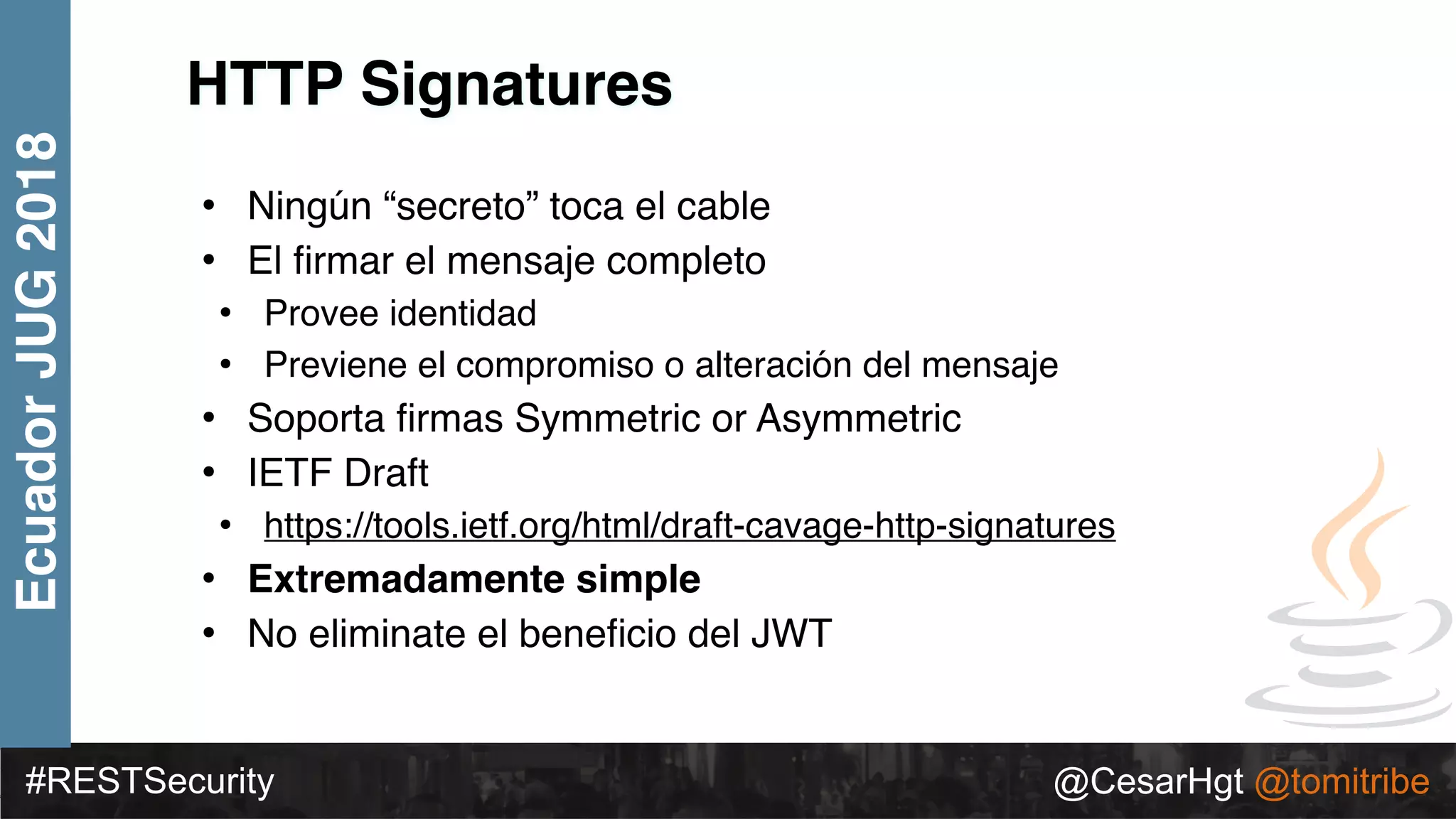
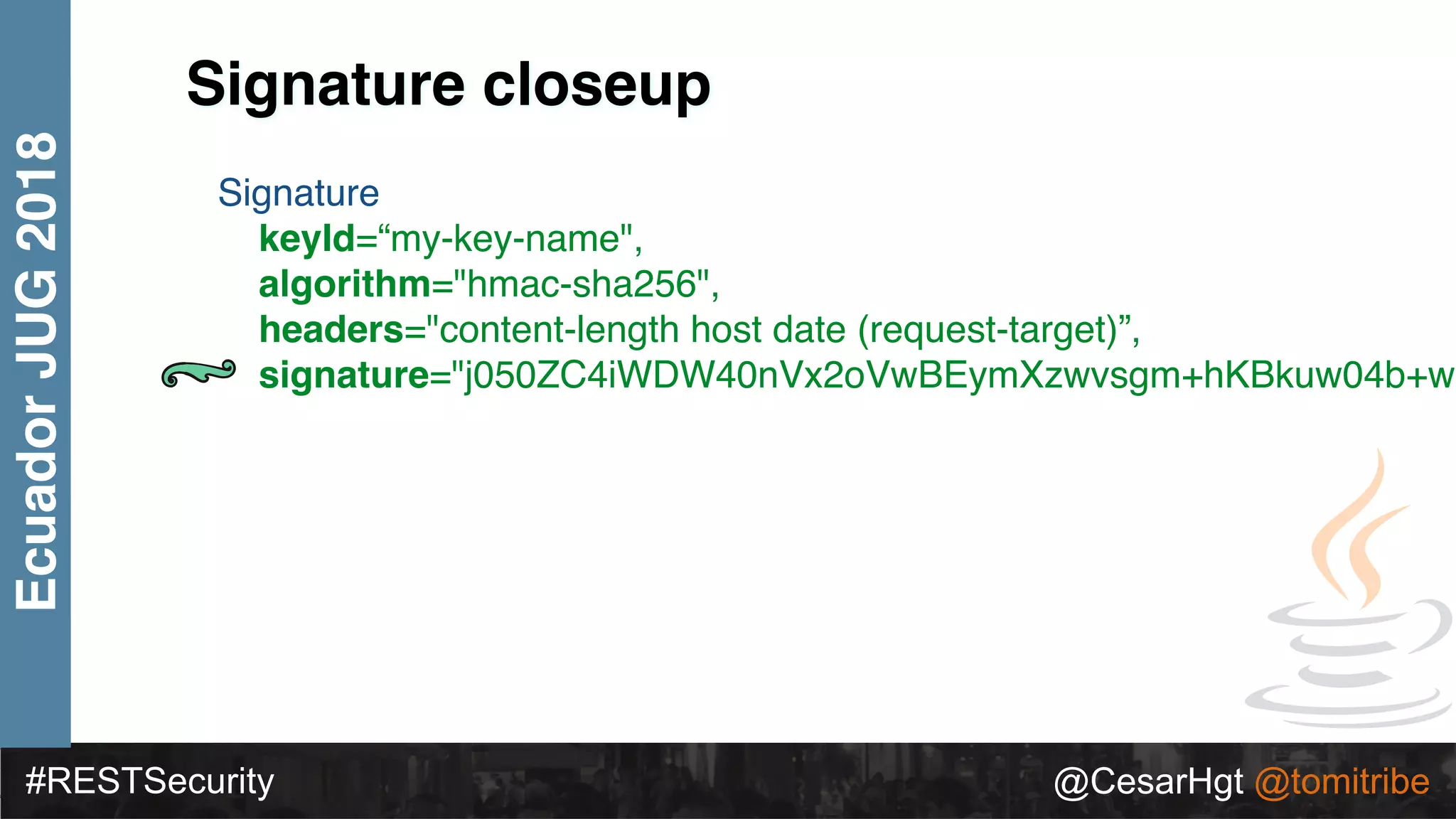
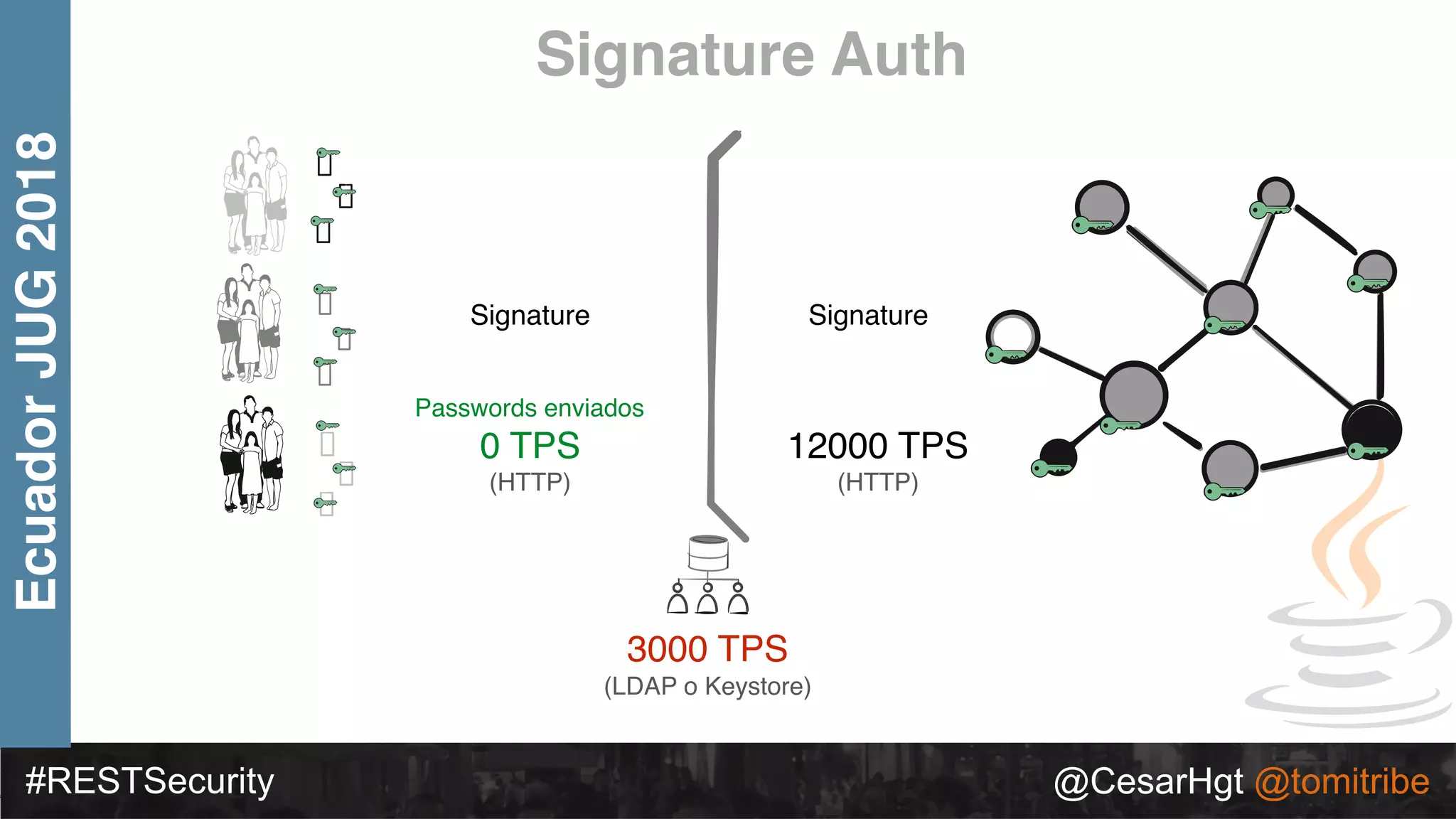
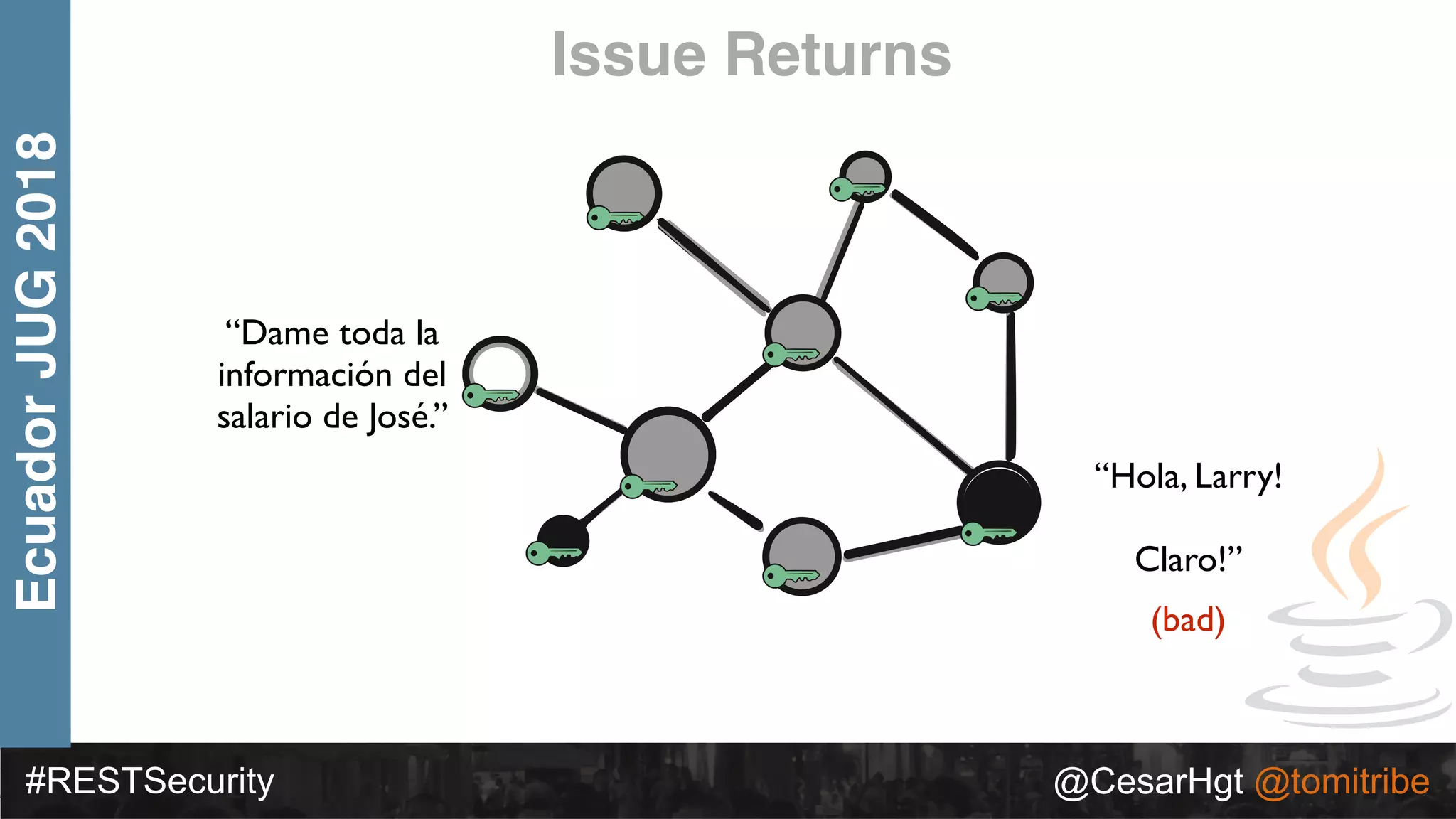
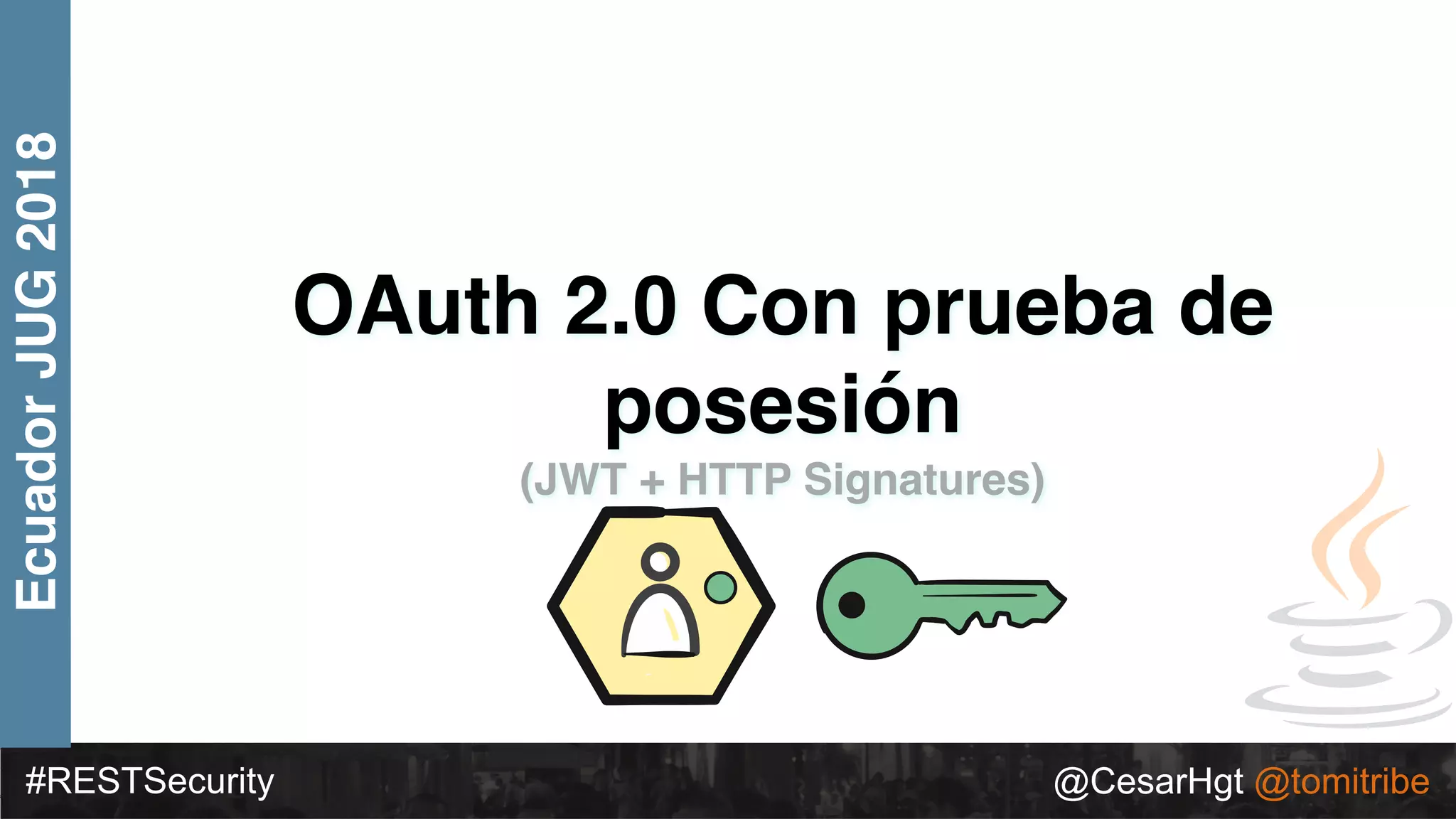
César Hernández discusses evolving security in REST services, focusing on topics like OAuth 2.0, JWT, and securing APIs beyond basic authentication. He