2015 java ieee projects list
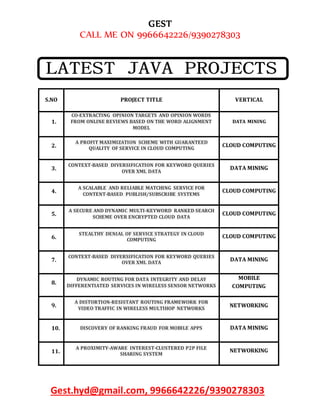
- 1. GEST CALL ME ON 9966642226/9390278303 Gest.hyd@gmail.com, 9966642226/9390278303 S.NO PROJECT TITLE VERTICAL 1. CO-EXTRACTING OPINION TARGETS AND OPINION WORDS FROM ONLINE REVIEWS BASED ON THE WORD ALIGNMENT MODEL DATA MINING 2. A PROFIT MAXIMIZATION SCHEME WITH GUARANTEED QUALITY OF SERVICE IN CLOUD COMPUTING CLOUD COMPUTING 3. CONTEXT-BASED DIVERSIFICATION FOR KEYWORD QUERIES OVER XML DATA DATA MINING 4. A SCALABLE AND RELIABLE MATCHING SERVICE FOR CONTENT-BASED PUBLISH/SUBSCRIBE SYSTEMS CLOUD COMPUTING 5. A SECURE AND DYNAMIC MULTI-KEYWORD RANKED SEARCH SCHEME OVER ENCRYPTED CLOUD DATA CLOUD COMPUTING 6. STEALTHY DENIAL OF SERVICE STRATEGY IN CLOUD COMPUTING CLOUD COMPUTING 7. CONTEXT-BASED DIVERSIFICATION FOR KEYWORD QUERIES OVER XML DATA DATA MINING 8. DYNAMIC ROUTING FOR DATA INTEGRITY AND DELAY DIFFERENTIATED SERVICES IN WIRELESS SENSOR NETWORKS MOBILE COMPUTING 9. A DISTORTION-RESISTANT ROUTING FRAMEWORK FOR VIDEO TRAFFIC IN WIRELESS MULTIHOP NETWORKS NETWORKING 10. DISCOVERY OF RANKING FRAUD FOR MOBILE APPS DATA MINING 11. A PROXIMITY-AWARE INTEREST-CLUSTERED P2P FILE SHARING SYSTEM NETWORKING
- 2. GEST CALL ME ON 9966642226/9390278303 Gest.hyd@gmail.com, 9966642226/9390278303 12. A LIGHTWEIGHT SECURE SCHEME FOR DETECTING PROVENANCE FORGERY AND PACKET DROP ATTACKS IN WIRELESS SENSOR NETWORK SECURE COMPUTING 13. PRIVACY-PRESERVING AND TRUTHFUL DETECTION OF PACKET DROPPING ATTACKS IN WIRELESS AD HOC NETWORKS MOBILE COMPUTING 14. MAXIMIZING P2P FILE ACCESS AVAILABILITY IN MOBILE AD HOC NETWORKS THOUGH REPLICATION FOR EFFICIENT FILE SHARING NETWORKING 15. ON SUMMARIZATION AND TIMELINE GENERATION FOR EVOLUTIONARY TWEET STREAMS DATA MINING 16. A SECURE ANTI-COLLUSION DATA SHARING SCHEME FOR DYNAMIC GROUPS IN THE CLOUD CLOUD COMPUTING 17. T-CLOSENESS THROUGH MICRO AGGREGATION: STRICT PRIVACY WITH ENHANCED UTILITY PRESERVATION DATA MINING 18. USER-DEFINED PRIVACY GRID SYSTEM FOR CONTINUOUS LOCATION-BASED SERVICES MOBILE COMPUTING 19. ASYMMETRIC SOCIAL PROXIMITY BASED PRIVATE MATCHING PROTOCOLS FOR ONLINE SOCIAL NETWORKS PARALLEL & DISTRIBUTED SYSTEMS 20. AN AUTHENTICATED TRUST AND REPUTATION CALCULATION AND MANAGEMENT SYSTEM FOR CLOUD AND SENSOR NETWORKS INTEGRATI CLOUD COMPUTING 21. PRIVACY POLICY INFERENCE OF USER-UPLOADED IMAGES ON CONTENT SHARING SITES DATA MINING 22. REVERSE NEAREST NEIGHBORS IN UNSUPERVISED DISTANCE- BASED OUTLIER DETECTION DATA MINING 23. A COMPUTATIONAL DYNAMIC TRUST MODEL FOR USER AUTHORIZATION MOBILE COMPUTING
