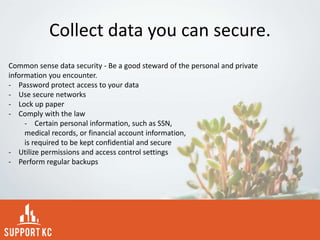
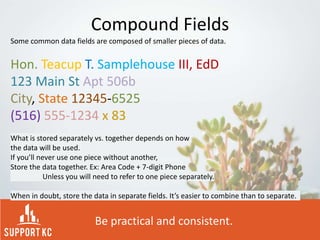
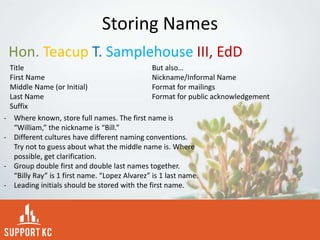
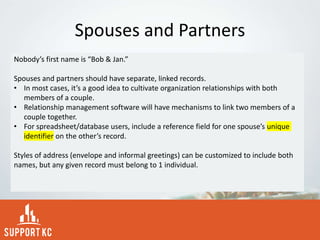
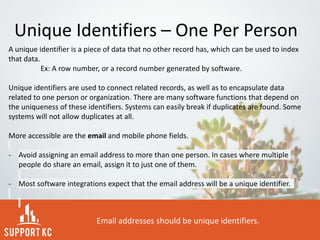
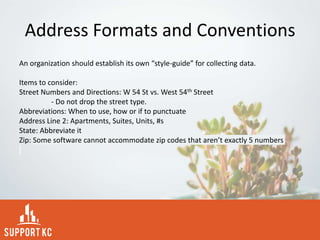
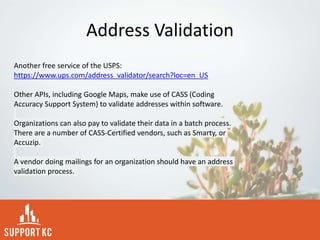
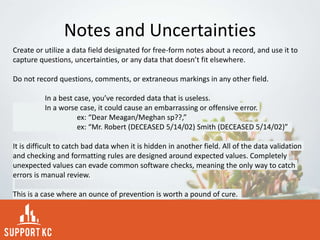
This document provides tips for collecting and storing data. It recommends collecting data that is needed, will be used, and can be gathered consistently. Specific types of data are recommended such as contact information, donation details, and information required by law or grants. Data should be stored securely and consistently using standardized formats and unique identifiers. Notes fields can capture any uncertainties or questions about the data. Address formats and validation are also discussed.