highlights the performance metrics for different authentication methods and the challenges associated with each. The presentation emphasizes the importance of secure token handling and modern practices in securing RESTful applications.

![#RESTSecurity @CesarHgt @tomitribe
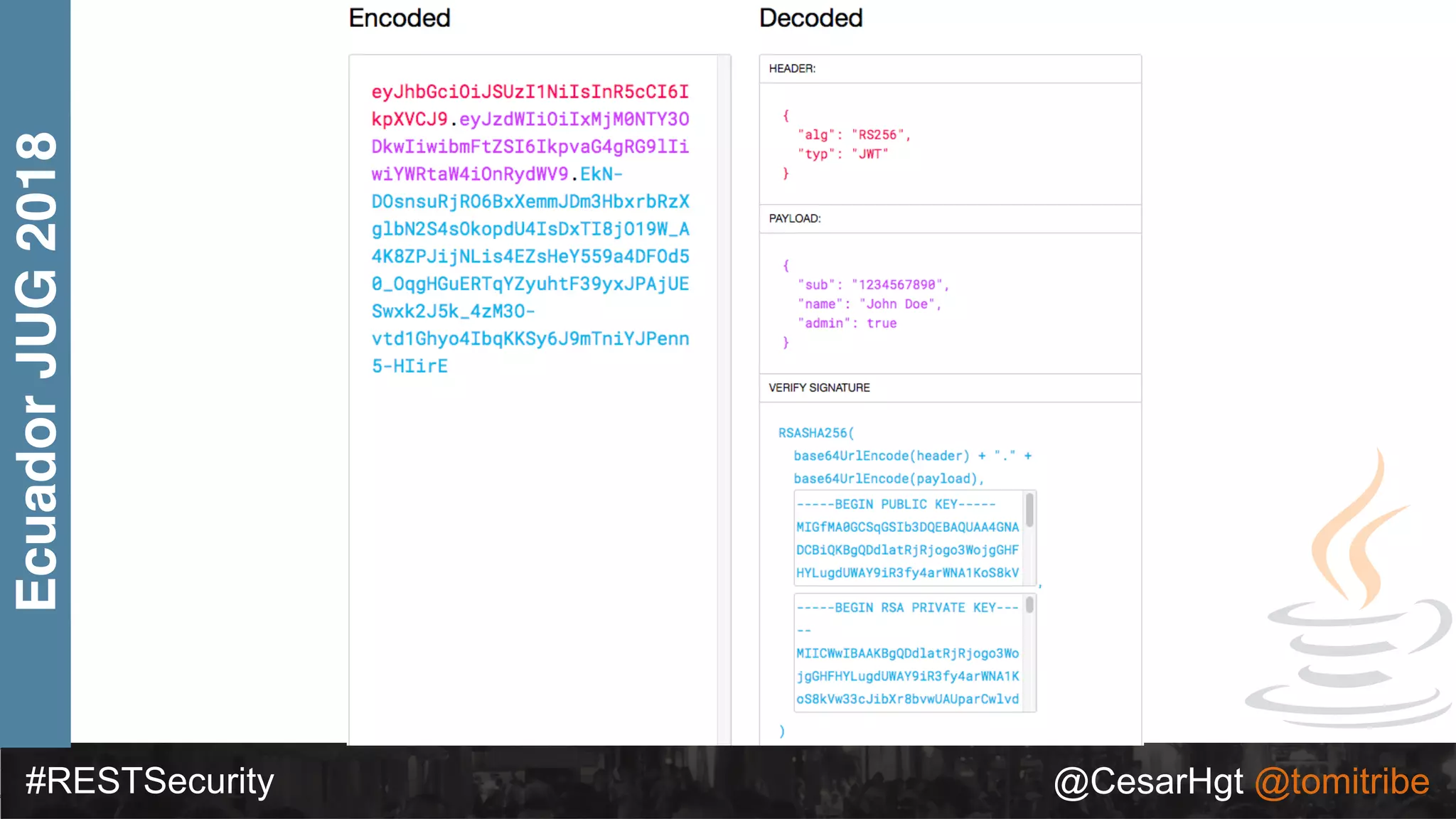
EcuadorJUG2018 • { "alg": “RS256", "typ": “JWT" }