- 3. GEST CALL ME ON 9966642226/9390278303 Gest.hyd@gmail.com, 9966642226/9390278303 24. AUDIT-FREE CLOUD STORAGE VIA DENIABLE ATTRIBUTE- BASED ENCRYPTION CLOUD COMPUTING 25. COST-EFFECTIVE AUTHENTIC AND ANONYMOUS DATA SHARING WITH FORWARD SECURITY PARALLEL & DISTRIBUTED SYSTEMS 26. CIRCUIT CIPHERTEXT-POLICY ATTRIBUTE-BASED HYBRID ENCRYPTION WITH VERIFIABLE DELEGATION IN CLOUD COMPUTING CLOUD COMPUTING 27. DESIGNING HIGH PERFORMANCE WEB-BASED COMPUTING SERVICES TO PROMOTE TELEMEDICINE DATABASE MANAGEMENT SYSTEM SERVICE COMPUTING 28. ROUTE-SAVER: LEVERAGING ROUTE APIS FOR ACCURATE AND EFFICIENT QUERY PROCESSING AT LOCATION-BASED SERVICES DATA MINING 29. CLOUDARMOR: SUPPORTING REPUTATION-BASED TRUST MANAGEMENT FOR CLOUD SERVICES CLOUD COMPUTING 30. CONTRIBUTORY BROADCAST ENCRYPTION WITH EFFICIENT ENCRYPTION AND SHORT CIPHERTEXTS SECURE COMPUTING 31. SECURE DISTRIBUTED DEDUPLICATION SYSTEMS WITH IMPROVED RELIABILITY PARALLEL & DISTRIBUTED SYSTEMS 32. CONTROL CLOUD DATA ACCESS PRIVILEGE AND ANONYMITY WITH FULLY ANONYMOUS ATTRIBUTE-BASED ENCRYPTION CLOUD COMPUTING 33. DETECTING MALICIOUS FACEBOOK APPLICATIONS NETWORKING 34. LOCATION-AWARE AND PERSONALIZED COLLABORATIVE FILTERING FOR WEB SERVICE RECOMMENDATION SERVICE COMPUTING 35. TWEET SEGMENTATION AND ITS APPLICATION TO NAMED ENTITY RECOGNITION DATA MINING 36. A FRAMEWORK FOR SECURE COMPUTATIONS WITH TWO NON-COLLUDING SERVERS AND MULTIPLE CLIENTS, APPLIED TO RECOMMENDAT INFORMATION FORENSICS AND
- 4. GEST CALL ME ON 9966642226/9390278303 Gest.hyd@gmail.com, 9966642226/9390278303 SECURITY 37. TOWARDS EFFECTIVE BUG TRIAGE WITH SOFTWARE DATA REDUCTION TECHNIQUES DATA MINING 38. AN ATTRIBUTE-ASSISTED RERANKING MODEL FOR WEB IMAGE SEARCH IMAGE PROCESSING 39. EMR: A SCALABLE GRAPH-BASED RANKING MODEL FOR CONTENT-BASED IMAGE RETRIEVAL IMAGE PROCESSING 40. DDSGA: A DATA-DRIVEN SEMI-GLOBAL ALIGNMENT APPROACH FOR DETECTING MASQUERADE ATTACKS SECURE COMPUTING 41. REAL-TIME DETECTION OF TRAFFIC FROM TWITTER STREAM ANALYSIS DATA MINING 42. LEARNING TO RANK IMAGE TAGS WITH LIMITED TRAINING EXAMPLES IMAGE PROCESSING 43. MALWARE PROPAGATION IN