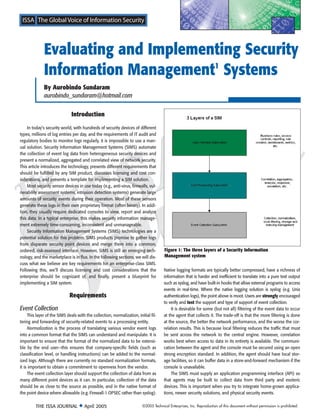
Evaluating and Implementing Security Information Management (SIM) Systems involves three key steps:
1. Defining requirements for event collection, processing, threat assessment, response and integration. Effective SIM systems automate log collection, normalization, correlation and threat analysis from various security devices.
2. Considering licensing and implementation costs, which can be over $100k for software alone. Larger enterprises are more suitable due to economies of scale.
3. Implementing SIM solutions in phases, starting with basic log collection before integrating more advanced correlation and incident response workflows. Pilot programs help evaluate vendor fit and estimate full deployment efforts.