• {
"token-type": "access-token",
"username": "snoopy",
"animal": "beagle",
"iss": "https://demo.superbiz.com/oauth2/token",
"scopes": [
“twitter”, "mans-best-friend"
],
"exp": 1474280963,
"iat": 1474279163,
"jti": "66881b068b249ad9"
}
• DTfSdMzIIsC0j8z3icRdYO1GaMGl6j1I_2DBjiiHW9vmDz8OAw8Jh8DpO32fv
0vICc0hb4F0QCD3KQnv8GVM73kSYaOEUwlW0k1TaElxc43_Ocxm1F5IUNZvzl
LJ_ksFXGDL_cuadhVDaiqmhct098ocefuv08TdzRxqYoEqYNo](https://image.slidesharecdn.com/2018ecuadordeconstruyendoyevolucionandolaseguridadenserviciosrest-180717191258/75/2018-ecuador-deconstruyendo-y-evolucionando-la-seguridad-en-servicios-rest-58-2048.jpg)
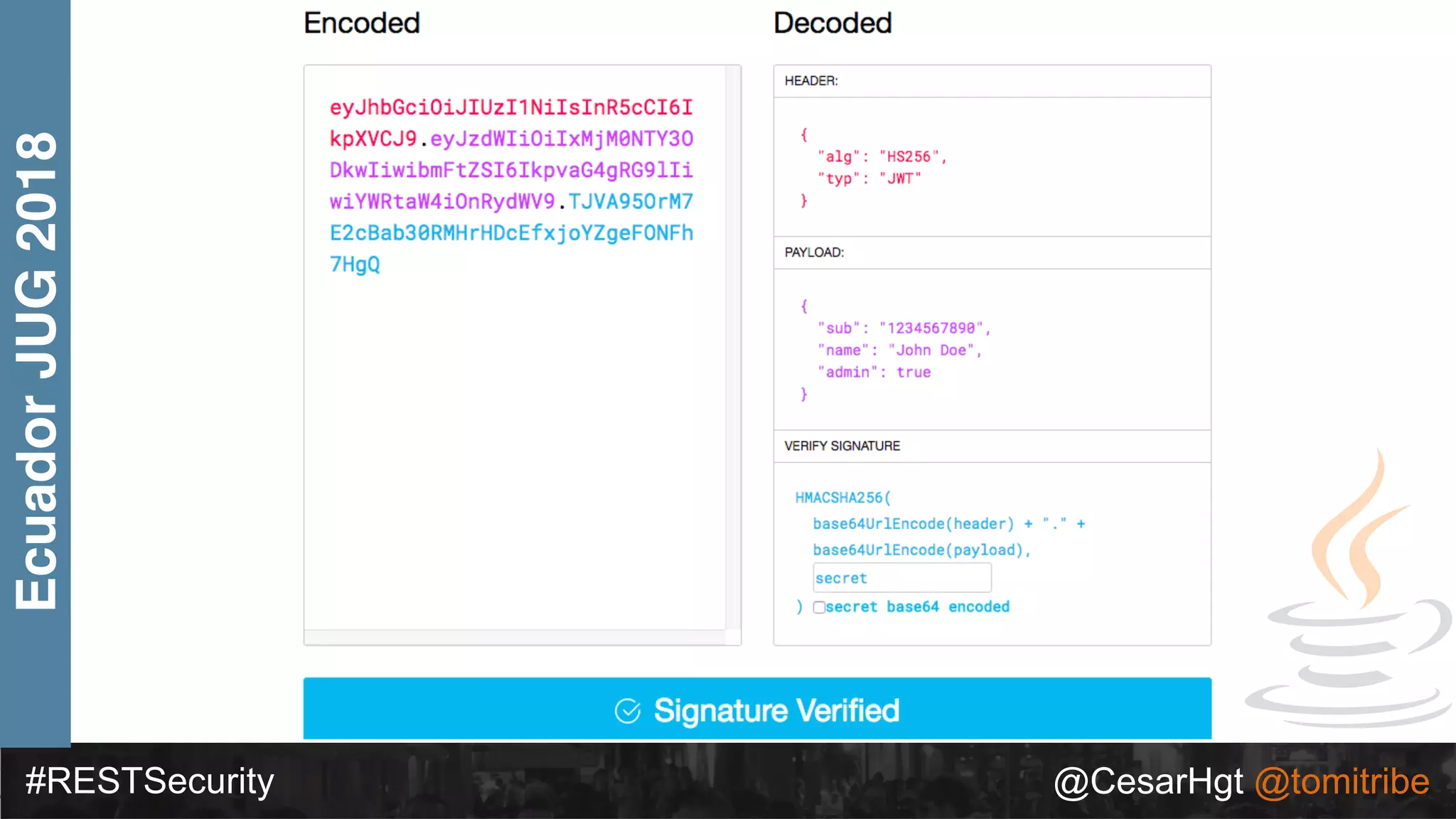




![#RESTSecurity @CesarHgt @tomitribe
