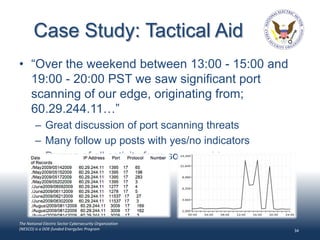
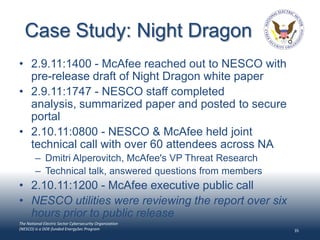
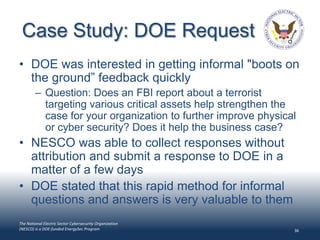
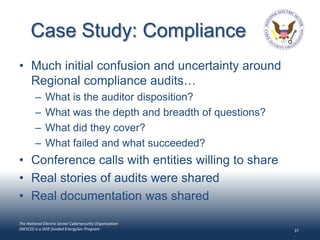
The document discusses the current challenges facing cybersecurity in the electric sector. It notes that legacy systems remain vulnerable, adversaries are intelligent and adaptive, and economic pressures have increased risks. It then introduces the National Electric Sector Cybersecurity Organization (NESCO), a non-profit funded by the Department of Energy to improve information sharing and cybersecurity practices across the electric industry through public-private collaboration. NESCO has over 650 members from electric utilities and aims to identify best practices, analyze threats, and encourage research to address cyber vulnerabilities.