This document provides an overview of configuring mailbox servers in Exchange Server 2010, including:
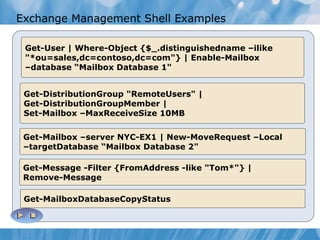
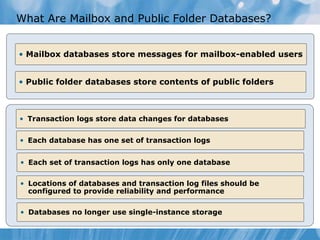
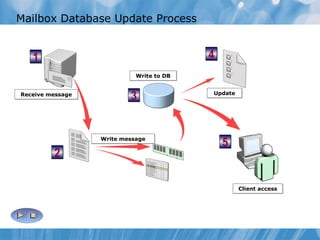
1) Configuring mailbox database roles and public folders using the Exchange Management Console and Exchange Management Shell.
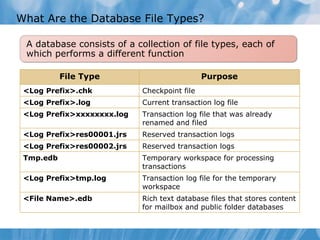
2) Topics on mailbox and public folder databases, storage options, managing mailbox size limits, and considerations for implementing databases.
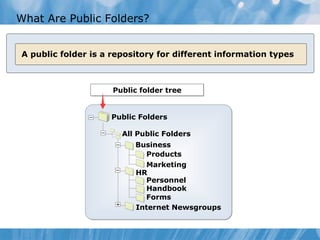
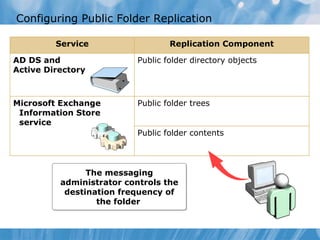
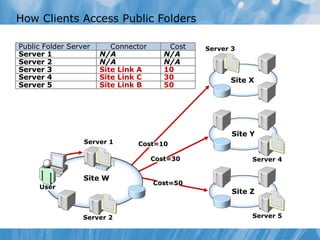
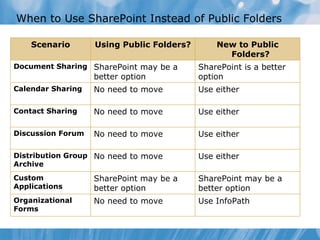
3) Configuring public folders, how clients access public folders, and when to use SharePoint instead.
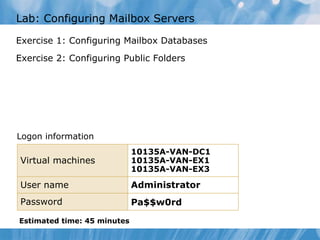
4) A lab scenario on configuring mailbox databases and public folders.
![Exchange Management Shell Cmdlets All Exchange Management Shell cmdlets use the same syntax Cmdlets can be pipelined to other cmdlets: get-user | sort-object name get-user | where-object {$_.name -ilike "a*" } | sort-object name Verb Noun Parameters Example Get User Get-User Get User -Identify -ExternalEmailAddress Enable-Mailuser –Identify Tom – ExternalEmailAddress [email_address]](https://image.slidesharecdn.com/10135a02-111229123846-phpapp01/85/10135-a-02-8-320.jpg)