EcuadorJUG2018
{ "alg": “RS256", "typ": “JWT" }
{ "token-type": "access-token",
"username": "snoopy",
"iss": "https://demo.superbiz.com/oauth2/token",
"scopes": ["twitter”, "mans-best-friend"],
"exp": 1474280963,
"iat": 1474279163,
"jti": "66881b068b249ad9"
}
DTfSdMzIIsC0j8z3icRdYO1GaMGl6j1I_2DBjiiHW9vmDz8OAw8Jh8DpO32fv0vICc
0hb4F0QCD3KQnv8GVM73kSYaOEUwlW0k1TaElxc43_Ocxm1F5IUNZvzlLJ_ksF
XGDL_cuadhVDaiqmhct098ocefuv08TdzRxqYoEqYNo
Access Token](https://image.slidesharecdn.com/2018ecuadordeconstruyendoyevolucionandolaseguridadenserviciosrest-180717191258/75/2018-ecuador-deconstruyendo-y-evolucionando-la-seguridad-en-servicios-rest-95-2048.jpg)
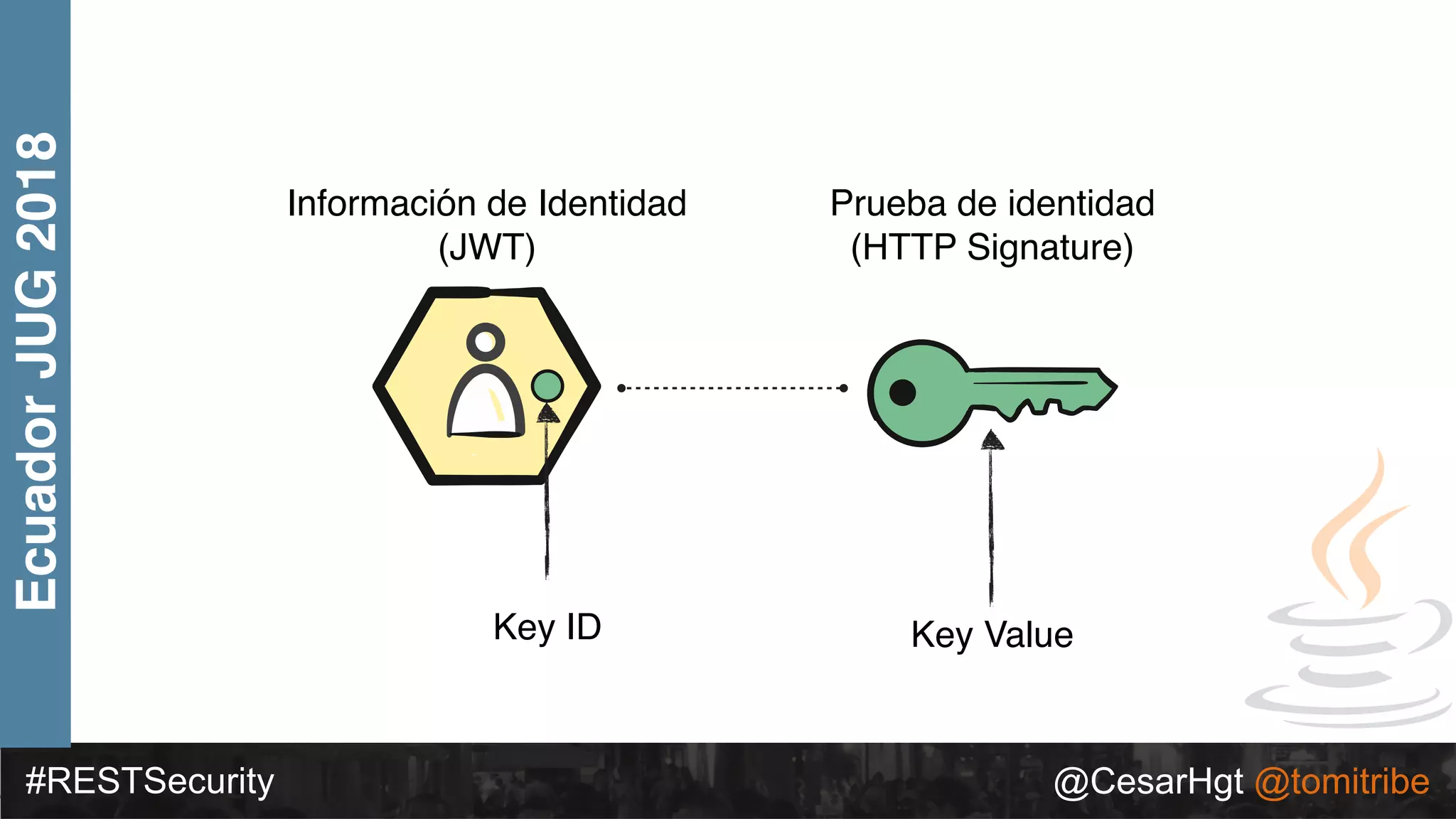
![#RESTSecurity @CesarHgt @tomitribe
EcuadorJUG2018
{ "alg": “RS256", "typ": “JWT" }
{ "token-type": "pop",
"cnf":{ "kid": "green-1234" }
"username": "snoopy",
"iss": "https://demo.superbiz.com/oauth2/token",
"scopes": ["twitter”, "mans-best-friend"],
"exp": 1474280963,
"iat": 1474279163,
"jti": "66881b068b249ad9"
}
DTfSdMzIIsC0j8z3icRdYO1GaMGl6j1I_2DBjiiHW9vmDz8OAw8Jh8DpO32fv0vICc
0hb4F0QCD3KQnv8GVM73kSYaOEUwlW0k1TaElxc43_Ocxm1F5IUNZvzlLJ_ksF
XGDL_cuadhVDaiqmhct098ocefuv08TdzRxqYoEqYNo
Access Token](https://image.slidesharecdn.com/2018ecuadordeconstruyendoyevolucionandolaseguridadenserviciosrest-180717191258/75/2018-ecuador-deconstruyendo-y-evolucionando-la-seguridad-en-servicios-rest-96-2048.jpg)