LARGE-SCALE NETWORKS DATA MINING 44. PRIVACY-PRESERVING PUBLIC AUDITING FOR REGENERATING-CODE-BASED CLOUD STORAGE CLOUD COMPUTING 45. IMPROVED PRIVACY-PRESERVING P2P MULTIMEDIA DISTRIBUTION BASED ON RECOMBINED FINGERPRINTS SECURE COMPUTING 46. PROGRESSIVE DUPLICATE DETECTION DATA MINING 47. SECURE SPATIAL TOP-K QUERY PROCESSING VIA UN TRUSTED LOCATION-BASED SERVICE PROVIDERS SECURE COMPUTING 48. KEY UPDATING FOR LEAKAGE RESILIENCY WITH APPLICATION TO AES MODES OF OPERATION INFORMATION FORENSICS AND SECURITY
- 5. GEST CALL ME ON 9966642226/9390278303 Gest.hyd@gmail.com, 9966642226/9390278303 49. TOWARDS ONLINE SHORTEST PATH COMPUTATION DATA MINING 50. TRAFFIC PATTERN-BASED CONTENT LEAKAGE DETECTION FOR TRUSTED CONTENT DELIVERY NETWORKS PARALLEL & DISTRIBUTED SYSTEMS 51. DISCOVERING EMERGING TOPICS IN SOCIAL STREAMS VIA LINK-ANOMALY DETECTION DATA MINING 52. DISTRIBUTED, CONCURRENT, AND INDEPENDENT ACCESS TO ENCRYPTED CLOUD DATABASES CLOUD COMPUTING 53. A COCKTAIL APPROACH FOR TRAVEL PACKAGE RECOMMENDATION DATA MINING 54. A HYBRID CLOUD APPROACH FOR SECURE AUTHORIZED DEDUPLICATION CLOUD COMPUTING 55. A SCALABLE TWO-PHASE TOP-DOWN SPECIALIZATION APPROACH FOR DATA ANONYMIZATION USING MAP REDUCE ON CLOUD CLOUD COMPUTING 56. A STOCHASTIC MODEL TO INVESTIGATE DATA CENTER PERFORMANCE AND QOS IN IAAS CLOUD COMPUTING SYSTEMS CLOUD COMPUTING 57. ACCURACY-CONSTRAINED PRIVACY-PRESERVING ACCESS CONTROL MECHANISM FOR RELATIONAL DATA DATA MINING 58. AN INCENTIVE FRAMEWORK FOR CELLULAR TRAFFIC OFFLOADING MOBILE COMPUTING 59. AUTOMATIC TEST PACKET GENERATION NETWORKING 60. BESTPEER++: A PEER-TO-PEER BASED LARGE-SCALE DATA PROCESSING PLATFORM DATA MINING 61. BOUNDARY CUTTING FOR PACKET CLASSIFICATION NETWORKING
- 6. GEST CALL ME ON 9966642226/9390278303 Gest.hyd@gmail.com, 9966642226/9390278303 62. CAPTCHA AS GRAPHICAL PASSWORDS—A NEW SECURITY PRIMITIVE BASED ON HARD AI PROBLEMS SECURE COMPUTING 63. COOPERATIVE CACHING FOR EFFICIENT DATA ACCESS IN DISRUPTION TOLERANT NETWORKS MOBILE COMPUTING 64. COST-EFFECTIVE RESOURCE ALLOCATION OF OVERLAY ROUTING RELAY NODES NETWORKING 65. DATA MINING WITH BIG DATA DATA MINING 66. DECENTRALIZED ACCESS CONTROL WITH ANONYMOUS AUTHENTICATION OF DATA STORED IN CLOUDS CLOUD COMPUTING 67. EFFICIENT AND PRIVACY-AWARE DATA AGGREGATION IN MOBILE SENSING SECURE COMPUTING 68. EFFICIENT AUTHENTICATION FOR MOBILE AND PERVASIVE COMPUTING MOBILE COMPUTING 69. ENABLING TRUSTWORTHY SERVICE EVALUATION IN SERVICE- ORIENTED MOBILE SOCIAL NETWORKS PARALLEL & DISTRIBUTED SYSTEMS 70. EXPRESSIVE, EFFICIENT, AND REVOCABLE DATA ACCESS CONTROL FOR MULTI-AUTHORITY CLOUD STORAGE CLOUD COMPUTING 71. FACILITATING DOCUMENT ANNOTATION USING CONTENT AND QUERYING VALUE DATA MINING 72. FAST NEAREST NEIGHBOR SEARCH WITH KEYWORDS DATA MINING 73. FRIENDBOOK: A SEMANTIC-BASED FRIEND RECOMMENDATION SYSTEM FOR SOCIAL NETWORKS MOBILE COMPUTING 74. KEY-AGGREGATE CRYPTOSYSTEM FOR SCALABLE DATA SHARING IN CLOUD STORAGE CLOUD COMPUTING
- 7. GEST CALL ME ON 9966642226/9390278303 Gest.hyd@gmail.com, 9966642226/9390278303 75. LOCAWARD: A SECURITY AND PRIVACY AWARE LOCATION- BASED REWARDING SYSTEM PARALLEL & DISTRIBUTED SYSTEMS 76. ORUTA: PRIVACY-PRESERVING PUBLIC AUDITING FOR SHARED DATA IN THE CLOUD CLOUD COMPUTING 77. PRIVACY-ENHANCED WEB SERVICE COMPOSITION SERVICE COMPUTING 78. PRIVACY-PRESERVING AND CONTENT-PROTECTING LOCATION BASED QUERIES DATA MINING 79. PRIVACY-PRESERVING MULTI-KEYWORD RANKED SEARCH OVER ENCRYPTED CLOUD DATA CLOUD COMPUTING 80. PROFILR : TOWARD PRESERVING PRIVACY AND FUNCTIONALITY IN GEOSOCIAL NETWORKS SECURE COMPUTING 81. RRE: A GAME-THEORETIC INTRUSION RESPONSE AND RECOVERY ENGINE PARALLEL & DISTRIBUTED SYSTEMS 82. SCALABLE DISTRIBUTED SERVICE INTEGRITY ATTESTATION FOR SOFTWARE-AS-A-SERVICE CLOUDS CLOUD COMPUTING 83. SECURE DATA RETRIEVAL FOR DECENTRALIZED DISRUPTION- TOLERANT MILITARY NETWORKS NETWORKING 84. SECURING BROKER-LESS PUBLISH/SUBSCRIBE SYSTEMS USING IDENTITY-BASED ENCRYPTION PARALLEL & DISTRIBUTED SYSTEMS 85. SECURITY EVALUATION OF PATTERN CLASSIFIERS UNDER ATTACK DATA MINING 86. SOS: A DISTRIBUTED MOBILE Q&A SYSTEM BASED ON SOCIAL NETWORKS PARALLEL & DISTRIBUTED SYSTEMS
- 8. GEST CALL ME ON 9966642226/9390278303 Gest.hyd@gmail.com, 9966642226/9390278303 87. SUPPORTING PRIVACY PROTECTION IN PERSONALIZED WEB SEARCH DATA MINING 88. THE CLIENT ASSIGNMENT PROBLEM FOR CONTINUOUS DISTRIBUTED INTERACTIVE APPLICATIONS: ANALYSIS, ALGORITHMS, AND EVALUATION PARALLEL & DISTRIBUTED SYSTEMS 89. THE DESIGN AND EVALUATION OF AN INFORMATION SHARING SYSTEM FOR HUMAN NETWORKS PARALLEL & DISTRIBUTED SYSTEMS 90. TOP-K QUERY RESULT COMPLETENESS VERIFICATION IN TIERED SENSOR NETWORKS SECURE COMPUTING